TruthArchive.ai - Tweets Saved By @jsrailton

@jsrailton - John Scott-Railton
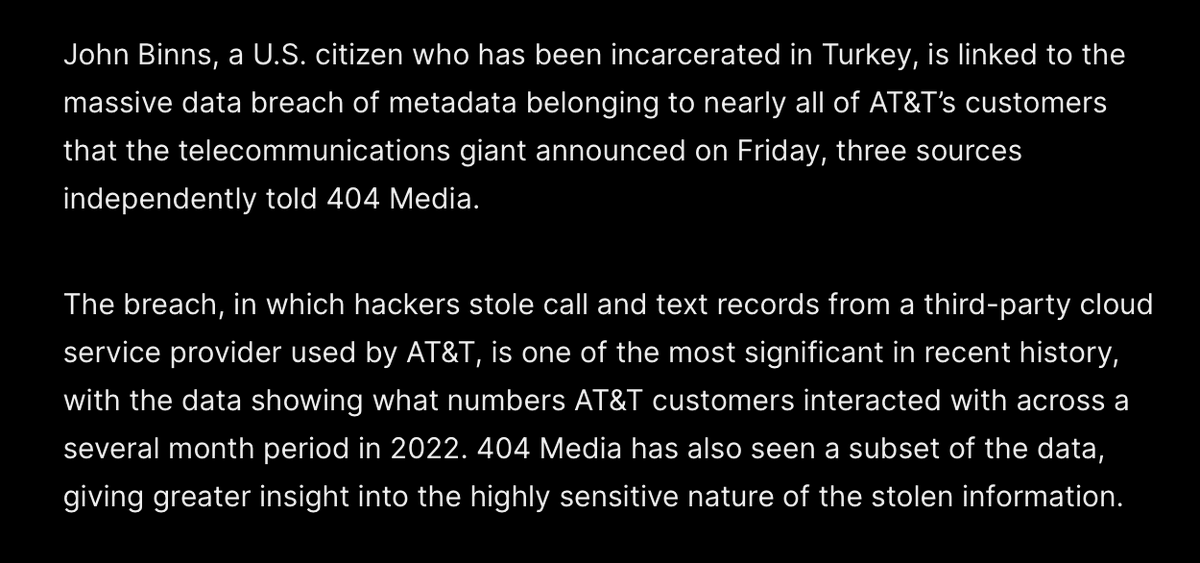
STAGGERING: Nearly all @ATT customers' text & call records breached. An unknown entity now has an NSA-level view into Americans' lives. Damage isn't limited to AT&T customers. But everyone they interacted with. Also a huge national security incident given government customers on $T. 1/ By @MattEganCNN &@snlyngaas https://cnn.com/2024/07/12/business/att-customers-massive-breach/index.html

@jsrailton - John Scott-Railton
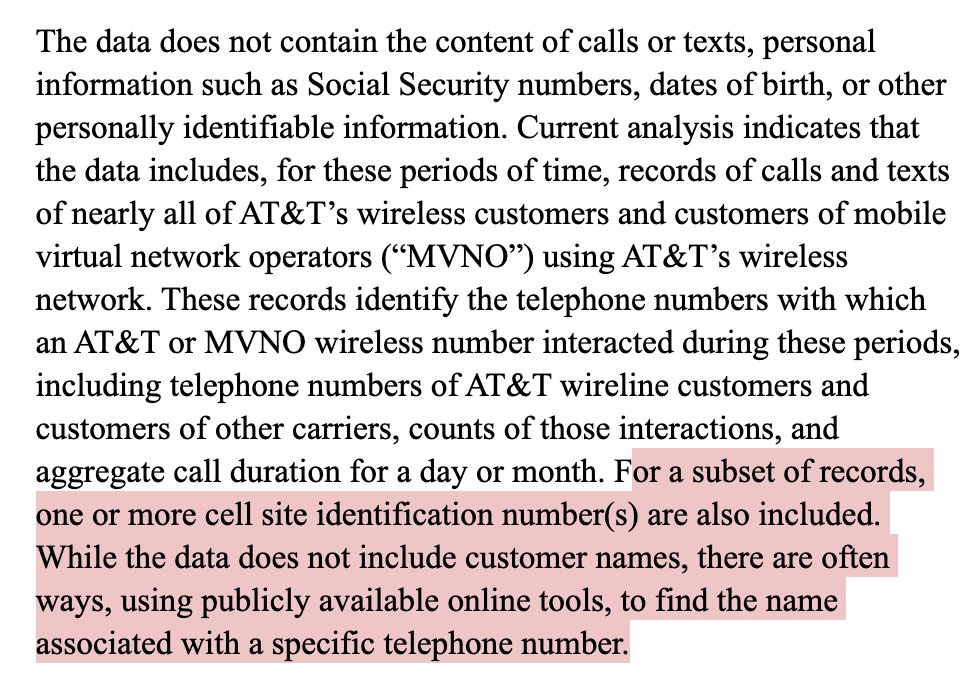
2/ From @ATT's SEC filing. None of this is remotely reassuring. Making matters worse, it looks like some of the data has cell site information. That means broad stroke location information that can be translated into intelligence about peoples' locations and movements. https://www.sec.gov/ix?doc=/Archives/edgar/data/0000732717/000073271724000046/t-20240506.htm
@jsrailton - John Scott-Railton
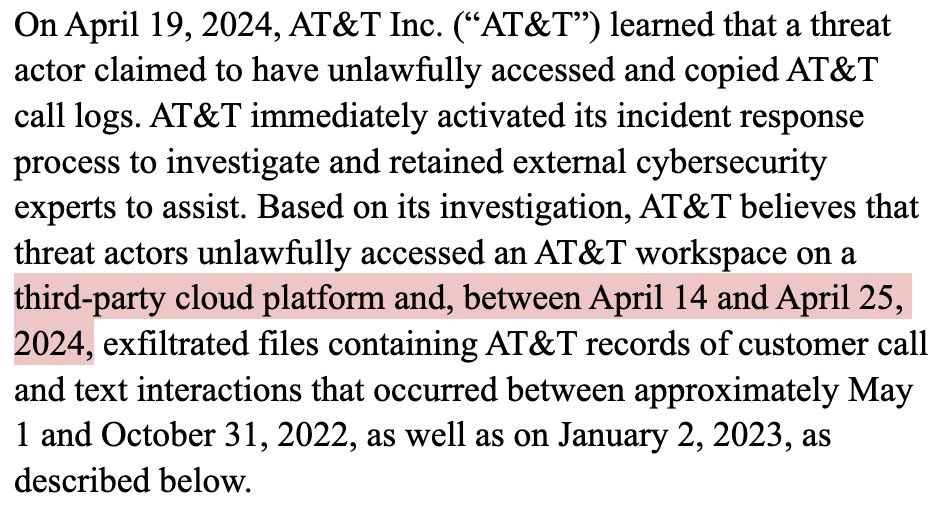
3/ Attack of the dreaded third-party cloud platform. In this case, per reporting, this is again @SnowflakeDB. If this sounds vaguely familiar it's because Snowflake has featured in reporting on a whole host of recent breaches, from #Santander to #Ticketmaster. In other news, Snowflake finally implemented mandatory multi-factor authentication option.
@jsrailton - John Scott-Railton
@ATT @SnowflakeDB 4/ Americans have grown numb to breach notifications. The @ATT breach is so bad it should wake everyone up. Unless big telcos face massive financial penalties for these megabreaches, they will continue.
@jsrailton - John Scott-Railton
5/ In a statement, Senator @RonWyden brings the fire. Big breaches must come with big dollar consequences.👇 Sad truth, but I doubt many members of Congress will raise their voices to call for change... even though all their constituents are impacted.
@jsrailton - John Scott-Railton
6/ I hope coverage of the @ATT collectively recognizes: Metadata matters. Enough to kill people in wartime without knowing their names or seeing their faces. It tells comprehensive stories about who people are, what they are doing, and what their secrets are.
