reSee.it - Tweets Saved By @RebelValkyrie17

@RebelValkyrie17 - ©.
Why aren’t the big “influencers” talking about this? He was trying to tell us. He was killed for it. They claim to loveeee Kappy but will never share his videos. Why? Because he talks about THEM in his videos. https://t.co/Rg6sQh3A1J
@RebelValkyrie17 - ©.
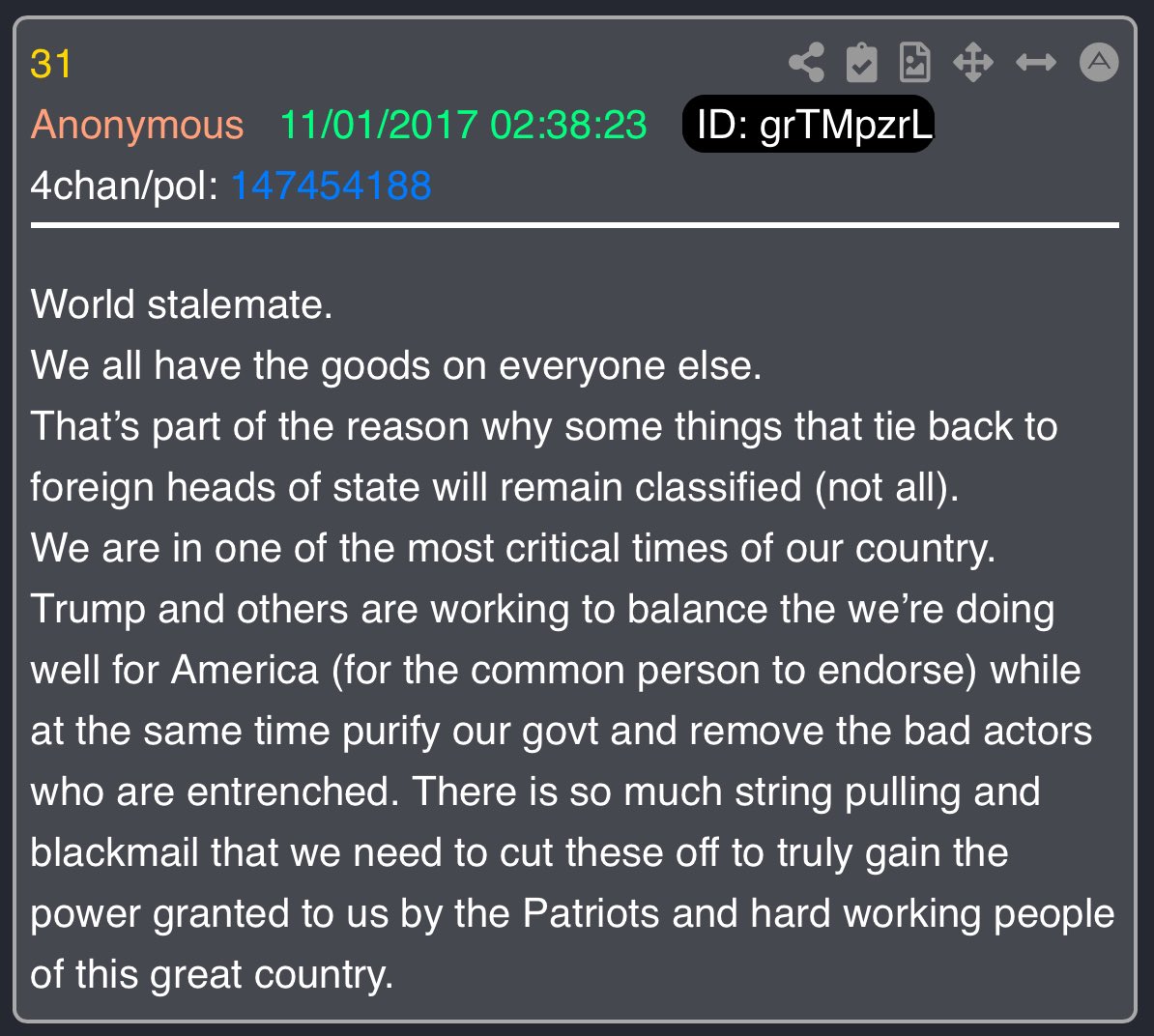
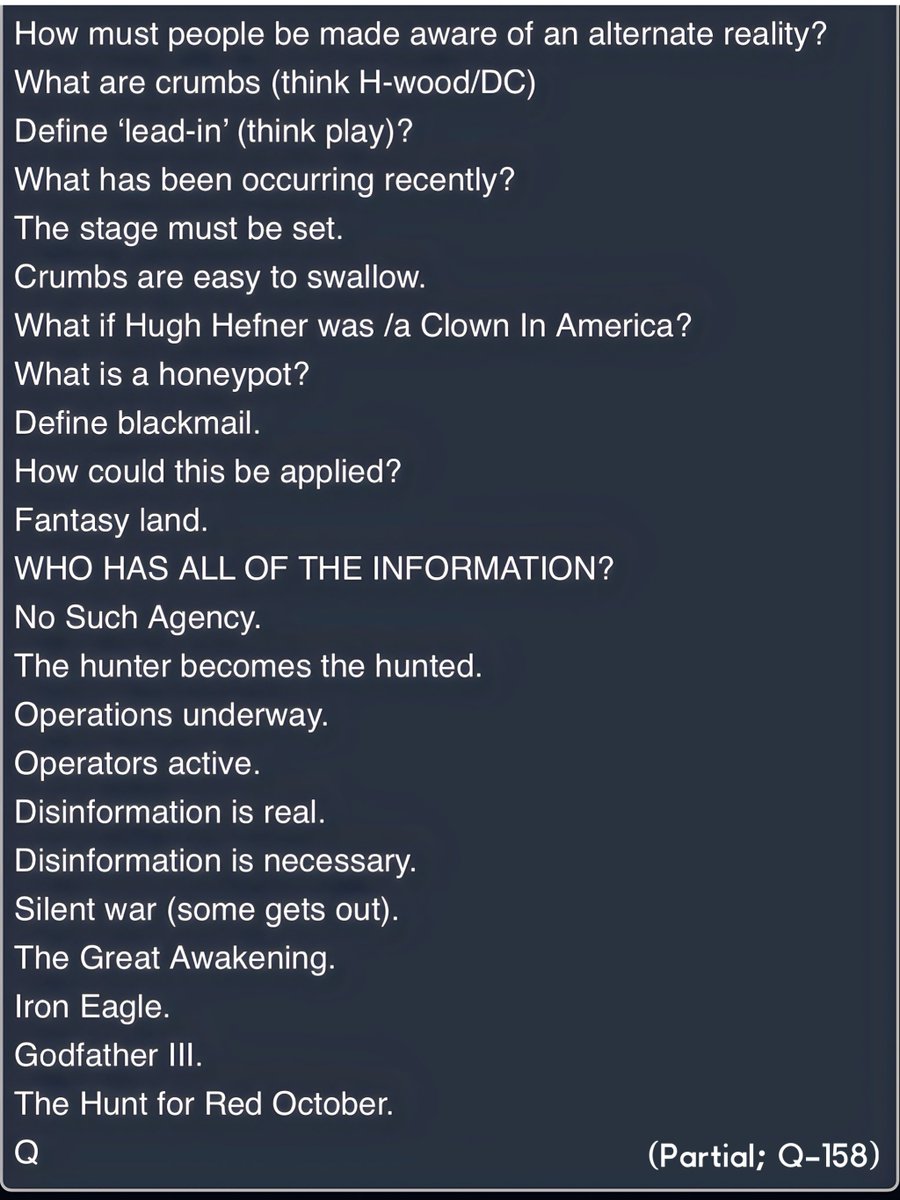
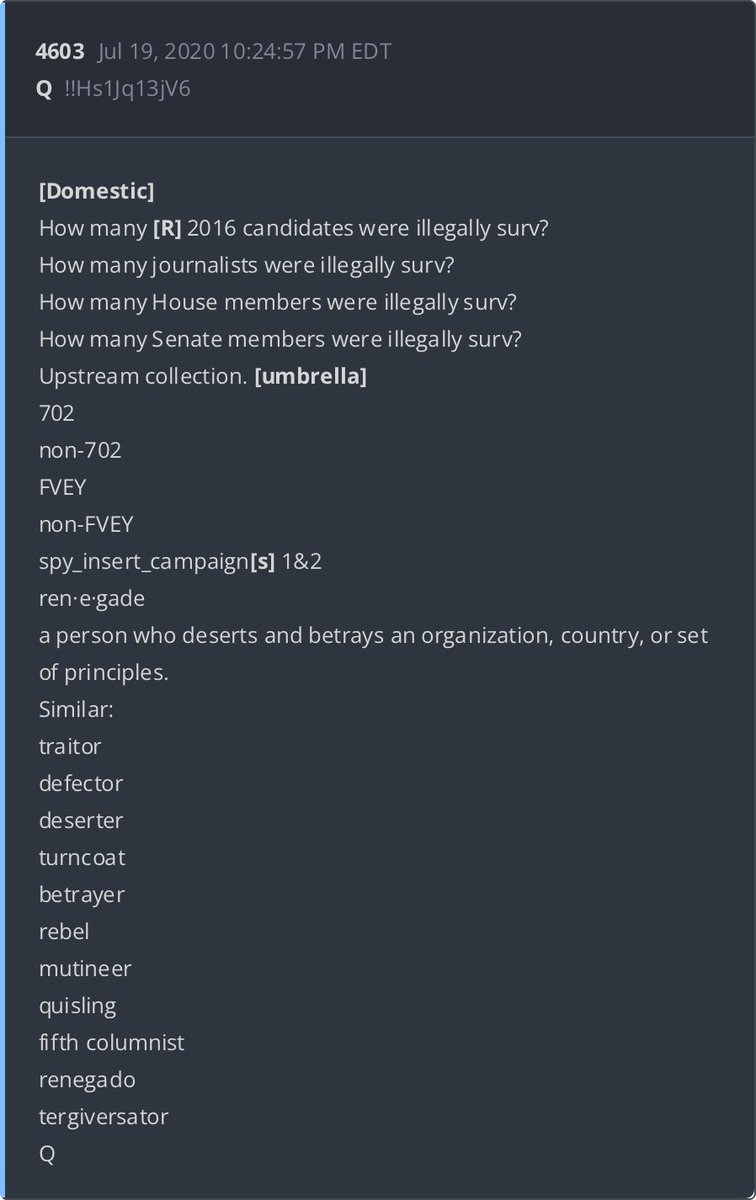
Shall we play a game? Find the spider(s) and build the web (the ‘map’). Remember, they consider you to be the fly (specifically, the ‘feeder’). Remember, they never thought she was going to lose. Therefore, they never thought investigations and/or public interest into their criminal acts would be exposed/investigated. Therefore, they never thought they had anything to fear. Therefore, they openly showcase their symbolism. Therefore, they were sloppy. Hussein’s last speech in Chicago re: ‘scandal free’. Why did he continually emphasize that phrase? As a backup, they