reSee.it - Related Post Feed

@themarketswork - Jeff Carlson
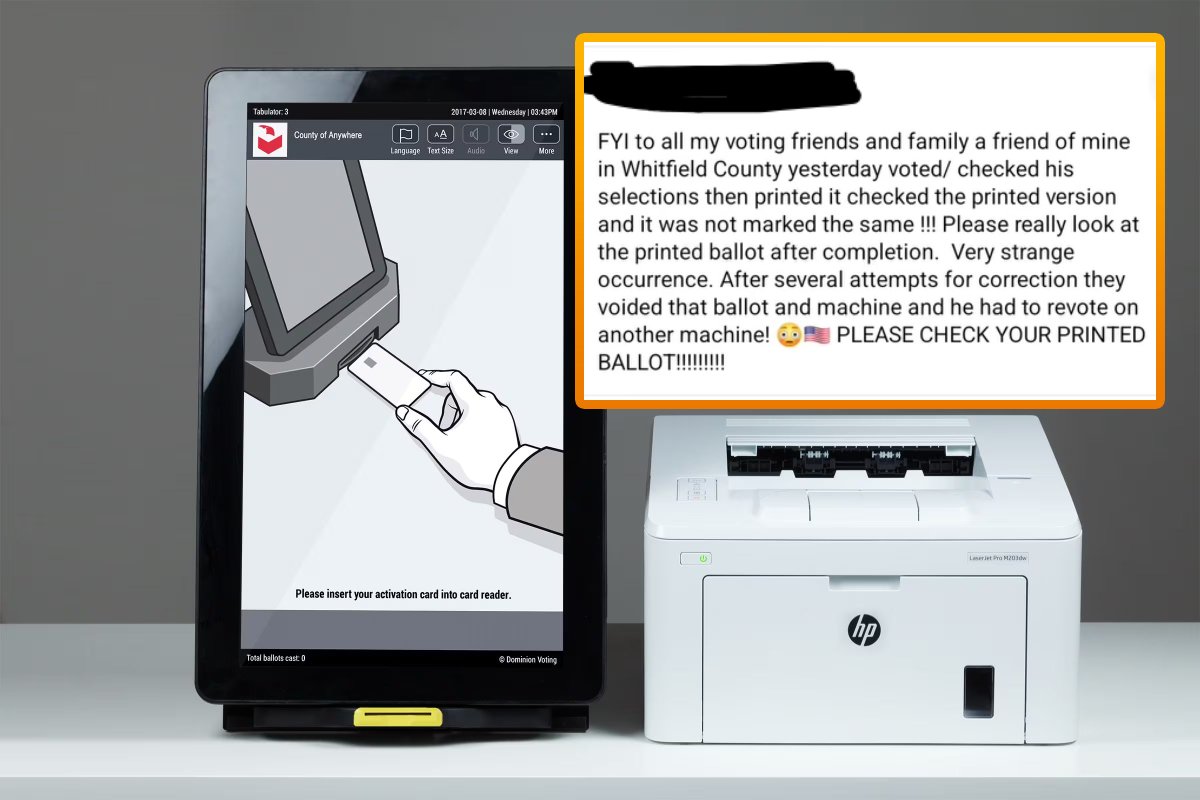
1) Georgia Years-long Court Battle Reveals Dominion’s Security and Audit Flaws, Weak Testing Rushed implementation of voting system questioned as experts raised fundamental concerns https://www.theepochtimes.com/georgia-years-long-court-battle-reveals-dominions-security-and-audit-flaws-weak-testing_3611494.html

@themarketswork - Jeff Carlson
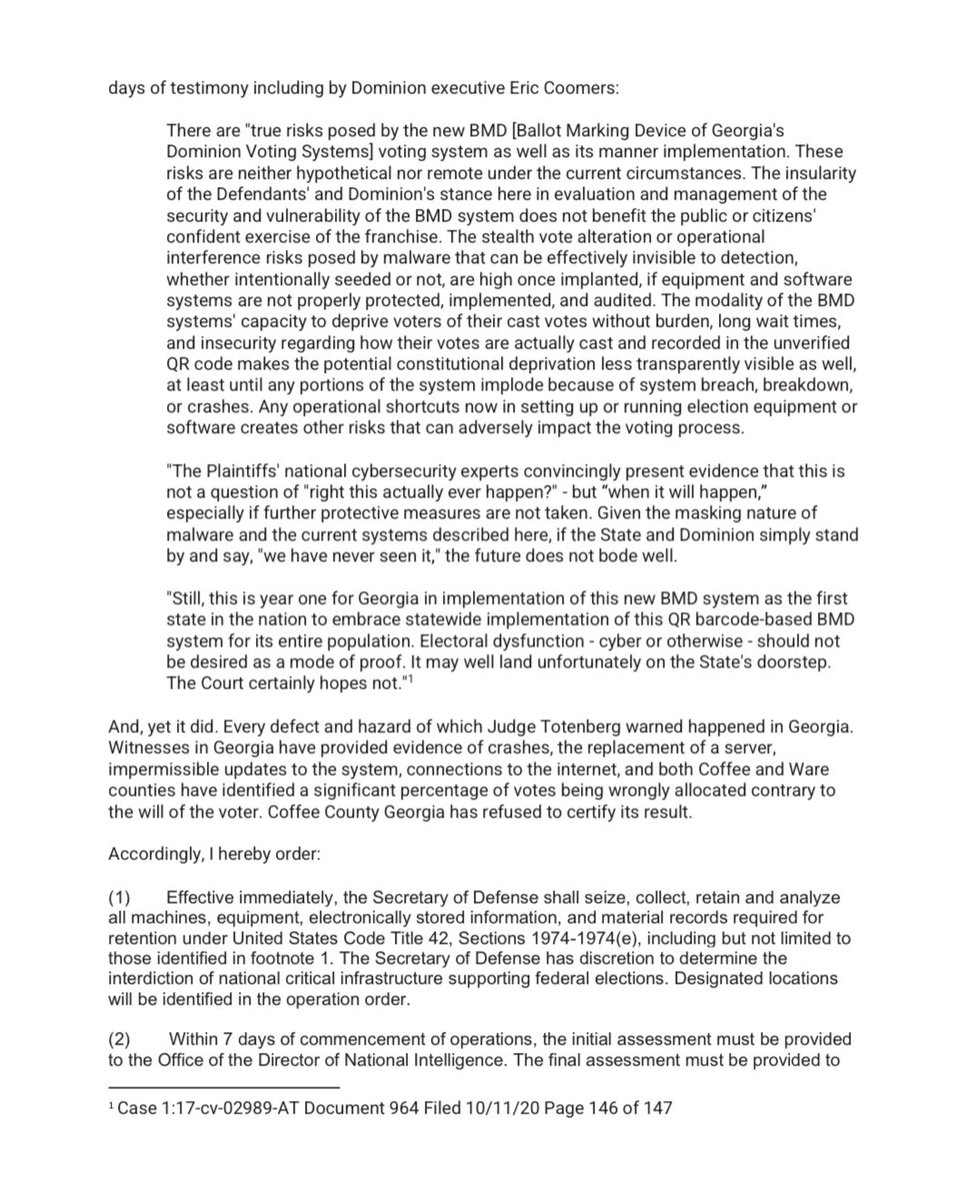
2) A review of court documents and sworn expert testimonies raise troubling questions regarding the Dominion voting system and its rushed implementation by the State of Georgia.
@themarketswork - Jeff Carlson
3) Among the many issues raised was the inability to accurately audit Dominion’s systems in order to verify that the intended votes were cast as intended.
@themarketswork - Jeff Carlson
4) Experts also demonstrated to the court how the Dominion system inherently prevented the successful use of Risk-Limiting Audits (RLAs) - the method employed by Georgia & VotingWorks during the recount.
