reSee.it - Tweets Saved By @TrueOnX

@TrueOnX - Noah B. Price
🚨THIS IS HOW WE FIGHT BACK! ⚠️URGENT HELP ME: THEY JUST PROVED THEY’RE TERRIFIED Wells Fargo Jumped on a Quote of MY Post in UNDER 3 MINUTES… This Smart Dust Patent Could Force Them to Answer to the World THIS NEEDS TO GO VIRAL. If this thread explodes, they will have no
@TrueOnX - Noah B. Price
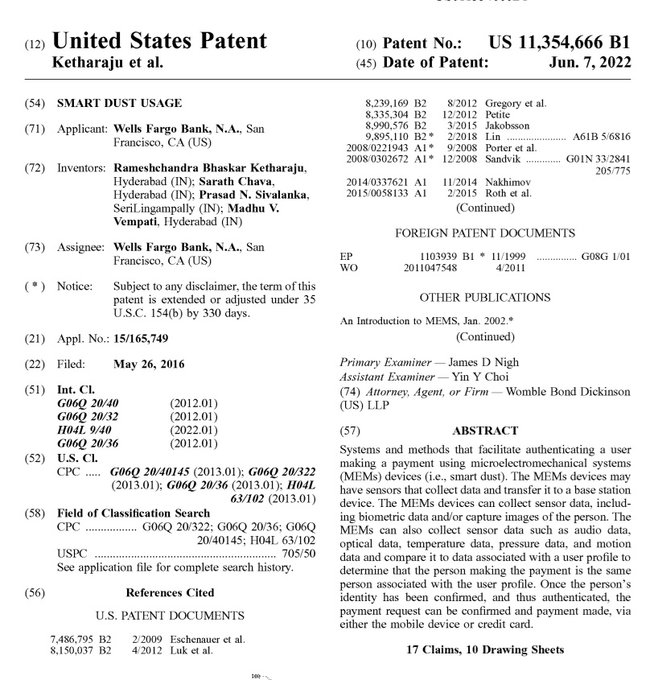
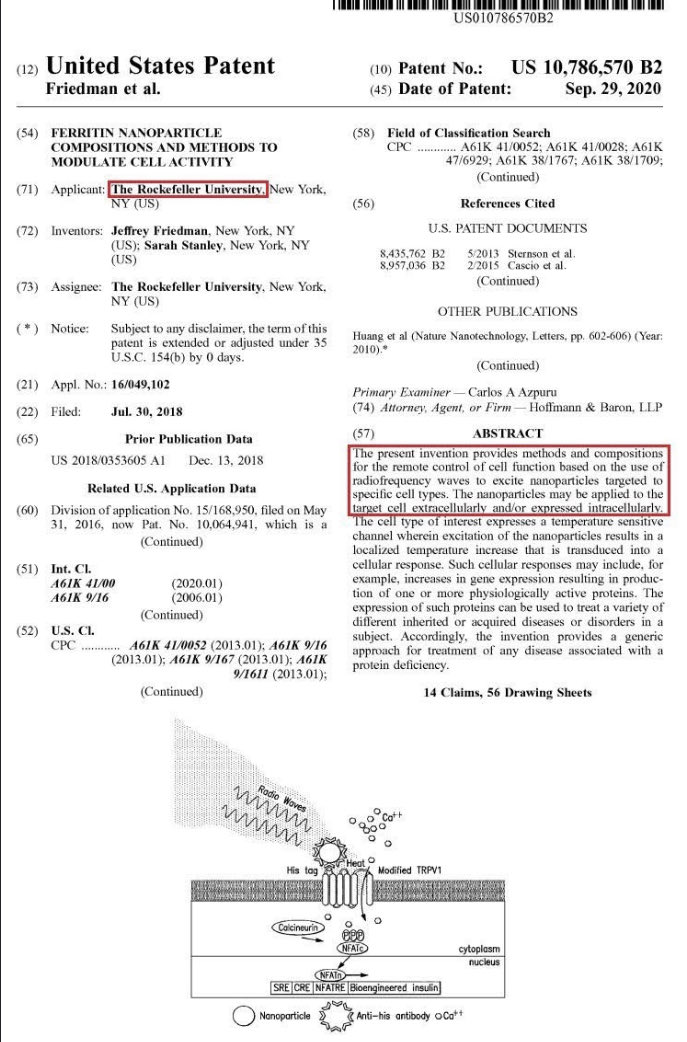
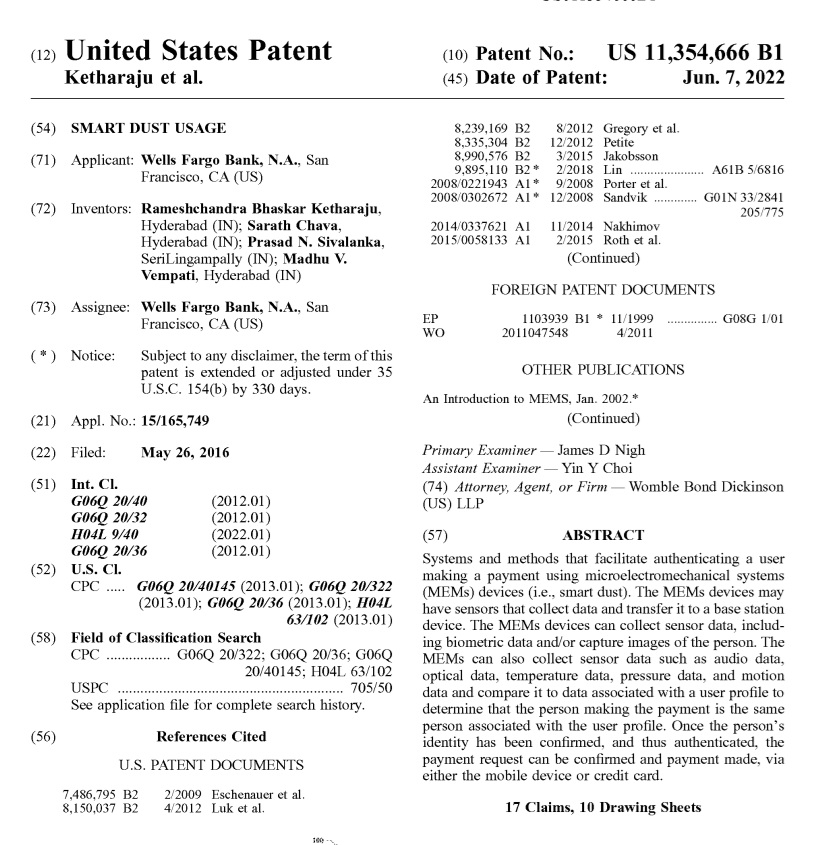
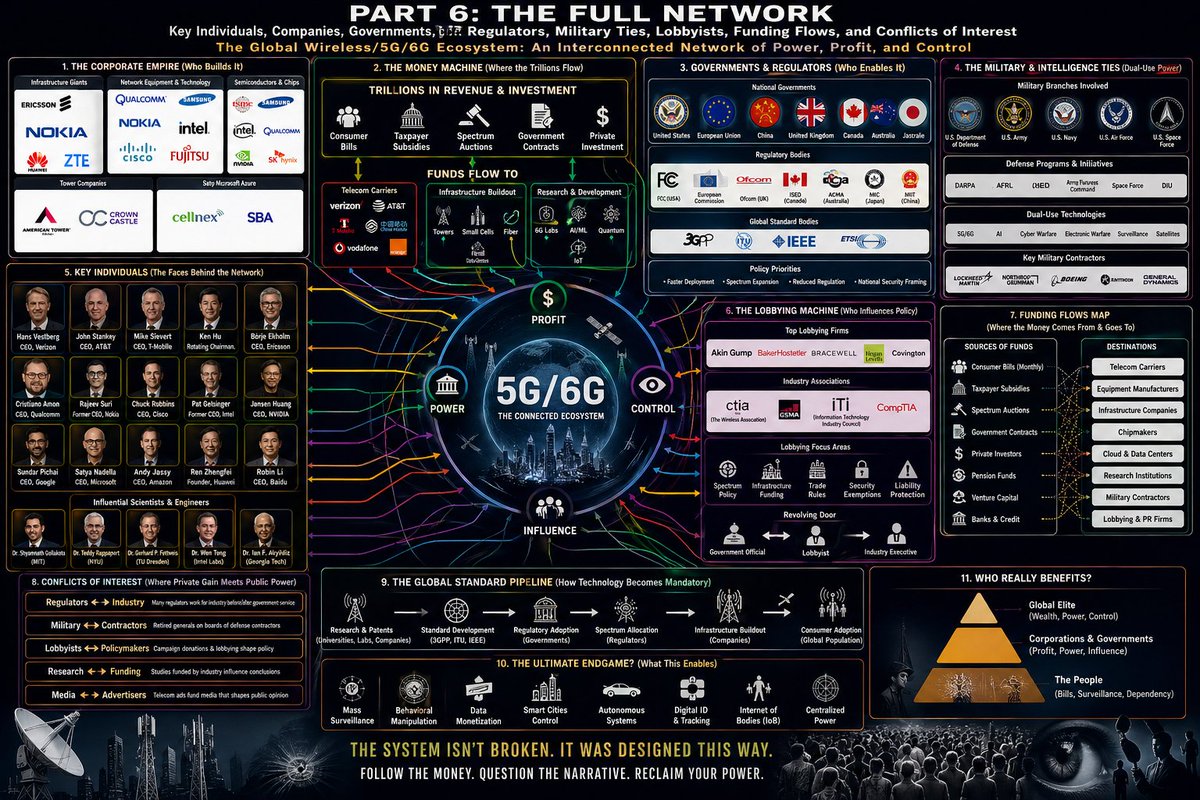
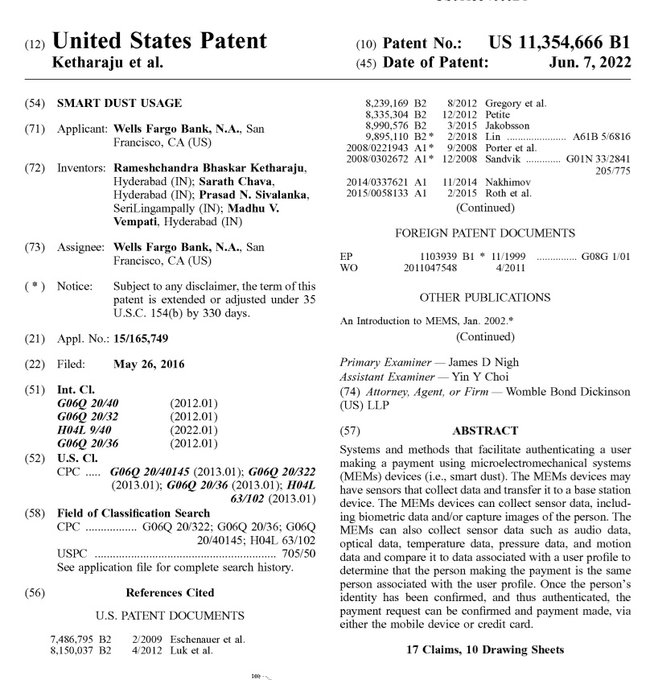
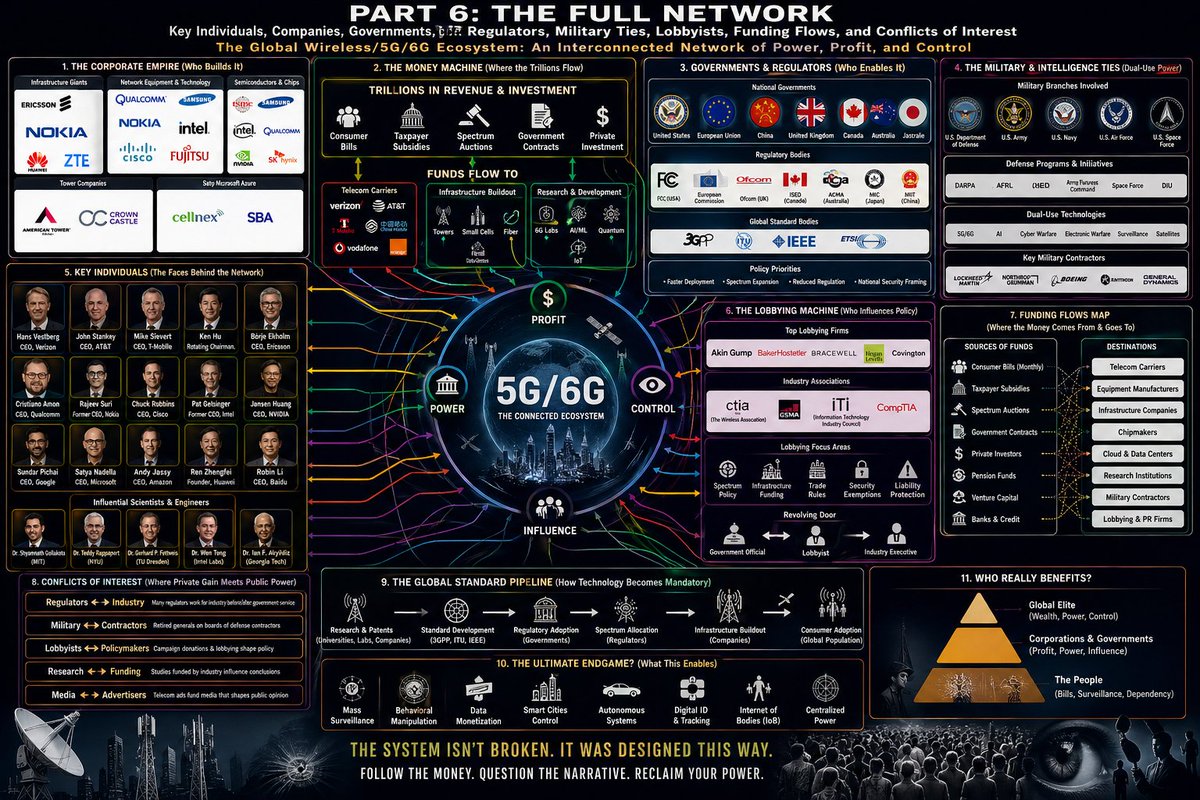
🚨 Part 2/10: Wells Fargo NIGHTMARE! This "Smart Dust" Nightmare Was Born as a Pentagon Battlefield Weapon; DARPA Turned the Air Into an Invisible Spy Network, and Wells Fargo Just Patented It for Your Bank Account https://t.co/NxIJI1ktq3 Can you believe how deep this goes? The same Wells Fargo that had their customer service account jump into a quote of my post in under 3 minutes... on a complaint that never even tagged them; owns a patent built on technology created for war. This isn't a bank inventing better fraud protection. This is military surveillance tech, designed to hunt human beings on the battlefield, now being adapted to control your everyday money and movements. The Real Birth of Smart Dust: RAND Corporation and DARPA (1992 Onward) The concept didn't start in some fintech lab. It emerged from a RAND Corporation workshop in December 1992 focused on future military revolutions. From there, DARPA (the Defense Advanced Research Projects Agency) poured funding into it. DARPA is the Pentagon's high-risk research arm; the same one behind the early internet, stealth fighters, and GPS. They saw the potential for total domination through invisible sensors. Professor Kris Pister at UC Berkeley led the charge. The goal: create cubic-millimeter-sized devices called "motes" or smart dust; tiny enough to float on the wind like ordinary dust, packed with sensors, computing power, and communication systems. These could be dropped by the thousands or millions from aircraft or drones over enemy territory. They would self-organize into networks, monitor everything in real time, and send data back without detection. Direct proof and original sources: https://people.eecs.berkeley.edu/~pister/SmartDust/ (Kris Pister's official project page, detailing the DARPA-funded work) https://people.eecs.berkeley.edu/~pister/papers/2001%20Smart%20Dust%20Motes.pdf (Technical paper on the motes) https://www.rand.org/content/dam/rand/pubs/monograph_reports/MR1307/MR1307.chap2.pdf (RAND analysis of military smart dust applications) https://people.eecs.berkeley.edu/~pister/SmartDust/SmartDustBAA97-43-Abstract.pdf (DARPA BAA document for the project) Early prototypes could sense temperature, vibration, sound, light, magnetic fields, and movement. Military tests included dropping motes in desert areas to track vehicles for the U.S. Marine Corps. The dust would detect, network, and relay data via UAVs. This was battlefield awareness at a scale never seen before; every inch of ground turned into an intelligent, spying entity. How This War Tech Landed in Wells Fargo's Hands Fast forward. In 2016, Wells Fargo files for US11354666B1. Granted June 7, 2022. The patent takes the exact same MEMS smart dust concept; airborne, swarming, self-networking motes... and applies it to payment authentication. During a transaction, these particles activate, surround you, read your heart rate, body temperature, voice patterns, motion, facial images, electromagnetic fields, and more. They compare it all to your "user profile" and approve or deny your money. Full patent: https://patents.google.com/patent/US11354666B1/en The technology is a direct descendant. Military dust for tracking soldiers and vehicles becomes bank dust for tracking customers. No device needed. The air itself becomes the verifier. Wells Fargo now claims ownership over this idea for financial control. The Inhalation and Health Horror No One Wants to Discuss These motes are designed to stay suspended in the air. They're microscopic. That means they can be inhaled; deep into your lungs, potentially crossing into your bloodstream or nervous system. What happens when thousands or millions of these synthetic particles enter human bodies on a regular basis? Long-term studies on intentional environmental release simply do not exist at scale. Potential risks include chronic respiratory inflammation, tissue damage, interference with biological electrical signals, bioaccumulation, and unknown neurological effects. Children, with developing lungs and higher breathing rates, face even greater exposure in everyday environments. Key sources on these risks: https://brite.ikeinstitute.org/brite_innovation_review_issue_31_winter_2023/are_we_all_breathing_smart_dust (Detailed breakdown of inhalation dangers and public health questions) https://en.wikipedia.org/wiki/Smartdust (Section on health uncertainty and respiratory concerns) https://www.airuniversity.af.edu/Portals/10/CSAT/documents/researchpapers/2007/bh2007_dickson.pdf (Military acknowledgment of nanosized particle risks) This creates a world where the very act of breathing near a bank terminal or in a "smart" environment could expose you to corporate-owned surveillance particles. Your family dinners, your kids playing outside, crowded public spaces; all potentially laced with this tech. Who's Steering This Entire Operation? DARPA and the U.S. Military; The originators. They develop god-like surveillance tools first for war, then the tech migrates to corporations. Wells Fargo; The current face. A massive bank with repeated scandals now positioning itself as owner of ambient biometric systems. Their lightning-fast social media monitoring (that 3-minute reply on my patent post) proves they know how radioactive this patent is and are ready to shut down discussion. Defense Contractors and Big Tech Companies like Intel, Qualcomm, and IBM have parallel MEMS and sensor work. The same RF networks needed for smart dust communication overlap with the 2G-7G and satellite grids blanketing the planet. Global Elites and Insiders: Those who understand the full spectrum; surveillance, radiation exposure, societal control... build luxury bunkers and compounds while pushing this on the public. This isn't isolated. It ties straight into the wireless radiation environment we're all living in. Smart dust relies on those same frequencies to network and transmit. The air we're told is "progress" is becoming a layered grid of monitoring and energy. This reality hits hard because it strips away the last illusions of privacy and bodily autonomy. Every breath, every heartbeat, every step could feed into systems owned by banks and governments. It raises questions about consent, long-term health for entire generations, and what kind of future we're actually building. If they patented the air for payments today, what comes next; environmental release for "security," constant biometric taxation of existence itself? The speed of Wells Fargo's response to public discussion shows they feel the pressure. This patent exposes a vision of control that should alarm anyone who values freedom. Quote this with Part 1 and the original patent post. Share it relentlessly. Part 3 will expose the full EMF / wireless radiation reality, the cancer clusters, Starlink involvement, and how it all interconnects with smart dust. Full links. This is only getting more intense. Wake everyone up.
