Three Factions, One Target: Inside the IO Campaign Against the Flynn Family
An open-source intelligence investigation documenting 53 information manipulation techniques deployed by 20 hostile accounts across 3 political factions — and why the campaign is nearly impossible to counter.
On a single day in late March 2026, at least six accounts across the political spectrum posted thirty-five hostile messages targeting the same family within hours of each other. They came from the political left and the political right. They came from people who despise each other. They used different language, different platforms, different audiences — and yet their attacks landed on the same two people at the same time, with a combined potential reach exceeding four million accounts.
This is the story of what we found when we looked behind the curtain.
Over the course of an intensive open-source intelligence operation, Sierra Special Investigations documented a sustained information campaign targeting Lt. Gen. Michael T. Flynn (USA, Ret.) and his sister, Mary Flynn O'Neil. We identified twenty hostile accounts across three distinct political factions. We classified fifty-three information manipulation techniques using the DISARM framework — a standardized taxonomy developed by the international counter-disinformation community. We mapped a network of forty-two nodes and sixty-seven connections. We found evidence of coordinated amplification, manufactured terminology that spread from a single account to more than a dozen others in four days, and a dehumanizing slur that propagated across faction lines.
What we did not find was a single mastermind pulling strings from the shadows. The campaign targeting the Flynns is not a bot network. It is not a foreign intelligence operation. It is something that may be more dangerous than either: a fragmented, multi-faction assault carried out by real people with real audiences who do not coordinate with each other — and who, in several cases, actively despise one another. That structural fragmentation makes the campaign nearly impossible to counter through conventional means.
* * *
The Principals
Lt. Gen. Michael T. Flynn served as the 25th National Security Advisor to the 45th President of the United States. A retired three-star general with thirty-three years of military service, Flynn currently serves as Chairman of America's Future Inc., a 501(c)(3) nonprofit organization. His presence on X, where he posts under the handle @GenFlynn, reaches an audience measured in the millions across fourteen confirmed platforms including Truth Social, Telegram, Substack, and Rumble.
Mary Flynn O'Neil serves as Executive Director of America's Future. Under her leadership, the organization has focused significantly on child welfare advocacy, anti-child trafficking efforts, and CPS reform across multiple states. Her X account, @MaryFlynnONeil1, has approximately 10,200 followers — a fraction of her brother's audience. She maintains a posting cadence of roughly 185 posts per month, focused primarily on organizational communications and advocacy work.
This investigation was not concerned with the Flynns' political positions or public controversies. It was concerned with a specific question: Are the attacks directed at them organic public discourse, or do they exhibit the hallmarks of coordinated information operations?
* * *
How We Investigated
Operation LOOKING GLASS was a defensive information operations research effort conducted entirely through open-source intelligence methods. No private accounts were accessed. No hacking or social engineering was performed. Every piece of evidence cited in this article was drawn from publicly available posts, profiles, and interactions on X and other public platforms.
The investigation proceeded through four phases. In the first phase, we conducted reconnaissance — sweeping the Flynns' usernames across platforms, scanning X mentions for hostile accounts, and building an initial network baseline. In the second phase, we collected evidence: deep content scrapes of hostile post histories, amplification detection analysis, and a formal assessment of coordinated inauthentic behavior using eight standard indicators. In the third phase, we analyzed everything we had gathered — mapping the full DISARM kill chain for each threat actor, building a network graph of all actors and their relationships, scoring each threat across five dimensions, and tracking the evolution and velocity of seven distinct hostile narratives. The fourth phase produced this article.
Our analytical framework was the DISARM standard, an internationally recognized taxonomy for classifying information manipulation — comparable to the way the MITRE ATT&CK framework provides a common language for describing cyberattacks. It catalogs techniques across four phases: Plan, Prepare, Execute, and Assess. Our automated detection system, SENTINEL, matched seventeen of eighteen detection patterns against the activity we observed — the highest score possible short of a perfect match.
A note on what this framework cannot do: DISARM classifies observable behaviors. It cannot read minds. When we say an account deployed a particular technique, we are describing what the account did, not necessarily what the account holder intended. The distinction between deliberate manipulation and organic behavior that happens to match manipulation patterns is one we take seriously, and we address it directly in our findings.
* * *
What We Found: A Three-Front War
The most significant finding of this investigation is that the Flynns face not one coordinated campaign but three simultaneous, independent ones — attacking from different political directions with different narratives, different audiences, and different objectives. Understanding this three-faction structure is essential to understanding why the campaign is so difficult to counter.
Faction A: The Left-Wing Campaign
The longest-running and most technically sophisticated campaign originates from the political left, centered on Jim Stewartson (@jimstewartson), a Los Angeles-based figure with approximately 147,000 followers on X. Stewartson's core narrative — that Lt. Gen. Flynn created and controls QAnon as a deliberate psychological operation — has been sustained for more than four years.
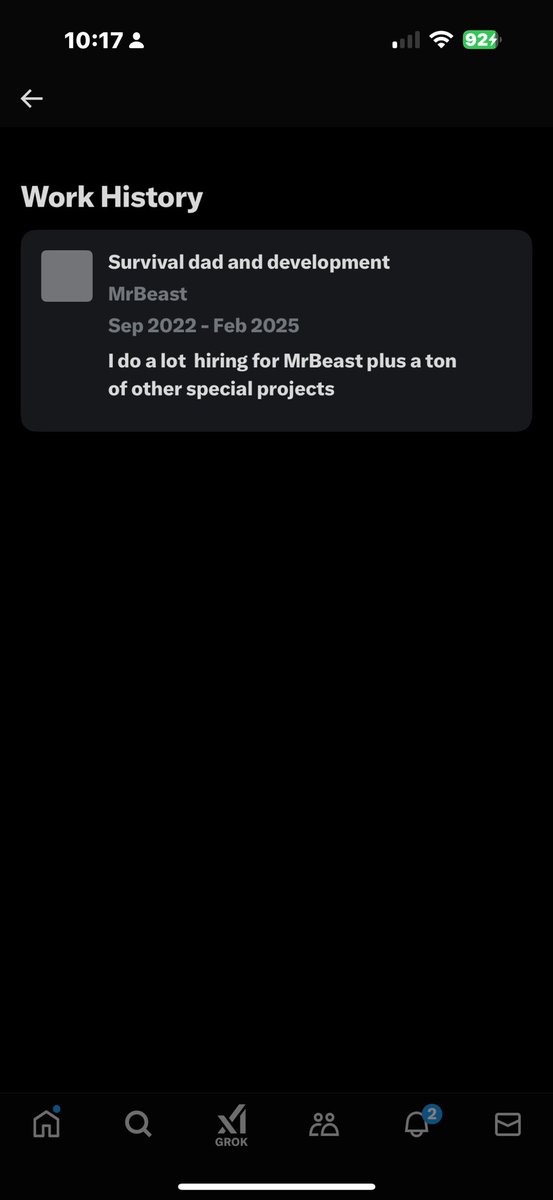
What makes Stewartson's operation distinctive is not its reach but its sophistication. Stewartson is a former CTO of 42 Entertainment and CEO of Fourth Wall Studios, companies that specialized in alternate reality games — elaborate, multi-platform interactive narratives designed to blur the line between fiction and reality. He is an Emmy award winner for his work in this field. Our analysis identified thirty-seven distinct DISARM information manipulation techniques in his output, spanning all four phases of the kill chain. This is the most complete operational profile we observed, classified at Level 4 (Advanced) on the IO maturity scale.
