reSee.it - Tweets Saved By @TheSCIF

@TheSCIF - The SCIF
Dr. Daugherity exposes the printer "glitch" and why 7,000 ballots every 30 minutes were rejected, proving that Maricopa County's printers were deliberately misconfigured in the 2020 election, turning thousands of ballots into unreadable rejects, which forced ballots into manual adjudication, where there is NO oversight, NO transparency, and NO paper trail. This same glitch happened all over the country where taxpayers votes are in the hands of a few people, in private, that can change hundreds of thousands of votes at the click of a button. Massive, non-random misfeeds, up to 7,000 ballots rejected every 30 minutes all day (far exceeding the legal 1-in-500 max misfeed rate). Hit 17K+ total in Maricopa, mostly in key vote centers. Changed from "heavy" to "normal" fusion. Timing marks (the critical black sync lines scanners need) came out too light/blotchy, toner never fused properly, so tabulators spat ballots back as "invalid/photocopy." 5% image shrinkage sabotage, ballot images printed at 19" instead of 20" length → edge markers + timing sync marks shrank/misaligned. Scanners threw constant errors, "edge marker #39 not found," "Determine Vertical edge markers failed," "Ballot misread." Daugherity calls it statistically impossible as "accidental" and accuses deliberate tampering to disrupt tabulation and open the door to manipulation. This isn't conspiracy, it's cold, hard engineering proof from the guy who reverse-engineered the exact PID-style vote control in prior AZ races.

@TheSCIF - The SCIF
USPS whistleblowers expose that around 280,000 completed ballots for the 2020 election were shipped across state lines from Bethpage, NY to Lancaster, PA to steal the 2020 election. Trump was ahead in PA by 700k votes with 70% already counted before they stopped the count. Fraudulent ballots were then injected into the count and the 2020 election was stolen. Coincidentally, the 280k fraudulent ballots from Lancaster and the 630k fraudulent ballots found by data expert Phil Waldron in Philadelphia equals the amount needed for Biden to overcome Trump's lead in PA. These fraudulent ballots were found to be printed in China and coming into the U.S. through the Mexico border and flown in by aircraft. An enormous national security threat to the U.S. and foreign involvement in our elections. The 2020 election was stolen using a combination of fraudulent mail-in ballots and compromised election equipment with engineered backdoors and remote internet access.

@TheSCIF - The SCIF
Over 1.2 MILLION votes were allegedly altered in Pennsylvania during the 2020 election. - 221K votes switched from Trump to Biden in PA - 941K Trump votes deleted in PA Election and cyber security expert dealing with intelligence and information warfare for over 30 years, Phil Waldron agreed and confirmed multiple findings that Dominion voting machines used in the U.S. were built for manipulating elections. Dominion has similar code, function, and have a common DNA to holding company SGO's Venezuelan-linked Smartmatic. These systems allow authorized and unauthorized users to cancel votes, shift votes, preload votes, vote blank ballots, all in real time and in large numbers. Most importantly these machines and are connected to the internet with backdoor access, send information to servers outside the U.S. and have connections to multiple hostile foreign nations.

@TheSCIF - The SCIF
Dominion, SGO, Smartmatic, Scytl, and ES&S, are ALL engaged In engineering election results, which are all connected to foreign countries. U.S. election data is held by Scytl on foreign servers before being sent back to the United States. ANYTHING can be altered before the data is sent back. WHY? Why would we EVER send sensitive data, especially election data, outside the U.S. to a foreign country? The answer is simple. To COMMIT FRAUD.

@TheSCIF - The SCIF
Obama diverted $400 million from Iran's pallets of cash through the Dubai Embassy to Italian operatives and Merrill Lynch in Geneva to fuel the stolen 2020 election, which was exposed, under oath, by Maria Zack. In return, Leonardo SpA officials used military satellites and CIA tools like Hammer and Scorecard to hack U.S. voting machines, flipping Trump votes to Biden along with other fraudulent methods, machines, mail-in ballots, and remote access. China coordinated the operation with tech and bribes, the CIA oversaw the stolen 2020 election, and the FBI covered it up, all to install Biden as a puppet to the cabal and foreign powers. This global election fraud cartel is the largest threat to American democracy and the world.

@TheSCIF - The SCIF
Dominion's foreign ties to the CCP and Serbia. It doesn't take a rocket scientist to figure out that our elections are rigged and have major foreign involvement. https://t.co/2YzStlWTyF

@TheSCIF - The SCIF
$3 BILLION worth of TAXPAYER DOLLARS funneled to protesters and rioters through corrupt front companies and NGOs. Neville Roy Singham tied to over 2k organizations, with 200 of them solely dedicated to producing anti-American propaganda. https://t.co/XDvG3S0bRH

@TheSCIF - The SCIF
They engineered a coup, spied, fabricated intelligence, and silenced career professionals, all to get Trump. - Obama - Hillary Clinton - John Brennan - James Comey - James Clapper And many more... TRAITORS who commit TREASON must pay a price. https://t.co/i2MNkCh8Kk

@TheSCIF - The SCIF
The journalists, the influencers, the mainstream media, and the elites who gaslit you for years, lying straight to your face with a smile, saying that there was no child trafficking sex rings, were actually the ones involved in the child trafficking sex rings themselves. https://t.co/E5H9TEJB82

@TheSCIF - The SCIF
MORE ELECTION FRAUD as California Attorney General attempts to block investigation into fraud. 45,000 more votes were added and certified to the Secretary of State from the original final count of 611,000 votes in the 2025 special election in California, which prompted an investigation by CA Sheriff, which was interfered and stopped by the CA State Attorney General. Update: The courts have sided with the Riverside Sheriff to continue the investigation. What are they afraid of them finding if there is no fraud occurring?

@TheSCIF - The SCIF
Dominion Voting System's built-in feature to flip votes exposed. Whoever has access to the machine can flip thousands of votes at the click of a button, on top of the built-in remotely accessible backdoors. They knew this and kept it a secret, even lied under oath, until it was exposed.

@TheSCIF - The SCIF
Dominion Voting Systems had remote desktops connected to the internet during the 2020 election. Belgrade, Serbia, was also revealed to be a main location of Dominion Voting Systems where all major decisions are made, and where U.S. elections are actually conducted, monitored, and altered, through Huawei servers with ties to China, Iran, and Serbian intelligence. This is the global election fraud cartel.