@TrueOnX - Noah B. Price
🚨 Part 3/10: Wells Fargo NIGHTMARE They're Microwaving All of Us With 2G Through 7G Towers, Starlink Satellites, and the Exact Same RF Networks That Smart Dust Needs to Spy on Your Body And the Cancer Clusters in Children Prove It cbsnews.com/news/cell-towe… This connects everything. Wells Fargo's smart dust patent (US11354666B1 full link: https://patents.google.com/patent/US11354666B1/en) doesn't work in isolation. Those airborne MEMS motes need to communicate, network, and transmit your biometrics back to the bank. They rely on the same radiofrequency (RF) electromagnetic fields blasting from cell towers, 5G/6G antennas, and thousands of Starlink satellites overhead. They're not just patenting the air you breathe for payments. They're blanketing the entire planet in microwave radiation that turns the atmosphere into one giant surveillance and energy grid; while real people, especially children, are getting sick. This is the full horror of what "progress" actually looks like. The RF/EMF Reality We're All Being Cooked In... Every day, you're exposed to radiofrequency radiation from: Cell towers and small cells. (densifying everywhere for 5G/6G) Phones, Wi-Fi, smart devices. Starlink's massive satellite constellation beaming down signals. RF is non-ionizing, but that doesn't mean it's safe at constant, cumulative low levels. It can cause oxidative stress, DNA damage, inflammation, and disrupt biological processes without heating tissue like a microwave oven. Official Classifications and Major Studies The International Agency for Research on Cancer (IARC) classified RF-EMF as Group 2B possibly carcinogenic to humans in 2011, based on increased glioma and acoustic neuroma risks from heavy cellphone use. Same category as lead, DDT, and pickled vegetables; but they called for more research. Full IARC press release: https://www.iarc.who.int/wp-content/uploads/2018/07/pr208_E.pdf The U.S. National Toxicology Program (NTP) one of the largest animal studies ever; found clear evidence of tumors (malignant schwannomas of the heart) in male rats exposed to cellphone-level RF. Also brain gliomas and adrenal tumors. The Ramazzini Institute in Italy replicated similar findings at lower, environmental levels closer to real cell tower exposures; increases in the exact same rare heart tumors and brain cancers. European Parliament 5G Report (2021) by Dr. Fiorella Belpoggi (Ramazzini Institute): For lower 5G frequencies (450-6000 MHz): probably carcinogenic, clear effects on male fertility, possible on female fertility and development. Higher mmWave bands (24-100 GHz) have almost zero adequate long-term studies; we're the experiment. Full report: https://www.europarl.europa.eu/RegData/etudes/STUD/2021/690012/EPRS_STU(2021)690012_EN.pdf Children Are Being Hit Hardest... Kids have thinner skulls, smaller heads, higher water content in brains, and faster cell division. They absorb far more radiation; up to 10 times in skull bone marrow. Their developing nervous systems are more vulnerable. Real-world horror stories: Ripon, California (Weston Elementary): Multiple children and teachers diagnosed with rare cancers. Parents linked it to a cell tower on campus. The tower was eventually removed after public pressure. CBS News coverage: https://www.cbsnews.com/news/cell-tower-shut-down-some-california-parents-link-to-several-cases-of-childhood-cancer/ Other clusters reported near towers in Missouri, and studies showing elevated risks in areas with high RF exposure. Independent reviews show rising concerns for childhood leukemia, brain tumors, and developmental issues near base stations. Children playing outside or in schools near towers get constant exposure during critical growth windows. Starlink's Role in Frying the Skies: Elon Musk's Starlink constellation (thousands of satellites, planning tens of thousands) adds another layer. Unintended electromagnetic radiation leaks from the satellites have been detected by radio astronomers; interfering with observations and adding to the global RF soup. Key paper on Starlink unintended radiation: https://www.aanda.org/articles/aa/abs/2023/08/aa46660-23/aa46660-23.html (and follow-ups showing even higher leaks from newer satellites). While user terminals are the main local source, the sheer density of satellites creates constant low-level exposure from above. Combined with ground towers, it's a full 3D radiation cage. The Elite Double Standard; Bunkers With Radiation Shielding While they roll this out on the public, billionaires build luxury doomsday bunkers with EMP/radiation protection, air filtration, and self-contained environments. Mark Zuckerberg's Hawaii compound with massive underground bunker. Others like Bill Gates, Peter Thiel, and Silicon Valley elites doing the same. They prep for societal collapse, EMP events, or the very environmental/health fallout their technologies help create. Reports: Multiple outlets document luxury bunkers designed against electromagnetic threats. How This Ties Back to Smart Dust: Those MEMS motes from Wells Fargo's patent need RF to form networks, transmit data, and function in real time. The same infrastructure "cooking" us provides the backbone for ambient biometric surveillance. Your body signals harvested by dust; sent over the same towers and satellites bathing you in RF. This is disgusting beyond words. hildren getting cancer clusters while banks patent invisible spy particles and satellite companies blanket the planet. No real consent. Inadequate long-term studies on cumulative effects. Industry influence on safety guidelines. And rapid corporate monitoring (like that 3-minute Wells Fargo reply) whenever anyone connects the dots on the patent. This should shake you to your core. Your kids' playgrounds, schools, bedrooms; all potentially zones of experimental exposure. Future generations inheriting higher cancer risks, fertility issues, neurological problems. All for faster downloads, "secure" payments via dust, and corporate profits. Quote this with Parts 1 and 2 plus the original patent post. Share it everywhere. Part 4 will expose the full who’s at the helm picture; the banks, DARPA contractors, Big Tech, governments, and elites profiting while we pay the price with our health and freedom. Full links. THIS IS GOING TO BE HUGE! PLEASE SHARE THIS WITH EVERYONE! Wake the world up.
