reSee.it - Tweets Saved By @gnukeith


@gnukeith - Keith
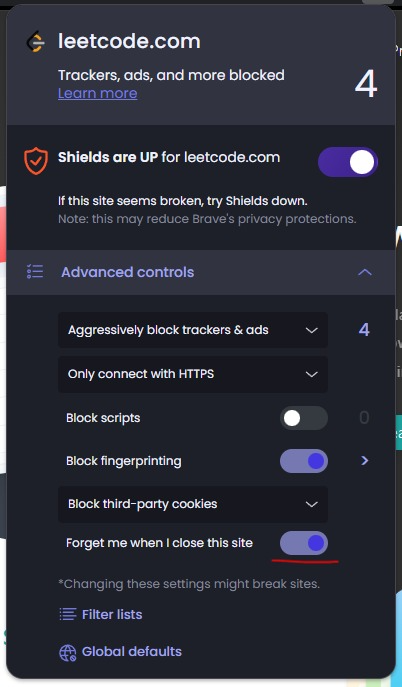
Brave can detect and block trackers that use CNAME cloaking tactics to hide their true origin and bypass traditional ad blockers, this is something that uBO is better at on Gecko based browsers, but Brave Shields isn't an extensions. Fighting against CNAME-based tracking is something people don't understand how important it really is: https://www.helpnetsecurity.com/2021/02/24/browsers-anti-tracking/ Brave Shields blocks ads at the browser level before they are even loaded onto a webpage, rather than blocking them after loading. When content is blocked at the browser level before loading, it prevents unnecessary network requests entirely. https://brave.com/blog/brave-saves-batteries/ This means that it doesn't waste bandwidth downloading ads, trackers, or malicious scripts that would be blocked anyway, this also helps with battery since resources don't need to take it into account since it's blocked before the page loads. Native protection against websites attempting to interact with local network resources, blocking attempts to scan ports or identify running services. https://github.com/brave/adblock-lists/blob/758de6cf238840e5741261a2796d57a90274bfc1/brave-lists/brave-specific.txt#L1-L4 Browsers without proper local network protections could be exploited: https://www.helpnetsecurity.com/2024/08/09/0-0-0-0-day-vulnerability-affects-chrome-safari-and-firefox/ This requires low-level access to the network stack that extension-based blockers cannot achieve. There is also ephemeral storage partitioning, so implements a unique ephemeral storage system that automatically deletes third-party storage while maintaining site functionality. This level of storage management requires native browser code access. Network-state partitioning that protects against sophisticated tracking techniques that attempt to abuse network caches and connection data. This partitioning occurs at the browser's core network stack level. https://brave.com/glossary/partitioning/ Extensions take memory and OS overhead too.




