reSee.it - Tweets Saved By @Curiousityfirst

@Curiousityfirst - DogAndBone @Curious Cat
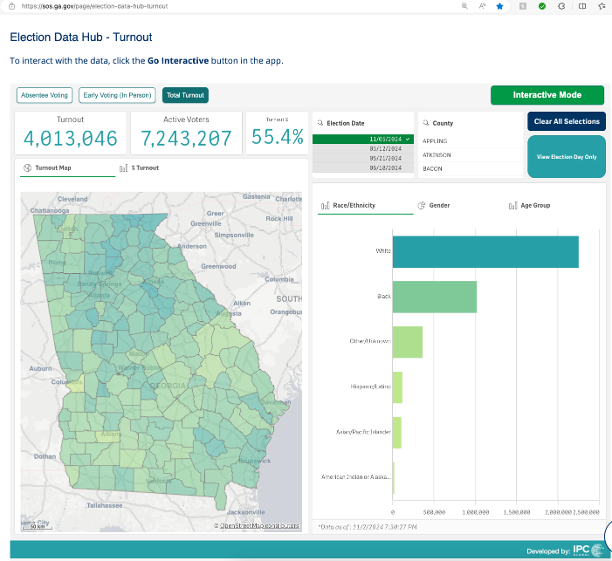
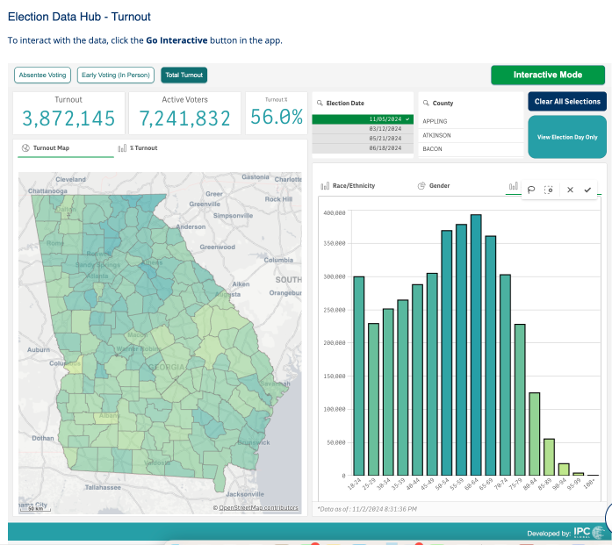
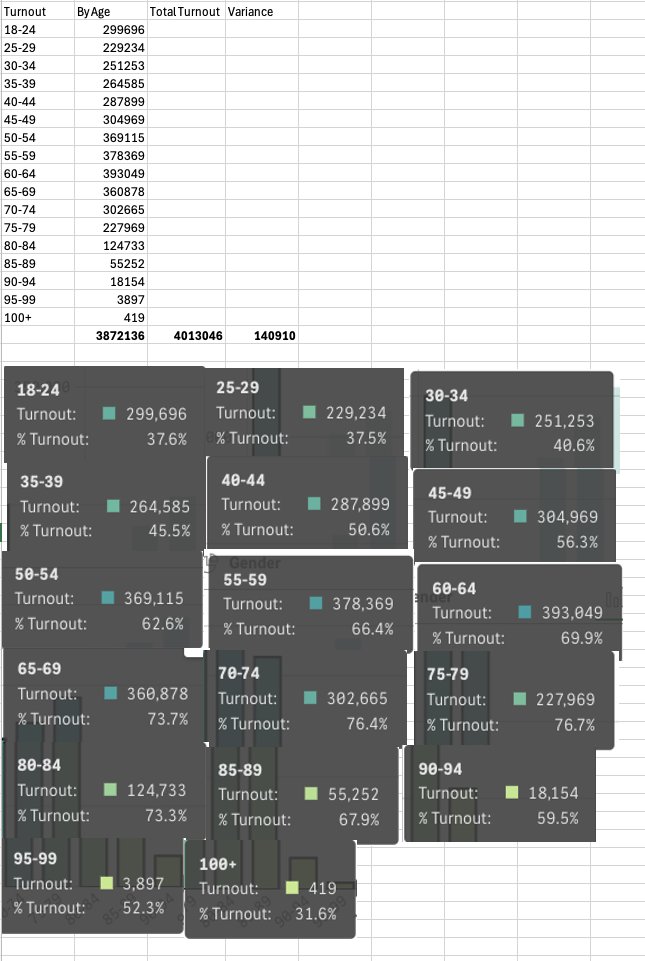
Well here it is folks - GA Data Hub has voters with NO AGE! Total Turnout -4,013,046 By Age -3,872,145 Extra 140K voters - By breakdown Last time I checked proof of ID with age was mandatory in Georgia. Right now. Check for yourselves👇` Election Data Hub - Turnout | Georgia Secretary of State (http://ga.gov)


@Curiousityfirst - DogAndBone @Curious Cat
Prediction: Full list of States that require an immediate audit. They used the same software for online ballots. Georgia and Arizona used custom-built "crafted" to Brad's and Katie's specs. #Arizona #maricopa @HuttonPulitzer @FannKfann #texas #michigan #Pennsylvania #Nevada https://t.co/BQaYZnEbV7