infiltrated and control the narrative. As a backup, they install only those on the team. As a backup, they blackmail those that aren’t. —>As a backup, they defined ‘conspiracy’ as crazy/mentally unstable and label anything ‘true’ as such. This works given most of what they engage in is pure evil and simply unbelievable (hard to swallow). The ‘fix’ has always been in – no matter which party won the election (-JFK (killed)/Reagan(shot)). This was always the promise made to those who played the game (willingly or otherwise) (i.e., they would never lose power). Power of the (3) letter agencies. —>Power over the US Military (WW dominance to push against other nations and install like-kind). These people are really stupid. Follow the husbands. Another Hint: Ian Cameron McKinsey & Company Clowns In America. Dr. Emmett J. Rice. Federal Reserve. Everyone is connected. How about a nice game of chess? Q
@RebelValkyrie17 - ©.
Imagine THIS. Raw intel collection. Narrative FEEDER. Narrative COLLECTORS. Narrative DISTRIBUTORS. LEAKS. CLASSIFIED. PAYMENTS. FOREIGN ACCOUNTS. CASH. SPOOK FILES. HOTELS. BLACKMAIL. How do you retain 'Freedom of the Press' if those in front of the camera [trusted by select viewers] are extensions of the ARM? Freedom of the Press is VITAL to retain. TRUST THE PLAN. THERE ARE A LOT MORE GOOD THAN BAD. You, THE PEOPLE, need to remember how TO PLAY. You, THE PEOPLE, have the POWER. We STRIKE every SINGLE DAY. We WIN every SINGLE DAY. EVERY SINGLE DAY THEY ARE BEING DESTROYED - LITERALLY. STAY STRONG. HAVE FAITH. THIS IS BIGGER THAN ANYONE CAN IMAGINE. Q
@RebelValkyrie17 - ©.
What happens when those who held positions of POWER (& INFLUENCE) no longer pull the strings? What happens when 'BLACKMAIL' no longer works? Do you become a LIABILITY? (H)> C, D, I Q
@RebelValkyrie17 - ©.
What happens when state actor(s) [assets] are removed? How does a state actor gain leverage over a person in power [re: blackmail]? Define 'Traitor'. Data exchange(s) can be very dangerous. Q

@RebelValkyrie17 - ©.