@TheSCIF - The SCIF
Maricopa County, Arizona, election official testifies that a Dominion employee was observed copying votes onto hard drives and taking them off site with absolutely no oversight or chain of custody, whatsoever, during the 2020 election. Complete free rein with no oversight is a huge security breach in our elections. They could have uploaded or downloaded or changed anything during the 2020 election.

@TheSCIF - The SCIF
George Soros involved and allegedly knew about Hillary Clinton's plan to frame President Trump with Russia Collusion. How deep is this entire plot and does the corruption really go? This is treason at the highest levels. Intercepted emails from 2016, from the Soros Foundation, exposed that Leonard Benardo, an executive at the foundation, indicated that Hillary Clinton approved a plan to highlight alleged Russian interference in U.S. elections, specifically framing President Trump with ties Russian hackers, to distract from her own email controversy. The annex suggests this was intended to escalate to an "Olympic level" of scrutiny. The document also criticizes the FBI for dismissing potential Clinton campaign involvement or Russian disinformation without a thorough investigation. This exposes Obama's entire administration and national security team, especially then-CIA Director John Brennan, and Hillary Clinton herself fabricating and executing a coup on a sitting president and the United States itself. This is sedition and treason at the highest levels. They must be held responsible and pay for their crimes.

@TheSCIF - The SCIF
Obama's secret kill list. Every Tuesday, Barack Obama and John Brennan would meet and create a hit list of people to assassinate that week. Assassinations were conducted by drone, air strike, tactical teams, or individual hitman. DRONES STRIKES 2009-2016: - Total Drone Strikes: 563+ - Total Drone Strike Targeted Deaths: 4,000+ - Total Drone Strike Civilian Deaths: 800+ BOMBS DROPPED 2009-2016: - Total Bombs Dropped: 91,930+ - Total Targeted Deaths from Bombs: 19,500+ - Total Civilian Deaths from Bombs: 4,950+ Obama has dropped the most bombs and has conducted the most targeted drone strikes, which have also killed civilians, more than any other president in history.

@TheSCIF - The SCIF
The Anthony Weiner laptop and the "Insurance Policy" file. 9+ NYPD cops don't all end up with self-inflicted gun shots to the head by accident. Once the Weiner laptop is exposed. The cabal will fall. This video will have you all frazzled up after watching it. The most important question still remains... Who has copies of the hard drive and will they release it and expose the truth once and for all?

@TheSCIF - The SCIF
Obama literally created one of the worst terrorist groups in history by deploying the Brennan CIA to create ISIS, which splintered into a jihadists group, in an attempt to overthrow Assad in a disastrous joint covert operation with the CIA and Saudi Arabia, which resulted in over 500,000 people killed, and displacing over 10 million in the U.S. proxy war with Syria. All roads lead to Obama.

@TheSCIF - The SCIF
Nation-state vulnerability expert Jeff Lenburg exposed Dominion voting machines and software used in the Antrim County 2020 election swapping Trump votes with Biden votes. Trump ballots inserted: 4 votes - Counted: 2 votes Biden ballots inserted: 2 votes - Counted: 4 votes "The highest priority as a bad guy would be to subvert our election system." — Jeff Lenburg: nation-state vulnerability expert

@TheSCIF - The SCIF
HUGE: $928 MILLION Stolen from California Solar Program and diverted to Democratic Voter Registration & Activism Efforts A new report from CAL DOGE alleges that $928 million from California's Solar on Multifamily Affordable Housing (SOMAH) program, intended to fund solar installations on affordable housing, has been diverted to Democratic voter registration and activism efforts. Funded by gas taxes and utility bills, the program has completed only 269 projects worth $72 million since 2015, raising questions about the missing funds.Organizations like GRID Alternatives and the California Environmental Justice Alliance (CEJA) are implicated, with CEJA's affiliated entity reportedly using public dollars for partisan activities, including voter mobilization and candidate endorsements. CAL DOGE calls for a full audit to ensure accountability.This highlights ongoing concerns about transparency in green energy initiatives. Source: NY Post

@TheSCIF - The SCIF
Hillary Clinton orchestrated the Russia Collusion operation against President Trump to divert attention from her foreign dealings and illegal private email server. Investigators found over 650,000 emails with state secrets, child exploitation content, pay-to-play schemes, money laundering, perjury, Obama's pseudonym for illicit communication, and more. Evidence was destroyed using hammers and bleach, despite claims of innocence. Clinton devised and approved the plot, Brennan ran it up the ladder after they knew no real collusion existed, and Obama lit the fuse. Brennan and Clapper's operatives executed the coup, involving slander, spying, taxpayer-funded psychological operations to not only undermine President Trump, but subverting the United States and the Constitution itself, all to conceal decades of crime and corruption and retain power. This constitutes high-level sedition and treason. Americans were deceived and gaslit for years by the mainstream media and our own government. It's time for accountability and imprisonment. What will it take for action against these criminals?

@TheSCIF - The SCIF
In 2020, Nevada Democrats mailed ballots, not applications, to every registered voter, requested or not. They knew over 41,000 registrants hadn't voted or updated registrations in 10+ years. Why? They were dead, but got ballots anyway, and many voted. This is called FRAUD. https://t.co/ShjUXQjm3N

@TheSCIF - The SCIF
Former CIA Director John Brennan is not only a traitor to the United States and involved in the coup against President Trump, but also signed the visas for half of the terrorists involved in the 9/11 attack on the World Trade Towers. You really think he didn't know what their plans were? He is as dirty and ruthless as they come and must be held accountable.

@TheSCIF - The SCIF
Democrats didn't expect Trump to be ahead by hundreds of thousands of votes in the 2020 election, which forced them to shut down multiple swing state's voting locations to cheat on top of already cheating in order to produce even more fraudulent votes to steal the 2020 election. https://t.co/rWxEvKr2oc

@TheSCIF - The SCIF
Hillary Clinton's own campaign manager testified that she started the entire Russia Collusion hoax by giving the media the greenlight to run a completely fabricated story about Trump having a "secret server" tied to Russia, when in reality, she was the one with an actual secret server tied to foreign countries and illegal activities, which was said to contain evidence of child trafficking and abuse, pay to play politics, money laundering, and many other serious federal crimes. Whatever they accuse Trump and conservatives of, they are literally guilty of themselves. The patterns don't lie.