@themarketswork - Jeff Carlson
5) Judge Totenberg agreed with the inability to successfully perform a RLA, noting in her ruling that “there is no audit remedy that can confirm the reliability and accuracy of the BMD system, as Dr. Stark has stressed.”
@themarketswork - Jeff Carlson
6) Cybersecurity experts provided evidence to the court that Dominion’s QR system wasn’t secure, was subject to duplication, and that the ability to generate fake QR codes existed.
@themarketswork - Jeff Carlson
7) A cybersecurity expert also found that during Georgia’s August 2020 elections, servers at two county election offices he visited “enabled unsafe remote access to the system through a variety of means,” including the use of flash drives.
@themarketswork - Jeff Carlson
8) This same expert found that in one of these counties, “server logs were not regularly recording or updated in full and that Dominion’s technical staff maintained control over the logs and made deletions in portions of the logs.”
@themarketswork - Jeff Carlson
9) Experts also found significant problems with the testing processes used by Pro V&V. In a case that involved last-minute updates to Dominion software, the court was told that the testing lab “performed only cursory testing of this new software.”
@themarketswork - Jeff Carlson
10) A Dominion system experienced a “memory lockup” after scanning only 4,500 ballots during testing in 2019. Dominion determined that a “power cycle” is required after scanning more than 4,000 ballots. It isn’t known if this issue was fixed prior to the 2020 elections.
@themarketswork - Jeff Carlson
11) The court also found that the manner in which the Dominion system functions failed to meet the requirements of Georgia election law. As U.S. District Judge Amy Judge Totenberg noted, Dominion’s system “does not produce a voter-verifiable paper ballot." /END

@Curiousityfirst - DogAndBone @Curious Cat