#ArrestRayEpps

@RebelValkyrie17 - ©.
I continue to get porn bots on this. Apparently they don’t like this.

@RebelValkyrie17 - ©.
This is a must listen of Bill Cooper! Thank you @stormready17 https://t.co/eC5pgCu619

@RebelValkyrie17 - ©.
Holy shit!! Is Roger Stone responsible for assassinations? https://t.co/cJ9SqDQCFT

@RebelValkyrie17 - ©.
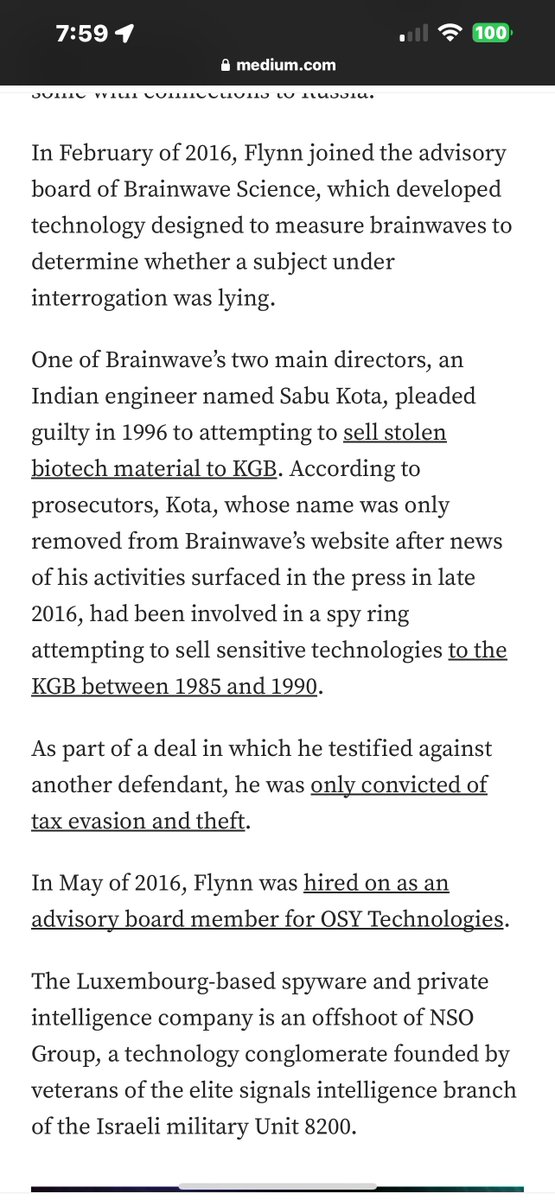
Cambridge Analytica, a company connected to Michael Flynn and Black Cube (MOSSAD backed intel company), was created by Aleksandr Kogan - professor, Cambridge University Psycho Centre. Cambridge University's Psychometrics Centre has been preforming psyops on the world for many years. Back in 2007, David Stilwell (funded by Intel agencies) created what is now called “Operation KitKat”. “[David Stilwell] had devised various apps for Facebook, one of which, a personality quiz called myPersonality, had gone viral. Users were scored on "big five" personality traits - Openness, Conscientiousness, Extroversion, Agreeableness and Neuroticism - and in exchange, 40% of them consented to give him access to their Facebook profiles. —->Suddenly, there was a way of measuring personality traits across the population and correlating scores against Facebook "likes" across millions of people.”
@RebelValkyrie17 - ©.
This research, which involved building the groundwork for the future psyops to be preformed on the American people (and the world), quickly caught the eyes of the US defense and military establishment. Boeing was the main source of funding and support of Michal Kosinski’s projects. “Boeing, a major US defence contractor, funded Kosinski's PhD and Darpa, the US government's secretive Defense Advanced Research Projects Agency, is cited in at least two academic papers supporting Kosinski's work.”
@RebelValkyrie17 - ©.
