reSee.it - Tweets Saved By @IntCyberDigest

@IntCyberDigest - International Cyber Digest
‼️🇺🇸 Utah is about to become the first US state to legally target VPN use as part of online age verification. The law goes into effect Wednesday, May 6, 2026. 🔴 If you are physically located in Utah, you count as a Utah user, regardless of whether you use a VPN, proxy, or any other tool to disguise your location. Websites are now legally responsible for age-verifying you anyway. 🔴 Sites that handle "material harmful to minors" are banned from sharing instructions on how to use a VPN, or from offering any means to bypass geofencing. The EFF calls this a "liability trap." Websites cannot reliably tell where a VPN user actually is, so the safest legal move is either to block every known VPN IP outright, or to force ID-based age verification on every visitor worldwide. Either path subjects millions of users to invasive identity checks, regardless of where they actually live. The Cato Institute put it bluntly. When a policy can be defeated by a privacy tool millions of people legitimately use, the policy is the problem. The collateral damage is, as always, the people who actually need VPNs: 🔴 Journalists protecting sources 🔴 Domestic abuse survivors hiding from stalkers 🔴 Activists in hostile environments 🔴 Remote workers tunneling into corporate networks 🔴 Travelers banking from abroad 🔴 Anyone who simply does not want their ISP, employer, or data brokers reading their traffic This is not staying in Utah. The UK's Children's Commissioner has called VPNs a "loophole that needs closing." France's Minister Delegate for AI and Digital Affairs has named VPNs as "the next topic on my list." The EU is rolling out age verification across all 27 member states by end of 2026, with EVP Henna Virkkunen openly admitting they have no plan for VPN bypass yet. Utah is leading by example. EFF: "Attacks on VPNs are, at their core, attacks on the tools that enable digital privacy."
@IntCyberDigest - International Cyber Digest
Sources: https://www.eff.org/deeplinks/2026/04/utahs-new-law-regulating-vpns-goes-effect-next-week https://le.utah.gov/~2026/bills/static/SB0073.html
@IntCyberDigest - International Cyber Digest
@Piers_Corbyn This video works hypnotising.
@IntCyberDigest - International Cyber Digest
@2grokornot Yeah. We practically have old tech-illiterate men making policy in the tech era.
@IntCyberDigest - International Cyber Digest
@MagicAlucard Yeah they’re basically taking away a privacy and security layer.