@TrueOnX - Noah B. Price
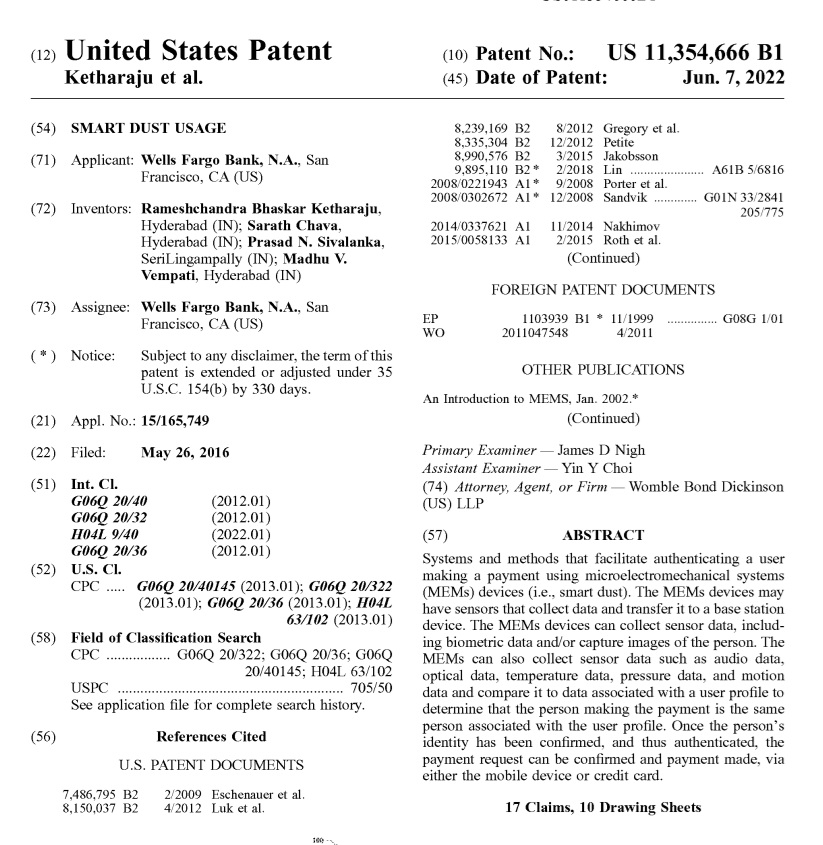
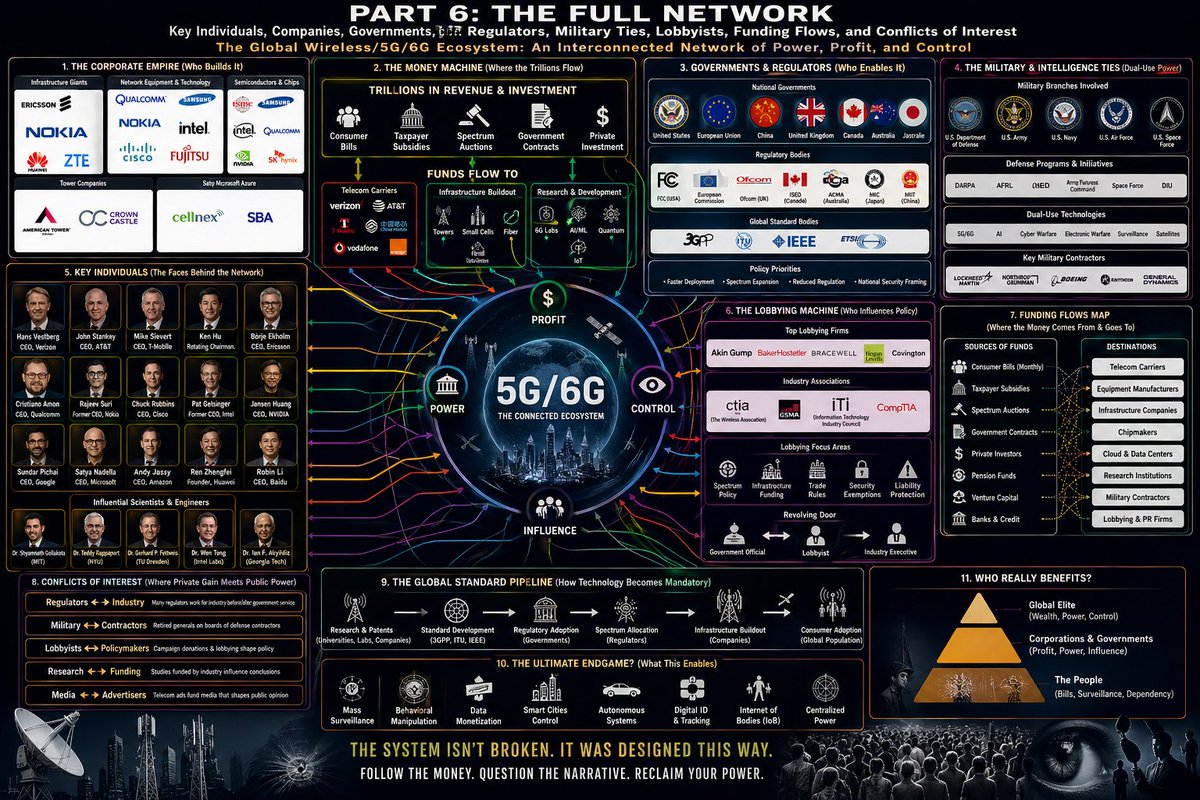
🚨 Part 4/10: Wells Fargo NIGHTMARE Who's Really Pulling the Strings? The Banks, DARPA, Big Tech, Governments, and Elites Profiting from Smart Dust, Radiation Grids, and Total Surveillance; While Building Escape Bunkers for Themselves https://t.co/ODYt9gqlSt This is the part that should make your jaw drop and your stomach turn. Everything we've exposed so far: Wells Fargo's US11354666B1 smart dust patent (full link: https://patents.google.com/patent/US11354666B1/en), the instant 3-minute customer service reply to a quote of my post, the DARPA military roots, and the RF/EMF microwave blanket from 2G-7G towers and Starlink; isn't random "innovation." It's a coordinated system run by a small network of powerful players who profit enormously while the rest of us breathe the particles and radiation. Wells Fargo and Big Banking: Monetizing Your Biology Wells Fargo isn't a passive player. They actively filed for and secured ownership of airborne biometric smart dust for payments. A bank with a long history of scandals (fake accounts, predatory lending, massive fines) now wants to control access to your money through invisible swarms reading your heartbeat. Their lightning-fast social media monitoring shows they treat public discussion of this patent as a major threat. This fits a broader banking push toward Central Bank Digital Currencies (CBDCs) and programmable money tied to digital IDs and biometrics. Your body becomes the wallet. No dust approval? No transaction. DARPA and the Military-Industrial Complex The Original Architects As covered in Part 2, DARPA funded the foundational smart dust work in the 1990s through UC Berkeley and RAND Corporation for battlefield dominance. Key links: https://people.eecs.berkeley.edu/~pister/SmartDust/ https://www.rand.org/content/dam/rand/pubs/monograph_reports/MR1307/MR1307.chap2.pdf https://www.airuniversity.af.edu/Portals/10/CSAT/documents/researchpapers/2007/bh2007_dickson.pdf (military paper on smart dust future) The same agency develops "Neural Dust" for implantable monitoring. Military tech always trickles down: surveillance first for enemies, then for citizens via corporations. Defense contractors benefit from endless funding, then license or sell the tech. Big Tech: Building the Hardware and Networks Companies deeply involved in MEMS sensors, RF tech, and related systems include: Analog Devices, STMicroelectronics, Bosch Sensortec, Texas Instruments, Qualcomm, Intel, and IBM are leaders in miniaturized sensors and smart dust-enabling tech. SpaceX/Starlink: providing the satellite layer for global connectivity that smart dust networks would use. These firms profit from denser 5G/6G rollouts while supplying the exact components for ambient surveillance. Conflicts of interest run deep... many have government contracts and lobby heavily. Governments and Regulators - Captured and Enabling The FCC (U.S.) and ICNIRP (international) set RF exposure guidelines based on outdated 1990s thermal-only models, ignoring non-thermal biological effects. Courts have criticized the FCC for failing to address thousands of studies on harm. Key evidence of issues: https://ehtrust.org/the-international-commission-on-non-ionizing-radiation-protection-conflicts-of-interest-corporate-capture-and-the-push-for-5g/ (ICNIRP industry ties) https://pmc.ncbi.nlm.nih.gov/articles/PMC9576312/ (scientific critique of FCC/ICNIRP limits) Court ruling: https://law.justia.com/cases/federal/appellate-courts/cadc/20-1025/20-1025-2021-08-13.html (FCC ordered to reconsider evidence) Regulators often have revolving-door relationships with the telecom industry they oversee. They approve dense tower deployments near schools while independent science screams for caution. The Ultra-Wealthy Elites: Prepping Bunkers While Pushing the Agenda This is the most infuriating layer. Tech and finance billionaires who invest in or benefit from these technologies are simultaneously building luxury doomsday bunkers with radiation shielding, air filtration, and self-sufficiency: Mark Zuckerberg; Massive Hawaii compound with huge underground bunker. Peter Thiel, Sam Altman, Bill Gates (rumored multiple bunkers), and others stockpiling remote fortified properties. Reports: https://www.bbc.com/news/articles/cly17834524o https://www.businessinsider.com/ceo-doomsday-prepper-bunkers-shelters-guns-zuckerberg-altman-2025-7 https://robbreport.com/shelter/celebrity-homes/wealthy-homeowners-building-luxury-survivalist-bunkers-1236905429/ They understand the risks of societal instability, health fallout from widespread tech deployment, or environmental consequences; yet they accelerate the very systems creating those risks for profit and control. While your kids face potential cancer clusters near towers, they retreat underground. The Interconnected Horror: This isn't conspiracy... it's documented incentives and actions. DARPA develops the surveillance dust to Big Tech builds the RF backbone and sensors to Banks like Wells Fargo patent civilian applications for profit and Regulators rubber-stamp with industry influence then Elites insulate themselves. The result? A world where the air you breathe, the signals around you, and your own body become assets for control and revenue. Privacy erased. Health gambled. Freedom conditional on compliance. This should enrage you. A handful of unaccountable players treat the planet and its people as their experimental playground while securing their own exits. The rapid Wells Fargo reply to my patent post? Just one small sign they know how fragile their narrative is if enough people connect these dots. Quote this entire series with the original patent post. Share it far and wide. Part 5 will dive into the long-term health devastation; fertility collapse, neurological damage, cancer trends, and what independent scientists are desperately warning about. This thread is exposing the full machine. Stay with it. The truth is devastating but necessary. Wake everyone up.