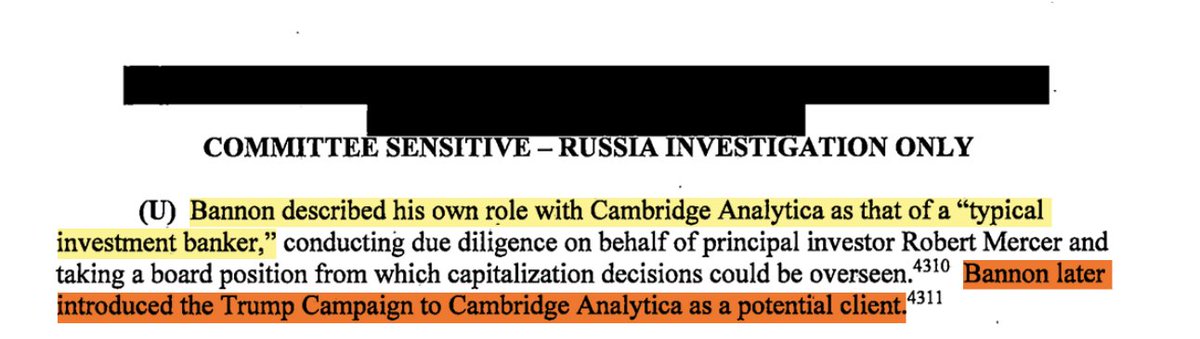
Steve Bannon, the “typical investment banker” involved with Cambridge Analytica, tried to convince Trump to take on Cambridge Analytica as a client.
@RebelValkyrie17 - ©.
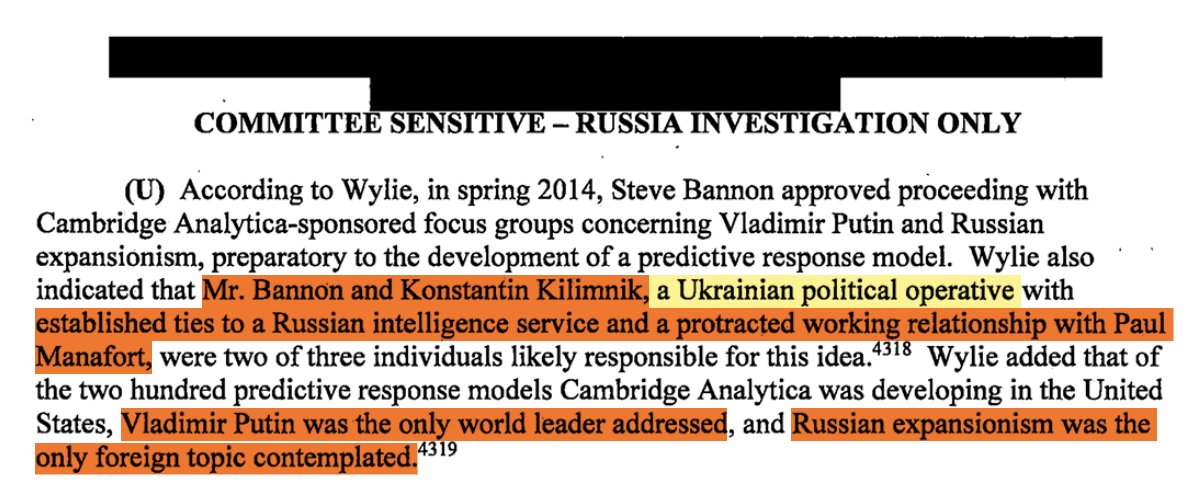
To prepare the development of a predictive response model, Bannon along with Ukrainian and Russian political/intel operative Konstantin Kilimnik developed a working relationship with Paul Manafort. The main target of Cambridge Analytica’s predictive response model was Vladimir Putin.
@RebelValkyrie17 - ©.