@IntCyberDigest - International Cyber Digest
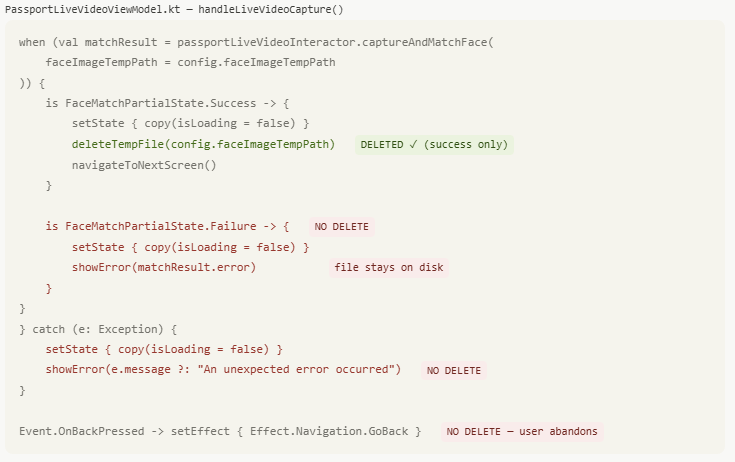
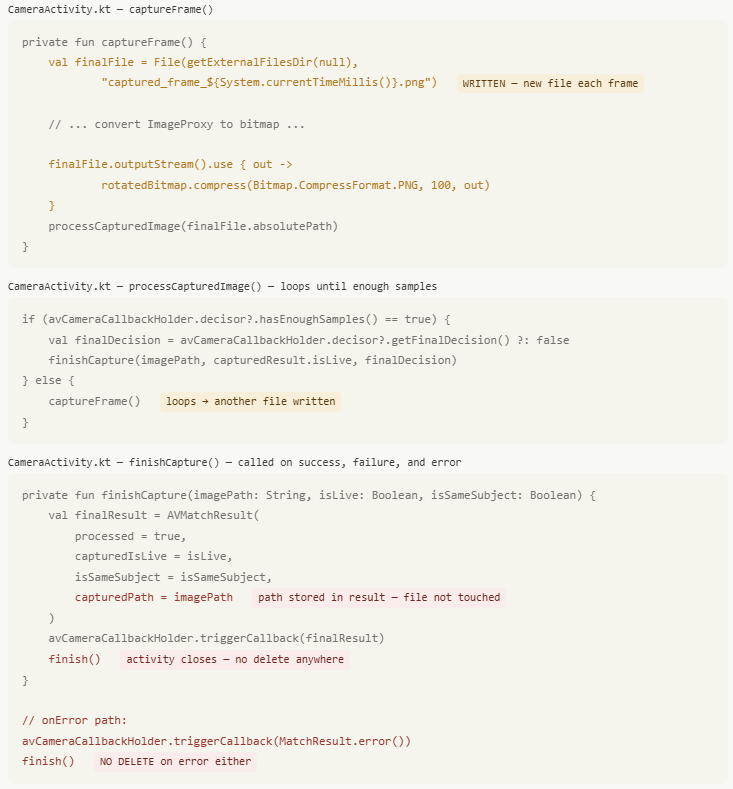
‼️🇪🇺 The EU's new Age Verification app was hacked with little to no effort. When you set it up, the app asks you to create a PIN. But that PIN isn't actually tied to the identity data it's supposed to protect. An attacker can delete a couple of entries from a file on the phone, restart the app, pick a new PIN, and the app happily hands over the original user's verified identity credentials as if nothing happened. It gets worse. The app's "too many attempts" lockout is just a counter in a text file. Reset it to 0 and keep guessing. The biometric check (face/fingerprint) is a simple on/off switch in the same file. Flip it to off and the app skips it entirely.
@IntCyberDigest - International Cyber Digest
Here is a demonstration video of how the 'hack' was performed. https://t.co/GA8oC9tRtn
@IntCyberDigest - International Cyber Digest
Important context: This is not a production EU app that citizens are being asked to install today. It is the official DEMO / DEV reference implementation (white-label blueprint) published at http://ageverification.dev and on GitHub. The project docs are explicit: “This white-label application is a reference implementation … that should be customised before publishing it.” Pre-built APKs and hosted services are for testing and demonstration purposes only. It ships relaxed storage (SharedPreferences for PIN/flags, visible PNGs) deliberately so developers in 27 member states can quickly test flows, debug, and reset state on emulators/devices. That said — fair criticism remains: Even for a reference/demo, the defaults are weaker than they should be (no secure-by-default keystore/Keychain example in the obvious path, no strong tamper detection in the demo build). The European Commission’s public statements (“technically ready … highest privacy standards in the world”) created the misleading impression that this was a finished, hardened product. That was sloppy messaging.
@IntCyberDigest - International Cyber Digest
@deforl I think this won't be included in the final version, it exists for convenience during development.
@IntCyberDigest - International Cyber Digest
@maanvis81 I believe Von Der Leyen said this, cannot confirm the source though "The European #AgeVerification app is technically ready. It respects the highest privacy standards in the world. It's open-source, so anyone can check the code..."