@TheSCIF - The SCIF
On November 5, 2020, during the Antrim County presidential election results, an anonymous user with elevated privileges remotely accessed the county’s Election Management System (EMS) and modified the database. This incident proves unauthorized remote access altering the tabulated results. In addition, ballots were found with altered timing marks in blocks 15, 18, 28, 41, and 44. The changes produced a 20% higher rejection rate for Republican ballots, routing them into adjudication where votes could be manually altered, switching Trump votes for Biden.

@TheSCIF - The SCIF
130,000 to 280,000 completed ballots for the 2020 election were shipped across state lines from Bethpage, New York to Lancaster, Pennsylvania to steal the 2020 election. There is no reason completed ballots should ever be transported across state lines from one state to another. These were fraudulent ballots to overturn Trump's massive 700,000 vote lead in PA with 75% of the votes already counted before they shut down swing state locations to produce and tabulate enough ballots to steal the 2020 election from President Trump.

@TheSCIF - The SCIF
Trucks of ballots arrived from Runbeck for over a week after Arizona's 2020 election. A worker testified ballots kept coming after Nov. 10 via front and back doors, with unknown quantities or origins, despite access to voter books. Runbeck prints, mails, fills, and counts ballots off-site without oversight, partnering with Dominion and ES&S for machine compatibility. Arizona needed an extra 2.5 weeks after the election to "count" all the ballots because that's how long it took to produce enough ballots to overturn Trump's massive landslide in the 2020 Election.

@TheSCIF - The SCIF
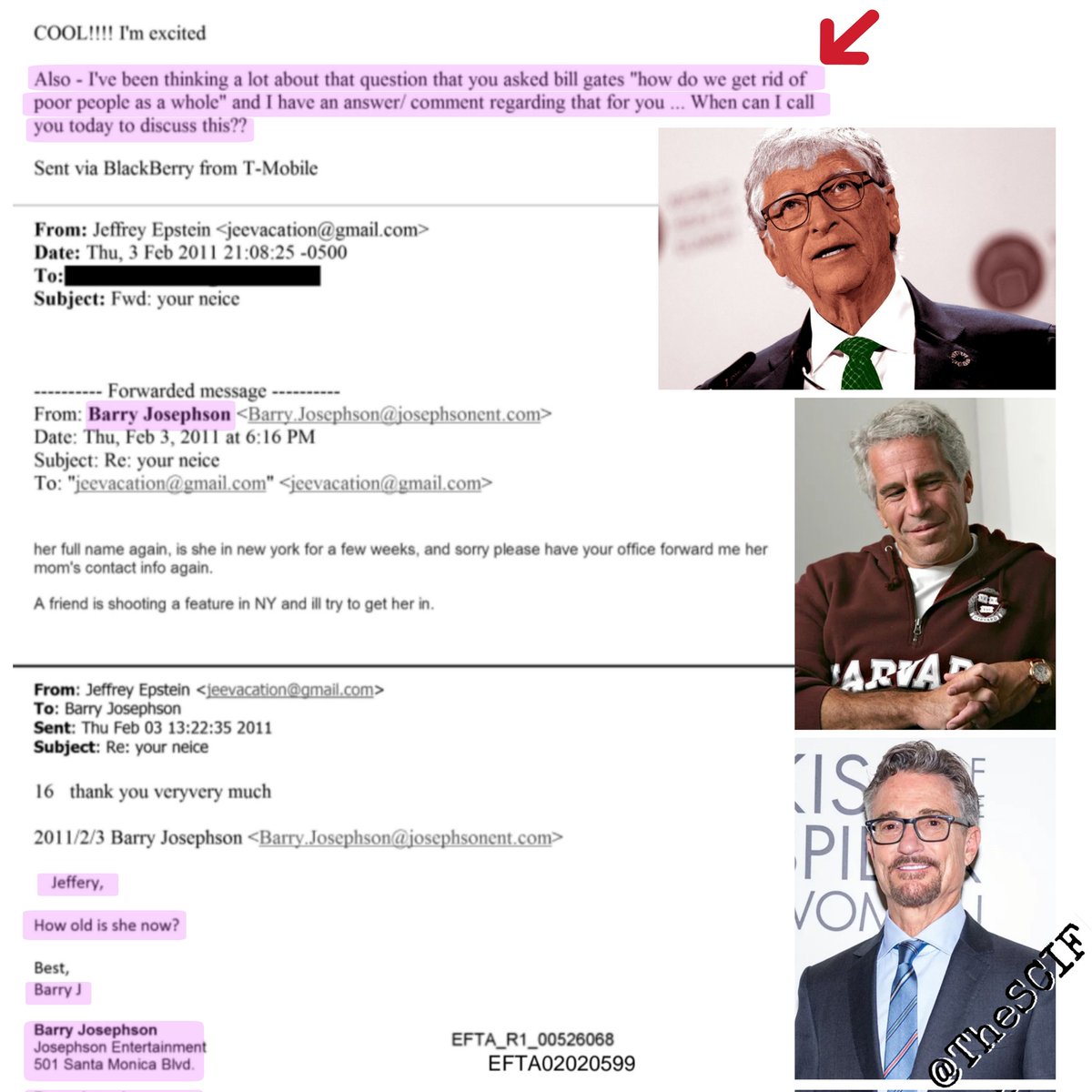
Epstein documents expose a 2011 email from Hollywood producer Barry Josephson to Jeffrey Epstein. In it, Josephson writes: "I've been thinking a lot about that question that you asked Bill Gates, 'how do we get rid of poor people as a whole' and I have an answer/comment regarding that for you…" It is Josephson referencing a supposed earlier conversation between Epstein and Gates discussing how to get rid of the "poor" population. And you wonder why Bill Gates was pushing the Covid vaccination so hard... They want to lower the population. You should clearly understand this by now, especially after experiencing what happened during Covid and what we know now.