@jsrailton - John Scott-Railton
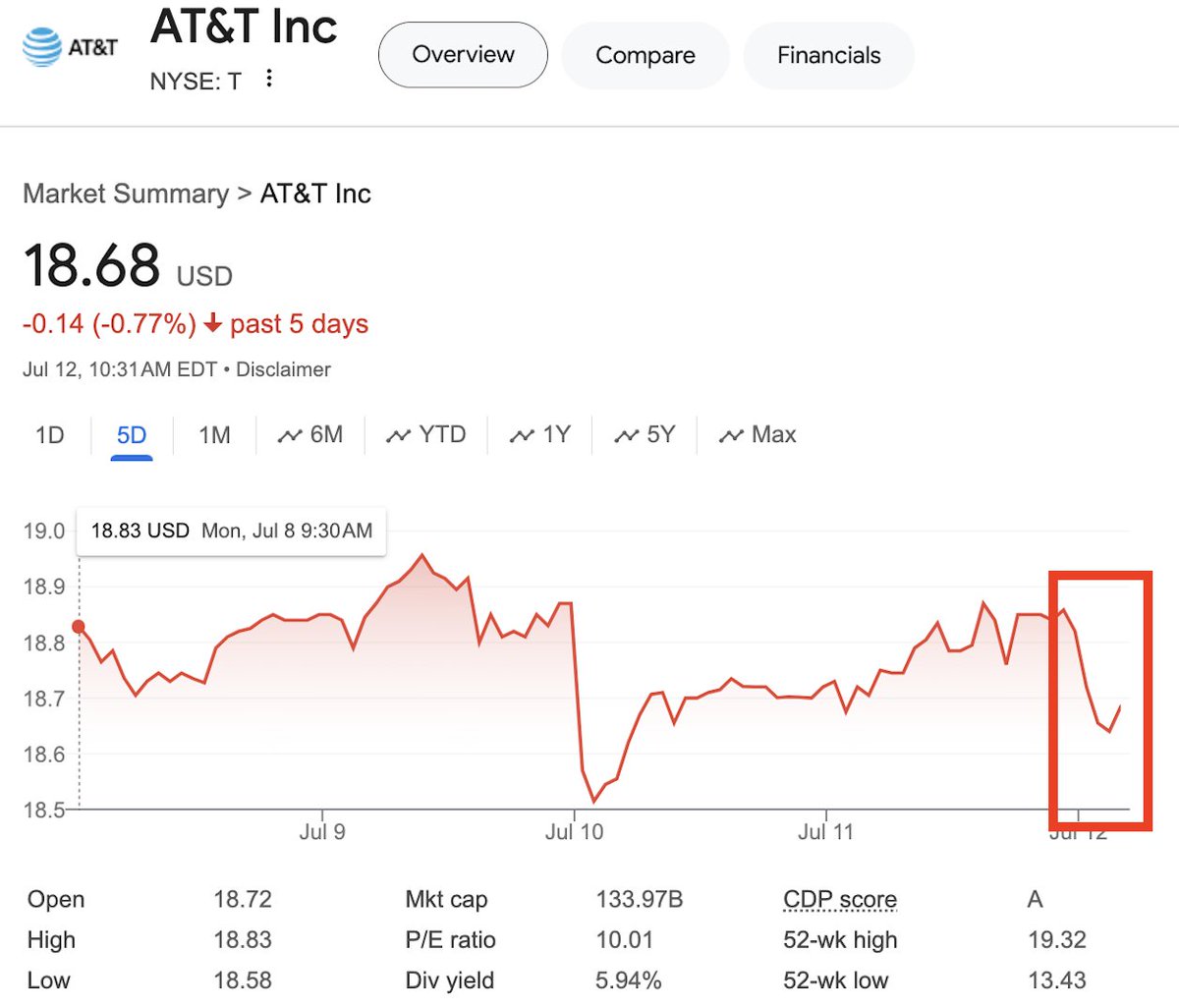
7/ Barely a blip on @att $T stock. For an absolutely unprecedented, historic breach of customer data. If the market won't punish telcos for being reckless with our data, regulators and the @FCC must.