@Curiousityfirst - DogAndBone @Curious Cat
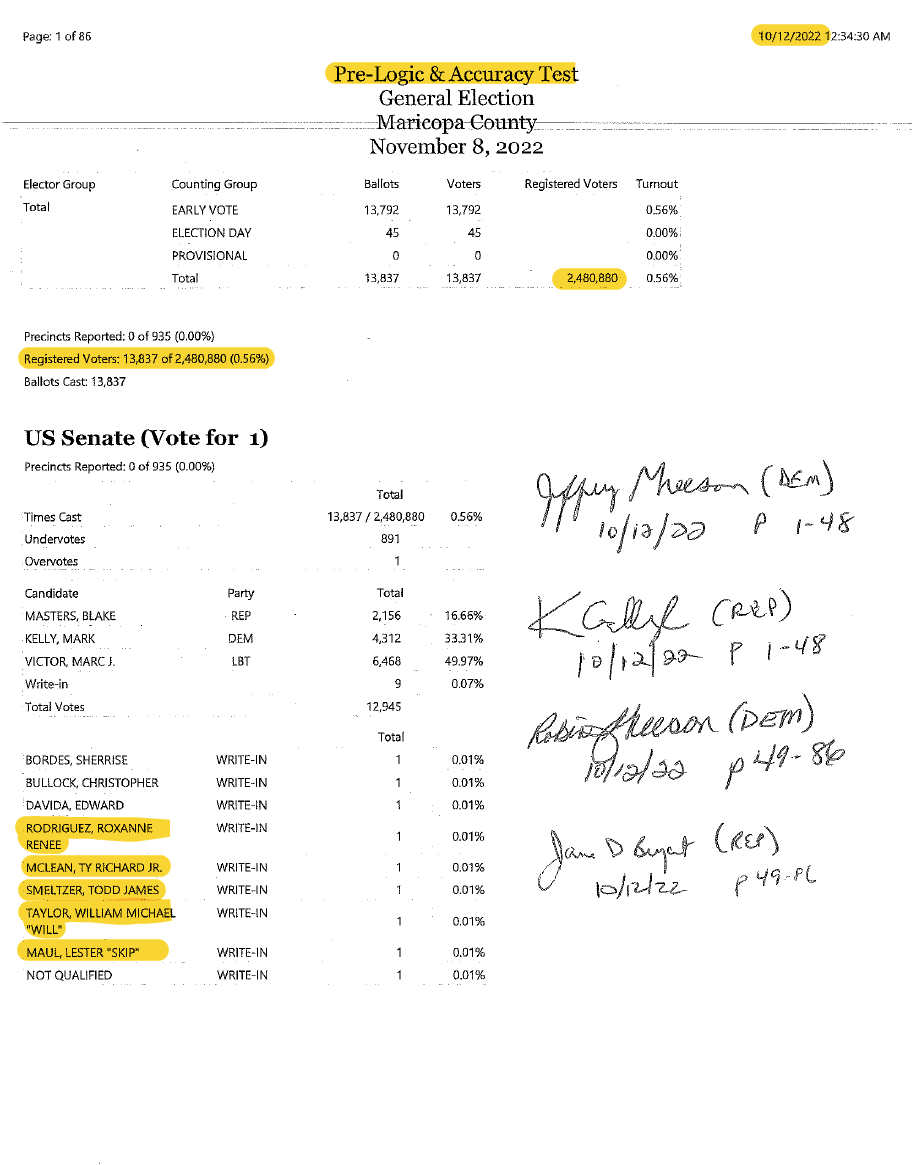
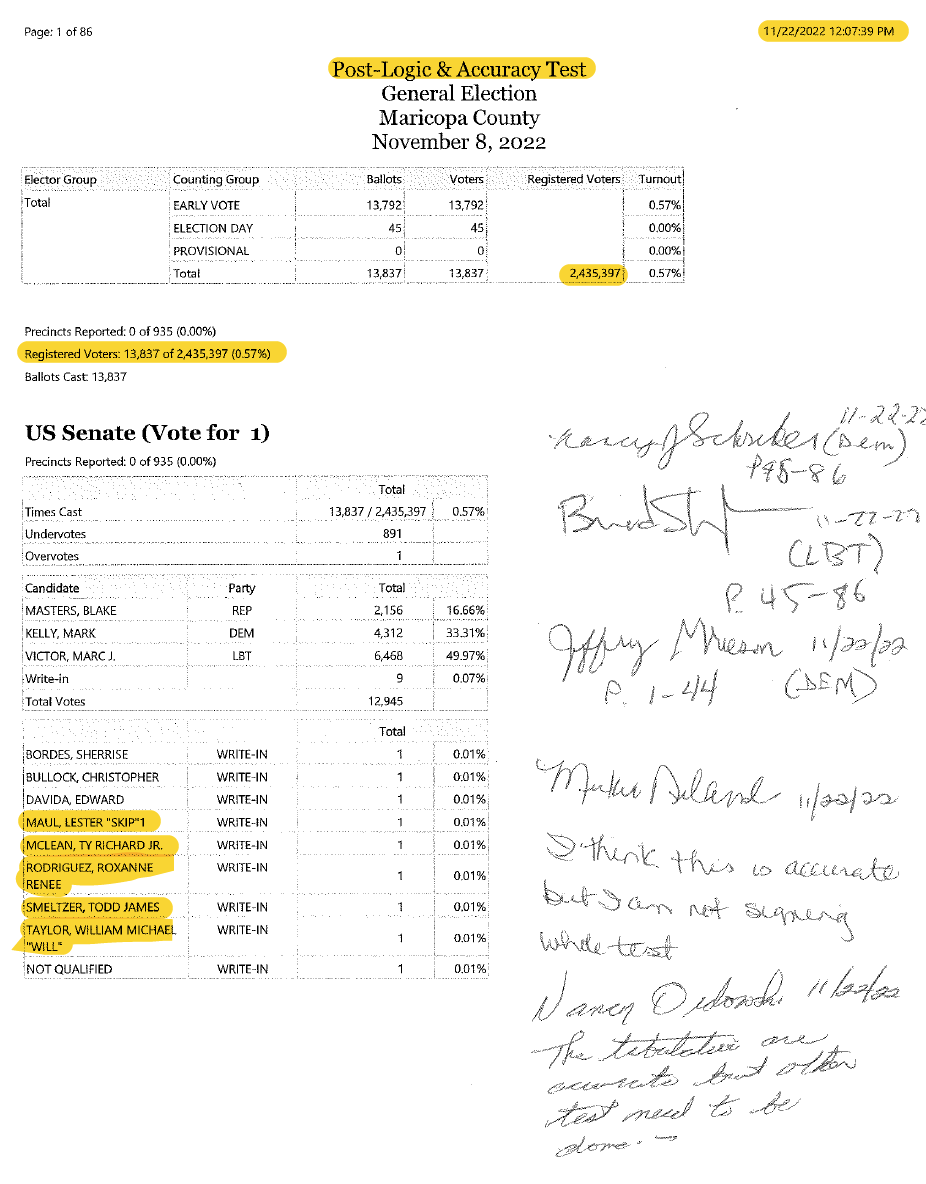
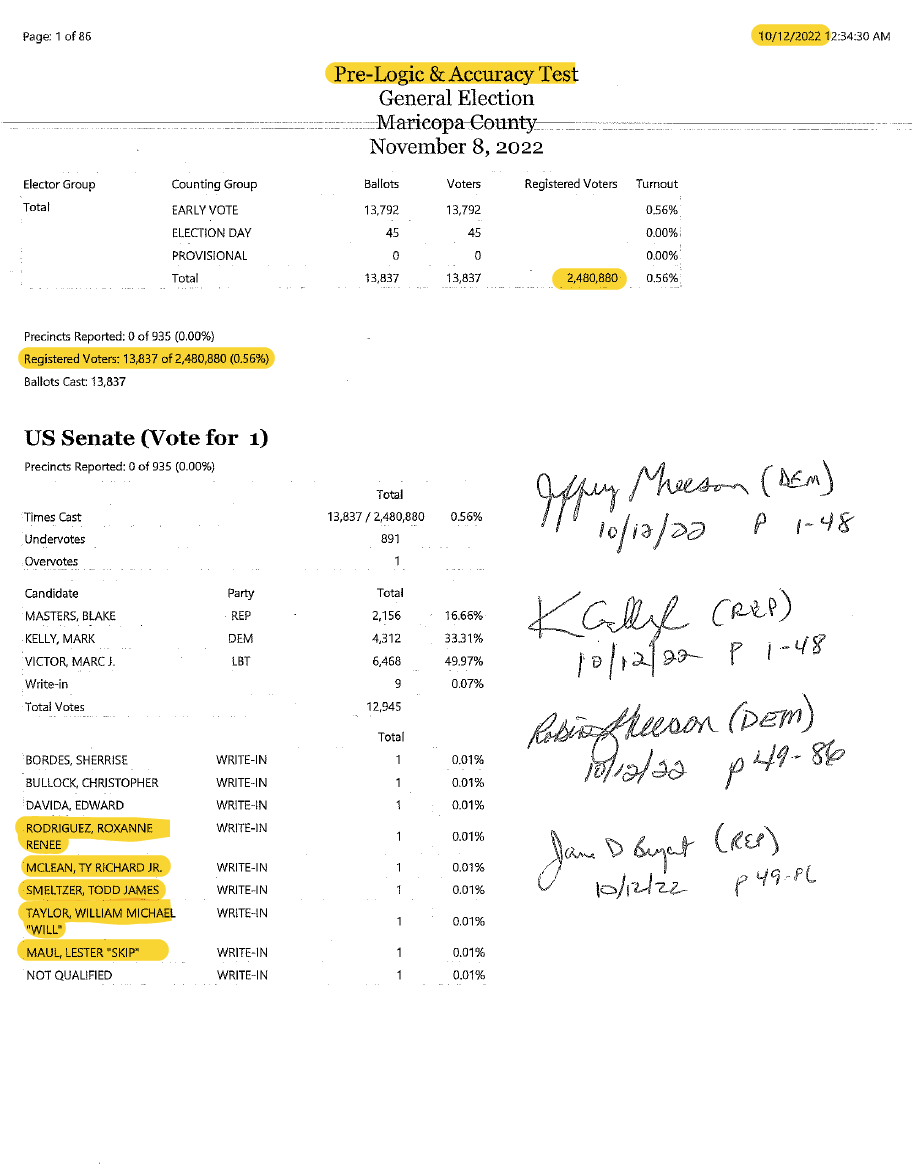
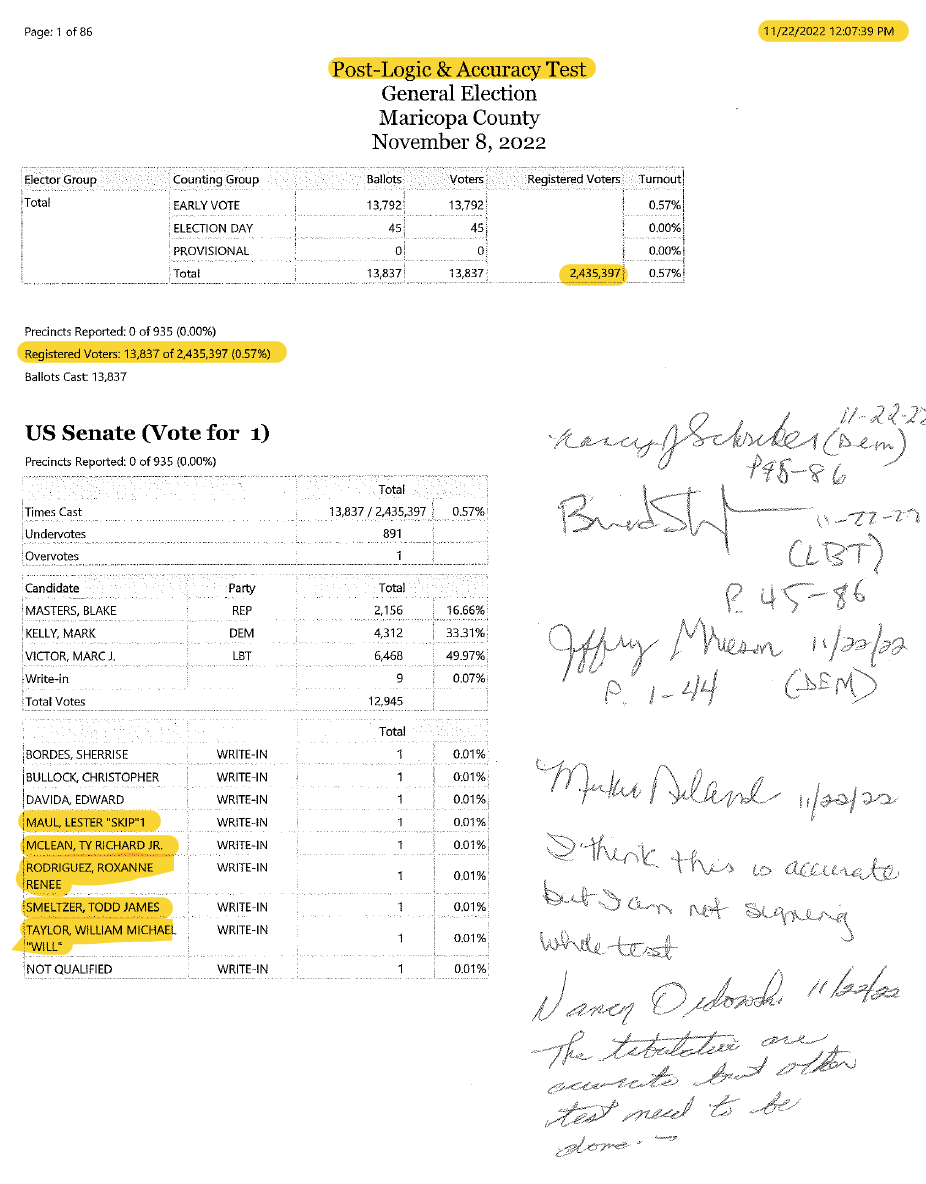
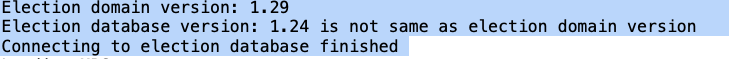
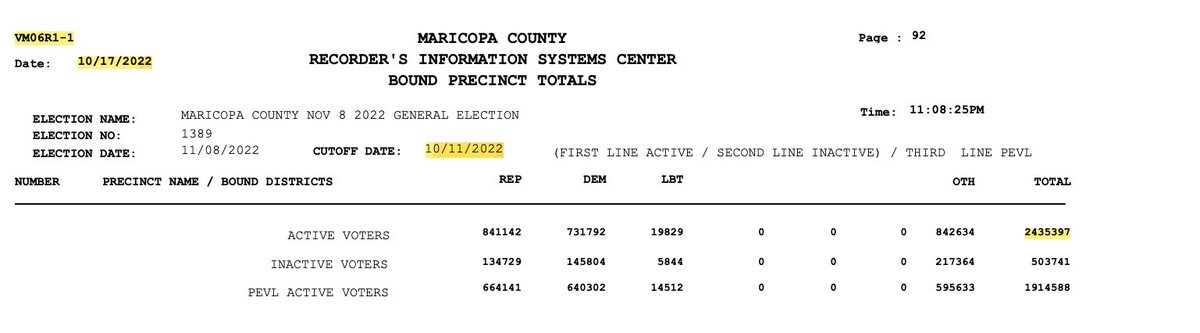
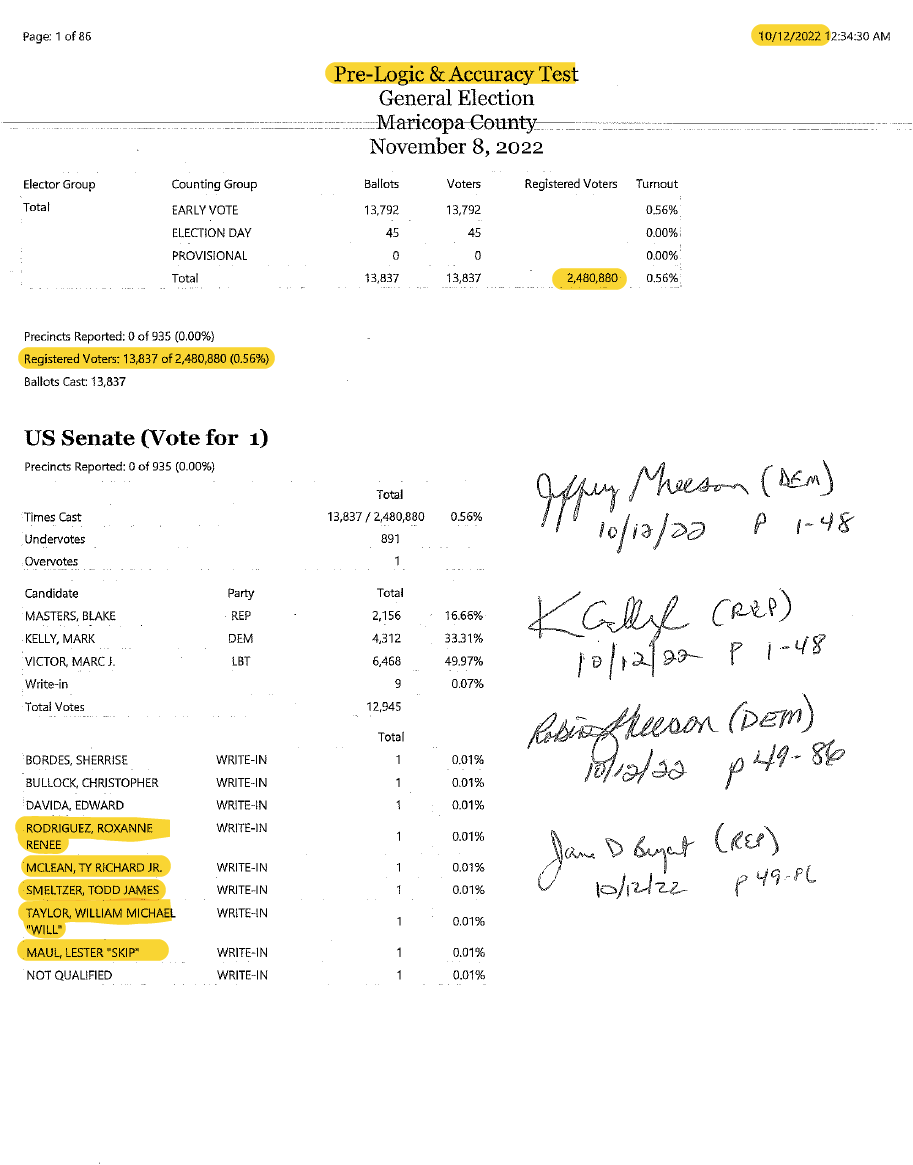
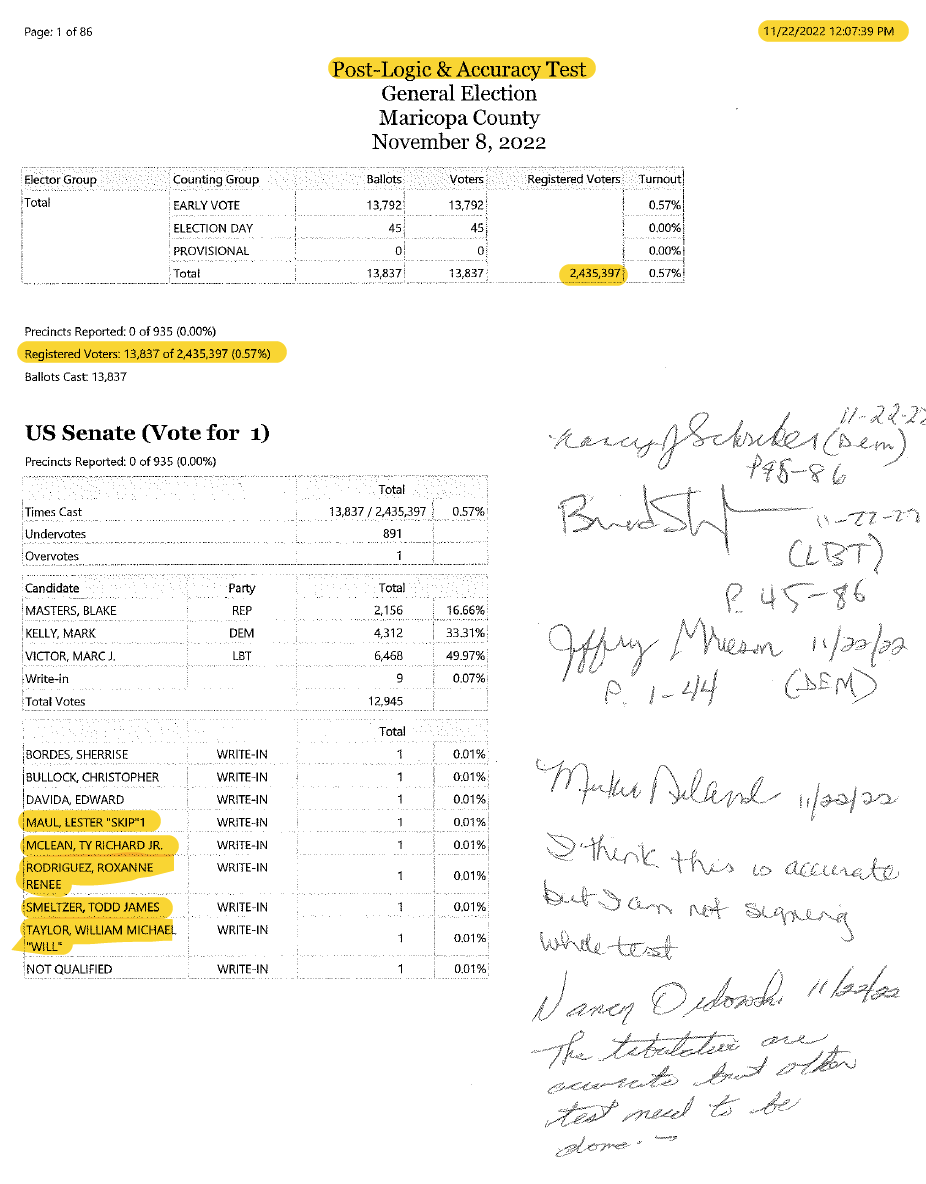
BREAKING: Maricopa County, Arizona General Election 2022 (Part 1) Documents reveal that the Pre L&A Testing and the Post L&A Testing HAVE DIFFERENT DATABASES. A VARIANCE OF 45,483 REGISTERED VOTERS. Screenshot 1: PRE L&A Testing Registered Voters: 2,480,880 Screenshot 2: POST L&A Testing Registered Voters: 2,435,397 Screenshot 3: Slog file Message confirms Election database version: 1.24 is not same as election domain version