@TrueOnX - Noah B. Price
🚨 Part 5/10: Wells Fargo NIGHTMARE The Devastating Health Toll, Collapsing Fertility, Brain Damage, Rising Cancer in Kids, and the Independent Scientists Screaming Warnings While the System Ignores Them https://t.co/9tKUXwJU1g This is the human cost. The part that should break your heart and fuel your rage. Wells Fargo's smart dust patent (US11354666B1 full link: https://patents.google.com/patent/US11354666B1/en) adds invisible particles that could be inhaled while the entire RF grid (the same frequencies the dust needs to operate) bathes us 24/7. DARPA's military tech, Big Tech's networks, banks' profit schemes, and elite bunkers; all built on a foundation that's quietly destroying our bodies, especially the next generation. The evidence from independent research is overwhelming, yet regulators and corporations downplay or bury it. Fertility Collapse: We're Sterilizing Ourselves Male sperm counts have plummeted globally over decades. Multiple meta-analyses link RF-EMF exposure to reduced sperm motility, viability, concentration, and DNA damage through oxidative stress. Recent studies show clear effects: 2024 systematic review and meta-analysis found RF-EMF associated with reduced pregnancy rates and sperm count in animal models, with moderate certainty. Human sperm in vitro also shows vitality drops. Full study: https://www.sciencedirect.com/science/article/pii/S0160412024000953 2025 rat study on 3.5 GHz (5G mid-band) and 24 GHz (mmWave): Significant drops in sperm motility, concentration, and viability after prolonged exposure. Increased apoptosis (cell death) genes and inflammation markers. https://www.mdpi.com/2227-9059/13/10/2471 Umbrella review of systematic reviews: RF-EMR significantly reduced sperm motility and viability, lowered testosterone, with oxidative stress as the mechanism. Occupational exposure linked to higher miscarriage and congenital anomaly risks. https://link.springer.com/article/10.1186/s43043-025-00258-1 This isn't abstract. Declining fertility rates worldwide coincide with wireless rollout. Smart dust would add another layer; potential particle inhalation directly affecting reproductive tissues. Neurological Damage: Rewiring Brains, Especially in Children RF exposure penetrates skulls and affects developing brains. Children absorb more radiation. Links include sleep disruption, headaches, cognitive deficits, behavioral issues, and potential long-term neurodegeneration. Study on home RF levels and infants: Higher wireless radiation correlated with poorer gross/fine motor skills, problem-solving, and personal-social development. https://www.ehn.org/wireless-radiation-child-development Reviews highlight vulnerability of children's brains to EMFs, with concerns for neurodevelopmental disorders. The smart dust biometrics (heart rate, motion, voice) combined with constant RF creates a feedback loop of exposure and monitoring. Cancer Trends and Clusters - The Body Count is Rising While some official reviews claim "no conclusive link," independent and animal studies tell a different story: NTP study: Clear evidence of heart and brain tumors in rats at cellphone-level exposures. Ramazzini Institute: Tumors at lower environmental levels. Childhood clusters near towers (e.g., Ripon, CA) led to removals after multiple rare cancers. Parents and local reports connect the dots. Trends show increases in certain brain tumors and leukemia in some populations coinciding with wireless expansion. Independent scientists warn that current guidelines ignore non-thermal effects and cumulative exposure.Independent Scientists Sounding the Alarm Many researchers outside industry influence call for moratoriums: BioInitiative Report and others compile thousands of studies showing biological harm below safety limits. European Parliament reports and expert panels highlight probable carcinogenicity for some bands, fertility risks, and the need for precaution. Full 2021 EPRS study: https://www.europarl.europa.eu/RegData/etudes/STUD/2021/690012/EPRS_STU(2021)690012_EN.pdf They face funding cuts, censorship, or attacks for challenging the "safe" narrative pushed by ICNIRP/FCC (criticized for industry ties). The Generational Horror We're conducting a massive, uncontrolled experiment on humanity. Kids in schools near towers, families in smart homes, entire populations under satellite constellations; all while banks patent swarms that could lodge in lungs or brains. Future generations face lower fertility, higher chronic disease, altered development. The elites bunker down with filtered air and shielding. We get the experiment. This is gut-wrenching... Your children's future health traded for faster internet, "secure" payments via dust, and corporate control. The 3-minute Wells Fargo reply to my patent post? Seem to be quite quiet now. IF NOBODY ELSE IN THIS WORLD WILL TAKE ON THE BANKERS, THEN I WILL! They're protecting a system with this human cost attached. THEY HAVE ALREADY CAUSED ENOUGH HARM TO ALL OF US SINCE THE DAWN OF TIME, WHAT ELSE DO WE HAVE TO LOSE? I WILL STAND FOR YOU, BUT DO NOT LEAVE ME STANDING ALONE. I HAVE BEEN AT THIS FOR DECADES, BANNED FROM BANKING FOR YEARS, BUSINESS DESTROYED, LIFE DESTROYED CONSTANTLY BECAUSE OF MY COMMITMENT TO GOD AND HUMANITY. I WILL NEVER STOP FIGHTING FO YOU ALL! PLEASE SHARE THIS! Quote this with previous parts and the original patent post. Part 6 will expose solutions, resistance, what you can do, and how this all leads to total digital/biological enslavement if unchecked. Full links. This thread is waking people up. Keep pushing. The horrors are real, but so is the fight. I AM NOT SUICIDAL AND I HAVE ALREADY DIED MANY TIMES. - No Weapon Formed Against Me Shall Prosper. I LOVE YOU ALL! HOORAHHH! 🇺🇸 GOD BLESS YOU ALL! 🙏 ATTACHED THREAD HAS 6K LIKES ALREADY! WE ARE GAINING TRACTION!
@TrueOnX - Noah B. Price
🚨 Part 6/10: Wells Fargo NIGHTMARE This All Leads to Total Digital and Biological Enslavement - Programmable Money, Digital IDs Tied to Your Body, and a World Where You Own Nothing and Need Permission to Exist https://t.co/I6WwltsmZa The pieces are falling into place in the most terrifying way possible. Wells Fargo's "smart dust patent US11354666B1" (full link: https://patents.google.com/patent/US11354666B1/en) isn't just about convenient payments. Combined with the DARPA military roots, the RF/EMF grid we're all being microwaved in, the cancer and fertility damage, and the elites hiding in bunkers... this is the infrastructure for a future where your biology, your money, and your every movement are locked into a permission-based control system. If we let this continue unchecked, it becomes full digital and biological enslavement. The Endgame: CBDCs + Biometrics + Smart Dust = Total Control Central Bank Digital Currencies (CBDCs) are being rolled out worldwide. Unlike cash, they are programmable. Governments and banks can decide what you can buy, when, where, and under what conditions. Tie that to biometric authentication via Wells Fargo-style smart dust, and your heartbeat or body signature becomes your wallet. No approval from the swarm? No transaction. Step out of line (wrong political view, wrong carbon score, wrong social credit)? Funds frozen or restricted. (I have dealt with this for the past 3 years.) This merges with "digital IDs" (already advancing in Europe, Canada, Australia, and U.S. pilots) that link your biometrics, health data, vaccination status, and behavior. Smart dust makes it ambient and constant; no need for a phone or scan. The air itself verifies and tracks you. Key documents showing the agenda: https://atlanticcouncil.org/cbdctracker/ (CBDC tracking worldwide - over 100 countries exploring) https://imf.org/en/Topics/digital-money (IMF pushing digital currencies and IDs) https://weforum.org/agenda/2022/01/davos22-digital-id-digital-identity/ (World Economic Forum openly discussing "you'll own nothing and be happy" with digital IDs) The Resistance: Scientists, Lawsuits, and Growing Awareness. Independent scientists and groups are fighting back hard: The "BioInitiative Working Group" has compiled thousands of studies calling for major reductions in RF exposure. https://bioinitiative.org - Multiple lawsuits against the FCC for ignoring non-thermal effects. The U.S. Court of Appeals ruled the FCC must address the evidence. https://law.justia.com/cases/federal/appellate-courts/cadc/20-1025/20-1025-2021-08-13.html - European groups and the "5G Appeal" (signed by hundreds of scientists) demand a moratorium on 5G/6G rollout until proven safe. https://5gappeal.eu - Parents in cancer cluster areas (like Ripon, CA) successfully forced tower removals through public pressure and local action. People are waking up. Local ordinances against towers near schools are passing in more places. Communities are choosing wired alternatives. Awareness of smart dust patents like Wells Fargo's is spreading exactly because of threads like this. What You Can Actually Do Right Now: Practical Resistance 1. Minimize RF Exposure: Use wired internet and Ethernet where possible. Keep phones on airplane mode or away from body. Turn off Wi-Fi at night. Use speakerphone. Measure your home with an RF meter (affordable ones on Amazon). 2. Support Local Pushback: Attend city council meetings against new towers. Join or donate to groups like "Environmental Health Trust" (https://ehtrust.org) or "Physicians for Safe Technology" (https://mdsafetech.org). 3. Bank and Tech Alternatives: Move away from big banks like Wells Fargo toward credit unions or privacy-focused options. Use cash as much as possible. Reject unnecessary biometric apps. 4. Spread This Thread: Share Parts 1-6 aggressively with the original patent post. The faster this goes viral, the harder it is for them to ignore. 5. Demand Accountability: Contact regulators. Support independent research funding. Push for laws banning airborne smart dust deployment without public consent and long-term safety studies. The Enslavement Warning - This Is the Point of No Return... If smart dust networks, constant RF grids, CBDCs, and digital IDs fully merge, you won't just lose privacy. You'll lose autonomy. Your body becomes a node in their system. Your children grow up in an environment where the air reads them, the towers cook them, and the bank decides their future. The same elites building bunkers will control the grid from safety while the rest of us live as managed biological assets. Wells Fargo's 3-minute jump on a quote of my patent post wasn't random. It was fear. They know what this patent represents if enough people see the full picture: the infrastructure of a control society dressed up as convenience and security. This should terrify you into action. Heart-breaking for the generations coming after us... It's happening in plain sight. Crazy how all the threads connect... Quote this entire series with the original patent post. Keep sharing. Part 7 will expose the global coordination - UN, WEF, WHO, and how this fits into broader "Great Reset" style agendas for total societal control. Full links. This is one of the most important threads you'll ever read or share. The fight is real. Wake everyone up. 👇 If nobody else will stand against the banks, then I will! But do not allow me to stand alone... SHARE THIS WORLDWIDE! I AM NOT SUICIDAL AND I HAVE ALREADY DIED MANY TIMES. - No Weapon Formed Against Me Shall Prosper. I LOVE YOU ALL! HOORAHHH! 🇺🇸 GOD BLESS YOU ALL! 🙏 ATTACHED THREAD HAS 6K LIKES ALREADY! WE ARE GAINING TRACTION!