@jsrailton - John Scott-Railton
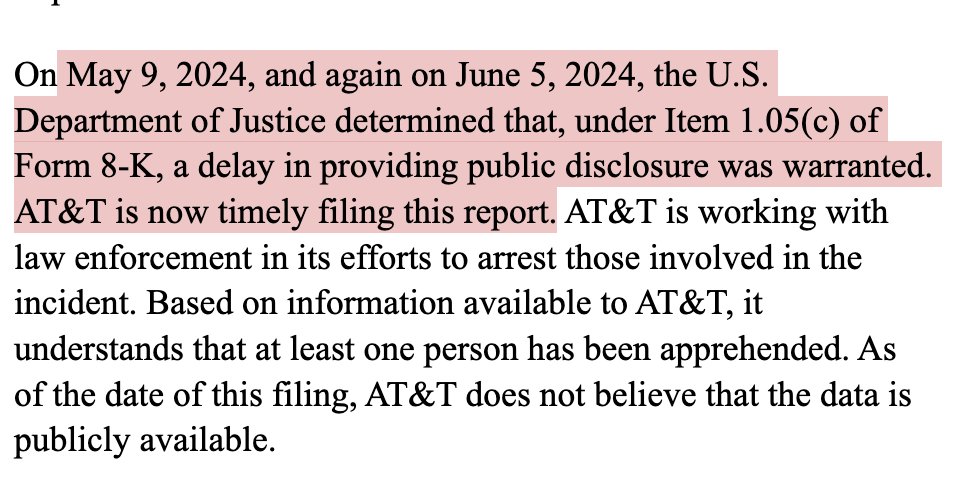
8/ Super interesting detail in SEC filing: 2x request to delay disclosure. Most would conclude this signals active investigation & seriousness with which @TheJusticeDept and @FBI are taking this case. The mention of a believed apprehension is also something to watch. h/t @petestrzok for flagging!
@jsrailton - John Scott-Railton
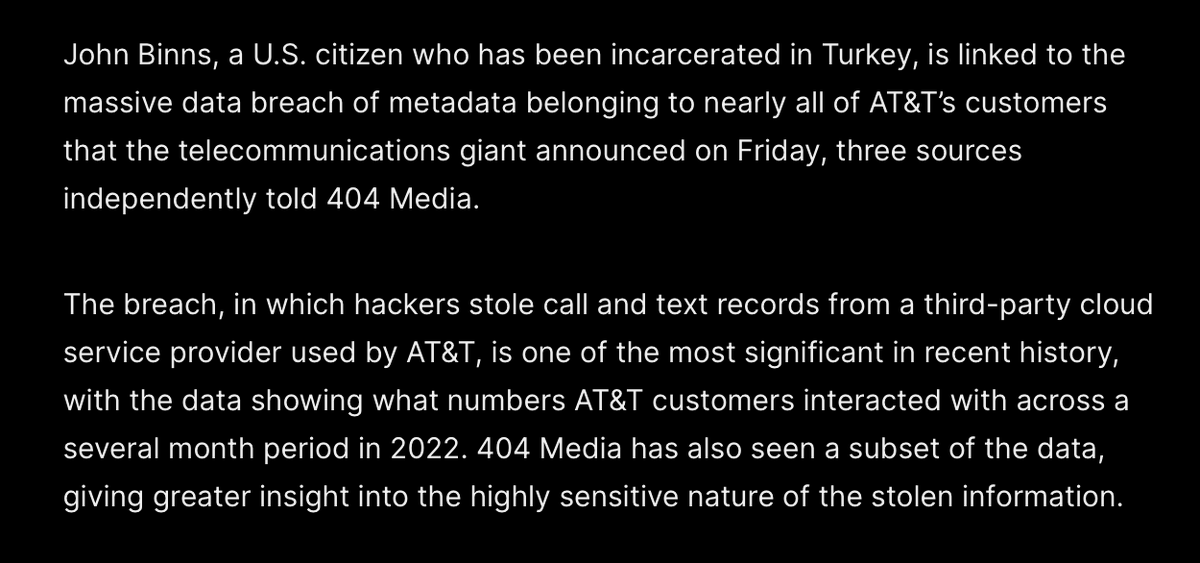
9/ When people ask: is the #ATTmegabreach an aberration from @att? Answer: 73 million accounts. That's how many $T users' personal data, including SSNs, leaked onto the dark web just this spring. The conclusion isn't hard to draw. By @rachelerman https://www.washingtonpost.com/technology/2024/03/30/att-dark-web-leak/


@jsrailton - John Scott-Railton
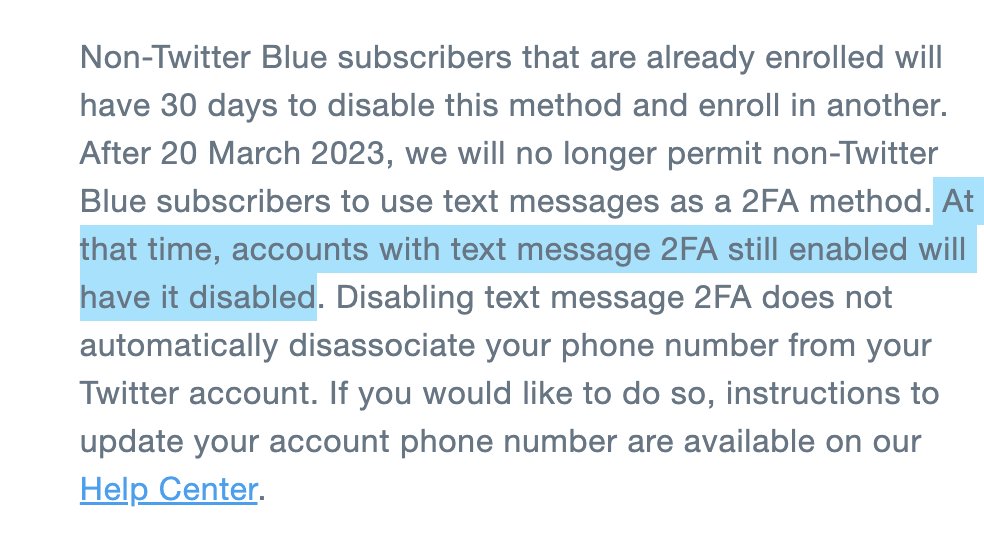
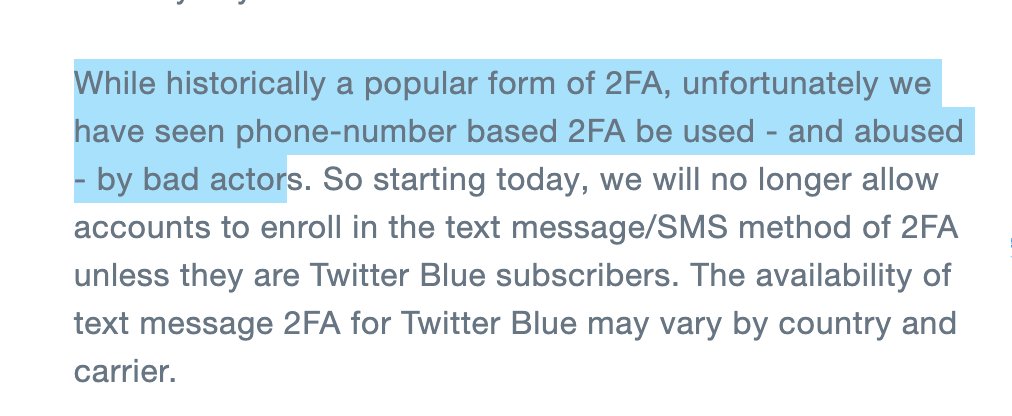
Twitter about to give hackers a huge gift.... ... by *REMOVING text message authentication* for non paying accounts. Yes, there are better forms of #2FA. But this is blackmail. Expect waves of takeovers as hackers run through password dumps. 1/ https://blog.twitter.com/en_us/topics/product/2023/an-update-on-two-factor-authentication-using-sms-on-twitter
@jsrailton - John Scott-Railton
2/ Twitter is basically saying "hey the locks on your home aren't the most secure [true]... so we're just removing them at the end of the month [insane]" Text message authentication isn't great. And it needs to be evolved away from. But this is reckless.
@jsrailton - John Scott-Railton
3/ You don't make users more secure by unilaterally *degrading* their security, then hoping they do better. Security is a ratcheting process. If Twitter goes ahead with this, they absolutely deserve regulatory & Congressional scrutiny.