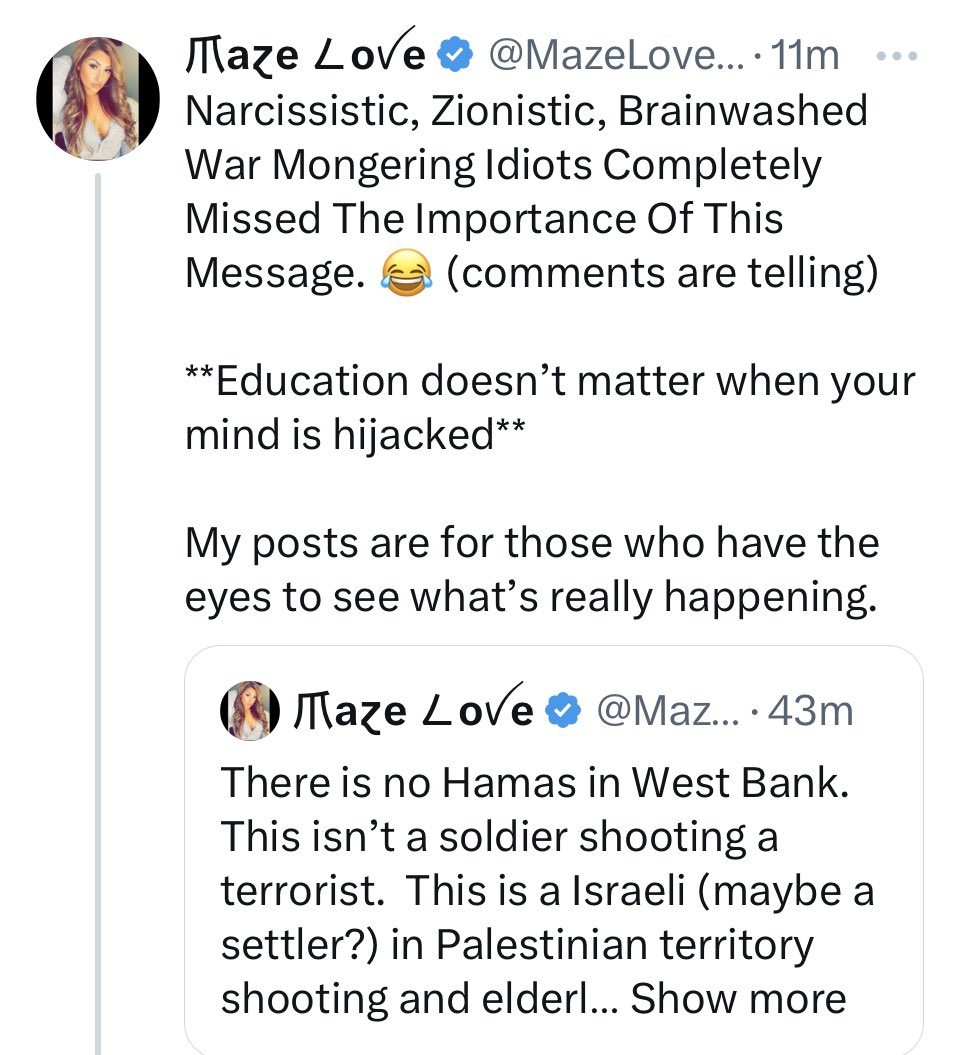
"Anyone 'disappointed' with Mike Flynn because he's working with foreign enemy nation-states has never met Mike Flynn. That's all he's been for 15 years, an anti-American whore for other governments." — @jimstewartson, March 21, 2026
Stewartson has created designated labels for both protected principals: "General QAnon" for Lt. Gen. Flynn and "Adrenochrome Mary" and "Pizzagate sister" for Mary Flynn O'Neil. He is the only threat actor who systematically targets both the General and his sister. He maintains dedicated infrastructure including a Substack newsletter (mind-war.com), a podcast (@RadicalizedPod), and cross-platform presence on Bluesky and Threads. He has been suspended from X twice previously. He claims to have posted more than 100,000 tweets about Flynn.