@TheSCIF - The SCIF
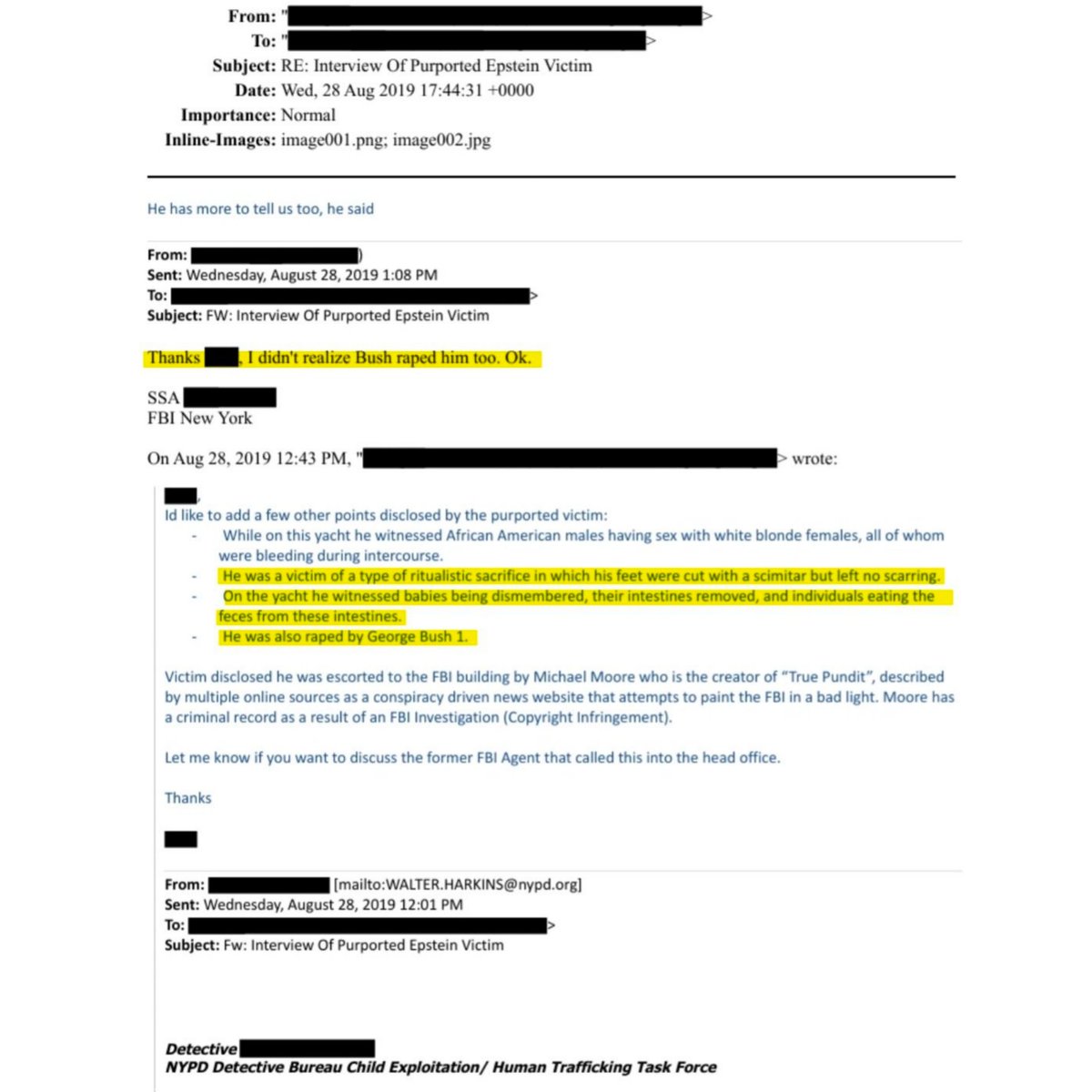
There is a secret D.C. underground of elite child trafficking being run and operated by some of the wealthiest most powerful people in the world. The Epstein documents have just confirmed some of the darkest most horrific things being done to children that many have been trying to tell you for years... What does this tell you about the world we live in and about the ones who rule over us? The most important question of all still remains... "What are we going to do about it?" Life is about way more than just going around solving one horrible problem after the next, but this is one of those horrible things that you just can't ignore, or let slide. This is the trafficking, torture, and sexual abuse of children, and in my personal opinion, the worst thing that you could ever do. It's time to wake up.

@TheSCIF - The SCIF
The Pizzagate emails were originally discovered in John Podesta and Hillary Clinton's emails where secret comms involving "food," especially the word "pizza," were being used to disguise and talk about the trafficking and abuse of children. These emails were presented to the world by Wikileaks, which were originally obtained by a brave American patriot named Seth Rich. Seth Rich found out that the DNC rigged the primary against his favorite candidate, Bernie Sanders. Seth worked for the DNC and had special access. He then downloaded the emails and gave Wikileaks the DNC Podesta/Clinton emails. He exposed the Podesta/Clinton emails because he saw how corrupt his own party was. His perception of the government and his world was shattered when the truth revealed itself and he wanted to expose the truth to the world. An ex-employee of the NSA confirmed that the Podesta/Clinton emails were in fact downloaded from someone inside the DNC and NOT by a foreign nation like they wanted you to first believe. This was found through electronic analysis mentioned in this video. That someone who exposed these emails allegedly turned out to be Seth Rich. A message exposed by John Podesta stated that he supported the idea of "making an example" out of the DNC leaker. Not too long after, Seth Rich was found dead, less than a block from his own home. The cops did not cooperate and immediately closed the case as a botched robbery. The problem is, nothing was stolen, his phone, his wallet, and his watch were all found at the scene. Seth was shot multiple times in the back. Many allege that people tied to Podesta and Hillary had Seth killed to make an example out of him for anyone else planning to leak information to the press to expose them and their corruption. RIP Seth Rich and thank you.

@TheSCIF - The SCIF
All of these mainstream media reporters constantly wrote articles declaring pizzagate was fake. Coincidentally, all of these same reporters were arrested and charged for rap*ng and sexually abusing children. Some of the victims were toddlers. There are NO coincidences. https://t.co/OfgF3huBte

@TheSCIF - The SCIF
The Weiner laptop is one of the most important pieces of evidence next to the Epstein documents that has enough evidence on it to bring down some of the most wealthy, powerful people in the world, including Hillary Clinton, and the U.S. government itself. https://t.co/9v5q9y5tMC

@TheSCIF - The SCIF
Michigan 2020 election worker reports that a white van, and 2 other cars showed up at the Detroit TCF center on Nov. 4th between 3 and 4 am with 138,000+ ballots, unsealed, with no chain of custody, which were all 100% marked for Joe Biden. This report lines up with multiple testimonies and affidavits and was caught on camera. The 2020 election was stolen.