@jsrailton - John Scott-Railton
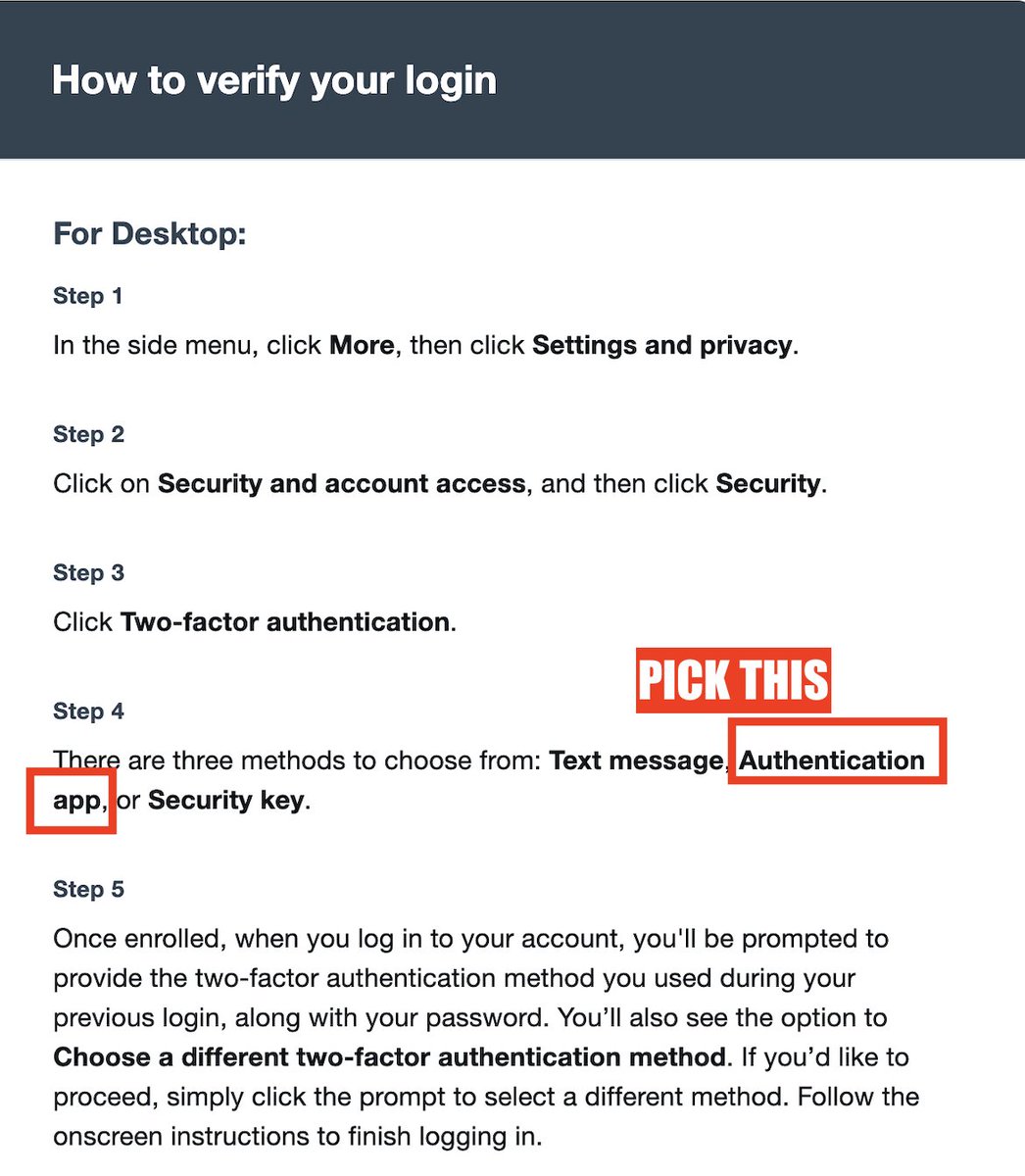
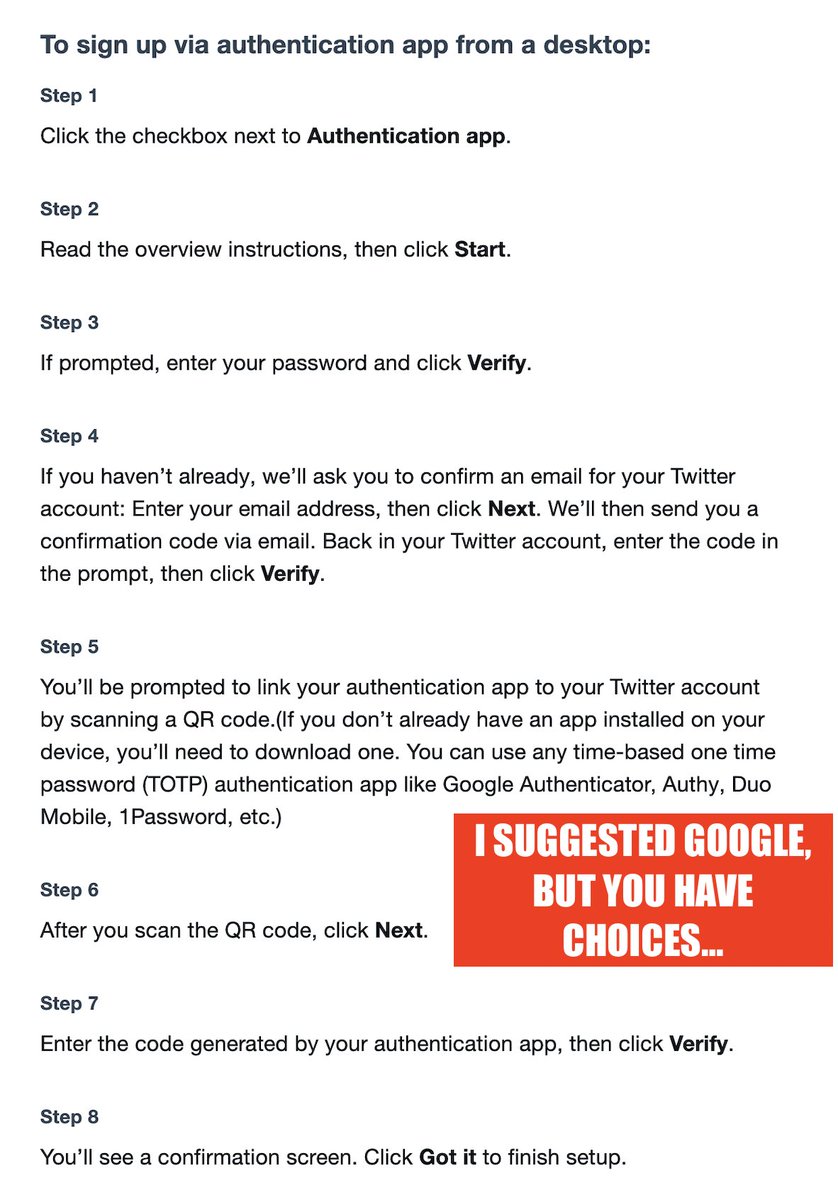
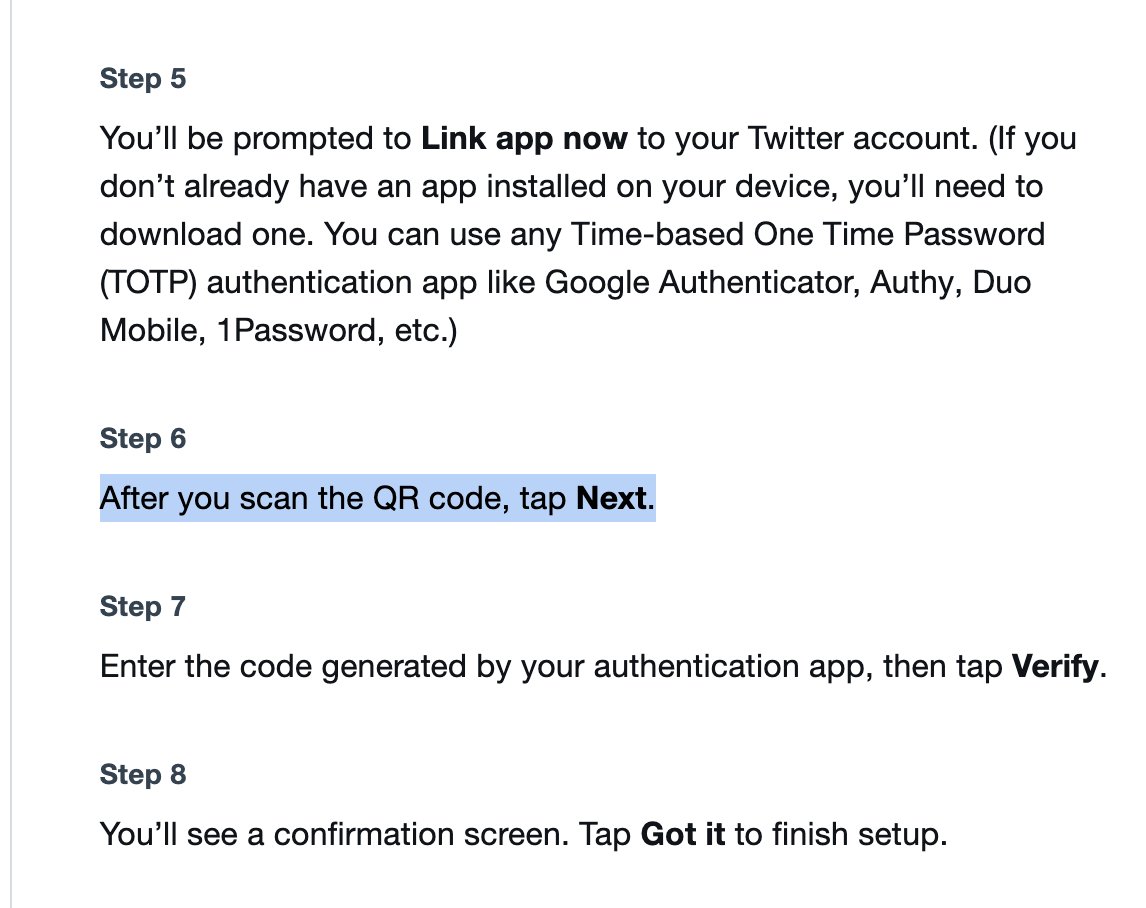
4/ Here's how to secure your Twitter account with the free Google Authenticator App.* Step 1: Get the Appp iOS: https://apps.apple.com/us/app/google-authenticator/id388497605 Android: https://play.google.com/store/apps/details?id=com.google.android.apps.authenticator2 Step 2: Follow these instructions (easiest is on desktop): https://help.twitter.com/en/managing-your-account/two-factor-authentication


@jsrailton - John Scott-Railton
5/Moreover, #Twitter's instructions for #TwoFactorAuthentication for mobile-only users = lame. Like not explaining that it may not be possible to scan a QR code on your phone...with your phone. (Hint: not possible on all apps, you may need an app that can scan a screenshot).