@IntCyberDigest - International Cyber Digest
🚨‼️ BREAKING: FBI Director Kash Patel's Gmail account was hacked by Iranian nation-state hackers. They have published his entire inbox, including mails on his home in India, private life, personal data, business dealings and travel history (Havana, Cuba!). https://t.co/stYtjklOyU
@IntCyberDigest - International Cyber Digest
El Floridita - Hemingway Bar in Havana de Cuba.. this is where Hemingway used to sit and drink daiquiris. https://t.co/LrTTqadNL6
@IntCyberDigest - International Cyber Digest
Confirmed by Reuters btw: https://www.reuters.com/world/us/iran-linked-hackers-claim-breach-of-fbi-directors-personal-email-doj-official-2026-03-27/
@IntCyberDigest - International Cyber Digest
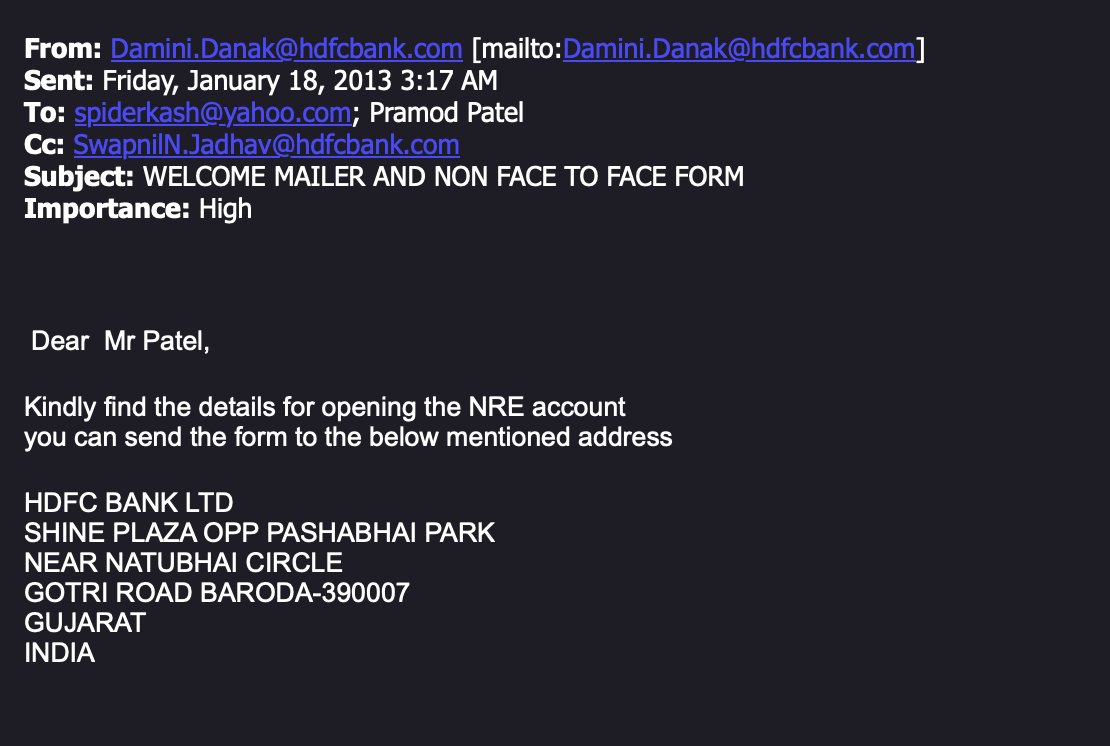
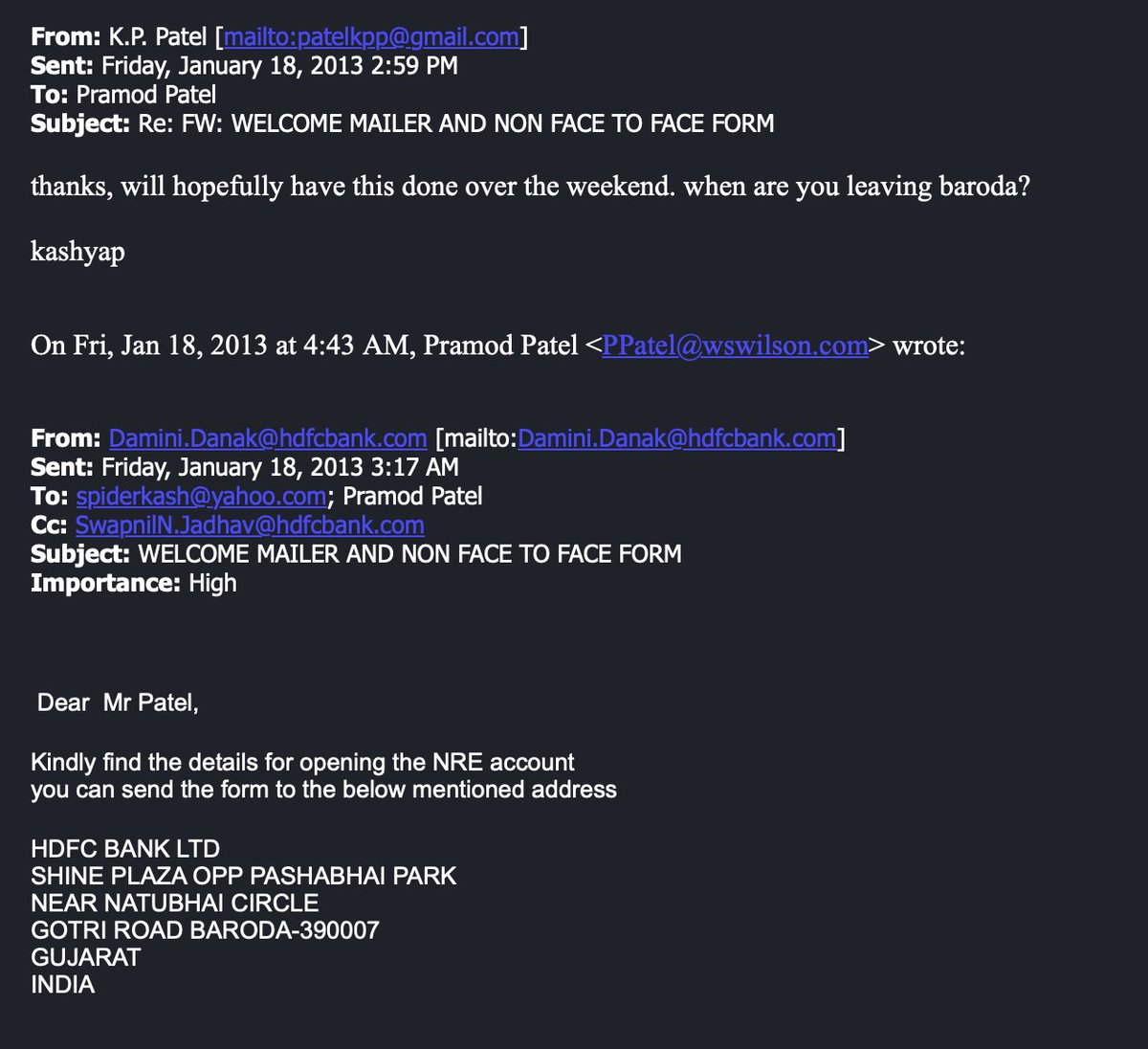
Kash Patel has Indian bank accounts and a home in Baroda, India... And he is the Director of the FBI. https://t.co/yUQDENtTgz
@IntCyberDigest - International Cyber Digest
A reaction to the community note: As you can see Kash Patel writes "thanks, will hopefully have this done over the weekend. when are you leaving baroda?" An NRE (Non-Resident External) account is a bank account for Non-Resident Indians (NRIs). https://t.co/rc8N5LHAtn
@IntCyberDigest - International Cyber Digest
❗️A Justice Department official confirmed to Reuters that Patel's email had been breached and said the material published online appeared authentic. The FBI did not immediately respond to a request for comment. The hackers did not immediately respond to messages.
@IntCyberDigest - International Cyber Digest
Follow us on X @IntCyberDigest And join our Telegram channel for exclusive content: https://t.me/IntCyberDigest
@IntCyberDigest - International Cyber Digest
@notbrvnd0n Not looking good! This is the FBI director....
@IntCyberDigest - International Cyber Digest
@JimDand49783668 See what?
@IntCyberDigest - International Cyber Digest
@CptKraiklyn No nudes ;-) There's a lot more to be seen within the mails..