Further evidence shows that the write-in candidates are out of sequence. Neither Republican Signed the POST test. STAY TUNED: Part 2. The composition of the 45,483 Registered Voters. @KariLake @FannKfann @BarnettforAZ @RealMarkFinchem @ShawnSmith1776 @ParikhClay @mad_liberals @FSociety_1942 @LeadingReport @Rach_IC @DC_Draino @ConradsonJordan @CannConActual @VoterGa @GAballots #arizona @KariLakeWarRoom @AbrahamHamadeh

@Curiousityfirst - DogAndBone @Curious Cat
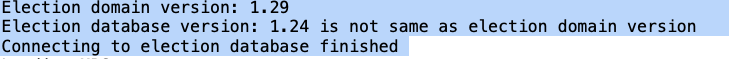
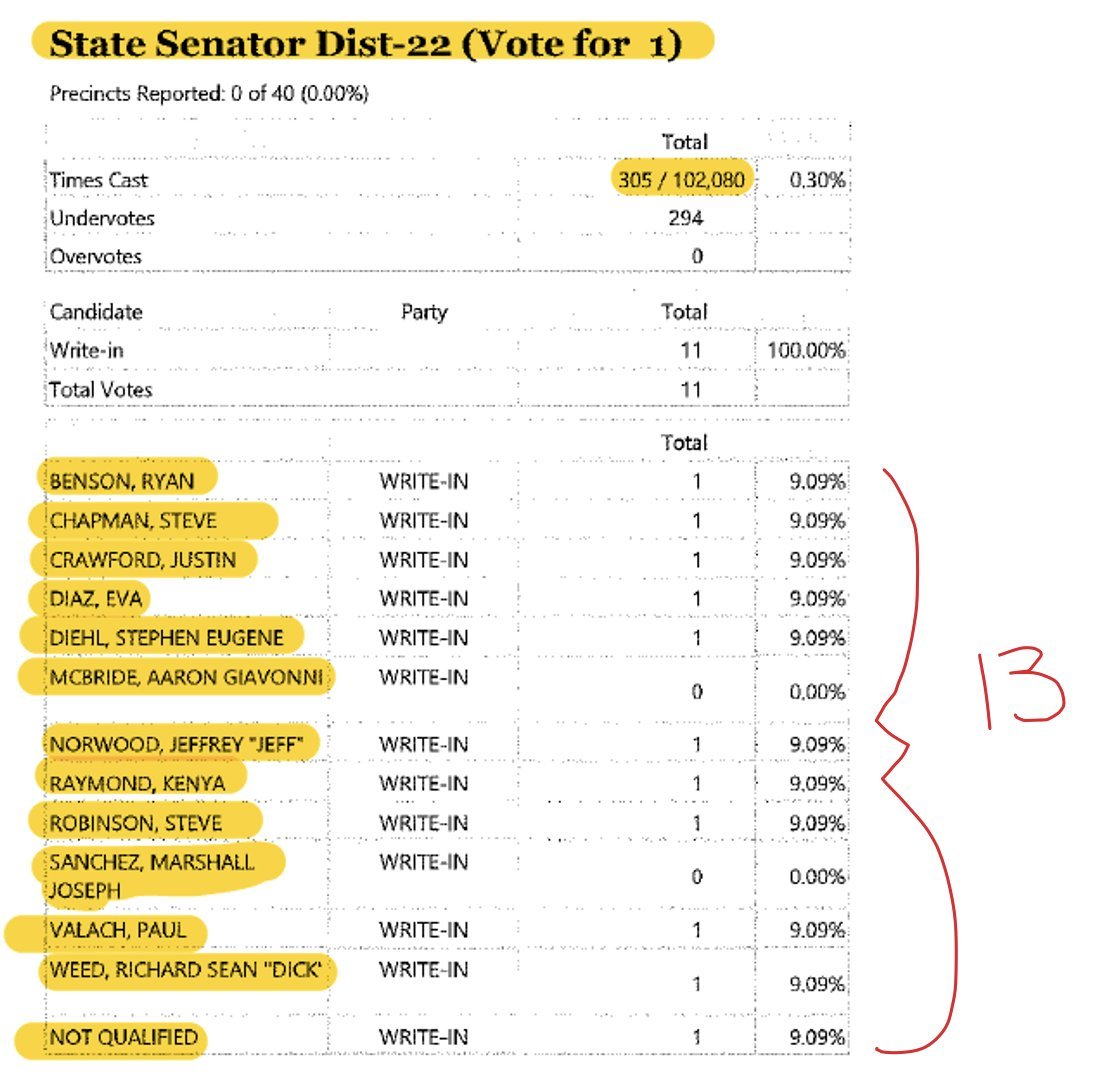
BREAKING: MARICOPA COUNTY, ARIZONA, 2022 GENERAL ELECTION - EVIDENCE SUGGESTS THAT THE ELECTION PROGRAM WAS ALTERED - RT RT RT PRR Documents reveal 2 candidates were ADDED AFTER L&A TESTING DURING THE ELECTION. Please see Pre and Post L&A TESTS.