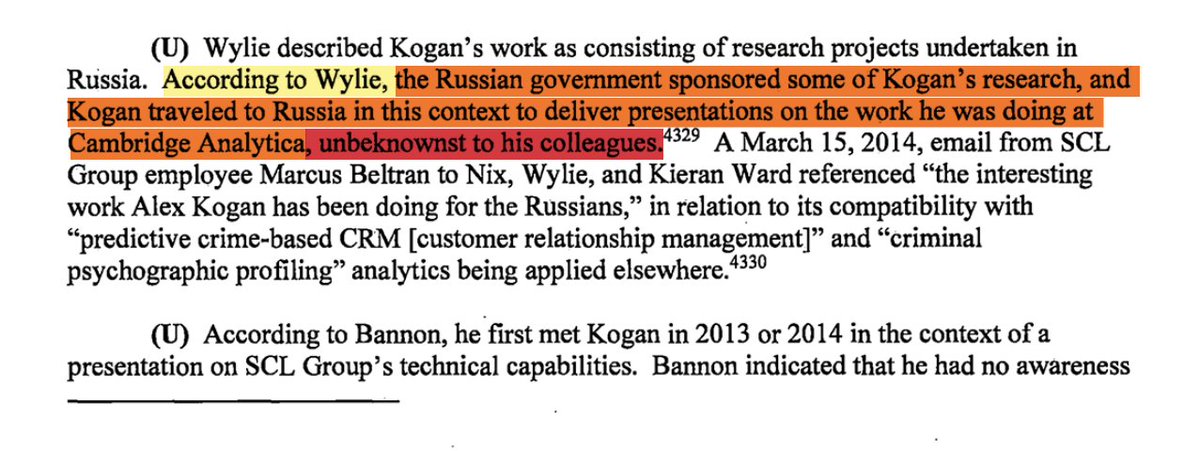
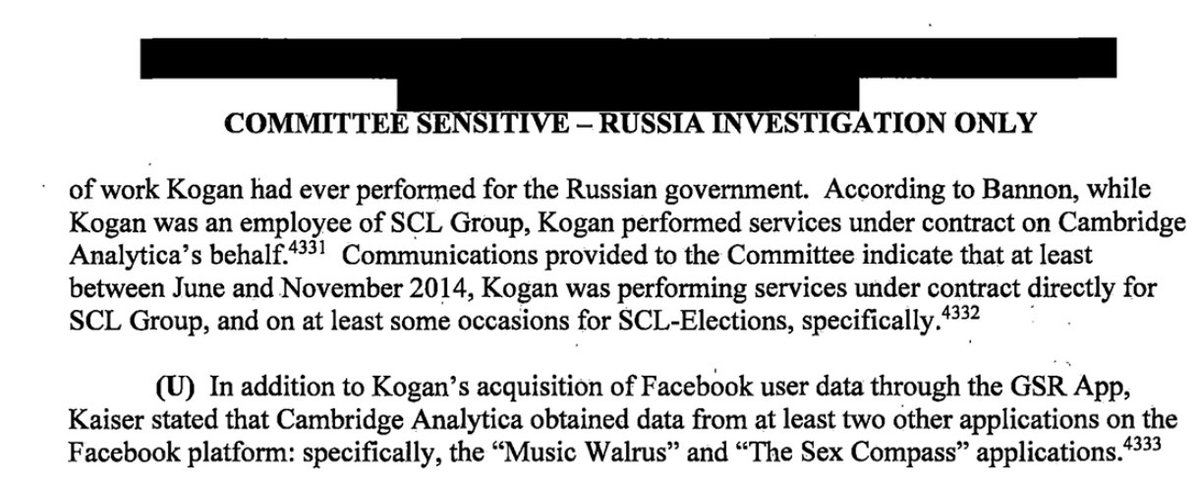
Unbeknownst to his colleagues, the founder of Cambridge Analytica - Aleksandr Kogan traveled to Russia to give presentations and collect funding from the Russian government. Bannon says that Kogan performed services under contract on Cambridge Analytica's behalf, without his knowledge. Cambridge Analytica created at least two other apps to collect psychological data from Facebook users, the "Music Walrus" and "The Sex Compass" applications.
@RebelValkyrie17 - ©.
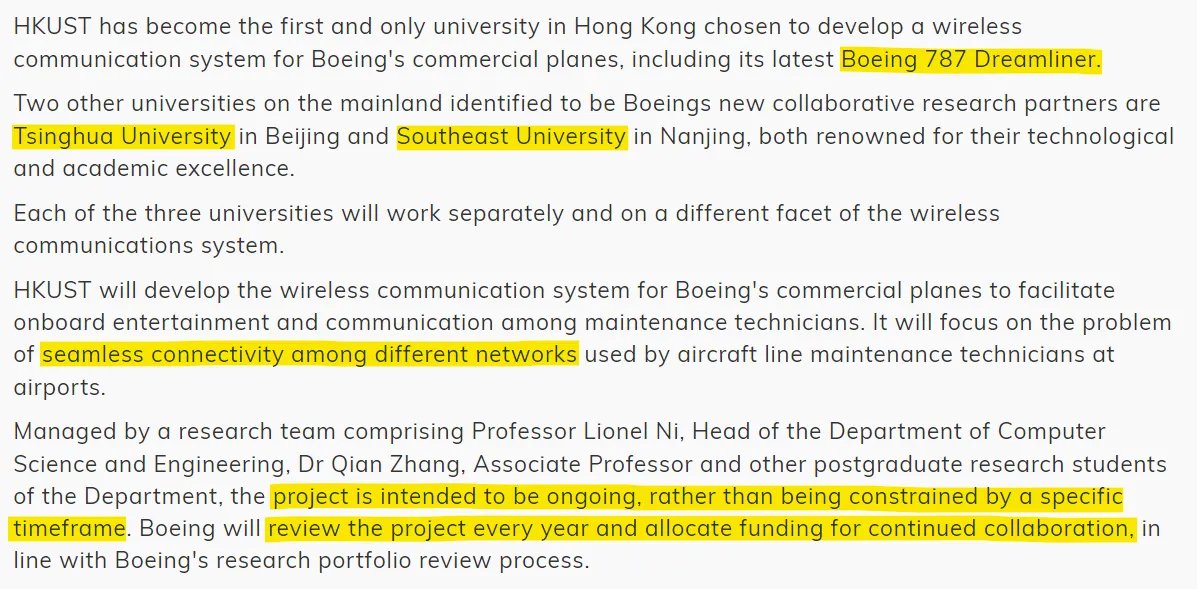
Lionel Ni, of Michigan State University and Tsinghua University (among other universities), was another Boeing funded talent worker. Lionel Ni managed projects to create wireless communication systems that have seamless connectivity. This project is intended to be ongoing.