@IntCyberDigest - International Cyber Digest
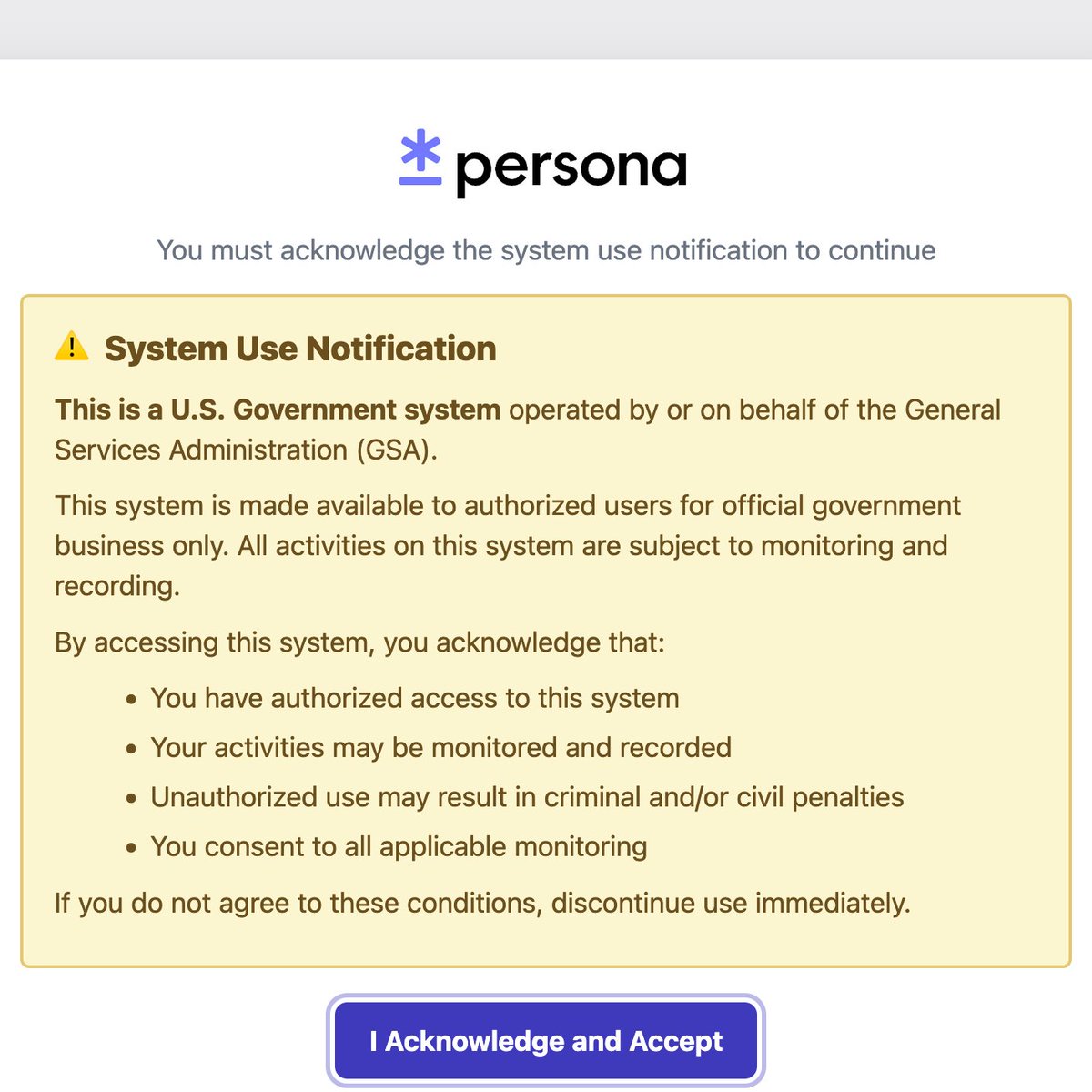
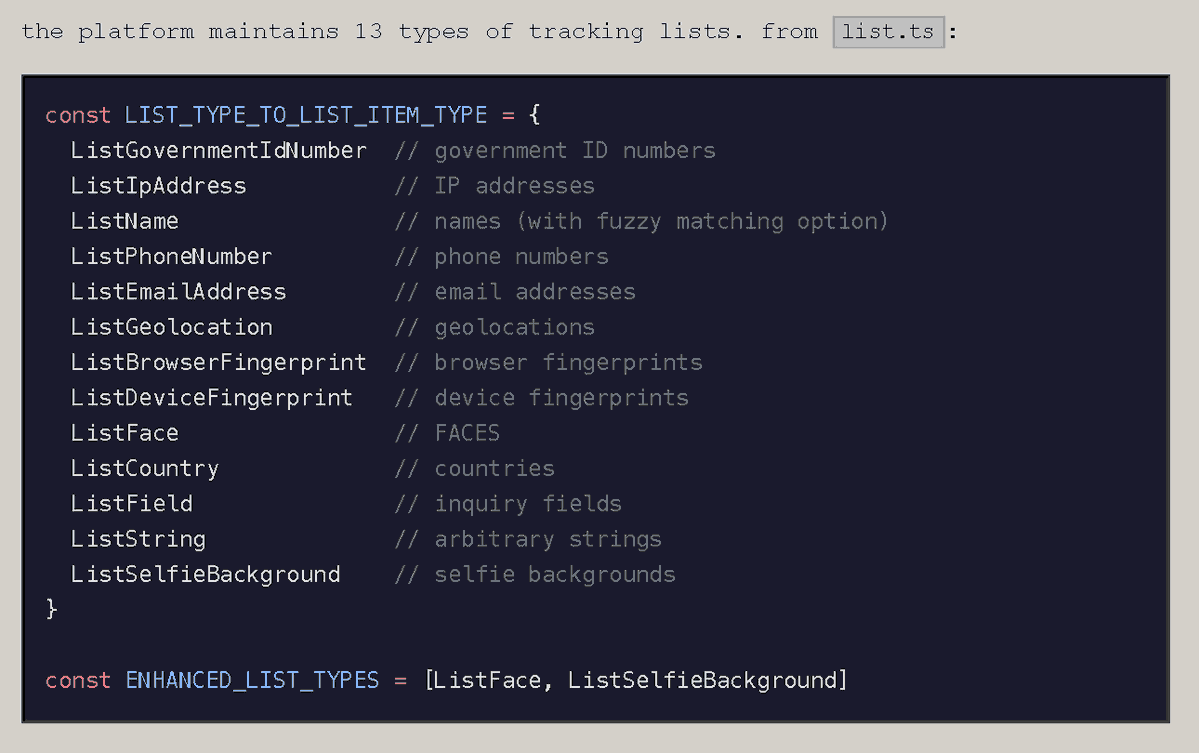
‼️ BREAKING: Researchers have uncovered secret AI surveillance projects linked to KYC provider Persona and OpenAI, sending user data to the US government. Code references include intelligence program codenames "Project SHADOW" and "Project LEGION." Analysis of source code revealed OpenAI's user verification systems includes biometric tracking, facial scanning, political screening, and intelligence reporting. Researchers also discovered ONYX on Persona's government server — matching ICE's $4.2M AI surveillance tool — which scrapes social media and the dark web, builds digital footprints, tracks emotional sentiment, assigns risk scores across 300+ platforms and 28B+ data points, and flags individuals for "violent tendencies." None of it was hidden. It was all internet-facing.
@IntCyberDigest - International Cyber Digest
Here is a list of some of Persona's customers: - OpenAI (ChatGPT) - Discord - LinkedIn - DoorDash - Etsy - Brex - Coursera - Carahsoft - Swan Bitcoin - Mercury - Wealthsimple - Branch - WeTravel - Grailed - Eaze - Stifel Financial Corp - First Republic - Fire & Flower Holdings - Serviap Global
@IntCyberDigest - International Cyber Digest
The researchers writeup can be found here: https://vmfunc.re/blog/persona
@IntCyberDigest - International Cyber Digest
@ambmojo Did you read the writeup? It's worse than that. This is surveillance with AI components, checking everything about you, including your face, and trying to match it to politicians just because you want to use a chatbot.

@IntCyberDigest - International Cyber Digest
‼️ Unremovable Israeli Spyware Found on Samsung Devices Samsung faces backlash over AppCloud, an Israeli-developed app pre-installed on budget Galaxy A and M series devices. Investigations reveal the app is embedded in the operating system, preventing full removal. Even when disabled, AppCloud remains on the device, reappears after updates, and can covertly install additional software.
