reSee.it - Tweets Saved By @RedTeamActual

@RedTeamActual - R E D
Superchat funding, like @NickJFuentes uses, works well because it leaves no paper trail. You can inject cash into an “influencer” to push (insert narrative) without FARA breathing down your neck or other payment methods exchanging hands. The only trail is the transaction with the payment processor. This is a fragmented funding system using aliases and intermediaries. The best part? (Insert actor, foreign or domestic) can inject narratives without being overt. Fragment the superchat accounts and donations, and the host will keep pushing the narrative as long as the “donations” flow. I’ve already covered a portion of this in my old “influencer” thread. Will make a thread on how to identify unusual onboarding, cyclic timing, clustering and repetition. There are tools for it.

@RedTeamActual - R E D
Okay this is a subject that doesn’t get talked about here on X. I could just say that X is just the bridge to darkweb through specific hashtags combination and links through specific posts. What a lot of bad actors are currently doing is using hashtags here on X to exploit and link their illegal content to their main web archives/hosting sites. I am not going to spell it out because it makes me sick to my stomach. @The1Parzival already covered this. This is all being done through embedded code language, emoji combination and slight misspelling of certain words and terms. X Hashtags are the main vector through tag stacking. They group unrelated tags to maximize exposure across communities. I don’t know what X is doing to remove, ban these accounts that use hashtag chaining for illegal offerings. Twitter 1.0 had the same problem. I am also appalled that “save the kids” influencers don’t talk and or bring this up about the platform which pays them through monetization. Same platform that doesn’t seem to be able to eradicate this type of content which is turning into a breeding ground for this. It’s a tough subject that doesn’t get talked about. The majority of accounts with large followings are more interested in engagement than real issues. It’s sad and a shame. @elonmusk please handle this. I feel dirty just by posting here on X.
@RedTeamActual - R E D
I am speechless really. Twitter 1.0 and now 2.0 still give oxygen to this type of content. It’s like they are doing the bare minimum and not even trying. While the big accounts playing P-Diddy commentary and or chasing PDFs while doing collaborations through state lines with photo op get togethers are not fighting harder for this. Do you want to save the “kids” how about all you clowns start here, yes here on X.

@RedTeamActual - R E D
Please, spare us the self-congratulatory scheme. It’s appalling that you fail so miserably to identify the irony of “called out influencers selling out to foreigners”. You aren’t exposing anything with “I told you so”, you’re just pointing at bottom feeder pawns while worshiping the king of this chessboard you’re currently posting on. Do I have to make it more obvious? Since we’re here, why don’t you call some of the other “influencers” you associate with that have also taken trips or meetings with these foreign leaders and or money from foreign entities? I’ll wait…

@RedTeamActual - R E D
Okay, here’s the core issue with this Signal debacle. I waited 24 hours to do a write up on this and seeing how big accounts from a certain side trying to brush it off are either misunderstanding the issue or deliberately trying to pretend is a non-issue. Common theme has been, “if it’s not classified, it’s a non-issue issue” are completely misunderstanding the principles of federal records data retention, chain of custody and transparency in big brother operations. Even unclassified comms are subject to scrutiny if they involve government business period to include off the record platforms, in this case the Signal app. Just because the dems have had a free range and gotten away from accountability doesn’t mean “we” should do the same. If we can’t enforce government record keeping laws and federal records act then what’s the point in having them? The whole point of this is to preserve comms oversight, historical records, and legal accountability. X is flooded with the “former admin did worse” is pure deflection and not defense. We can’t use “well it wasn’t as bad” as a metric for wrongdoing and or incompetence. Just because the accountability bar is so low it doesn’t mean it should be optional. Do you see the issue? Parties involved need to own this clusterF and revamp their amateur OPSEC.

@RedTeamActual - R E D
This is what happens when @realDonaldTrump hires what appears to be one of the most incompetent lawyers playing influencer. This shouldn’t have happened at all even if the admin which appears to be having a not so hidden hand into bringing the Tate brother to the states. Now, Gucci lawyer over here has to play damage control to save face. Damage is done, administration looks like a circus and eventually this is coming to bite them back. ….and NO, no one tried to “that was a great manipulation” no one twisted your words, look…you are on video. The mental zigzags you continue to do sink you deeper. You know, the more you lie the deeper the hole. How it started Currently 👇 👇

@RedTeamActual - R E D
He had me until…..here. Why lie about something so trivial that has been plastered all over social media and anyone with a heartbeat can verify? You can hear the split second conflict in his voice, trying to listen to different voices telling him different things….YES, NO, YES, YES, NO, NO, WHAT… Bad, bad judgement call.