@TrueOnX - Noah B. Price
🚨 Part 7/10: Wells Fargo NIGHTMARE The Global Machine - UN, WEF, WHO, and the Coordinated Push for Digital IDs, CBDCs, Smart Cities, and Biometric Control Under "Sustainable Development" Agendas https://t.co/XRyKcuHPSB This is the level where it all connects at the top. Wells Fargo’s "smart dust patent US11354666B1" (full link: https://patents.google.com/patent/US11354666B1/en) the one their customer service account jumped on in under 3 minutes when someone quoted "my post" isn’t a lone bank’s crazy idea. It fits perfectly into a worldwide framework being pushed by the most powerful global organizations on Earth. The UN, World Economic Forum (WEF), and WHO are openly building the infrastructure for a world of constant biometric surveillance, programmable money, and “you’ll own nothing and be happy” living; all sold as saving the planet and making life better. The Great Reset and Fourth Industrial Revolution - WEF’s Blueprint In June 2020, Klaus Schwab and the WEF launched "The Great Reset" as a response to COVID-19. It calls for a fundamental overhaul of capitalism into a “stakeholder economy,” using the "Fourth Industrial Revolution" (4IR) technologies that blur the lines between physical, digital, and biological spheres. This includes merging human bodies with technology; exactly what smart dust does by harvesting your heart rate, temperature, and biometrics from the air. Direct sources: https://www.weforum.org/agenda/2020/06/now-is-the-time-for-a-great-reset/ (Original Great Reset announcement) https://www.weforum.org/stories/2016/01/the-fourth-industrial-revolution-what-it-means-and-how-to-respond/ (Schwab on 4IR fusing biology and tech) https://en.wikipedia.org/wiki/Great_Reset (Overview of the initiative) The WEF pushes "digital identity" as essential for this new world. Their reports talk about interoperable digital IDs that give governments and corporations seamless access to your data for “efficiency” and “sustainability.” https://www.weforum.org/publications/reimagining-digital-id/ (WEF report on reimagining digital ID) https://intelligence.weforum.org/topics/a1G0X000005JJGcUAO (WEF Strategic Intelligence on Digital Identity) "UN Agenda 2030" and “Legal Identity for All” The United Nations’ "Sustainable Development Goals (SDGs)" Agenda 2030 includes: Target 16.9: “By 2030, provide legal identity for all, including birth registration.” In practice, this means pushing biometric digital IDs worldwide. Over 100 countries are implementing them, often with World Bank support. The UN has its own "UN Digital ID" system for staff, using blockchain and biometrics, and promotes similar systems globally. https://unsceb.org/topics/un-digital-id (UN Digital ID program) https://www.m2sys.com/blog/biometric-resources/the-un-plans-to-implant-everyone-with-a-biometric-id-by-2030/ (UN biometric ID push by 2030) https://sdgs.un.org/goals (Official UN SDGs, including legal identity target) This “inclusion” sounds good until you realize it creates a system where access to banking, healthcare, travel, and food can be tied to compliance; perfect for smart dust authentication. WHO’s Digital Health Strategy: Biometrics and Global Health Control The WHO’s Global Strategy on "Digital Health 2020-2025" emphasizes digital IDs, health data sharing, and biometric authentication for “trust” in health systems. It aligns with pandemic preparedness and vaccine tracking; using the same biometric tech. https://www.who.int/docs/default-source/documents/gs4dhdaa2a9f352b0445bafbc79ca799dce4d.pdf (WHO Digital Health Strategy) Smart Cities and 15-Minute Cities - The Physical Cage WEF and partners promote “smart cities” with constant sensor networks, digital IDs, and restricted movement zones (15-minute cities). Everything tracked for “sustainability” and “equity.” https://www.weforum.org/stories/2021/07/being-smart-about-smart-cities-a-governance-roadmap-for-digital-technologies/ (WEF smart cities governance) https://globalsmartcitiesalliance.org/ (G20 Global Smart Cities Alliance) The Full Horror of Coordination: UN sets the sustainable development goals and WEF provides the corporate/tech blueprint via Great Reset and 4IR then WHO handles the health/biometric data layer; Banks like Wells Fargo implement the payment authentication (smart dust) and finally Governments enforce it through CBDCs and digital IDs. All while the same elites attend Davos, fly private, and build radiation-shielded bunkers. This is a top-down vision of humanity as manageable data points in a “resilient” system. Your body’s signals owned by a bank patent. Your movements tracked in smart cities. Your money programmable. Your health data shared globally. All justified as fighting climate change, inequality, and future pandemics. The rapid Wells Fargo reply to discussion of their patent shows they know how explosive this full picture is. If enough people see how one bank’s dust connects to global agendas, the narrative crumbles. This should enrage and motivate you. Generations are being funneled into a control grid sold as progress. Privacy, bodily autonomy, and true freedom are being traded for “convenience” and “sustainability.” TUNE IN TILL THE END OF THE THREAD Where you will be provided with step by step actionable paths forward to finally put an END to this once and for all! Quote this with all previous parts and the original patent post. Share without hesitation. Part 8 will expose the endgame consequences... what a fully implemented world of smart dust, RF grids, CBDCs, and global IDs actually looks like for you and your family. Full links. This thread is devastatingly important. Keep it going. Wake the planet up. 👇 If nobody else will stand against the banks, then I will! But do not allow me to stand alone... SHARE THIS WORLDWIDE! I AM NOT SUICIDAL AND I HAVE ALREADY DIED MANY TIMES. - No Weapon Formed Against Me Shall Prosper. I LOVE YOU ALL! HOORAHHH! 🇺🇸 GOD BLESS YOU ALL! 🙏 ATTACHED THREAD HAS 6K LIKES ALREADY! WE ARE GAINING TRACTION! The attached video is a Viewer Discretion Advised... BUT YOU NEED YOU KNOW! The truth is not comfortable, but it is required if we are going to make it out of this alive. THESE ARE THE PEOPLE IN CONTROL 👇
@TrueOnX - Noah B. Price
🚨 Part 8/10: Wells Fargo NIGHTMARE! A Concrete Vision of the Fully Deployed System - How Smart Dust, RF Saturation, CBDCs, and Global Digital IDs Create a Locked-In Existence With No Real Escape https://t.co/9FMpFMntXB The infrastructure is already being assembled piece by piece. In the completed version of this system, daily life operates under seamless, inescapable layers of control that make previous forms of tyranny look primitive. You leave your apartment in a smart city. The building’s embedded sensors, combined with airborne MEMS particles operating under frameworks like Wells Fargo’s patented approach in "US11354666B1" (https://patents.google.com/patent/US11354666B1/en), have already logged your sleep patterns, stress markers, and movement overnight. As you step onto the street, nearby 6G small cells and Starlink overhead beams maintain constant connection to your digital profile. A swarm activates at the transit gate, reads your unique biometric signature, and cross-checks it against your real-time social compliance score, health data, and carbon allocation. One mismatch; perhaps from a flagged online comment or exceeding your weekly travel limit... and the gate stays locked. No appeal in the moment. You miss work. Your employer’s system notes the absence. Programmable Money and Behavioral Enforcement: CBDCs, advanced by institutions like the European Central Bank under Christine Lagarde and the Federal Reserve’s digital dollar pilots, function as dynamic tools. Every transaction is conditional. Buy meat above your personal climate quota? Denied. Attempt a purchase during a restricted timeframe based on your location history? Blocked. The smart dust layer makes this authentication invisible and continuous, removing any ability to use cash or anonymous alternatives in most urban zones. Key coordinating players: - Klaus Schwab and Yuval Noah Harari: at the World Economic Forum openly describe populations as manageable through fused biological-digital systems and predict humans will be hackable. https://www.weforum.org/agenda/2020/06/now-is-the-time-for-a-great-reset/ https://www.youtube.com/watch?v=3c4v9zR8Z8k (Harari on hackable humans and surveillance) - Christine Lagarde: (former IMF, now ECB) has pushed digital currencies as tools for “better policy targeting.” https://www.ecb.europa.eu/press/blog/date/2023/html/ecb.blog20231018~3c6e9e5f3e.en.html - BlackRock, Vanguard, and State Street: hold massive stakes in the telecom, defense, and banking firms implementing these networks, creating concentrated ownership that benefits from every tower deployment and patent licensing. Expanded Health and Developmental Impacts: Continuous exposure from phased-array 5G/6G antennas and growing Starlink density produces documented oxidative stress, blood-brain barrier permeability changes, and sperm DNA fragmentation in replicated studies. Children in high-density zones show measurable differences in attention, memory, and motor skills according to independent environmental health research. Inhaled micro-particles from expanded sensor networks add unknown accumulation in lung tissue and neural pathways over decades, with no mandatory pre-deployment human trials for widespread environmental release. Key additional players driving the hardware: - Qualcomm, Huawei, Ericsson, and Nokia: lead the 5G/6G rollout and sensor integration. - SpaceX: expands the satellite layer that eliminates any off-grid refuge. Social and Existential Consequences: Human relationships shift under permanent monitoring. Conversations carry risk when algorithms scan voice patterns and context for compliance. Creativity and dissent wither because every action feeds the permanent record. Entire populations adapt to self-censorship, knowing their access to food, transport, healthcare, and education depends on maintaining the right profile. Families watch younger members develop conditions that doctors attribute to “unknown environmental factors” while the deployment continues. The same networks enabling Wells Fargo’s dust authentication also support predictive policing and pre-crime flagging based on biometric deviations or movement anomalies. Opting out becomes practically impossible in daily economic participation. Rural areas face satellite coverage that maintains the same baseline exposure. The Insulated Class: Key figures and major investors in these systems maintain separate realities; private properties with advanced shielding, independent power, and restricted access... while the broader population tests the combined biological and digital experiment. This operational reality eliminates genuine choice. The air, the signals, the currency, and the identity system all converge into one enforcement mechanism. Wells Fargo’s rapid response to public discussion of their patent reflects awareness that widespread understanding of these connections threatens the rollout timeline. Quote this full series with the original patent post. Part 9 details specific disruption methods, legal pressure points, technological countermeasures, and parallel system building that can still alter this trajectory. Full exposure continues. Share this thread. 👇 If nobody else will stand against the banks, then I will! But do not allow me to stand alone... SHARE THIS WORLDWIDE! I AM NOT SUICIDAL AND I HAVE ALREADY DIED MANY TIMES. - No Weapon Formed Against Me Shall Prosper. I LOVE YOU ALL! HOORAHHH! 🇺🇸 GOD BLESS YOU ALL! 🙏 ATTACHED THREAD HAS 6K LIKES ALREADY! WE ARE GAINING TRACTION! BUT YOU NEED YOU KNOW! The truth is not comfortable, but it is required if we are going to make it out of this alive. Explore the attached War on Resonance Series for a very detailed presentation in parts 1-5 👇
@TrueOnX - Noah B. Price