@TheSCIF - The SCIF
Michigan secretary of state official caught on video ordering 2020 election volunteers to count ballots that all contained the same signature, even after making her aware of the obvious and apparent election fraud. https://t.co/bHpCDht1tn

@TheSCIF - The SCIF
New Epstein document states, "George Bush 1" (senior?) allegedly rap*d a male victim (child) and witnessed a type of ritualistic sacrifice. This should tell you everything you need to know about what people were screaming from the rooftops about for years. https://t.co/ZrIxECDtS6

@TheSCIF - The SCIF
Analysis from the 2020 Georgia election found over 40 data points where negative voting, or outright vote switching occurred, totaling over 200,000 votes, along with machine learning algorithms, which flagged over 500 precincts, with over 1,000,000 corresponding votes that had suspicious activity in the 2020 Georgia election alone. The total amount of fraud that occurred during the 2020 election is absolutely mind-boggling and one of the most sophisticated election fraud operations in U.S. history.

@TheSCIF - The SCIF
A military style color revolution regime change operation is taking place on U.S. soil, right in front of us, in real time. Color revolutions, often characterized by mass protests and violent riots leading to regime changes, have been linked to U.S. foreign policy tools like USAID, the NED, and the CIA, which channel taxpayer dollars through non-governmental organizations (NGOs) to promote "democracy" abroad. Historically, in events such as Ukraine's 2004 Orange Revolution and Georgia's 2003 Rose Revolution, U.S.-funded groups like the National Endowment for Democracy (NED), described by critics as a CIA proxy, provided training, resources, and logistical support to opposition movements. These NGOs, often portrayed as independent, facilitate voter mobilization, media campaigns, and protest coordination, using funds from congressional appropriations to USAID and NED. This amounts to covert interference, while supporters frame it as legitimate aid for civil society. Key players include billionaire philanthropist George Soros through his Open Society Foundations, which have collaborated with or received matching funds from USAID in various countries. Allegations tie Democratic administrations to these efforts, with reports of USAID grants flowing to Soros-linked NGOs during the Biden era, totaling millions in taxpayer dollars. In foreign contexts, this network is accused of orchestrating unrest by funding local activists and media outlets to amplify grievances against incumbent governments, often under the guise of human rights promotion. Just like we see playing out against ICE and to also cover up massive operations of fraud, once again being stolen from American taxpayer dollars, with the Minnesota State government involved. Soros and related organizations have denied orchestrating revolutions, but we all know this is far from the truth, with Democrats and the cabal itself orchestrating our entire countries downfall which also has ties to China and the CCP. Domestically, similar dynamics are in play, with USAID and federal funds reportedly supporting progressive NGOs tied to Democratic causes and Soros, influencing U.S. protests and policy advocacy. These grants for "social justice" initiatives are actually fueling division, using taxpayer dollars via "shady" networks to lobby for far left communist reforms. All in an attempt to install globalist communist regimes, not just in the U.S. but abroad. It's all connected and is the blueprint running in multiple countries worldwide, which is also tied to the global election fraud cartel which is just another arm of this entire operation. Now, it's time to shut it all down.

@TheSCIF - The SCIF
Princeton Professor shows how easy it is to hack electronic voting machines. The researchers craft a virus that exploits software flaws in the machine's operating system. Votes are silently redirected from one candidate to another, symbolizing how an attacker could "steal" an election without detection. The machine's interface shows no signs of tampering, and the final tally reflects the altered results. The hack leaves no traceable evidence on the machine itself, as the malware erases its tracks after execution. This makes post-election audits challenging without independent verification methods. The entire process takes mere minutes, emphasizing that such attacks are not the domain of nation-state actors alone but could be executed by motivated individuals or groups with moderate resources. The part that anyone could buy costs $4 dollars and this was just ONE simple demonstration from all the way back in the 2006 to 2008 era. Now it's even easier and done remotely with built-in back doors.

@TheSCIF - The SCIF
A military style color revolution regime change operation is taking place on U.S. soil, right in front of us, in real time. Color revolutions, often characterized by mass protests and violent riots leading to regime changes, have been linked to U.S. foreign policy tools like USAID, the NED, and the CIA, which channel taxpayer dollars through non-governmental organizations (NGOs) to promote "democracy" abroad. Historically, in events such as Ukraine's 2004 Orange Revolution and Georgia's 2003 Rose Revolution, U.S.-funded groups like the National Endowment for Democracy (NED), described by critics as a CIA proxy, provided training, resources, and logistical support to opposition movements. These NGOs, often portrayed as independent, facilitate voter mobilization, media campaigns, and protest coordination, using funds from congressional appropriations to USAID and NED. This amounts to covert interference, while supporters frame it as legitimate aid for civil society. Key players include billionaire philanthropist George Soros through his Open Society Foundations, which have collaborated with or received matching funds from USAID in various countries. Allegations tie Democratic administrations to these efforts, with reports of USAID grants flowing to Soros-linked NGOs during the Biden era, totaling millions in taxpayer dollars. In foreign contexts, this network is accused of orchestrating unrest by funding local activists and media outlets to amplify grievances against incumbent governments, often under the guise of human rights promotion. Just like we see playing out against ICE and to also cover up massive operations of fraud, once again being stolen from American taxpayer dollars, with the Minnesota State government involved. Soros and related organizations have denied orchestrating revolutions, but we all know this is far from the truth, with Democrats and the cabal itself orchestrating our entire countries downfall which also has ties to China and the CCP. Domestically, similar dynamics are in play, with USAID and federal funds reportedly supporting progressive NGOs tied to Democratic causes and Soros, influencing U.S. protests and policy advocacy. These grants for "social justice" initiatives are actually fueling division, using taxpayer dollars via "shady" networks to lobby for far left communist reforms. All in an attempt to install globalist communist regimes, not just in the U.S. but abroad. It's all connected and is the blueprint running in multiple countries worldwide, which is also tied to the global election fraud cartel which is just another arm of this entire operation. Now, it's time to shut it all down.