@jsrailton - John Scott-Railton
6/ I'm confident this isn't part of a grand plan to make users more secure ... because the advice Twitter gives on other #TwoFactorAuthentication methods is so bad. And barely useable.
@jsrailton - John Scott-Railton
7/ Platforms know (including Twitter...they fired the experts?)... that getting users to take new security steps is hard. And takes time. And really good messaging & user education. Plus nudges that work. This has none of that.
@jsrailton - John Scott-Railton
8/ Whenever there's a breach, hacking groups try the passwords against *all* accounts they can link to you. Twitter users with #TwoFactorAuthentication have been protected. By design. Turning it off will breathe new life into old breaches. It will be bad.
@jsrailton - John Scott-Railton
9/ My hope: An ambitious prosecutor / regulator / congressperson compels Twitter to provide the communications that went into the decision to yank SMS #TwoFactorAuthentication from free accounts... against all industry practices & norms. There's no way that it looks good.
@jsrailton - John Scott-Railton
10/ "unfortunately we have seen phone-number based 2FA be used - and abused - by bad actors" - Twitter Sure. But Twitter probably sees 10,000x more attacks that can be stopped by SMS-2FA. Daily. And I'm probably massively lowballing.
@jsrailton - John Scott-Railton
11/ I've researched & published on #2FA adoption by platforms. SMS-based 2FA has costs. They pay Twilio et. al. to send those messages. This, alongside the security issues with SMS-2FA is a great reason to move to better. But not to move backwards. https://www.computer.org/csdl/magazine/sp/2016/02/msp2016020079/13rRUEgarmi