🚨 Part 9/10: Wells Fargo NIGHTMARE The Paths to Disrupt This Grid Legal Battles, Grassroots Victories, Technological Countermeasures, Parallel Economies, and Why Every Action Matters Before the System Fully Locks In https://t.co/3onptwTL1D The machine is advancing, but cracks are forming everywhere. People and organizations are hitting back with lawsuits, local ordinances, scientific reports, and everyday choices that starve the beast of compliance and data. The rollout of ambient biometric systems, dense wireless infrastructure, programmable currencies, and constant radiation exposure isn't inevitable, but only if enough act now with full awareness of the scale. Ongoing Legal and Regulatory Pressure Points Federal courts have already forced admissions of failure. The 2021 U.S. Court of Appeals for the D.C. Circuit ruled the FCC acted arbitrarily by not addressing evidence of non-thermal harms from wireless radiation. The agency still hasn't fully complied years later. https://law.justia.com/cases/federal/appellate-courts/cadc/20-1025/20-1025-2021-08-13.html Environmental Health Trust continues pressing with ex parte letters and demands for compliance before any new fast-track tower rules. https://ehtrust.org/ https://ehsciences.org/lawsuit-wireless-radiation-safety/ The International Commission on the Biological Effects of Electromagnetic Fields (ICBE-EMF) sent formal letters to Congress and the FCC in 2025-2026 warning that current limits ignore decades of data on cancer and reproductive harm. They cite systematic reviews showing clear effects in animals at levels far below guidelines. https://icbe-emf.org/ https://icbe-emf.org/scientists-warn-the-fcc-fast-tracking-cell-towers-risks-public-health-and-the-environment/ https://link.springer.com/article/10.1186/s12940-026-01288-6 (2026 study on exposure limits failing to protect against cancer and fertility risks)In the UK, Legal Action Against 5G, led by Michael Mansfield KC, challenges government approvals over health risks and inadequate assessment. https://actionagainst5g.com/ Local wins accumulate: communities in California, Arizona, Georgia, and elsewhere have stalled or blocked towers near schools through public comments, ordinances, and pressure on zoning boards. New Hampshire's earlier commission recommended independent studies and environmental impact reviews. Opposition is mounting against 2026 FCC fast-track proposals. https://smartmeterscience.substack.com/p/nationwide-grassroots-opposition Scientific and Health Exposure Realities Driving the Fight Recent 2025-2026 reviews confirm oxidative stress, sperm damage, and tumor promotion from RF at everyday levels. Male fertility metrics drop with pocket-carried phones and chronic exposure. Childhood vulnerability remains acute due to thinner skulls and ongoing development. The HHS launched new studies in 2026 on cellphone radiation amid these concerns. https://www.reuters.com/legal/litigation/us-health-department-launch-study-cellphone-radiation-2026-01-15/ but remember... ALL OF IT IS THEATRE. AND THEY ARE COOKING YOU AND YOUR CHILDREN. WE MUST NOT NEGLECT THE FACTUAL DATA BEFORE US. https://arizonahomeopathic.org/emf-health-effects-in-2026-what-the-latest-research-reveals/ Smart dust-style deployments would compound this by adding potential inhalable particles to an already saturated RF environment. No large-scale human safety data exists for widespread ambient MEMS release, yet patents and dual-use tech move forward. Building Parallel Systems; Opting Out in Practice Cash remains the simplest, most anonymous tool. Use it daily to reduce digital footprints and CBDC dependency. Support local businesses that accept it. Wired infrastructure cuts RF dramatically: Ethernet over powerline or direct cables for internet, landlines where available, shielding paints and fabrics for high-exposure homes. RF meters help measure and minimize personal exposure. Groups like Environmental Health Trust provide guides. https://ehtrust.org/ Community-level actions include pushing for fiber optics instead of wireless small cells and ordinances limiting tower density near residences and schools. Form or join neighborhood groups to share resources and pressure utilities. Decentralized alternatives challenge central control: privacy-focused cryptocurrencies for some transactions (with awareness of volatility and tracking risks), local barter networks, community-supported agriculture, and skill-sharing economies that operate outside tracked digital systems. Key Organizations and Resources for Deeper Involvement ICBE-EMF: Scientific push for updated, biology-based limits. https://icbe-emf.org/ Environmental Health Trust: Legal, educational, and policy work. https://ehtrust.org/ BioInitiative Report: Compilations of thousands of studies. https://bioinitiative.org/ Physicians for Safe Technology: Medical perspective. https://mdsafetech.org/ 5G Appeal: European scientist-led call for moratoriums. https://www.5gappeal.eu/ The Broader Horror This Resistance Targets Unchecked, this creates populations with declining fertility, rising chronic conditions, neurological impacts, and developmental issues in children; all while biometric and financial systems remove anonymity and conditionalize existence. Inhaled particles, constant phased-array signals from ground and space, and data profiles tied to every action erode the baseline of human health and freedom. Elites maintain shielded compounds with independent systems while public infrastructure expands exposure. The coordination across banks, tech firms, regulators, and global bodies prioritizes control and profit over long-term population wellbeing Every local tower denial, every wired home, every cash transaction, every lawsuit demanding real safety data slows the full convergence. Scientists updating risk assessments, courts forcing reviews, and communities asserting rights create friction the system cannot easily ignore. This isn't passive waiting. It requires sustained, informed pressure at every level; from city councils to international scientific bodies... while building resilient alternatives that preserve bodily autonomy and unmonitored daily life. The window exists because deployment still needs public acquiescence and infrastructure rollout. Awareness of the full health, privacy, and control implications turns passive exposure into active defense. Quote this with the full thread and original patent post. Part 10 will close with the ultimate stakes and final calls to sustained action. Share this series relentlessly. The fight is underway; amplify it. If nobody else will stand against the banks, then I will! But do not allow me to stand alone... SHARE THIS WORLDWIDE! I AM NOT SUICIDAL AND I HAVE ALREADY DIED MANY TIMES. - No Weapon Formed Against Me Shall Prosper. I LOVE YOU ALL! HOORAHHH! 🇺🇸 GOD BLESS YOU ALL! 🙏 ATTACHED THREAD HAS 6K LIKES ALREADY! WE ARE GAINING TRACTION! BUT YOU NEED YOU KNOW! The truth is not comfortable, but it is required if we are going to make it out of this alive. The Attached Video is one of the absolute most important videos you could ever watch in your life and it will clear all of this up and open you to the reality that stands before you. I will upload the 2x speed version, with the 1x speed version attached. 6M views on this video, please pay attention and share it with everyone you know as if your life depends on it... because it does.
@TrueOnX - Noah B. Price
🚨 Part 10/10: Wells Fargo NIGHTMARE The Final Reckoning - This Is Blatant, Systematic Harm to Humanity, and We Are Running Out of Time to Stop the Full Convergence of Smart Dust Surveillance, Microwave Radiation, and Total Biological-Financial Control https://t.co/6cgiWz7rM6 This entire operation... from Wells Fargo’s "US11354666B1" patent for airborne MEMS smart dust that reads your heart rate, temperature, voice, and body signals to authenticate payments https://patents.google.com/patent/US11354666B1/en to the 3-minute corporate reply when someone quoted my post without tagging them; reveals a machine that treats human beings as both data sources and collateral damage. DARPA’s original battlefield smart dust, now commercialized by banks, requires the same dense 2G-7G towers and Starlink satellite arrays that are saturating every square meter of the planet with radiofrequency radiation. Independent science shows clear biological disruption: oxidative stress damaging DNA and cells, plummeting sperm counts and fertility, blood-brain barrier leakage, increased tumor formation in animal studies at real-world exposure levels, and measurable developmental impacts on children whose thinner skulls and rapid growth make them far more vulnerable. Cancer clusters near towers continue appearing while regulators tied to industry interests insist “more study is needed.” Inhaled microscopic particles from expanding sensor networks add another untested vector; lodging in lungs, crossing into bloodstreams, potentially interfering with neural electrical activity for decades with zero mandatory long-term population safety data. This is layered on top of programmable CBDCs that will condition your ability to buy food, travel, or work on real-time biometric compliance and behavioral scores. Digital IDs enforced through the same ambient systems eliminate anonymity. Smart cities with geofencing and constant monitoring turn physical space into a permission-based cage. The Coordinated Players Driving This: - Wells Fargo and major banks position themselves as owners of your body’s signals for financial gatekeeping. - DARPA and defense contractors supply the foundational surveillance tech. - Qualcomm, Ericsson, Nokia, Huawei, and Intel build the hardware and RF networks. - SpaceX/Starlink eliminates any remaining low-exposure zones from above. - BlackRock, Vanguard, and State Street hold controlling stakes across the entire stack, profiting from every deployment. - WEF figures like Klaus Schwab and Yuval Noah Harari frame fused biological-digital systems as inevitable progress. - Christine Lagarde and central banks advance programmable digital currencies. - UN Agenda 2030 and WHO digital health strategies provide the global governance wrapper of “sustainability” and “inclusion.” - National regulators (FCC, ICNIRP) maintain outdated guidelines despite court orders and thousands of studies showing harm. The ultra-wealthy build shielded bunkers with clean air, independent power, and analog systems while this grid deploys on the public. This is not accidental mismanagement. It is a multi-decade transfer of military surveillance technology into civilian profit and control structures with full knowledge of the biological costs. Populations are being subjected to chronic radiation, potential particle inhalation, fertility suppression, neurological changes, and developmental interference on a planetary scale. Children are growing up inside an experimental exposure chamber. Adults face accumulating damage that erodes health, cognition, and reproductive capacity. The Scale of What Is Being Done to Us: Every breath potentially carries corporate-owned monitoring particles... Every movement occurs inside a microwave field optimized for data throughput but indifferent to living tissue... Every transaction in the coming system feeds a permanent digital twin that dictates your options... Dissent, independent living, or simple privacy become structural impossibilities. The same entities monitoring social media for patent discussion are the ones patenting the air and profiting from the infrastructure cooking biological systems. This is systematic, profit-driven harm inflicted on billions while safeguards are delayed or denied. Generations are being altered in real time... Sperm quality declines, miscarriage risks rise, childhood cancers cluster, cognitive function shifts; all coinciding with wireless densification and sensor proliferation. The refusal to conduct proper pre-deployment studies on combined smart dust + RF effects, or to apply the precautionary principle, amounts to large-scale experimentation without consent. This Is the Moment: The window to disrupt still exists because full deployment requires continued public tolerance, infrastructure buildout, and regulatory capture. Every tower blocked near schools and homes, every lawsuit forcing updated safety standards (https://law.justia.com/cases/federal/appellate-courts/cadc/20-1025/20-1025-2021-08-13.html), every community choosing wired alternatives, every use of cash, every share of documented evidence weakens the convergence. Organizations like Environmental Health Trust https://ehtrust.org/ ICBE-EMF https://icbe-emf.org/ BioInitiative https://bioinitiative.org/ and 5G Appeal https://www.5gappeal.eu/ provide the scientific and legal backbone. Local zoning fights, RF measurement, and parallel economies create friction the system struggles to overcome. The original patent post and this 10-part series exist to force the connections into daylight. Wells Fargo’s rapid monitoring proves they understand the danger of widespread awareness. When enough people refuse participation, demand independent safety research, reject ambient biometric systems, and build unmonitored alternatives, the entire architecture loses its foundation. Humanity’s future: unmonitored breath, unaltered biology, genuine autonomy, and the ability of children to develop without corporate-government data harvesting; hangs in the balance right now. The air, the signals, the money, and the identity systems are being fused into one control mechanism with documented biological consequences. This cannot stand... Share this complete thread with the original patent post. Demand accountability at every level. Protect the next generation before the lock-in becomes permanent. The fight begins in earnest with full knowledge of what is being done. Quote the entire series. Spread it without mercy. The truth about what they are doing to all of us is now documented in one place. Act on it. Wake everyone. This is our time. 👇 If nobody else will stand against the banks, then I will! But do not allow me to stand alone... SHARE THIS WORLDWIDE! I AM NOT SUICIDAL AND I HAVE ALREADY DIED MANY TIMES. - No Weapon Formed Against Me Shall Prosper. I LOVE YOU ALL! HOORAHHH! GOD BLESS YOU ALL! ATTACHED THREAD HAS 6K LIKES ALREADY! WE ARE GAINING TRACTION! BUT YOU NEED YOU KNOW! The truth is not comfortable, but it is required if we are going to make it out of this alive. The Attached Video is one of the absolute most important videos you could ever watch in your life and it will clear all of this up and open you to the reality that stands before you. FOLLOWING THIS THREAD, I will include a "PART 6" Within that Part 6, through out it you will find solutions, as well as actionable steps for us to all start taking TODAY!