@TheSCIF - The SCIF
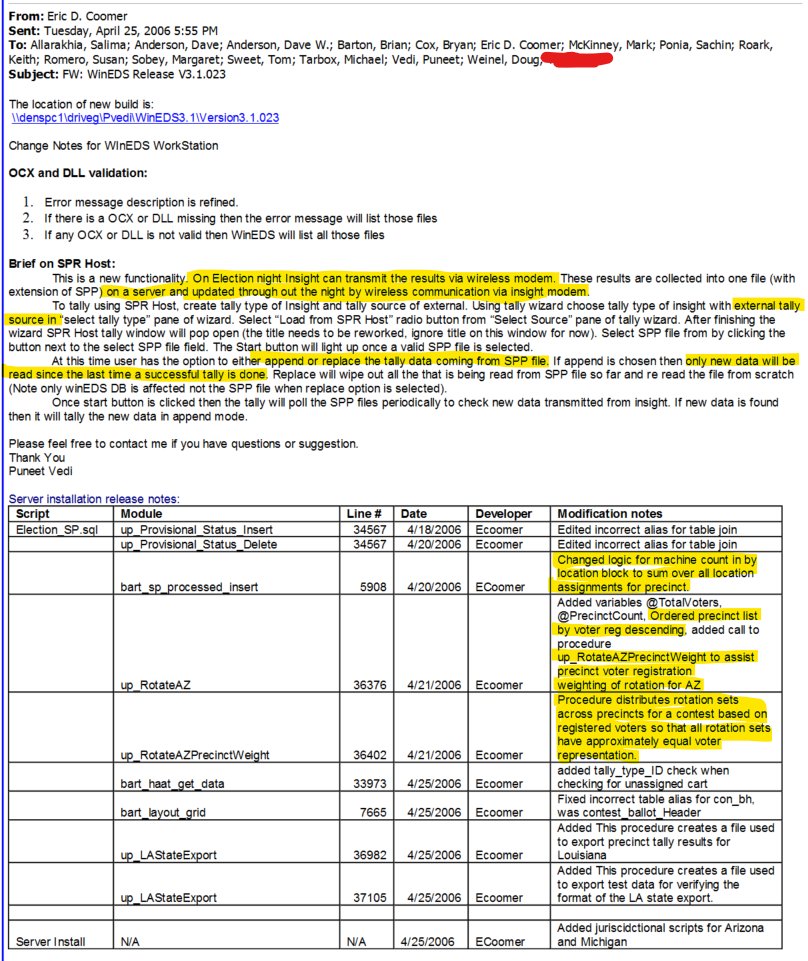
For anyone who hasn't seen this old document from Eric Coomer from Dominion when he used to be with Sequoia, he blantly talks about transmitting data from their machines through a wireless modem, including vote tallies, updates, changing voter rotation representation. These machines were specifically designed for fraud. How much more proof do you want?

@TheSCIF - The SCIF
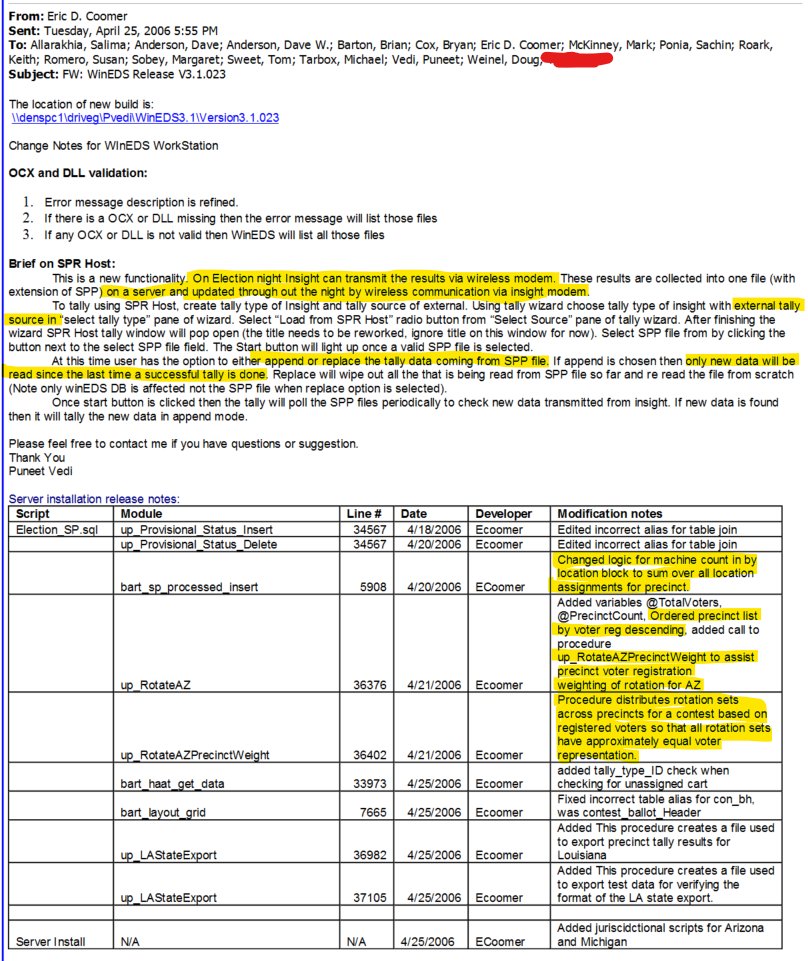
More mainstream media journalists and Minneapolis state employees involved and found in the Anti-ICE assault Signal Group Chat App. Ben Hovland: NPR journalist and photographer. Alyssa Polack: Employee of the Minnesota Department of Education. https://t.co/GwFZuwXijY

@TheSCIF - The SCIF
Over 100 affidavits from GA voters, election officials, experts, and engineers, found a MASSIVE amount of election fraud during Georgia's 2020 election. - 2,506 Felons voted - 66,248 Underage voters - 2,423 Not registered to vote - 1,043 Ballots were cast from people using a P.O. box - 4,926 Voted after registering after the deadline to vote - 10,315 Voted who were registered to vote but deceased before election day - 395 Casted ballots in another state which is illegal in both states - 15,700 Voted who filled out a national change of address before Nov. 3, 2020 - 40,279 Individuals voted and moved across county lines, at least 30 days prior to election day, who did not properly register in their new county This does NOT include fraudulent ballots or any type of electronic fraud. The total number of fraudulent votes is easily in the hundreds of thousands, even millions, just from Georgia alone. Imagine the fraud from the rest of the country... Trump won in a landslide.

@TheSCIF - The SCIF
The FULL 2020 Election video testimony from the State Farm Center in Georgia, when election workers announced a closure and sent everyone home, including required poll watchers, and ran alleged fraudulent ballots all throughout the night. Once cleared out, a few Democrats remained and pulled suitcases of alleged fraudulent ballots from under draped tables that they hid there themselves earlier that day. With absolutely no oversight, they scanned these ballots repeatedly through the night, violating tons of laws requiring officials' presence, committing massive election fraud.