@gnukeith - Keith
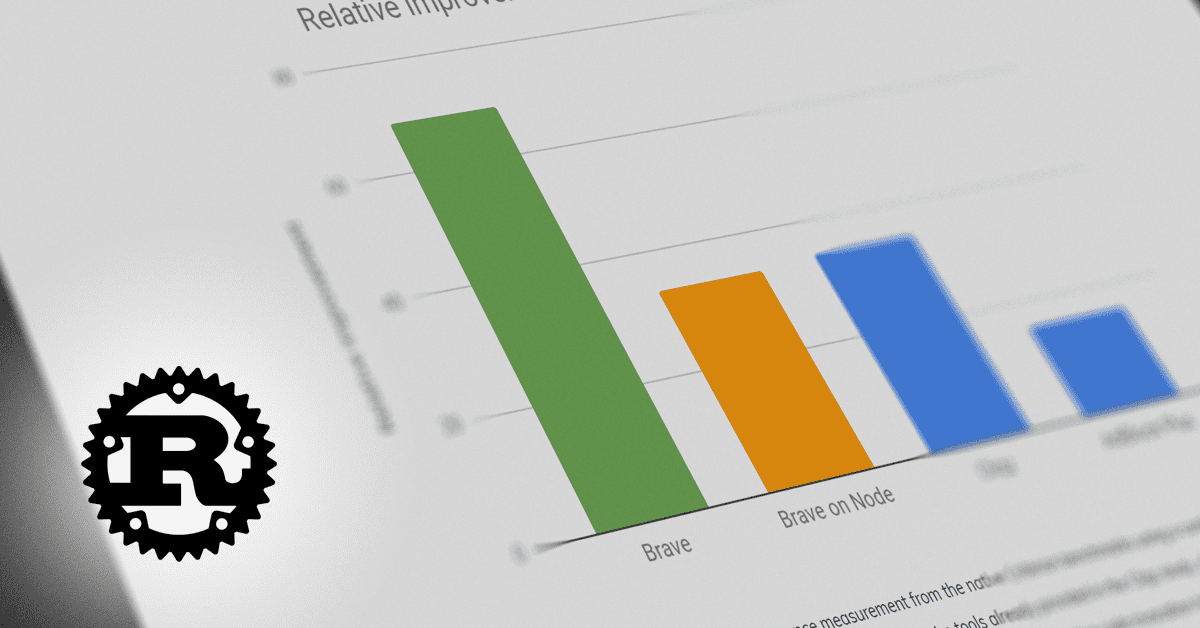
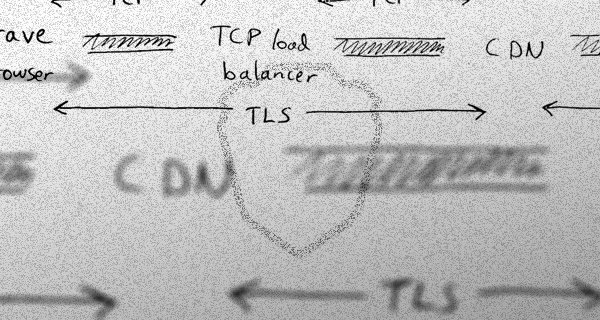
Brave is using a stripped-down version of Chromium with the bad bits removed/nullified. https://github.com/brave/brave-browser/wiki/Deviations-from-Chromium-(features-we-disable-or-remove) Brave has an issue captured for pulling in relevant patches from the ungoogled-chromium project. https://github.com/brave/brave-browser/issues/1431 Brave shields can blocks network requests from extensions, which uBO cannot do as an extension. Implements CNAME uncloaking directly at the browser level for better tracking protection. Features Sugarcoat technology to defuse anti-adblock scripts more effectively. https://brave.com/privacy-updates/6-cname-trickery/ https://brave.com/privacy-updates/12-sugarcoat/ https://brave.com/privacy-updates/10-custom-filter-lists/ https://brave.com/privacy-updates/1-web-resource-replacements/ Apart from Brave Shields being a full stack, it's written in Rust. https://brave.com/blog/improved-ad-blocker-performance/ https://github.com/brave/adblock-rust Farbling is Brave's technique of adding subtle randomization to certain browser APIs to prevent fingerprinting. Randomization is based on a seed that changes per: > Session > Site (eTLD+1) eTLD stands for "effective Top Level Domain" and eTLD+1 refers to the effective top-level domain plus one level down - essentially the registrable domain name that a person or organization can directly register. > Storage area https://github.com/brave/brave-browser/wiki/Fingerprinting-Protections Visit a site like https://browserleaks.com/canvas, note the fingerprint, and then visit the same site in: > Private Window > Private Window with Tor > After restarting the browser > In a different profile You should get a different fingerprint each time. Here's another test: https://dev-pages.brave.software/fingerprinting/farbling.html Not to mention that Brave has developed a Private Content Delivery Network (CDN) to protect user privacy while delivering content. https://brave.com/blog/brave-private-cdn/ Prevent users from touching yet another Google endpoint: https://github.com/brave/brave-browser/issues/1715






@gnukeith - Keith
@qeldegna @lossofclarity @xvfos Brave Rewards are moving to on-chain which doesn't require KYC. Brave has never mined crypto/anything off peoples computers. Brave Shields actively blocks them.

@gnukeith - Keith
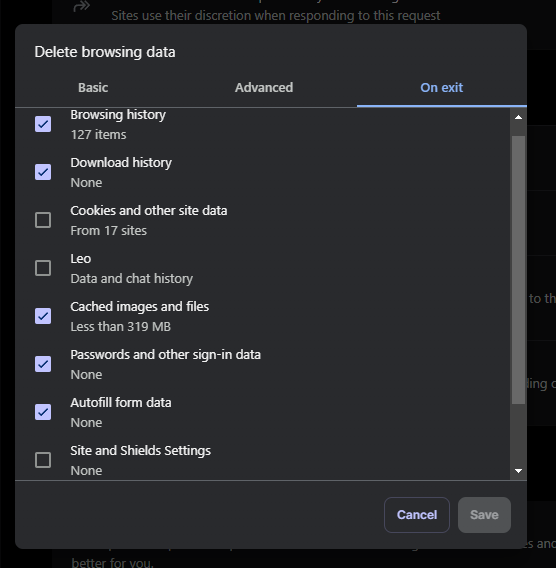
@ConvxO2 @lossofclarity @xvfos Make sure you have Cookies and other site data toggled off when clearing things on exit. brave://settings/clearBrowserData Check if you have FMWICTS on: https://t.co/eNkZy9BMkI

@gnukeith - Keith
@lossofclarity @xvfos Not to mention: https://www.bleepingcomputer.com/news/security/tor-says-its-still-safe-amid-reports-of-police-deanonymizing-users/ This is essentially a small-scale proof of concept. What occurs when it's implemented on a much larger scale? https://www.tagesschau.de/investigativ/panorama/tor-netzwerk-100.html


@gnukeith - Keith
@lossofclarity @xvfos TOR and TOR browser are two different things. TOR is well aware of Firefox's (Gecko) limitations. https://web.archive.org/web/20241225063856/https://gitlab.torproject.org/tpo/applications/tor-browser/-/wikis/Hardening