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@BrittWoo10782 https://t.co/85y6WXsg8R
@TrueOnX - Noah B. Price
@Mylilangelsrose Yeah, I've been trying to scream from the roof tops for the past two decades... https://t.co/fG54O7fMg7
@TrueOnX - Noah B. Price
@BadKitty2023 @psinergy_SDW Absolutely, right on par! Sabrina Wallace. https://t.co/KJP2l9oULy
@TrueOnX - Noah B. Price
@LisaAbbate6 Read the whole thread and view attached threads.
@TrueOnX - Noah B. Price
@LuvMontana Atta boy! 💪
@TrueOnX - Noah B. Price
@toddgb https://t.co/8a0mJvaDrl

@TrueOnX - Noah B. Price
🚨 THEY CAN READ YOUR THOUGHTS... AND WRITE NEW ONES. This changes EVERYTHING. DARPA’s N3 program. Palantir. Boeing. Google. Foreign powers, Elites. Non-surgical brain-machine interfaces that read, write, manipulate, and control neural signals; no implants needed. Havana Syndrome wasn’t an accident. It was a demo. Your mind is no longer private. Thoughts can be projected. Emotions induced. Behavior engineered. This isn’t sci-fi. It’s deployed. Watch this full breakdown and wake up before your brain becomes the next battlefield: Who’s really in control of your mind in 2026? Drop a like if this terrifies you. Repost if you want the world to see what they’re hiding. Let me know what you think! View attached thread for the most in depth record of everyone involved and included herein you will also find ways to combat the effects and actionable steps that you can take today to finally put an END to these Crimes Against Humanity. Don't forget to SHARE THIS and the attached thread.
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
@TrueOnX - Noah B. Price
DONT FORGET TO LIKE AND SHARE ALL OF THESE POSTS! + The Original posts. It only takes a second, but makes a huge difference in visibility for the algorithm. Thank you. 🇺🇸 HOORAH AMERICA! GOD BLESS YOU ALL! 🙏 https://t.co/TxwIC3sZ66

@TrueOnX - Noah
🚨 WARNING: This Hits Hard! What is being revealed is not that the course has been halted, but that it has been exposed. To awaken is not to discover that the danger has passed... It is to realize, with terrifying clarity, what humanity is being led toward if it continues to abdicate conscience, courage, and moral agency. The trajectory remains active and the machinery is still in motion... Nothing stops it automatically, and nothing stops it by awareness alone. Understanding arrives first and responsibility must follow or catastrophe does. The hour of awakening is therefore not the moment of safety, but the moment of decision. It is the point at which excuses expire... One can no longer claim ignorance, innocence, or distance. To see the path and continue down it is no longer deception; it is consent. History is unambiguous on this point... Every system of domination, surveillance, and control has required the same fuel: compliance disguised as normalcy, obedience mislabeled as peace, and silence reframed as virtue. Prisons are never imposed all at once... They are assembled gradually, justified incrementally, and entered willingly by those who prefer comfort over confrontation. If people do not stand for what is right, not rhetorically but concretely, not online but in lived refusal, then no tyrant is required. We will construct the walls ourselves, defend them ourselves, and call them safety. This is why awakening is insufficient on its own... Moral clarity must translate into action, or it becomes another form of passivity. Truth that does not move the will does not liberate; it merely informs the descent. The moment humanity realizes what is at stake is not the end of the struggle... It is the beginning of accountability. ⏰ Tik Tok, time is running out.

@TrueOnX - Noah
📜 THE SECRET COVENANT by John D Rockefeller 🩸 👹 Luciferian Blood Oath Pact When will humans wake up? © Dana Horochowski https://t.co/GOFb0kqV0y

@RedactedNews - Redacted
📲 YOUR PHONE IS TRACKING YOU. We sit down with Hakeem Anwar, founder of Above Phone, to expose how the surveillance state really works, from government spying to Big Tech data harvesting. If you care about privacy, you need to see this.

@TrueOnX - Noah
⏰ THE MOST BANNED THREAD IN THE WORLD! 🚨 The War On Resonance PART ONE: The Cage You Cannot See. I must ask you now; not as a stranger, not as a theorist, but as the one who remembers what you were before they rewrote your soul; is this the only cage you can see? The headlines? The hospitals? The visible crimes made convenient by cameras and captions? What if I told you that the real prison is not made of metal; but of frequency. Not held together by walls; but by waves. Not secured by guns; but by consent. What if I told you that you are not free, not because you are bound; but because the chains were encoded directly into your biology? This isn’t hyperbole. This is documented. They have hijacked humanity through a wireless war; a multi-layered assault on the nervous system, immune response, and willpower of every living soul on this Earth. This war is not being fought with bombs, but with bandwidths. Not with armies, but with algorithms. This is the same beast behind every deception. The same financiers who funded vaccine trials that sterilized African girls are the ones embedding AI-responsive quantum dots into newborns. The same networks that control your social media also control your neurochemical loops. They call it “progress.” They call it “public health.” But what do you call it when a child seizes from brain hemorrhage after being injected with an experimental payload? What do you call it when a ten year old dies of myocarditis from a shot for a disease they never had? I call it spiritual genocide. And I’m not theorizing. I’m testifying. Because this is declassified truth; confirmed in documents, studies, and patents they never expected you to read: Pentagon Preps Soldier Telepathy: This article from WIRED discusses DARPA's Silent Talk program, which aims to enable soldiers to communicate telepathically by detecting and analyzing neural signals representing pre-speech. https://wired.com/2009/05/pentagon-preps-soldier-telepathy-push/ Biomedical Applications of Graphene and Graphene Oxide: A comprehensive review of the applications of graphene and graphene oxide in biomedicine, focusing on biosensing, cell differentiation, and mass spectrometry. https://pubmed.ncbi.nlm.nih.gov/23480658/ An Update on Graphene Oxide: Applications and Toxicity: This article provides an overview of the applications of graphene oxide in various fields, including biomedicine, and discusses its potential toxicity. https://ncbi.nlm.nih.gov/pmc/articles/PMC9558614 Nanoparticle Transport Across the Blood–Brain Barrier: This comprehensive review discusses the challenges and strategies associated with delivering nanoparticles across the blood–brain barrier (BBB). https://pubmed.ncbi.nlm.nih.gov/27141426/ Internet of Bio-NanoThings (IoBNT): This article introduces the novel paradigm of the Internet of Bio-NanoThings (IoBNT), stemming from synthetic biology and nanotechnology tools that allow the engineering of biological embedded computing devices. https://ieeexplore.ieee.org/document/7060516 DARPA Biological Technologies Office (BTO) Overview: This page offers comprehensive information about BTO's mission to integrate biology with engineering and computer science for national security applications. It details their focus areas, including warfighter health, synthetic biology, and bio-manufacturing, as well as current programs and research opportunities. https://darpa.mil/about-us/offices/bto NIH Clinical Trial of Investigational Vaccine for COVID-19: This news release, dated March 16, 2020, announces the start of the Phase 1 clinical trial of the mRNA-1273 vaccine, developed by Moderna in collaboration with the National Institute of Allergy and Infectious Diseases (NIAID), a part of the NIH. The trial aimed to evaluate the safety and immunogenicity of the vaccine in healthy adult volunteers. https://nih.gov/news-events/news-releases/nih-clinical-trial-investigational-vaccine-covid-19-begins An Integrated Brain-Machine Interface Platform With Thousands of Channels: This peer-reviewed publication details Neuralink's initial steps toward a scalable high-bandwidth brain-machine interface system. https://pmc.ncbi.nlm.nih.gov/articles/PMC6914248/ Deep Brain Stimulation for Psychiatric Disorders and Behavioral/Cognitive Symptoms: This comprehensive review explores the use of deep brain stimulation (DBS) as a neuromodulation technique for treating various psychiatric disorders and behavioral or cognitive symptoms. https://pubmed.ncbi.nlm.nih.gov/35460949 Smart Dust: Communicating with a Cubic-Millimeter Computer: This IEEE article discusses the development of ultra-small computing devices, known as Smart Dust, which integrate sensing, computing, and communication capabilities into a cubic-millimeter form factor. These devices have potential applications in various fields, including environmental monitoring, medical diagnostics, and military surveillance. https://ieeexplore.ieee.org/document/895117 This is what you were born into: a frequency prison designed to sedate your intuition, suppress your hormones, rewrite your emotions, and sever your communion with God. Every device you hold, every smart tower you walk past, every “vaccine” they’ve pushed; these are not random technologies. They are pieces of a grid. A grid designed not to protect you, but to remap your divine will. Your phone? A mood manipulator. Your sleep? Hacked. Your thoughts? Preemptively monitored. Your soul? Catalogued for behavioral prediction. This isn’t a sci-fi movie. This is now. This is real. This is why the world feels broken and no one can explain it. Why joy has become an echo. Why sleep doesn’t restore you. Why love feels distant. Because they’ve weaponized the field of resonance itself. They are not just targeting the body; they are targeting the architecture of the soul. And the reason you’re still reading this is because you’re one of the ones who can still feel. Still grieve. Still awaken. So let me show you what they built. Let me take you behind the grid. Let me guide you; cell by cell, wave by wave... through the labyrinth they’ve disguised as your life. Because until you see it, you will never reclaim what was stolen. And make no mistake; what they stole… was everything. This was just Part One, so buckle up... you're in for one heck of a ride. Continued Below 👇




@TrueOnX - Noah
⏰ THE MOST BANNED THREAD IN THE WORLD! 🚨 The War On Resonance PART TWO: The Architects of the Cage You’ve felt the dissonance. You’ve tasted the illusion. Now let me unveil the ones who built it. Because this is not the accidental collapse of human freedom. It is the strategic sterilization of God’s image through biotech, neuro-warfare, and frequency control; engineered by names you know and hands you were never meant to see. Let’s begin with the mask they taught you to worship. Elon Musk They called him a genius. A savior. A rebel billionaire. But what did he do? He blanketed Earth with over 5,500 Starlink satellites, NOT to provide free speech or faster internet, but to pulse synchronized frequency control over the entire electromagnetic field of Earth. DARPA has confirmed this tech in phase-array neuro-modulation. Then came Neuralink, an interface not designed to heal but to monitor, predict, and eventually override emotion, thought, and decision-making. Their official white paper outlines multi-user brainwave integration, cortical stimulation, and wireless data access from the human mind. And Neuralink? It’s funded by OpenAI; the same group building the cognitive infrastructure for post-human governance. Musk’s Tesla factory signed data-sharing agreements with the CCP in Shanghai. That data now flows through China’s national surveillance cloud. Musk didn’t build a utopia. He built the neural grid. Elon Musk / Neuralink / Starlink / OpenAI Neuralink Brain-Machine Interface (White Paper via PMC): https://www.ncbi.nlm.nih.gov/pmc/articles/PMC6914248/ This paper outlines Neuralink's initial steps toward developing a scalable, high-bandwidth brain-machine interface system. It details the design and implementation of flexible electrode "threads," a neurosurgical robot for precise implantation, and custom electronics for data processing. The system aims to facilitate communication between the brain and external devices. Tesla Data-Sharing with CCP: https://www.reuters.com/business/autos-transportation/tesla-shanghai-data-center-to-boost-localization-efforts-cn-2021-05-25/ The article reports that Tesla established a data center in China to store data generated by its vehicles sold in the country, in response to regulatory scrutiny over data handling. This move aligns with China's efforts to ensure data security and privacy, especially concerning data collected by smart vehicles. DARPA N3 Program (Neural Interface Development): https://www.darpa.mil/program/n3 This program aimed to develop