@TheSCIF - The SCIF
A forensic dive into DOMINION Voting Systems by Allied Security Operations Group (ASOG), proved that Antrim County, Michigan's election management system was accessed remotely by an anonymous user on Nov. 5th with "escalated privileges" and made changes to the database when they were trying to retabulate the election. This alone PROVES the machines were remotely accessible, and by an "unknown" 3rd party. The second massive finding was that the "black solid boxes" on the side of the ballot were altered to trick machines and trigger and automatic error, "adjudication," if Republican candidates were selected on the ballot. There are 59 total "black solid boxes" on the side of a ballot for the machine to register specific information. Within the forensic images in Antrim County, blocks 15, 18, 28, 41, and 44 were ALL intentionally modified. The height, the width, and the overall shape were intentionally modified to generate errors if a republican was voted for on the ballots in order to cause an "error" and be sent to adjudication. And that ladies and gentleman, is where you can change all the rejected ballots, at one time, at the click of a button. In adjudication. ASOG reported that these were built-in features of a flawed system. With over 15,000 logged errors in a single forensic exam. The glitch is the steal, with error rates skyrocketing to 68.05%, far exceeding the federal allowable limit of 0.0008%. In Central Lake Township alone, 81.96% of ballots were reversed and sent for adjudication— a staggering rejection rate unheard of in prior elections. This is the blueprint for election fraud in the U.S. and around the world in over 100+ countries.

@TheSCIF - The SCIF
A forensic dive into DOMINION Voting Systems by Allied Security Operations Group (ASOG), proved that Antrim County, Michigan's election management system was accessed remotely by an anonymous user on Nov. 5th with "escalated privileges" and made changes to the database when they were trying to retabulate the election. This alone PROVES the machines were remotely accessible, and by an "unknown" 3rd party. The second massive finding was that the "black solid boxes" on the side of the ballot were altered to trick machines and trigger and automatic error, "adjudication," if Republican candidates were selected on the ballot. There are 59 total "black solid boxes" on the side of a ballot for the machine to register specific information. Within the forensic images in Antrim County, blocks 15, 18, 28, 41, and 44 were ALL intentionally modified. The height, the width, and the overall shape were intentionally modified to generate errors if a republican was voted for on the ballots in order to cause an "error" and be sent to adjudication. And that ladies and gentleman, is where you can change all the rejected ballots, at one time, at the click of a button. In adjudication. ASOG reported that these were built-in features of a flawed system. With over 15,000 logged errors in a single forensic exam. The glitch is the steal, with error rates skyrocketing to 68.05%, far exceeding the federal allowable limit of 0.0008%. In Central Lake Township alone, 81.96% of ballots were reversed and sent for adjudication— a staggering rejection rate unheard of in prior elections. This is the blueprint for election fraud in the U.S. and around the world in over 100+ countries.

@TheSCIF - The SCIF
DARPA, Palantir, Boeing, foreign countries, and even Google have programs and technology that can read & write, manipulate, induce, project, and effect things and people in ways you never thought possible. All this is already here and already weaponized. The tech reported in the U.S. military raid on Maduro is just a taste. These DEWs have many layers and include, A.I., electromagnetics, and other frequency weapons.
@45Lori1 - TPLori2 🇺🇸
@TheSCIF This is beyond the pale for consumption on the Public. Using it on our captured enemies would be useful in lieu of torture.
@TheSCIF - The SCIF
These needs to come already. People need to start taking this more seriously because it's already here and has been here for over 50+ years. It is just extremely more advanced then back then with the adaptation and incorporating A.I. and newer tech into it, which what makes it extremely effective.

@TheSCIF - The SCIF
Former Nicolás Maduro security guard delivers a firsthand account of the advance technology used in the U.S. raid in Venezuela. State-of-the-art drones, massive firepower, but the Direct Energy Weapons were the most terrifying. 20 elite American soldiers, armed with cutting-edge technology, dismantled defenses and neutralized hundreds without a single casualty on their side. This isn't just a story of victory—it's a masterclass in modern warfare supremacy. The Americans arrived undetected, Advanced electronic warfare systems completely disabled Venezuelan radars and other equipment. Drones struck with lightning speed, obliterating bases and outpacing any counter-response. The guard notes Venezuela had "no technology to fight against drones," highlighting the asymmetric edge of U.S. unmanned aerial systems. Most interesting, was the mention of Direct Energy Weapons, causing immediate incapacitation, with victims bleeding from ears, nose, and mouth. This matches the Long Range Acoustic Device (LRAD) or emerging directed-energy systems like the Active Denial System (ADS). and other electromagnetic and acoustic weaponry. If you follow me, this is nothing new and a taste of what we really have and are capable of. The result? 20 operators vs. hundreds, equaling total domination. "You think you can fight Americans? You don't even know what their weaponry is like." With President Trump eyeing Mexico's cartels next—"You're on the list too" Don't FAFO with the USA!

@TheSCIF - The SCIF
PROJECT MAVEN and the U.S. Military's Cutting-Edge Arsenal of AI-Driven Warfare and Directed Energy Weapons. This is an important deep dive into one of the U.S. Department of War's most transformative initiatives, a game-changer that's reshaping modern warfare through artificial intelligence. Launched in 2017 under the Algorithmic Warfare Cross-Functional Team, Project Maven isn't just another tech buzzword; it's the Pentagon's flagship AI program designed to supercharge military intelligence by automating the analysis of vast troves of data from drones, satellites, and surveillance feeds. Highlighting how Maven uses machine learning and computer vision to detect, classify, and track targets in real-time, compressing the "kill chain" from hours to minutes. The weapon and defense systems powering this revolution, including the seamless integration of Directed Energy Weapons (DEWs). Project Maven serves as the brain, processing petabytes of imagery to identify threats like enemy vehicles, personnel, or infrastructure with pinpoint accuracy—far beyond what human analysts could achieve alone. Initially deployed against ISIS in 2017, it fused data from full-motion video (FMV) and other sensors to flag potential strikes, always with human oversight in the loop to ensure ethical decision-making. Today, under the National Geospatial-Intelligence Agency (NGA), Maven has expanded to all military branches—Army, Air Force, Space Force, Navy, and Marines—via platforms like the Maven Smart System (MSS). MSS isn't just about detection; it's a force multiplier, enabling rapid targeting in exercises like Scarlet Dragon, where it slashed manpower needs from thousands to mere dozens while handling complex scenarios in CENTCOM and beyond. Now, pair this AI prowess with the U.S. military's Directed Energy Weapons, and you get a lethal, futuristic synergy. DEWs harness concentrated electromagnetic energy—think high-energy lasers (HELs) and high-power microwaves (HPMs)—to neutralize threats without traditional munitions, offering infinite "ammo." These aren't hypothetical; they're operational and evolving rapidly. High-Energy Lasers (HELs), systems like the Navy's HELIOS (High-Energy Laser with Integrated Optical-Dazzler and Surveillance) aboard destroyers like the USS Preble deliver speed-of-light strikes to down drones, missiles, or small boats for pennies per shot. Integrated with Maven's AI targeting, HELIOS can acquire, track, and zap threats in swarms, as demonstrated in recent Pacific tests. The Army's DE M-SHORAD (Directed Energy Maneuver-Short Range Air Defense) prototype, mounted on Stryker vehicles, recently shredded drone swarms at Fort Sill, blending lasers with kinetic defenses for layered protection. High-Power Microwaves (HPMs), weapons like the Air Force's THOR (Tactical High-Power Operational Responder) unleash radiofrequency waves to fry electronics in drones or missiles from afar, covering wide areas with a single pulse. In urban or congested environments, HPMs provide non-lethal options, disrupting signals without collateral damage—perfect for Maven-identified targets in sensitive ops. Broader Defense Ecosystems, Maven feeds into systems like the Joint All-Domain Command and Control (JADC2), linking sensors across domains for seamless ops. DEWs complement this by offering scalable effects—from dazzling sensors (e.g., Vigilant Eagle for airport defense) to outright destruction. The Pentagon's Directed Energy Roadmap, with $1 billion annual investments, pushes for higher power outputs to tackle hypersonic threats, while initiatives like the High Energy Laser Scaling Initiative bolster industrial production. What makes this combo so revolutionary? Speed, precision, and cost-efficiency. Maven's AI spots the threat; DEWs eliminate it at light speed, with deep "magazines" that outlast ammo stockpiles. Project Maven is the spark igniting this fire, keeping the U.S. ahead in an era where data and energy are the ultimate weapons.