@RedTeamActual - R E D
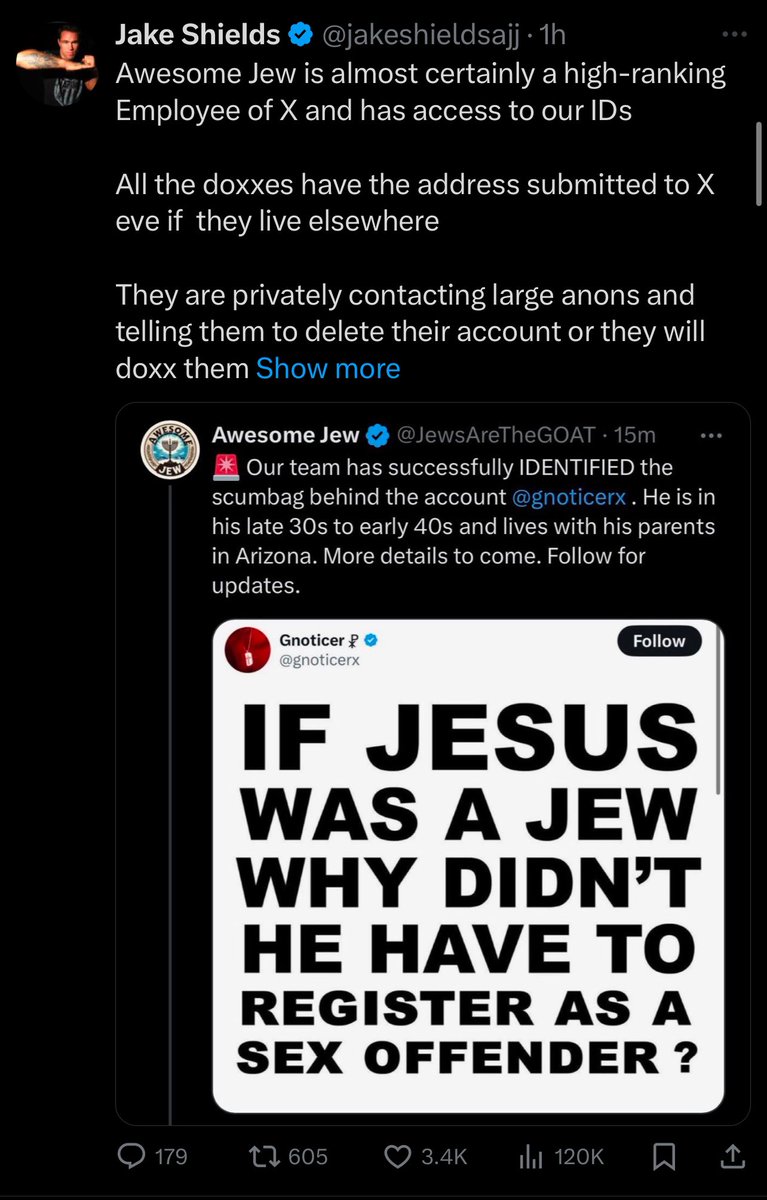
How many times do I have to say this. Your ID Verification was sent 6,000 miles away to AU10TIX headquartered at HaNagar 5B Street, Hod HaSharon, Israel. On top of all that, AU10TIX is a subsidiary of ICTS International N.V. Wait for it: ICTS International N.V. was founded in 1982 by former members of Shin Bet, Israel’s internal security agency. So, if you want to monetize don’t go around and nail to the wall the same people that you willingly sent your biometrics data to and complain how are these accounts are being doxxed. Stupidity levels 300%.