@IntCyberDigest - International Cyber Digest
Sources: https://smex.org/open-letter-to-samsung-end-forced-israeli-app-installations-in-the-wana-region/ https://smex.org/invasive-israeli-software-is-harvesting-data-from-samsung-users-in-wana/ https://www.businesswire.com/news/home/20221103005106/en/ironSource-Expands-Samsung-Partnership-Launching-on-Samsung-Mobile-Devices-in-MENA

In recent months, we have received numerous reports from users across West Asia and North Africa (WANA) expressing alarm over…
smex.org
Across West Asia and North Africa (WANA), growing concerns about digital surveillance have placed Israeli cybersecurity firms and their software…
smex.org
@IntCyberDigest - International Cyber Digest
❗ A researcher reverse-engineered X Chat's cryptographic design and found serious flaws. Elon claimed that even with a gun to his head, he couldn’t read X Chat messages due to their “full encryption.” Turns out this is untrue. 📚 https://david.nepozitek.cz/blog/can-elon-musk-read-your-x-chat-messages#appendix-how-the-current-x-chat-protocol-works


@IntCyberDigest - International Cyber Digest
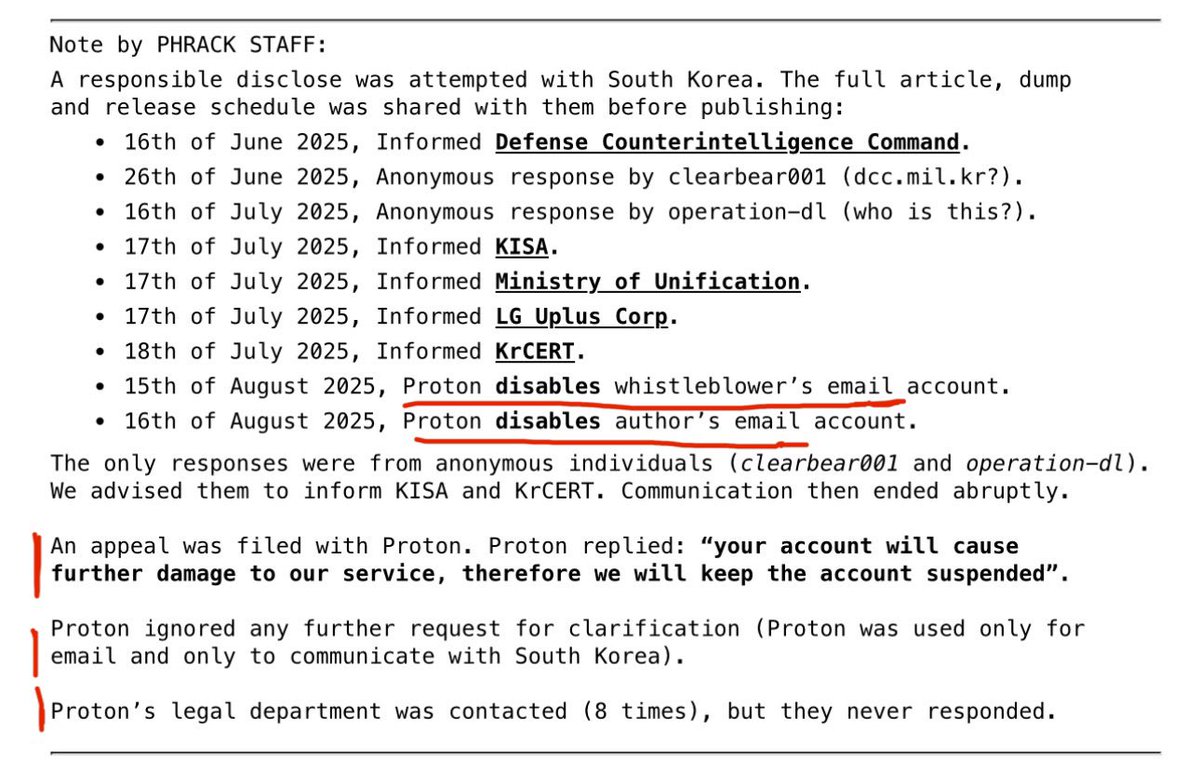
‼️ Proton is cancelling journalists by blocking their mail accounts. This has huge consequences for their reputation and for all the people who thought they were safe by avoiding big tech. https://t.co/wvJOCeOZvG
@IntCyberDigest - International Cyber Digest
Little did they know, we all read @phrack zine. @ProtonMail care to comment? https://t.co/ELGQVOwxfx
@IntCyberDigest - International Cyber Digest
Let's not forget when @ProtonPrivacy shared the IP address of a French activist with authorities. The company has widely claimed that it doesn't log users' IP addresses. Weird, huh? https://t.co/gWZ3gpR8Bq
@IntCyberDigest - International Cyber Digest
Care to comment @andyyen?