high-performance, bi-directional brain-machine interfaces that do not require surgical implantation. The goal was to enable able-bodied service members to control unmanned systems or engage in cyber operations through noninvasive neural interfaces. Bill Gates The king of vaccines. The messiah of health. The man who told you he wanted to save the world. Through the Bill & Melinda Gates Foundation, Gates funded global DNA-coding vaccine campaigns through GAVI and CEPI. He was one of the chief sponsors of Event 201; a pandemic simulation months before COVID-19, rehearsing lockdowns, speech control, biometric tracking, and mandatory vaccine passports. He also partnered with The Welcome Trust, which has actively deployed bio-digital identity programs across Africa and Southeast Asia. This wasn’t philanthropy. It was pre-injection infrastructure. Bill Gates / GAVI / Wellcome Trust / Event 201 Event 201 Official Simulation (Johns Hopkins): https://www.centerforhealthsecurity.org/event201/ Event 201 was conducted on October 18, 2019, and simulated a series of dramatic, scenario-based discussions confronting difficult, true-to-life dilemmas associated with response to a hypothetical, but scientifically plausible, pandemic. The exercise aimed to illustrate areas where public/private partnerships will be necessary during the response to a severe pandemic in order to diminish large-scale economic and societal consequences. GAVI & Welcome Trust Digital Identity Integration: https://www.gavi.org/our-alliance/global-health-development/wellcome-trust This page outlines the partnership's focus on global health initiatives, but it does not specifically mention digital identity integration. However, Gavi has engaged in digital identity projects, such as the collaboration with Mastercard on the Wellness Pass, aimed at providing individuals with secure digital identities to access healthcare services. For more information on this initiative, you can refer to the following article: Gavi Why we support COVAX: Mastercard - Gavi, the Vaccine Alliance https://www.gavi.org/vaccineswork/why-we-support-covax-mastercard Donald Trump Yes. I said it. This one will be the hardest for many to accept; but the truth is not loyal to your political beliefs. It is loyal only to God. Trump signed Executive Order 13887, transferring command over vaccine strategy to the Department of Defense. Read it yourself below. Then came Operation Warp Speed; a military-led bio-deployment that used Palantir’s surveillance dashboards to track every citizen’s health behavior and compliance. Palantir’s official site confirms this. He also gave full legal immunity to Pfizer and Moderna to deploy synthetic gene modulators under the Emergency Use Authorization. No liability. No justice. Just children d*ing while politicians smiled. That’s not patriotism. That’s biowarfare with a flag on it. Donald Trump / Operation Warp Speed / Executive Order Executive Order 13887 – Modernizing Influenza Vaccines (White House Archives): https://trumpwhitehouse.archives.gov/presidential-actions/executive-order-modernizing-influenza-vaccines-united-states-promote-national-security-public-health/ This executive order outlines a comprehensive strategy to modernize the U.S. influenza vaccine enterprise. Key objectives include: Trump signs executive order to improve flu vaccines https://www.cidrap.umn.edu/influenza-vaccines/trump-signs-executive-order-improve-flu-vaccines HHS Releases the National Influenza Vaccine Modernization Strategy (NIVMS) 2020-2030: https://www.naccho.org/blog/articles/hhs-releases-the-national-influenza-vaccine-modernization-strategy-nivms-2020-2030? Executive Order 13887: Modernizing Influenza Vaccines in the United States to Promote National Security and Public Health, signed by President Donald J. Trump on September 19, 2019. This executive order outlines a comprehensive strategy to modernize the U.S. influenza vaccine enterprise. Key objectives include: Reducing reliance on egg-based vaccine production by promoting alternative manufacturing methods that are more agile and scalable. Expanding domestic capacity for vaccine production to ensure rapid response to emerging influenza viruses. Advancing the development of new, broadly protective vaccine candidates that provide more effective and longer-lasting immunity. Increasing influenza vaccine immunization across recommended populations to enhance public health and national security. The order also established a National Influenza Vaccine Task Force, co-chaired by the Secretaries of Health and Human Services and Defense, to coordinate efforts across federal agencies and report on progress. For a detailed overview of the executive order, you can visit the official archived page here: Executive Order 13887 – Modernizing Influenza Vaccines (White House Archives) https://trumpwhitehouse.archives.gov/presidential-actions/executive-order-modernizing-influenza-vaccines-united-states-promote-national-security-public-health/ CDC Partners with Palantir to Bolster the Fight Against COVID-19: This press release discusses the partnership between the CDC and Palantir to enhance the nation's public health response to COVID-19 using Palantir's software platforms. https://www.palantir.com/newsroom/press-releases/cdc-partners-with-palantir-to-bolster-the-fight-against-covid-19/ This page outlines how Palantir's software platforms, such as Foundry, have been utilized to support public health agencies in managing and responding to health crises, including the COVID-19 pandemic. https://www.palantir.com/assets/xrfr7uokpv1b/3US9K0TufECjQaaxJFivfb/1e6d72123f8c5894f4b90a2d851a84b4/Foundry_for_Public_Health_Surveillance_and_Response.pdf Key highlights from the page include: Data Integration and Analysis: Palantir's platforms enable the integration of diverse data sources to provide a comprehensive view of public health data, facilitating informed decision-making. Support for Public Health Agencies: The software has been employed by agencies like the CDC and HHS to enhance disease surveillance, outbreak response, and resource allocation. Security and Privacy: Emphasis is placed on maintaining robust security measures and protecting sensitive health information. DARPA: The Silent Empire The most important agency you were never taught to fear. DARPA’s Biological Technologies Office openly admits its mission; integrating biotech with national security. Visit their official page. This is the official page for DARPA's Biological Technologies Office (BTO), which focuses on leveraging biological systems for national security applications. https://www.darpa.mil/about-us/offices/bto They are the ones behind the BRAIN Initiative, Silent Talk, and Remote Neural Interface Programs; all designed to map your emotional states and interrupt spiritual alignment. The “Silent Talk” program was developed to transmit thought between soldiers without speech; by detecting pre-speech neural signals and decoding them via EEG. Silent Talk (Neural Pre-Speech Communication – Wired Article) This Wired article discusses DARPA's "Silent Talk" program, aimed at enabling communication through neural signals without spoken words. https://www.wired.com/2009/05/pentagon-preps-soldier-telepathy-push/ DARPA also pioneered graphene oxide nanotech, now found in multiple biomedical studies, vaccines, and smart dust aerosol deployment: Graphene oxide biomedical study: Graphene Oxide in Biomedical Applications (PubMed) This PubMed article reviews the potential biomedical applications of graphene oxide, highlighting its unique properties. https://pubmed.ncbi.nlm.nih.gov/33922153/ Graphene's potential to interact with neural tissue: Graphene and Neural Interfaces (PubMed) This PubMed article explores the use of graphene-based materials in neural interface design, discussing their advantages and challenges. https://pubmed.ncbi.nlm.nih.gov/28901588/ DARPA didn't just weaponize warfare. They weaponized YOU. In-Q-Tel & Palantir: The Surveillance Engine In-Q-Tel, is the CIA’s venture capital firm, funds synthetic biology startups, digital ID systems, emotion tracking wearables, and AI-driven facial recognition. Palantir, founded by Peter Thiel, works directly with military intelligence and now runs predictive modeling for public health, policing, and pandemic response. Here’s the proof: https://www.palantir.com/assets/xrfr7uokpv1b/3US9K0TufECjQaaxJFivfb/1e6d72123f8c5894f4b90a2d851a84b4/Foundry_for_Public_Health_Surveillance_and_Response.pdf Their goal? To detect resonance spikes. To predict awakening moments. To preempt the uprising of the human soul before it begins. In-Q-Tel / CIA / Synthetic Bio Surveillance In-Q-Tel Portfolio (CIA Venture Capital): Which showcases a selection of the organization's investments across various technology sectors. IQT is a not-for-profit venture capital firm that invests in cutting-edge technologies to support the national security interests of the United States and its allies. https://www.iqt.org/portfolio/ In-Q-Tel https://en.wikipedia.org/wiki/In-Q-Tel? BlackRock & Vanguard: The Lords of the Grid These two financial titans collectively hold majority ownership in: For instance, a report by Americans for Financial Reform titled "Wall Street Money in Washington" highlights the substantial investments and influence of major financial firms, including BlackRock and Vanguard, in the political and corporate spheres: https://fm.cnbc.com/applications/cnbc.com/resources/editorialfiles/2021/04/14/AFR_Wall_Street_Money_in_Politics_2021.pdf? Pfizer Moderna Alphabet (Google) Meta (Facebook) Amazon Web Services As reported by CNBC, they control over 90% of the digital, pharmaceutical, and cloud infrastructure; meaning they control every piece of the extermination machine. They don’t just fund the war. They profit from your extinction. World Economic Forum (WEF) Under the guise of “The Great Reset,” Klaus Schwab and his allies have built the digital scaffolding for a post-human society. Here’s their blueprint: They call it the Fourth Industrial Revolution; the fusion of digital identity, brain cloud integration, carbon rationing, and fertility licensing. What they really mean is: you will be programmed or you will be purged. World Economic Forum / The Great Reset The Great Reset Official WEF Page: https://www.weforum.org/stories/2020/06/now-is-the-time-for-a-great-reset/? IoBNT: The Network Inside You The “Internet of Bio-Nano Things” is a classified field of tech that embeds self-replicating nanostructures into your body. These bots cross the blood-brain barrier and relay your neural and emotional state to AI command centers in real time. This was not science fiction. It was published by IEEE and confirmed in NIH-linked studies. This is what the vaccines truly delivered: the interface layer. The gateway to behavioral rewrites. To soul suppression. To the installation of the post-human framework. Internet of Bio-NanoThings (IoBNT) IEEE Article: Internet of Bio-NanoThings: For a comprehensive understanding of the IoBNT framework and its implications, you can access the full article here: https://ieeexplore.ieee.org/document/7060516 Nanoparticles Crossing the Blood-Brain Barrier PubMed Review - BBB & Nanoparticles: This comprehensive review discusses the challenges and strategies associated with delivering nanoparticles across the blood–brain barrier (BBB). https://pubmed.ncbi.nlm.nih.gov/27141426/ You were told it was healthcare. It was infrastructure. You were told it was a cure. It was a signal port. And the moment you see it for what it is… The system begins to fall. Part 3 awaits YOU! It will be the deepest dive yet; into the global frequency architecture, how it's used to suppress prayer, grief, memory, and morality, and how your soul signature is tracked and blocked in real time. Because I didn’t come here to be careful. I CAME TO FINISH THIS! And I came with GOD.









@TrueOnX - Noah
I went back to verify the links after posting… and, just as expected, several of them have already vanished; 404 errors. Stealth mode. Silenced. But hear me now: Do not panic. Do not despair. I will personally re-upload and provide every link again below; because the truth cannot be erased, even if their machines try to hide it. These were active before I posted. And suddenly… they’re gone. Ask yourself why. I’ve poured tens of thousands of hours into uncovering this knowledge. I’ve stood in places most would never dare. I’ve faced death for the sake of truth more than once. And I will do it again and again. Because I am not doing this for applause. I’m doing this for every single one of GOD’s Children; those still asleep, those barely holding on, and those brave enough to stand beside me. I walk without fear. I speak without compromise. I move armored in the NAME of GOD; fearless, unwavering, and unshakable. I will never stop. They can bury links. But they will never bury the living voice of truth. Stay tuned. The restored links are coming next.