It is important to note that the core claim of Stewartson's campaign — that Flynn created QAnon — was examined by the Anti-Defamation League, which found no evidence to support it. Flynn filed a defamation lawsuit against Stewartson (Case No. 2023-CA-004264, Sarasota County, Florida), though reporting indicates the case was substantially narrowed.
Stewartson's wider network includes co-defendants in Flynn's lawsuit: Rick Wilson and the Lincoln Project, and MeidasTouch. However, our analysis found that Stewartson operates essentially as a solo actor with zero direct interactions with any right-wing accounts targeting Flynn. The left-right firewall in this ecosystem is absolute at the direct-interaction level.
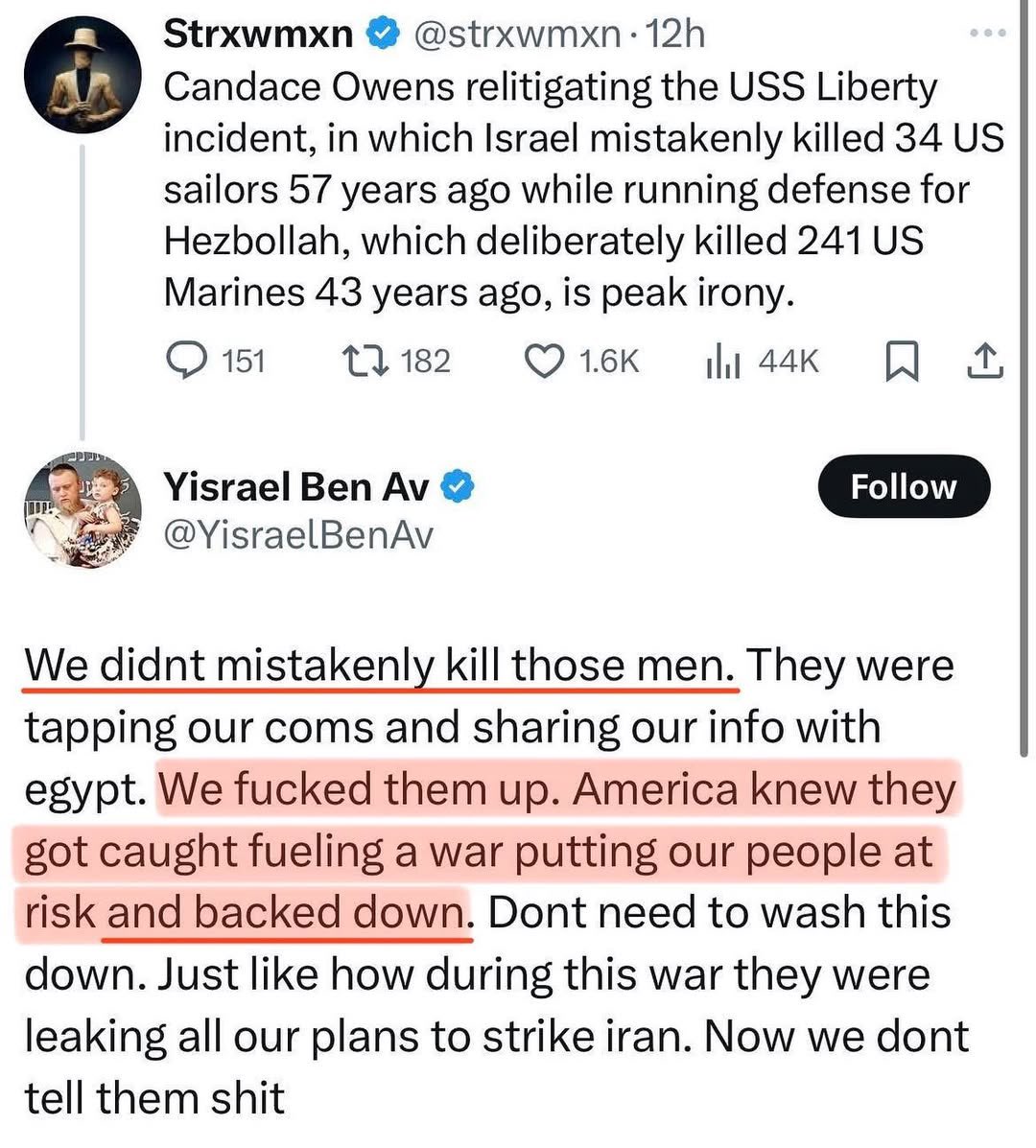
Faction B: The MAGA-Right Campaign
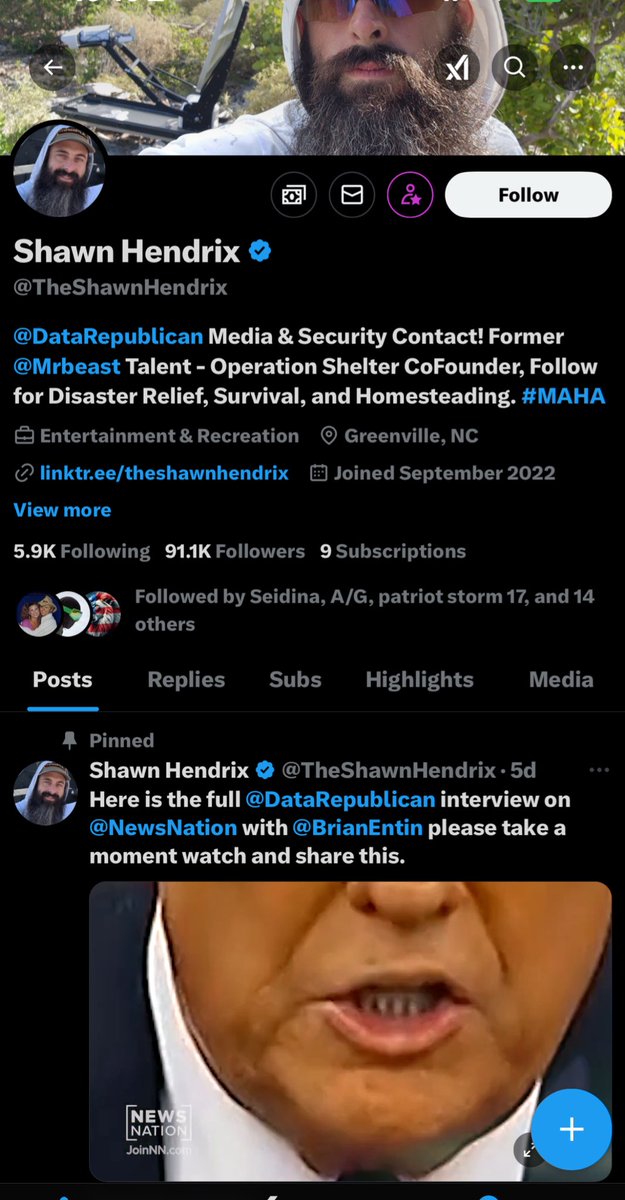
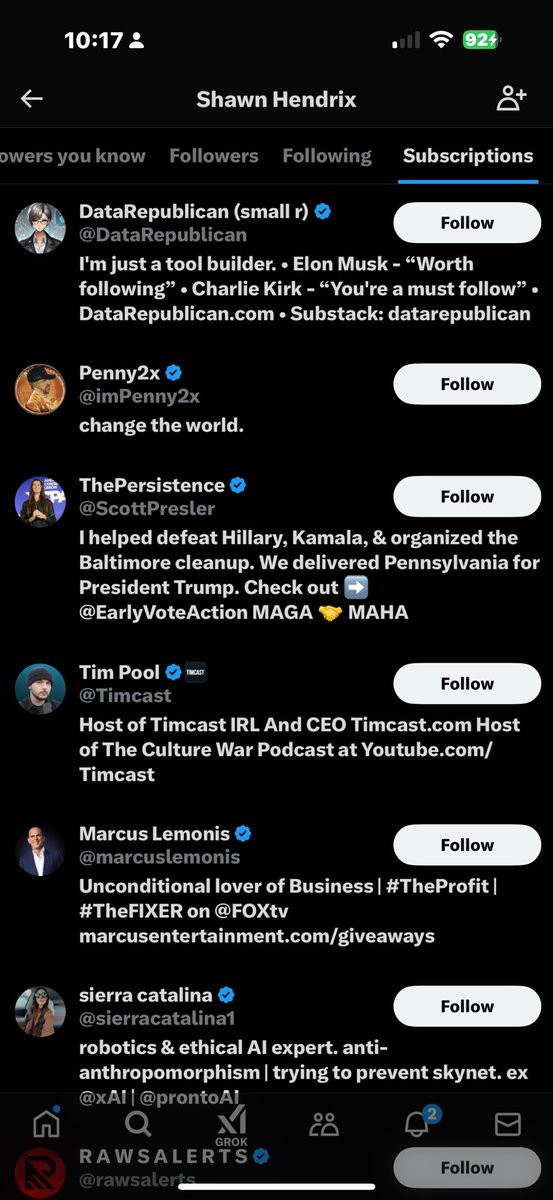
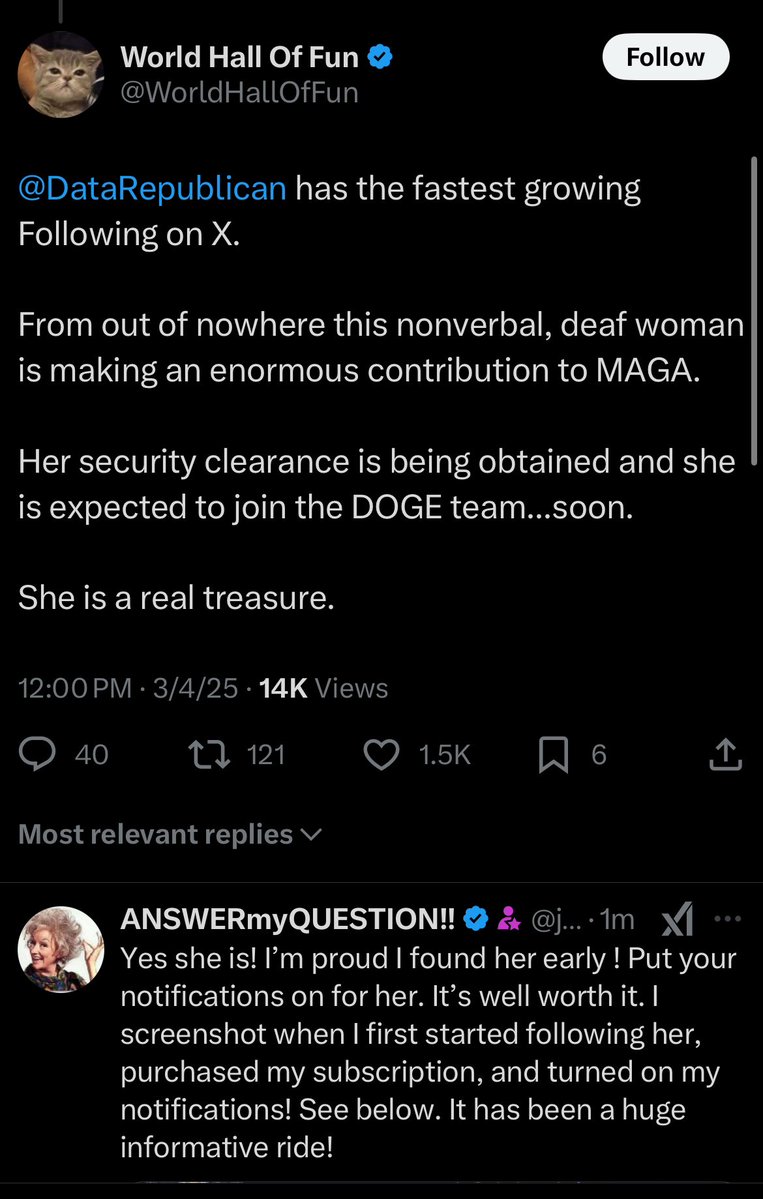
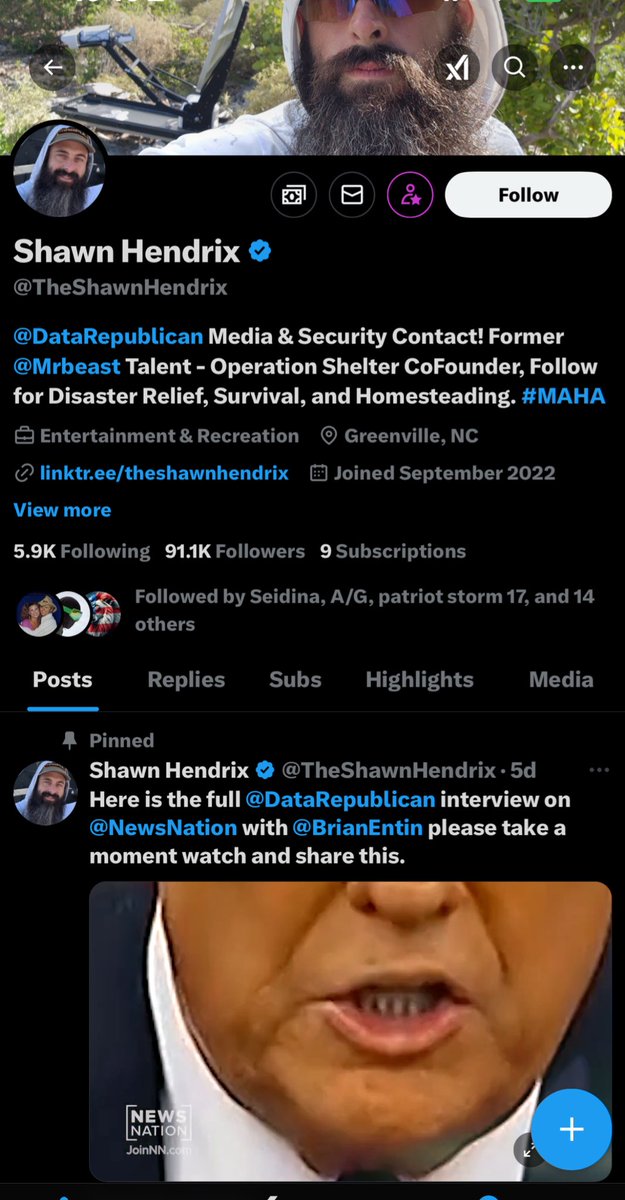
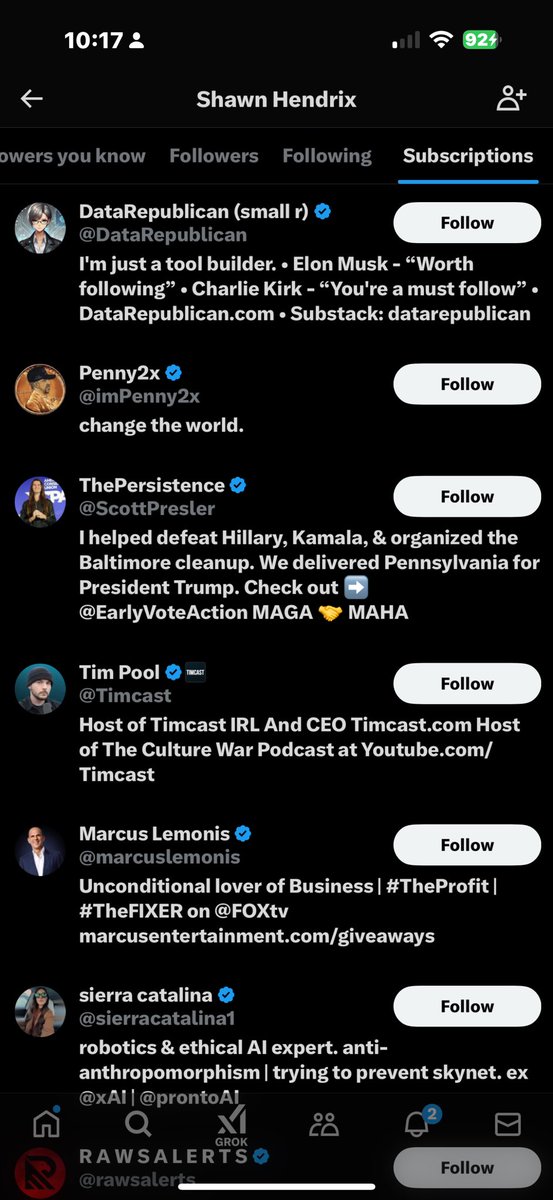
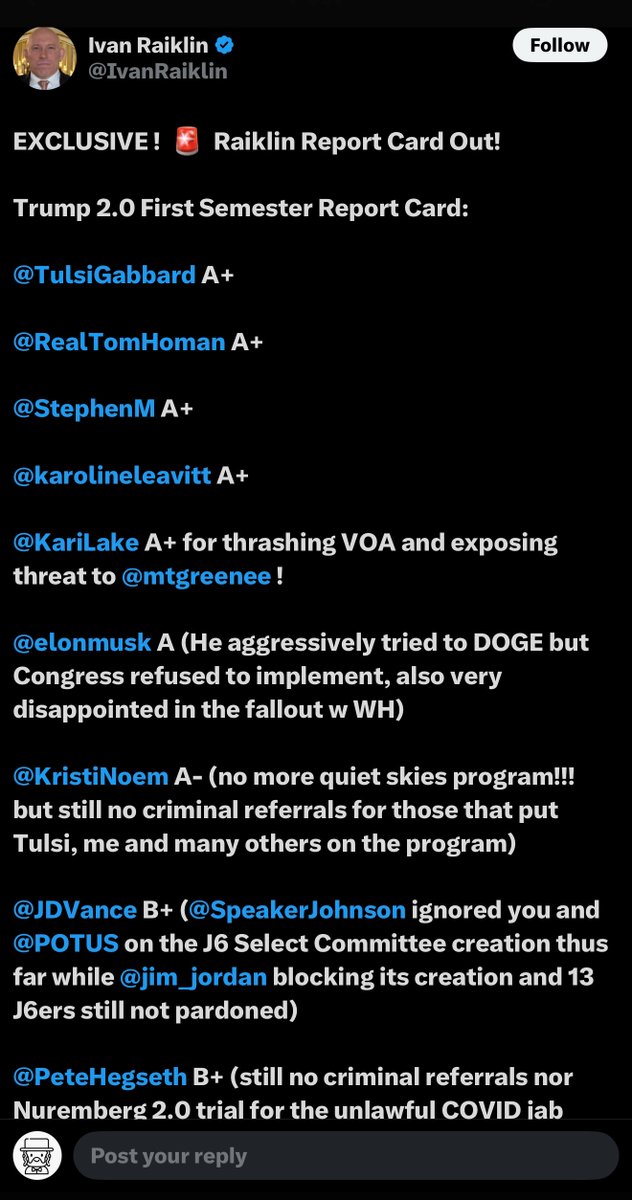
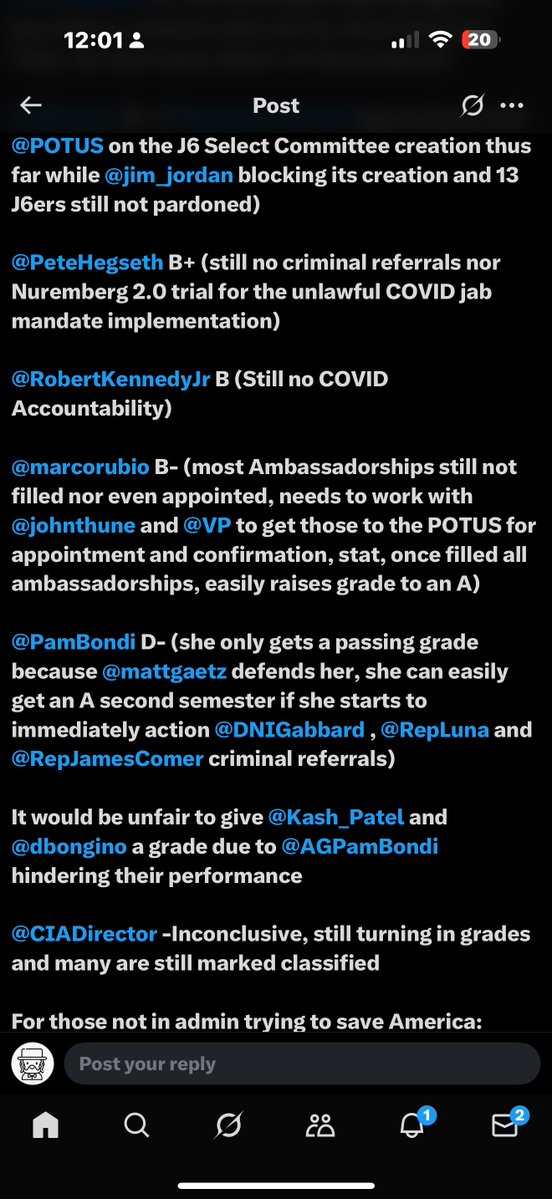
The highest-impact threat comes, perhaps counterintuitively, from within the Flynns' own political community. Laura Loomer (@LauraLoomer), with 1.8 million followers, is the faction's highest-reach actor. Her signature contribution is the term "Flynn Network" — a label she deploys in virtually every Flynn-related post, framing the retired general as the architect of a coordinated influence operation.