@RebelValkyrie17 - ©.
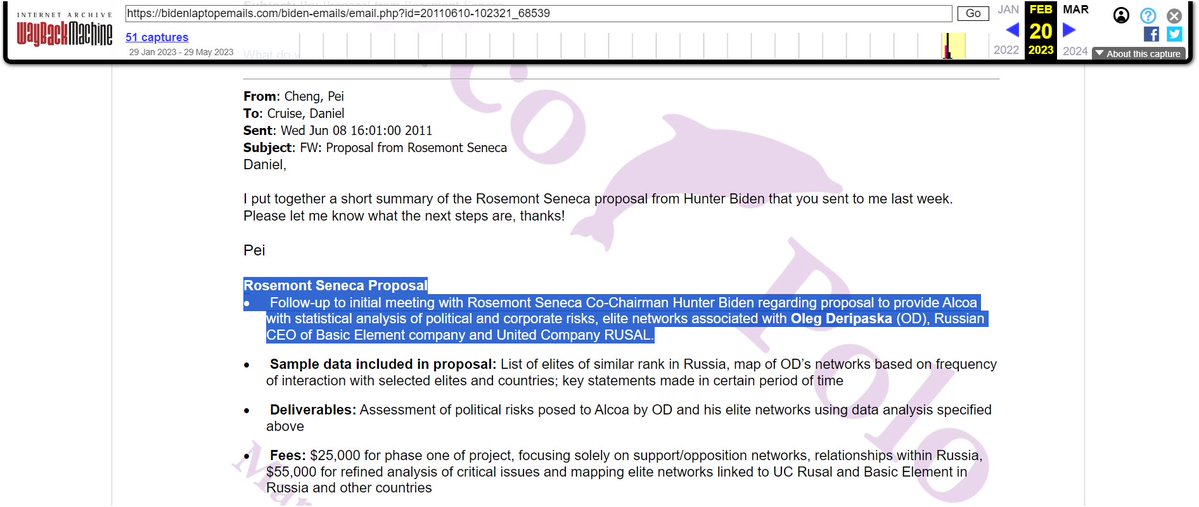
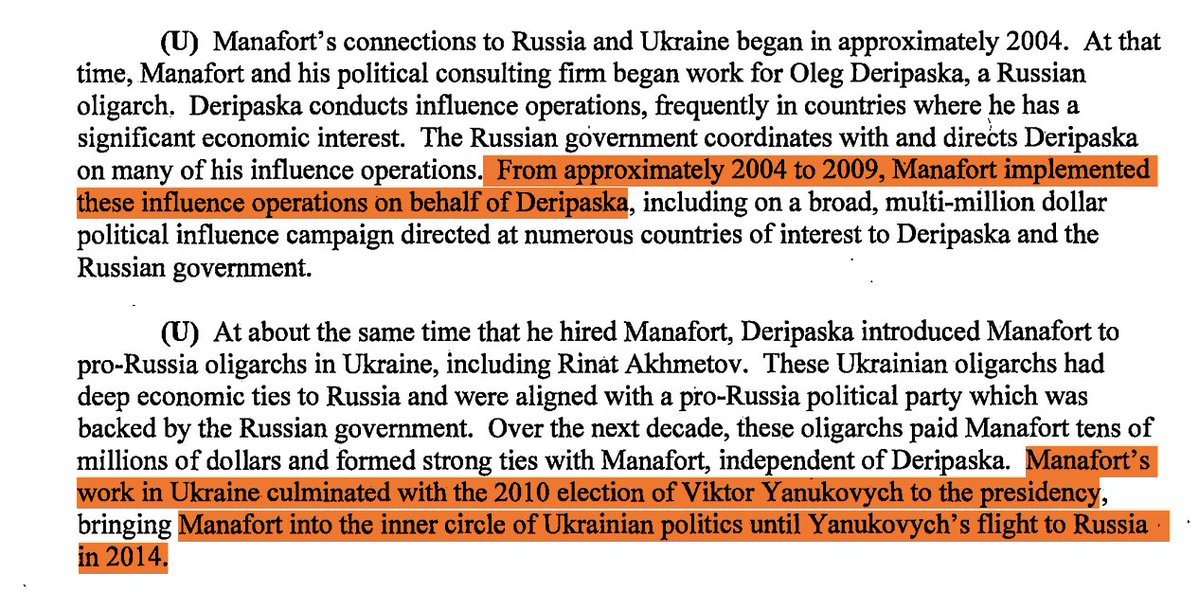
In 2011, another CEFC affiliate - Rosemont Seneca, Co-Chairman - Hunter Biden proposed to provide a company called Alcoa with statistical analysis of political and corporate risks, elite networks associated with Oleg Deripaska (Russian CEO of Basic Element company and United Company RUSAL). Deripaska is responsible for many major influence operations, often tied to his economic interests, with coordination from the Russian government. Between 2004 and 2009, Paul Manafort executed these operations on Deripaska's behalf, involving a multi-million dollar campaign across various countries. Simultaneously, Deripaska introduced Manafort to pro-Russia oligarchs in Ukraine, leading to lucrative ties and Manafort's involvement in Ukrainian politics until 2014.

@RebelValkyrie17 - ©.
Emoluments Clause, U.S. Const. art. I, § 9, cl. 8. “No Person holding any Office of Profit or Trust under [the United States], shall, without the Consent of the Congress, accept of any present, Emolument, Office, or Title, of any kind whatever, from any King, Prince, or foreign State.” ** Emolument: "profit," "advantage," "benefit," and/or "comfort." https://www.theusconstitution.org/wp-content/uploads/2018/01/The-Text-and-History-of-the-Foreign-Emoluments-Clause.pdf


@RebelValkyrie17 - ©.
🧵MGshow Reading CTIL files @shadygrooove @intheMatrixxx 1/
@RebelValkyrie17 - ©.
2/ https://x.com/RebelValkyrie17/status/1732797624762126662?s=20
@RebelValkyrie17 - ©.
@RebelValkyrie17 - ©.
2C/ https://x.com/RebelValkyrie17/status/1732800177646243975?s=20