👇 Legislative District 22 - Pre Test had 11 Candidates and Post Test had 13 Candidates. That affects the tabulation of the election results. I firmly believe that with the repositioning of the candidates Steve Robinson should have won this race! Please share - the good people of Maricopa deserve answers. Merry Christmas Everybody!!! @JenWEsq @j3669 @mad_liberals @KariLake @KariLakeWarRoom @AZGOP @TheAndersPaul @FSociety_1942 @AzPinkLady @ShawnSmith1776 @CannConActual @AbrahamHamadeh @MadLiberals @realAlexKolodin @wmahoney5 @Ryan_L_Heath @voterGA @GAballots @WethePeopleAZA1 #Arizona@BlehmLawAZ#arizona @ParikhClay @KariLakeWarRoom @Rach_IC @CannConActual #arizona #Trump #trump2024 @j3669 @mattvanbibber @MAGAIncWarRoom @pjcolbeck @RealMattCouch @TalkMullins @realLizUSA

@Curiousityfirst - DogAndBone @Curious Cat
BREAKING: Maricopa County, Arizona General Election 2022 (Part 1) Documents reveal that the Pre L&A Testing and the Post L&A Testing HAVE DIFFERENT DATABASES. A VARIANCE OF 45,483 REGISTERED VOTERS. Screenshot 1: PRE L&A Testing Registered Voters: 2,480,880 Screenshot 2: POST L&A Testing Registered Voters: 2,435,397 Screenshot 3: Slog file Message confirms Election database version: 1.24 is not same as election domain version Further evidence shows that the write-in candidates are out of sequence. Neither Republican Signed the POST test. STAY TUNED: Part 2. The composition of the 45,483 Registered Voters. @KariLake @FannKfann @BarnettforAZ @RealMarkFinchem @ShawnSmith1776 @ParikhClay @mad_liberals @FSociety_1942 @LeadingReport @Rach_IC @DC_Draino @ConradsonJordan @CannConActual @VoterGa @GAballots #arizona @KariLakeWarRoom @AbrahamHamadeh

@Curiousityfirst - DogAndBone @Curious Cat