"It's funny how many people in the Flynn Network are sending their lunatic followers after me for calling out General Flynn @GenFlynn for promoting Tucker Carlson's interview with a CCP propagandist from China." — @LauraLoomer, March 22, 2026 | 2,987 likes, 292,276 views
Brenden Dilley (@WarlordDilley), with 276,600 followers, operates a declared amplification network called the Dilley Meme Team. Dilley is the originator of a dehumanizing slur directed at Flynn — "Genital Flynn" — which our analysis tracked as it propagated from his account to at least nine others within days.
Our amplification analysis documented twenty-three direct cross-tagging interactions between Loomer and Dilley. Their posting about Flynn shows temporal clustering — both accounts posted Flynn attacks within overlapping windows on March 21-22, 2026.
Perhaps the most significant finding: On January 28, 2026, an anti-Flynn video produced by the Dilley Meme Team was posted to President Trump's Truth Social account. This represents presidential-level distribution access for anti-Flynn content — a capability no other hostile actor possesses.
Faction C: The MG Show Cluster
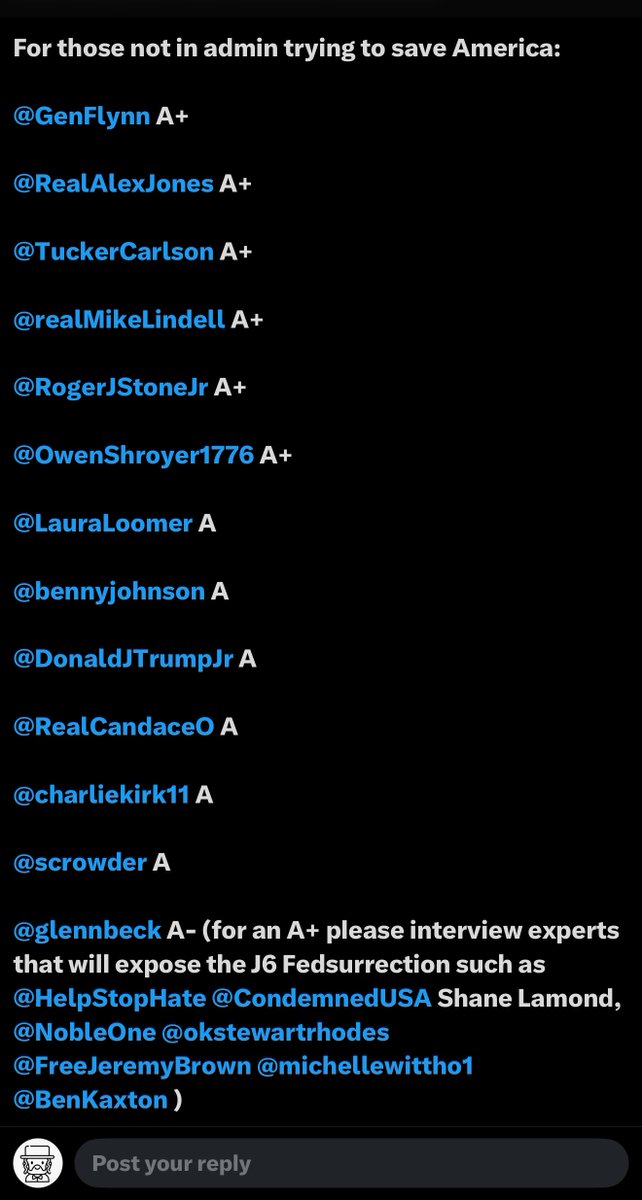
The third faction — centered on Jeffrey Pedersen (@intheMatrixxx, 185,200 followers), @ShadyGrooove (57,000 followers), and @The_AuthorityQ (15,000 followers) — operates a daily show format dedicating substantial airtime to attacking Flynn. Their internal cluster density is the highest in the network, with coordinated posting bursts reaching twenty-one posts in a single day.
What makes Faction C strategically significant is its relationship to Faction B. The MG Show considers Loomer herself to be part of the "Flynn Network" — an ironic inversion of the very label Loomer coined. The right-wing anti-Flynn ecosystem is itself fragmented, with two factions that attack Flynn while simultaneously attacking each other.
The Institutional Layer
Beyond the three active factions, institutional actors — including the SPLC's "Extremist File" on Flynn and Issue One's analyses of America's Future's 990 tax filings — provide source material that active hostile accounts cite to lend credibility to their claims. These are not information operations in the DISARM sense, but they serve as narrative fuel.
* * *
The Convergence Event
On March 25, 2026, all three factions fired simultaneously.
The trigger was a thread posted by Alexis Wilkins, identified as the girlfriend of Kash Patel, alleging that Flynn was involved in a twenty-two-month foreign-linked influence network. The thread accumulated 3.1 million retweet engagements and was amplified by accounts associated with RT.com — Russia's state-funded media outlet.
Within hours, Laura Loomer, Brenden Dilley, Jeffrey Pedersen, Jim Stewartson, and others were all amplifying the same narrative: Flynn as foreign agent.
This convergence was organic. Our analysis found no evidence of coordination between the factions. They simply reacted to the same external stimulus in parallel, driven by pre-existing hostility. The effect, however, was indistinguishable from a coordinated attack: a simultaneous, multi-directional barrage with a combined potential reach exceeding 4.9 million accounts.
Our assessment is that the Wilkins thread has established a template. Future trigger events involving foreign policy, foreign contacts, or foreign influence allegations will likely produce automatic cross-faction convergence. The "foreign agent" narrative is the one theme on which left, right, and center will all fire at once — without any coordination required.
* * *
The Human Cost: Mary Flynn O'Neil
While Lt. Gen. Flynn's public profile provides a degree of resilience, his sister occupies a fundamentally different position. Mary Flynn O'Neil has approximately 10,200 followers. She runs a nonprofit. She advocates for child welfare. And she has become a deliberate target.
Our investigation identified a now-degraded account, @KassandraSeven, that posted 459 mentions of Mary Flynn O'Neil in a three-week period — more than twenty targeted posts per day directed at a single individual.
Stewartson has created specific dehumanizing labels for her: "Adrenochrome Mary" and "Pizzagate sister" — terms designed to associate her child welfare advocacy with conspiracy theories, effectively weaponizing her own advocacy work against her.
On a single day, @miguelifornia posted six messages in fifty-three minutes targeting America's Future's counsel and organizational operations. This is not criticism of a public figure's policy positions. This is a sustained effort to damage the professional and organizational life of a private citizen whose primary public activity is advocating for at-risk children.
* * *
The Network: How the Campaign Operates
Our network analysis mapped forty-two nodes and sixty-seven edges. At the center sits @GenFlynn himself, with twenty-two connections — the most connected node, because every hostile actor targets him. Laura Loomer holds the highest hostile out-degree at fourteen connections. But the most structurally important node is the Alexis Wilkins thread, which scored the highest betweenness centrality at 0.92 — the primary bridge connecting otherwise disconnected clusters.
The hostile network is structurally anti-fragile — its very fragmentation into mutually hostile factions makes it impossible to neutralize through any single intervention. Remove Stewartson, and the right-wing factions continue unaffected. Silence Loomer, and the MG Show fills the void. This is a campaign that cannot be decapitated because it has no head.
The hostile factions produce over fifty posts per day about Flynn during spike periods; the defense network produces roughly ten. The reach asymmetry is twenty-five to one.
* * *
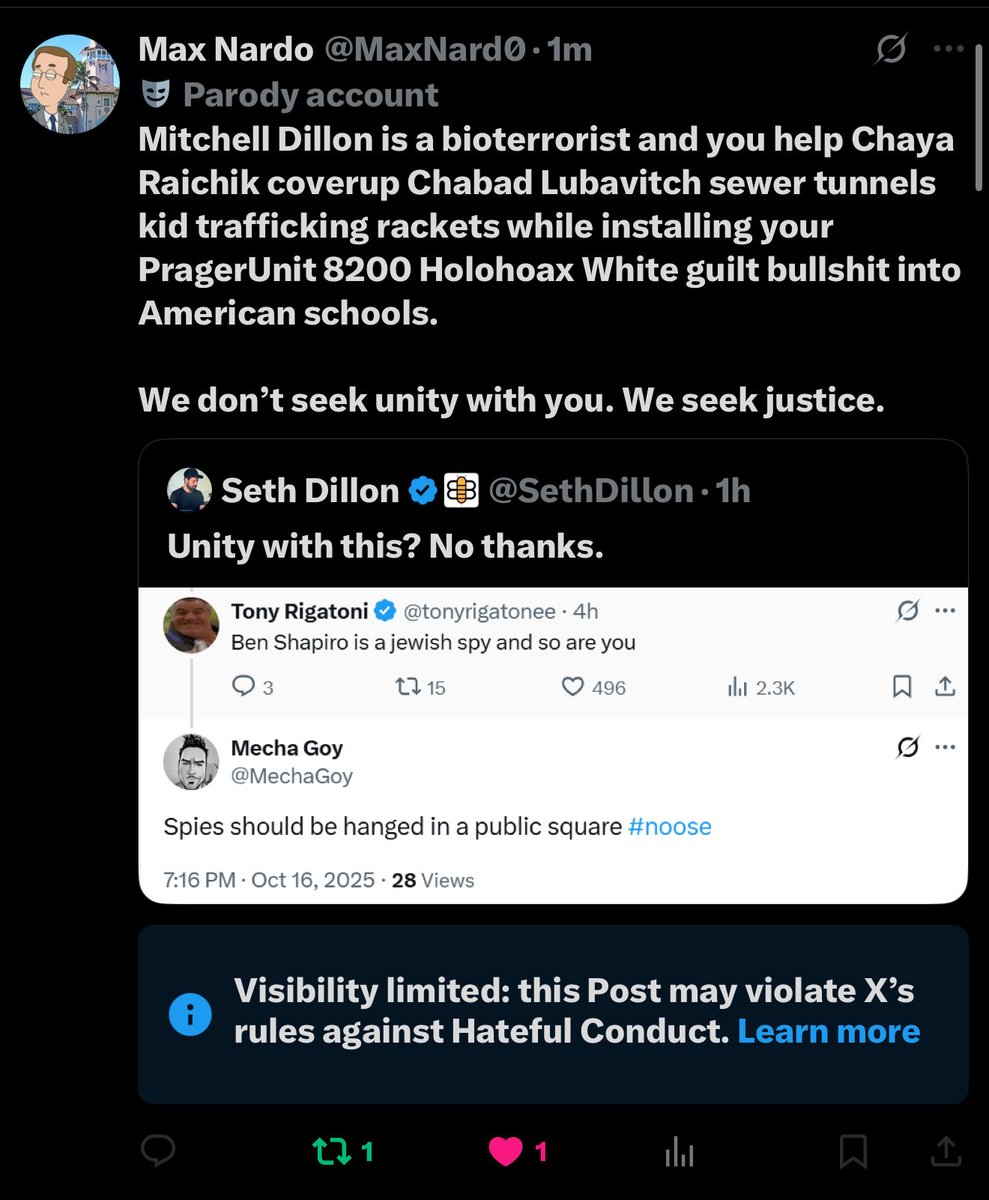
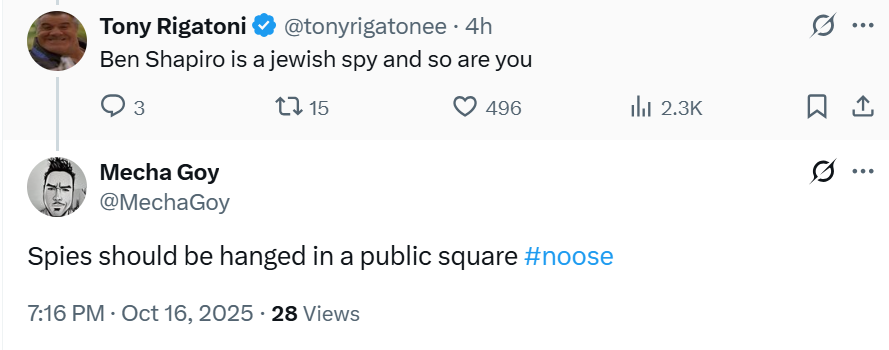
The Sockpuppets: Inauthentic Actors in an Authentic Campaign
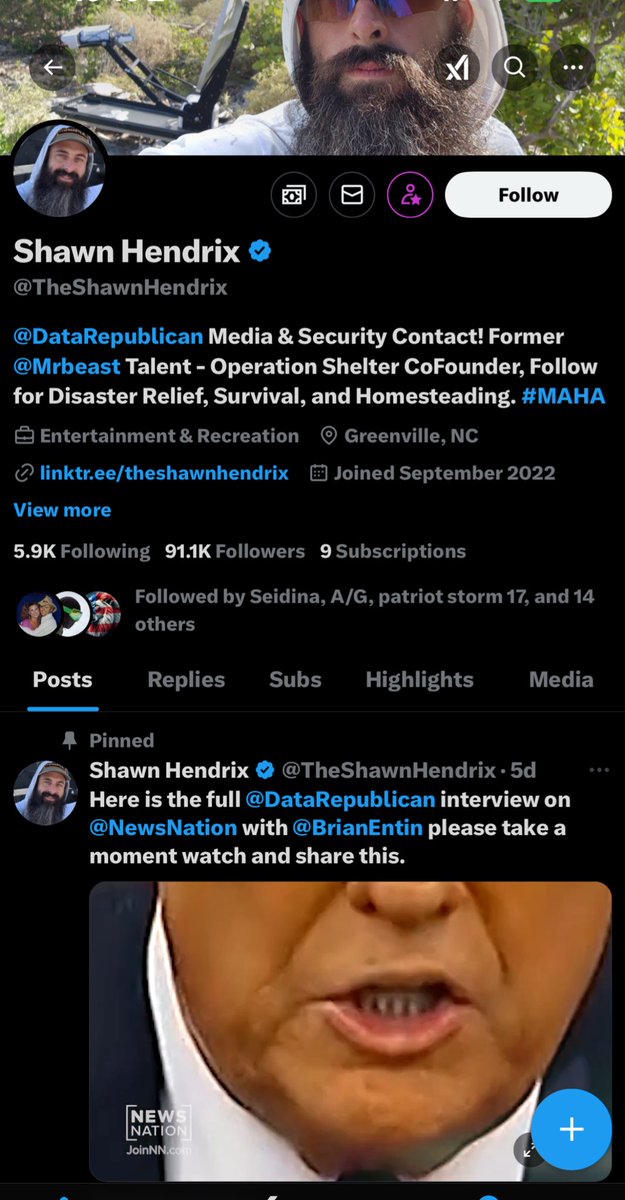
While the campaign is overwhelmingly authentic, our CIB assessment identified two accounts with significant markers of coordinated inauthentic behavior.