@TheSCIF - The SCIF
DARPA, Palantir, Boeing, foreign countries, and even Google have programs and technology that can read & write, manipulate, induce, project, and effect things and people in ways you never thought possible. All this is already here and already weaponized. The tech reported in the U.S. military raid on Maduro is just a taste. These DEWs have many layers and include, A.I., electromagnetics, and other frequency weapons.

@TheSCIF - The SCIF
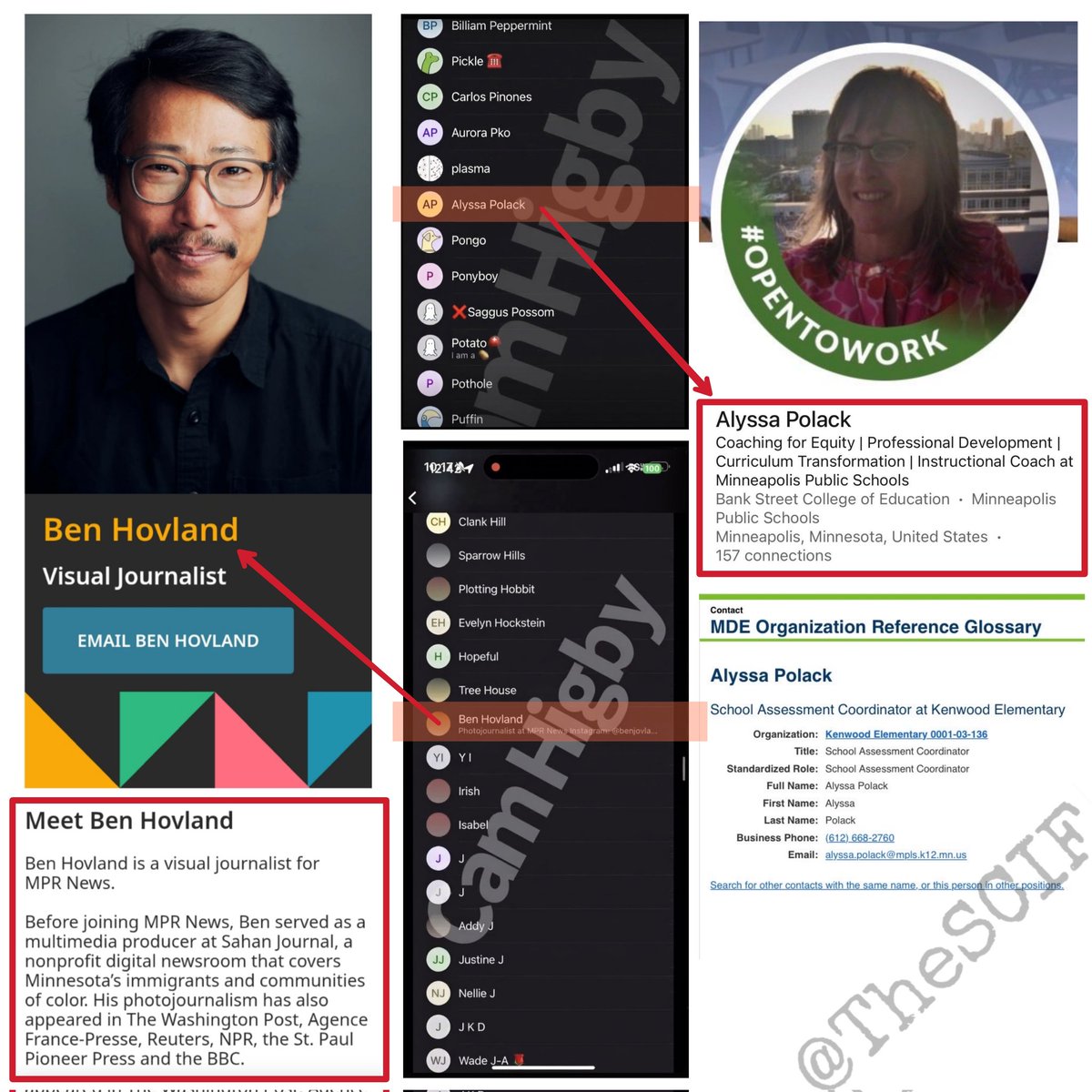
Rep. Anna Paulina Luna refers Seth Harp to the DOJ for investigation and pursues criminal charges regarding the intentional publication of information related to Operation Absolute Resolve, including the doxxing of a U.S. Delta Force operator. "That conduct is not protected journalism. It was reckless, dangerous, and put American lives at risk. The First Amendment does not give anyone a license to expose elite military personnel, compromise operations, or assist our adversaries under the guise of reporting."