@RebelValkyrie17 - ©.
3/ "Hogwarts School of Misinformation" -Scraping social media -Narratives/Counter narratives -Trolls for hire -"Repetition is truth" -Pseudonyms and secret identities -CISA; Countering Foreign Influence Taskforce -"DISARM" framework, inspired by AMITT -EIP -& more.
@RebelValkyrie17 - ©.
4/ @shadygrooove Shady-Monologue: "If you don't feel like you've been made a fool of, you are not paying attention." -Chris Krebs/Election Interference "They did not think you would be able to figure it out."
@RebelValkyrie17 - ©.
5/ CTIL Files CON'T. Sockpuppets, and spy tactics, and doxxing. OH MY!! [THEY] sell merch in order to obtain your private information.
@RebelValkyrie17 - ©.
6/ 🕵️♂️CTIL "Spy Disguise" for "impact containment" -Security -Compartmentation -Persona
@RebelValkyrie17 - ©.
7/ "BURNER PHONES" 📲 CTIL's "Big Book of Disinformation Response" PLAYBOOK?

@RebelValkyrie17 - ©.
🧵Critical Thinking & Logic🧵 1./ Critical Thinking: the process of actively and objectively analyzing information, concepts, situations, or problems in a systematic and disciplined way. It involves evaluating evidence, arguments, and assumptions, and considering alternative perspectives or solutions. Critical thinkers are open-minded, inquisitive, and willing to question their own beliefs and biases. They use reasoning and logic to make informed and thoughtful decisions, solve problems, and form well-considered judgments. Critical thinking is an essential skill for making sound choices, understanding complex issues, and effectively navigating the challenges of everyday life.