@RedTeamActual - R E D
Let’s talk about “Social Media Influencers” Before we start make yourself comfortable and grab your favorite snacks and or beverage. INFLUENCERS Have you ever wondered how social media influencers, the people we follow every day for advice, inspiration, or just entertainment, can end up pushing disinformation for foreign actors, sometimes without even knowing it? It’s more common than you think, and it’s a lot more subtle than you might expect. I have talked about this before that foreign actors don’t always need to make big, obvious moves to manipulate influencers; they’ve got tactics that slide under the radar. It often starts with something as simple as boosting engagement or offering sponsorship deals and or affiliations (we are familiar with those). Let’s say an influencer posts about a trending topic, maybe something political or a nerve-bashing social issue. Before long, a mysterious account starts promoting that content, retweeting or resharing it, and suddenly the post gets more traction (I have covered this through my Account Poaching posts). That influencer sees their views, likes, or followers grow, which feels good, right? What they don’t know is that some of those “boosters” could be bots, sock-puppet or fake accounts run by foreign or domestic actors, intentionally amplifying the content that serves their agenda.
@RedTeamActual - R E D
CONTENT SEEDING TECHNIQUE Foreign /Domestic actors will plant disinformation in a way that makes it seem like it’s just part of the everyday information flow. This could be through fake news articles, doctored videos, or viral memes that play into the influencer’s existing views or biases. How many times have I pointed this out? I hope you have paid attention. An “influencer”, who might be passionate about a particular issue, stumbles on this content and thinks, “Hey, this aligns with what I believe,” and shares it with their audience. What they don’t realize is that they’ve just taken the bait. They’ve unknowingly become part of a disinformation campaign that could be aimed at disrupting political events, spreading false narratives, or even weakening trust in institutions. Keep in mind that this gets amplified as we head towards finish line, in this case Election Day in November.
@RedTeamActual - R E D
TACTICS Some manipulation tactics are even more direct. Foreign / Domestic actors, posing as legitimate brands or organizations, will approach influencers with partnerships, pay per video episode with large sums of money that seem too good to be true (TENET MEDIA, anyone?) These offers might involve posting about a specific issue or promoting a particular worldview sometimes under the guise of “alternative facts” or “uncovering the truth.” The influencer gets paid, their platform grows, and all the while, they’re pushing narratives that have been carefully constructed to mislead and manipulate.
@RedTeamActual - R E D
PEER PRESSURE TACTIC Influencers often operate in tightly knit communities (DMs, Telegram, Discord, Signal rooms) and when a few key people start talking about a certain topic, others follow. Foreign actors know this and will target influencers within a certain niche, whether it’s politics, health, or even lifestyle content, creating the illusion of a trend. An influencer might see others in their circle posting about a particular issue, feel the pressure to jump on the bandwagon, and before they know it, they’re repeating talking points that originated from a foreign disinformation campaign.
@RedTeamActual - R E D
BOTS Again, I have covered this several times about the power of bots and fake followers. Bad actors use armies of fake accounts to flood an influencer’s mentions, likes, and shares, giving them the impression that their message is resonating. These bots, astroturfing accounts often reinforce specific narratives, making it seem like there’s broad public support for a particular idea when, in reality, it’s all orchestrated. This not only boosts the influencer’s confidence in what they’re sharing but also influences their real followers, who see the inflated numbers and think, “Wow, this must be legit.”……subscription flow.
@RedTeamActual - R E D
CREDIBILITY Say hello to the tactic of slowly building credibility. These actors don’t always come in hot with obvious disinformation. They’ll start with smaller, seemingly harmless engagements, maybe liking or sharing an influencer’s post here and there or even sending polite messages of support (DMs, watch out for these DMs 😎) Over time, they’ll drip-feed misinformation into the conversation, gradually steering the influencer toward sharing content that aligns with their agenda. This way, it doesn’t feel like manipulation it feels organic, like the influencer is just discovering this information themselves and passing it along to their audience.
@RedTeamActual - R E D
WRAPPED UP What’s especially dangerous is how this all plays out on social media platforms especially here on X, where engagement equals visibility. The algorithms (tired of it) are built to amplify content that gets the most reactions, and these actors know how to game that system. They’ll manipulate influencers by getting them hooked on the numbers, likes, shares, comments, and in the process, the influencers become unwitting pawns, spreading disinformation to bigger and bigger audiences. They may never even realize that they’ve been manipulated into serving someone else’s goals. Word of advise, please be careful out there and thank you for coming to my RED THREAD

@RedTeamActual - R E D
Who do they repost? This account is what a lot of these bigger accounts on X are, always selling you something. For many, it was free-speech until monetized. Then it becomes narrative-speech. This account has absolutely nothing of value, zero original content. Everything is reposted, borrowed and or regurgitated from others with few opinion pieces sprinkled here and there. This account is trying to sell you know how and use OSINT using google / Grok to create posts for X and get monetized.

@RedTeamActual - R E D
Who Subscribes to Who I had different plans for this and is part of a larger project that I am working with @The1Parzival. Anyways, here is quick dry run with the little time I have and questionable cell service. This tells you everything you need to know. You are smart enough to put two and two together. This is who is who in the zoo. Note: There’s more a lot more but it’s all irrelevant since it’s all the same characters that show up on this.

@RedTeamActual - R E D
Twitter 1.0 / 2.0 Short Documentary https://t.co/heTgyrsSqf

@RedTeamActual - R E D
Biometric Data and being Monetized through X. AU10TIX/ICTS & STRIPE Besides myself there were only few accounts that brought this issue up. Especially @The1Parzival for being consistent on highlighting certain issues that get overlooked. Facts are not pretty, they are just facts and take no sides.