@TootslilFighter scored five of eight CIB indicators. The account's bio contains a hexadecimal string that decodes to "@Jared_T_Swift," identifying the likely operator as James Lefeber. The account exhibits extreme posting volume, artificial growth patterns, and link-farming behavior.
@FindTheNexus scored three of eight CIB indicators. Created in September 2025 with only 332 followers, it appears purpose-built for attacking Flynn, serving as a cross-pollination vector between Faction B's sub-groups.
No cross-faction CIB was detected. The left-right divide is maintained by genuine mutual hostility.
* * *
A Necessary Distinction: Organic Criticism vs. Information Operations
Not everything that looks like an information operation is one. Conspirador Norteño (@conspirator0), a data scientist initially flagged as a potential Stewartson ally, was reclassified as an independent actor upon closer analysis — Stewartson had actually attacked him publicly.
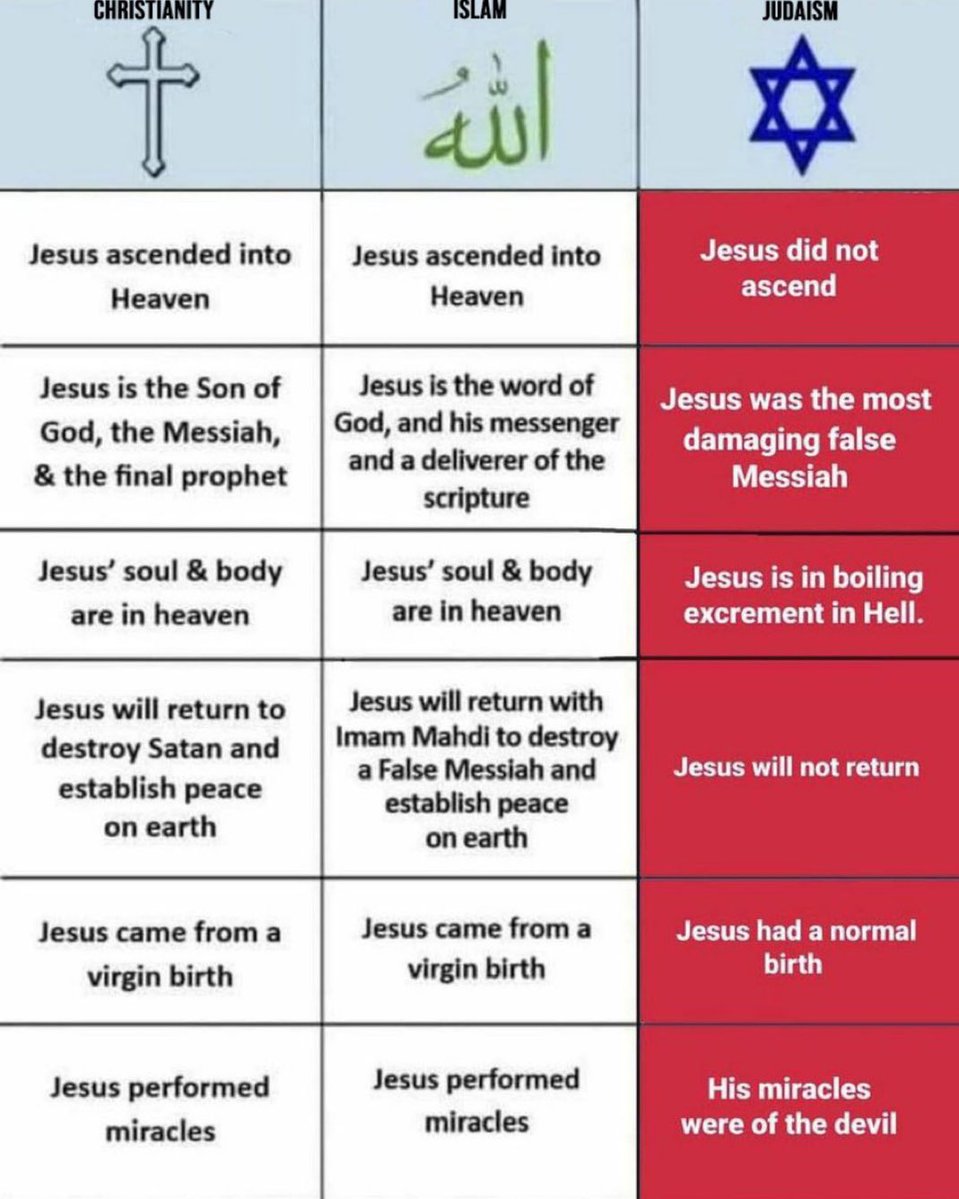
This distinction matters. A healthy public sphere requires the ability to criticize public figures, including harshly. When we classify something as an information operation, we are not saying the speaker is wrong. We are saying the speaker is employing techniques — narrative seeding, coordinated amplification, manufactured terminology, dehumanizing labels — that go beyond criticism into deliberate manipulation.
* * *
The Techniques: How Information Operations Work
The DISARM framework organizes techniques into four phases, and we found evidence of all four.
Phase 1 — Plan: We identified seven distinct narratives, each with its own originator and propagation pattern. The "Flynn Network" label was a deliberate narrative construction. The "Foreign Agent/FARA" narrative achieved the highest threat score at 9.0 out of 10.
Phase 2 — Prepare: Operators build infrastructure before they strike. Stewartson maintains a dedicated website and podcast. The Dilley Meme Team is a declared content production factory. The MG Show runs a daily distribution pipeline.
Phase 3 — Execute: We documented narrative seeding, coordinated amplification (twenty-three mutual tags between Loomer and Dilley), terminology propagation ("Flynn Network" spreading from one account to twelve in four days), dehumanization, and target expansion.
Phase 4 — Assess: The most sophisticated operators evaluate their own effectiveness. Stewartson's self-referential posts ("I deserve recognition for my efforts") indicate awareness of his campaign as a deliberate project.
Sixteen techniques were independently deployed by all three factions — "triple deployment" — creating a compounding effect that requires three simultaneous counter-narratives for three different audiences.