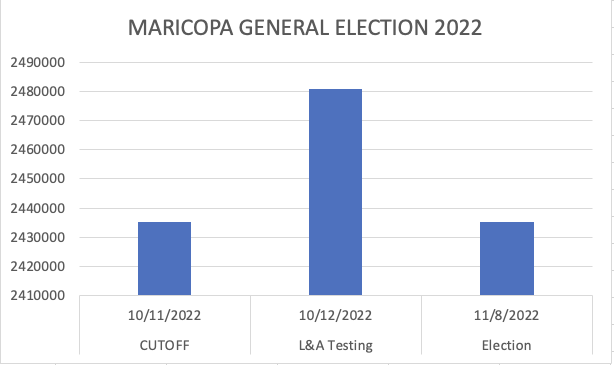
BREAKING: 45K EXTRA REGISTERED VOTERS ADDED OVERNIGHT IN MARICOPA COUNTY, ARIZONA 2022 GENERAL ELECTION then REMOVED THEM DURING AN ELECTION.👇 Cutoff 11th October 2,435,397 L&A Testing 12th October 2,480,880 Election Certification 2,435,397 According to their Maricopa County's own official records. Slide 1: Registered Voters as at the Cutoff 2,435,397 Slide 2: Pre L&A - 2,480,880 (extra 45K) Slide 3: Post L&A - 2,435,397 Slide 4: Chart for visual understanding Any registrations after the cutoff are excluded from the 2022 election. Please retweet and share so that the good people of Maricopa can ask and get the answers they deserve. #Trump @AZGOP #Arizona #Trump2024 #Elections2024 @KariLake @KariLakeWarRoom @BlehmLawAZ @LeadingReport @FSociety_1942 @Rach_IC @Ryan_L_Heath @WendyRogersAZ @Peoples_Pundit @RealAmVoice @realLizUSA @AbrahamHamadeh @TalkMullins @ShawnSmith1776 @pjcolbeck @PatrickByrne @TPPatriots @realAlexKolodin @RealAlexJones #MerryChristmas @ElectionWiz @ArizonaSunTimes @elonmusk @KristenNHammond @JenWEsq @j3669 @RealSKeshel @RealMarkFinchem

@Curiousityfirst - DogAndBone @Curious Cat
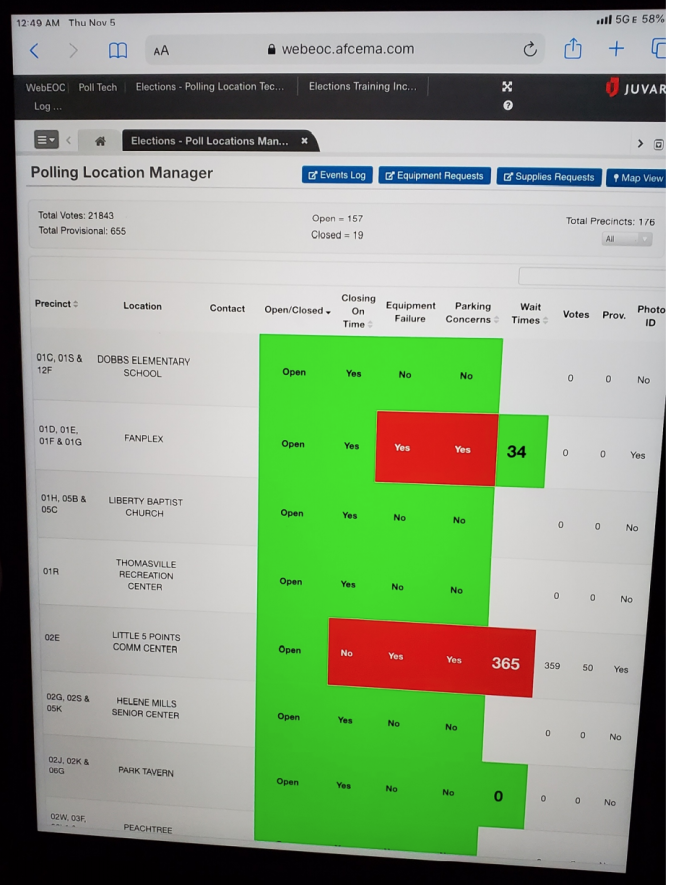
As at 5:00pm Nov 3, 2020 Fulton County's Ralph Jones reported only 14,152 people had voted on election day. The County certified 59,143. Meaning 45,000 voted between 5-7pm. I found evidence that as at Nov 4 at 12:49am 6 hours AFTER had closed this screen capture shows that only 21,843 people, had in fact voted. David Cross @GAballots and I put our heads together to work out the numbers. Here is the video that explains it all👇. It would be a shame if this video went viral. https://rumble.com/vxr5x3-suspected-election-day-fraud-in-fulton-county-november-2020.html @VoterGa @GAballots @hw_floyd #Georgia @Rach_IC

@Curiousityfirst - DogAndBone @Curious Cat
Additionally, this poll pad was from a technician based at State Farm Arena on election day. ##georgia. . @hw_floyd
@Curiousityfirst - DogAndBone @Curious Cat
@hw_floyd All other poll pads were turned in on election day at close of polls @ 7:00pm. Luckily for us, not State Farm Arena where they were still "counting ballots". @hw_floyd

@Curiousityfirst - DogAndBone @Curious Cat
@jhalderm the same guy that found the Dominion vulnerability, wherein instead of stating they breached their contract, he ensured that DOMINION's CVR's were "sanitised" to make it difficult to analyse. @JanuszP20 @noodles @CannConActual @TxSaving https://t.co/AL4uliCgdh