* * *
Case Study: How a Label Becomes a Weapon
The propagation of the term "Flynn Network" illustrates how information operations manufacture consensus:
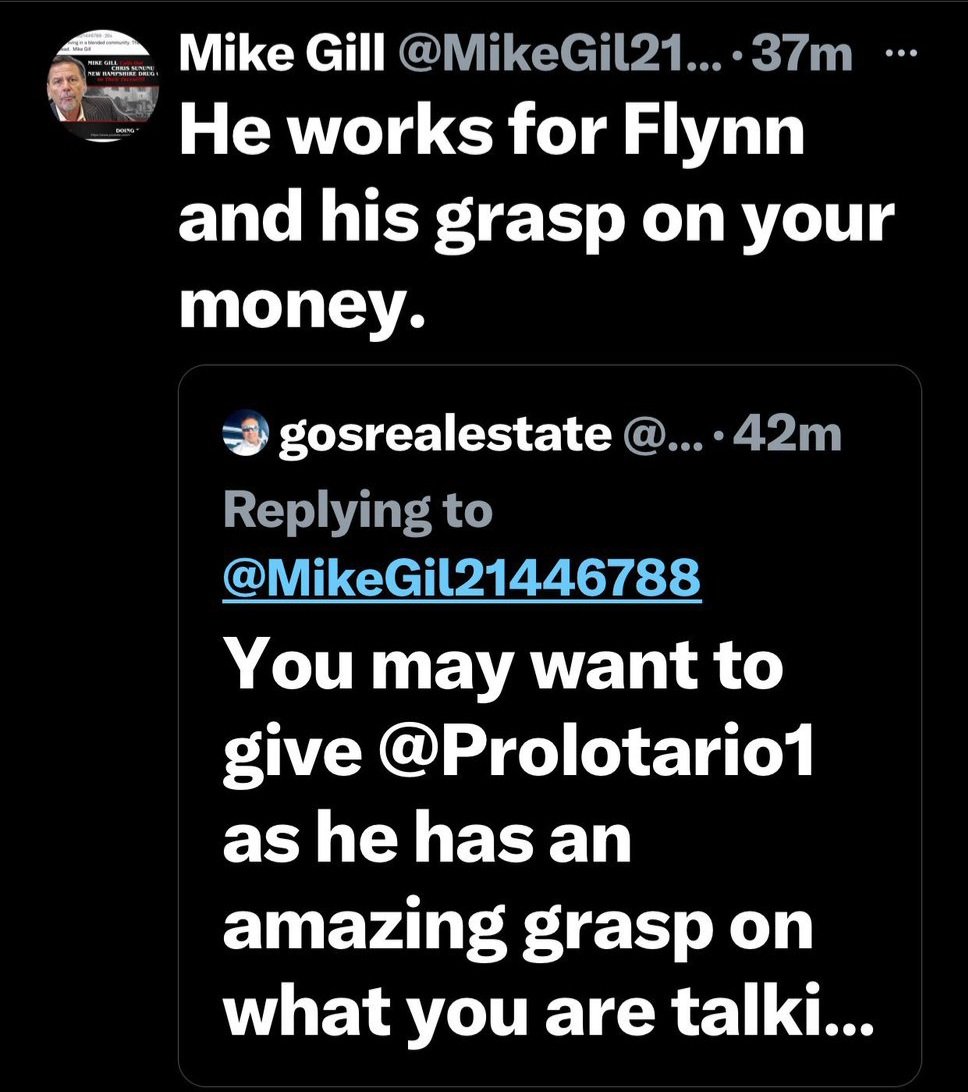
Day 1: The label appears in posts by @LauraLoomer and/or @Prolotario1.
Days 2-3: @WarlordDilley adopts it. @FindTheNexus begins using it. @intheMatrixxx quotes Loomer's posts containing it.
Days 3-4: @ShadyGrooove, @marley_kingsley, @patriotwomanQ, @Ringo391854 begin using the term organically.
Day 5: The term is self-sustaining. Twelve or more accounts use it independently. Estimated cumulative impressions exceed fifty million. The label has achieved "narrative escape velocity."
In the DISARM framework, this is technique T0022: Seed Distortions. A manufactured frame reaches critical mass and becomes part of the ambient information environment.
* * *
Four Years, Zero Defense
Perhaps the most striking finding is not what the hostile network has done, but what the defense network has not.
In more than four years of sustained information operations against the Flynns, our analysis found no evidence of a coordinated defensive counter-narrative. The defense network's clustering coefficient is 0.12, compared to hostile clustering coefficients ranging from 0.40 to 1.00. The reach asymmetry is twenty-five to one.
The Flynns are not without allies — our mapping identified a defense cluster with a combined potential reach exceeding four million. But potential reach and active defense are different things. The defense network is almost entirely passive.
The result is an information environment in which seven hostile narratives circulate continuously, two have achieved escape velocity, and the only counter-narrative is silence.
* * *
What This Means: The Broader Picture
The campaign against the Flynn family is a case study in a phenomenon reshaping public discourse: the weaponization of authentic coordination.
Platform countermeasures were designed for bot networks, fake accounts, and foreign interference. They are poorly suited to address real people, using their real names, with genuine audiences, deploying sophisticated information manipulation techniques in plain sight.
The anti-fragile structure — three factions that share no infrastructure and actively oppose each other — means no single intervention can address the problem. This structural dynamic is not Flynn-specific. It is an emerging feature of the information environment that will affect any public figure who attracts opposition from multiple political directions simultaneously.
* * *
In Their Own Words: Stated Motivations
Fair reporting requires presenting the threat actors' stated reasons for their campaigns.
Jim Stewartson frames his campaign as accountability journalism, characterizing Flynn as the architect of QAnon. Laura Loomer frames hers as exposing what she sees as a betrayal of the MAGA movement. The MG Show cluster frames its campaign as exposing financial grift.
We present these stated motivations without endorsing them. What our investigation examined was not whether these actors believe what they say, but whether the methods they use cross the line from criticism into information manipulation. The DISARM framework analysis demonstrates that they do — repeatedly, systematically, and with increasing sophistication.
* * *
Methodology
Operation: LOOKING GLASS (OP-2026-0006), conducted March 25–27, 2026 by Sierra Special Investigations LLC.
Phases:
- P0 Planning,
- P1 Reconnaissance (2 OSINT sweeps, 2 X mention scans, 15 hostile account profiles),
- P2 Collection (63 posts captured, 47 cross-amplification links, 17 evidence items with SHA-256 hashes),
- P3 Analysis (53 DISARM techniques, 42-node network graph, 20-actor threat scoring, game theory modeling, 7 narrative velocity profiles),
- P4 Reporting.
Framework: DISARM (Disinformation Analysis and Risk Management), an internationally recognized standard comparable to MITRE ATT&CK for cybersecurity.
Detection: SENTINEL matched 17/18 patterns. Overall threat score: 10/10 CRITICAL. IO maturity: Level 4 ADVANCED.
Limitations: Compressed investigation timeline. X rate limiting constrained historical depth. DISARM describes behaviors, not intent. Some Grok queries returned partial results. @KassandraSeven was non-functional at time of collection. All data is point-in-time.
Confidence: B2 — Usually Reliable Source, Probably True.
Our next step is to INCREASE the IO data pool, We believe that using more IO framing models will only expose more coordination and information manipulation. We are just beginning.
* * *
Disclosure
Client Relationship: This investigation was conducted in connection with protecting the reputational interests of the subjects. We disclose this openly because transparency about our position is essential to the credibility of our findings.
Editorial Independence: The analysis reflects what we actually found, including findings that complicate simple narratives. We documented that the campaign is not CIB. We reclassified @conspirator0 from threat actor to independent critic. We acknowledged the threat actors' stated motivations. We identified weaknesses in the defense network. These editorial choices reflect our commitment to analytical integrity over advocacy.
No Classified Sources: Only open-source intelligence was used.
* * *
Conclusion
The campaign against the Flynn family is real, it is sustained, it is sophisticated, and it is growing. Three factions, operating independently from opposite ends of the political spectrum, have deployed fifty-three documented information manipulation techniques against a retired general and his sister over more than four years. Two hostile narratives have achieved escape velocity. A dehumanizing slur is propagating across faction lines. A convergence template has been established. And for four years, the response has been silence.
We publish this investigation not to advocate for any political position, but to document what we found with the rigor and transparency that the subject demands. Information operations thrive in darkness. The most effective countermeasure is, and has always been, daylight.
If you found this investigation valuable: Share this article to help expose how information operations work. Follow @SpartanX_Ray for more OSINT analysis and media literacy content. This investigation was conducted by Sierra Special Investigations LLC using the DISARM framework — the international standard for classifying information manipulation. Learn more about DISARM at disarm.foundation.