@jhalderm the same guy that found the Dominion vulnerability, wherein instead of stating they breached their contract, he ensured that DOMINION's CVR's were "sanitised" to make it difficult to analyse. @JanuszP20 @noodles @CannConActual @TxSaving https://t.co/AL4uliCgdh

@imyourmoderator - Chris Paul
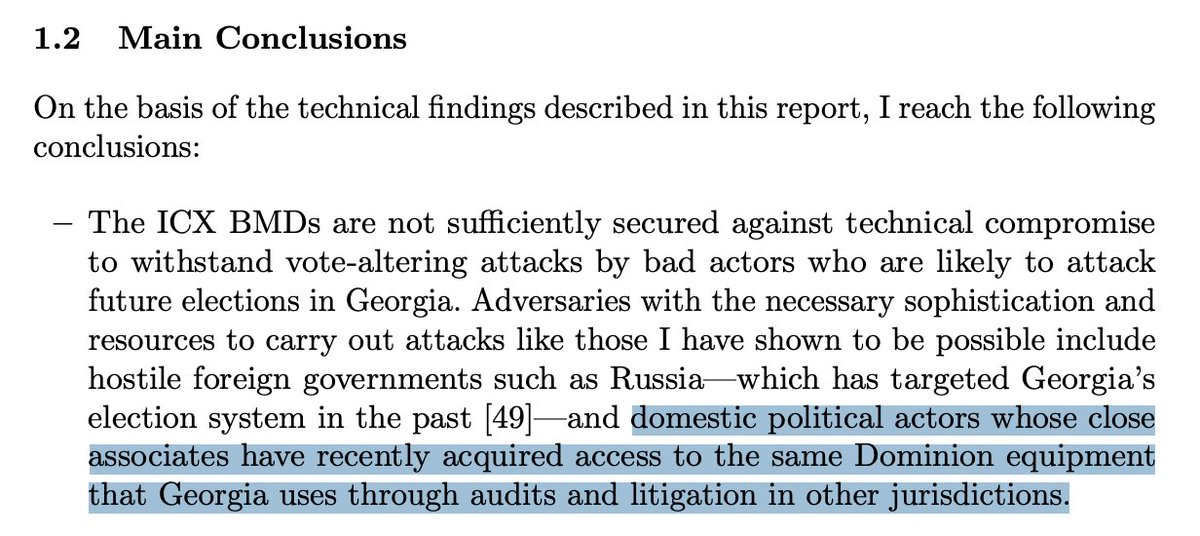
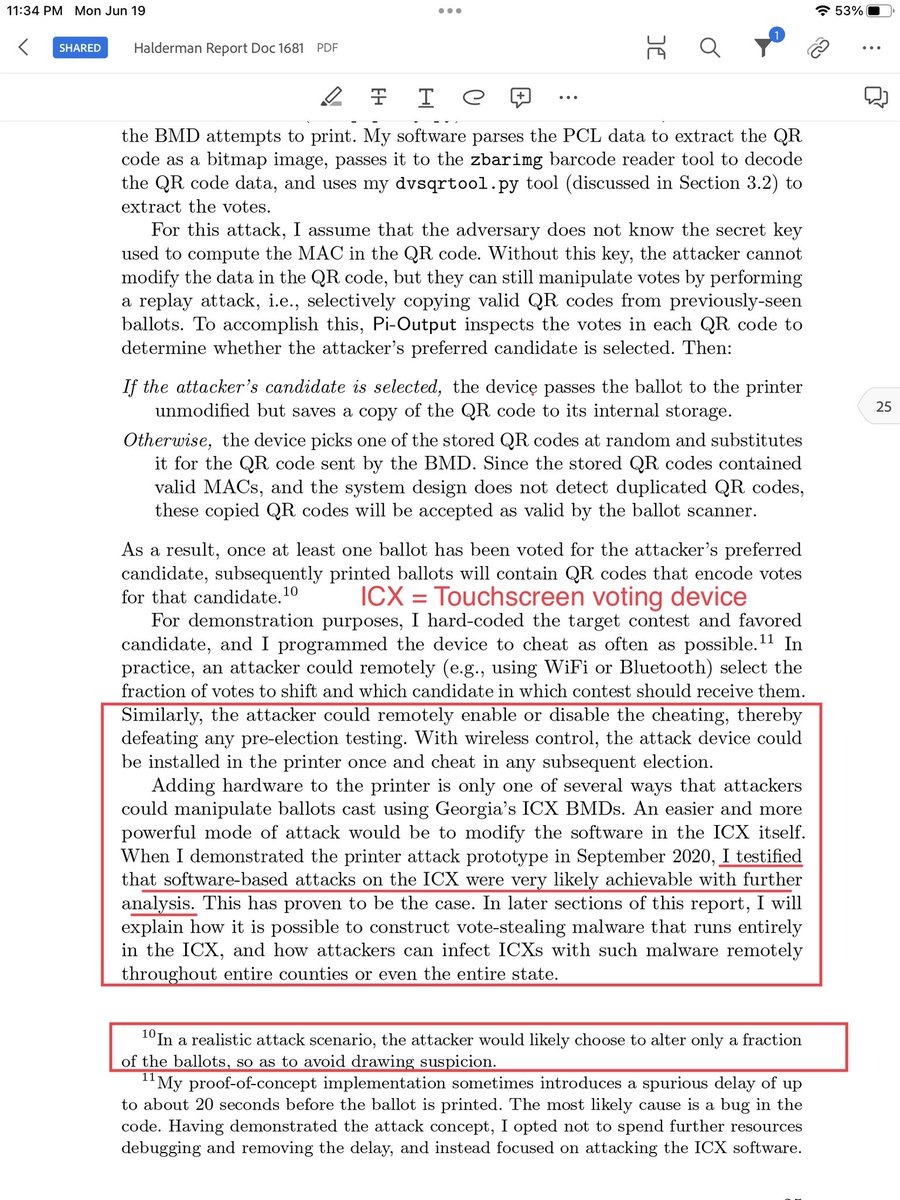
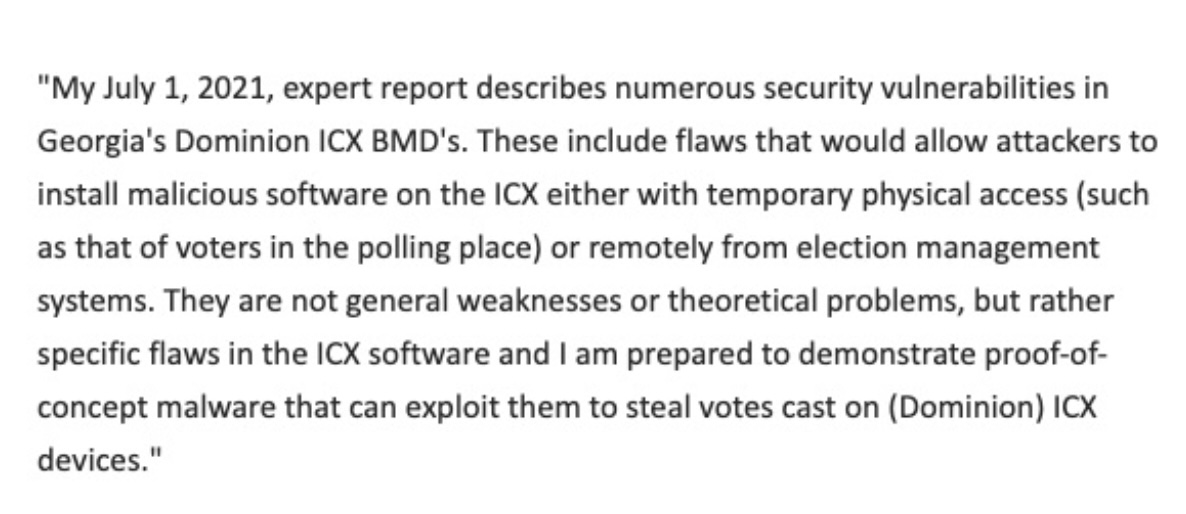
Halderman report. “There is no realistic mechanism to fully secure vote casting and tabulation computer systems from cyber threats.” "Many of the attacks I successfully implemented could be effectuated by malicious actors with very limited time and access to the machines, as little as mere minutes. This report documents my findings and conclusions." https://storage.courtlistener.com/recap/gov.uscourts.gand.240678/gov.uscourts.gand.240678.1681.0.pdf
@imyourmoderator - Chris Paul
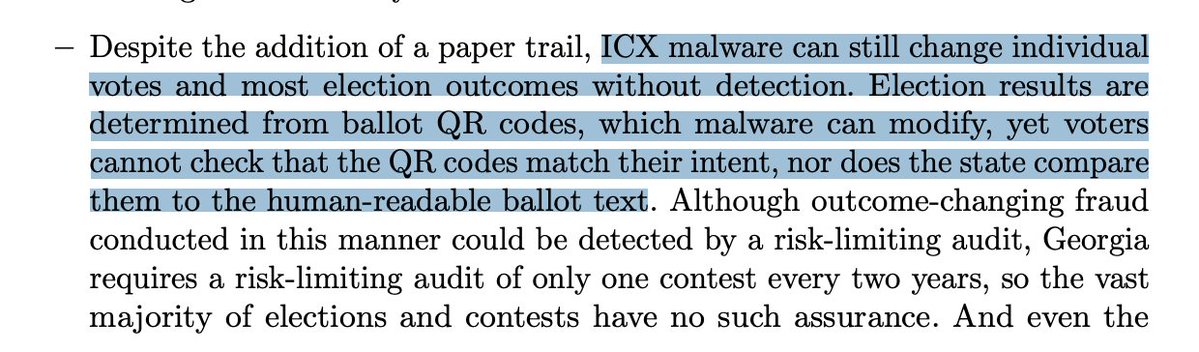
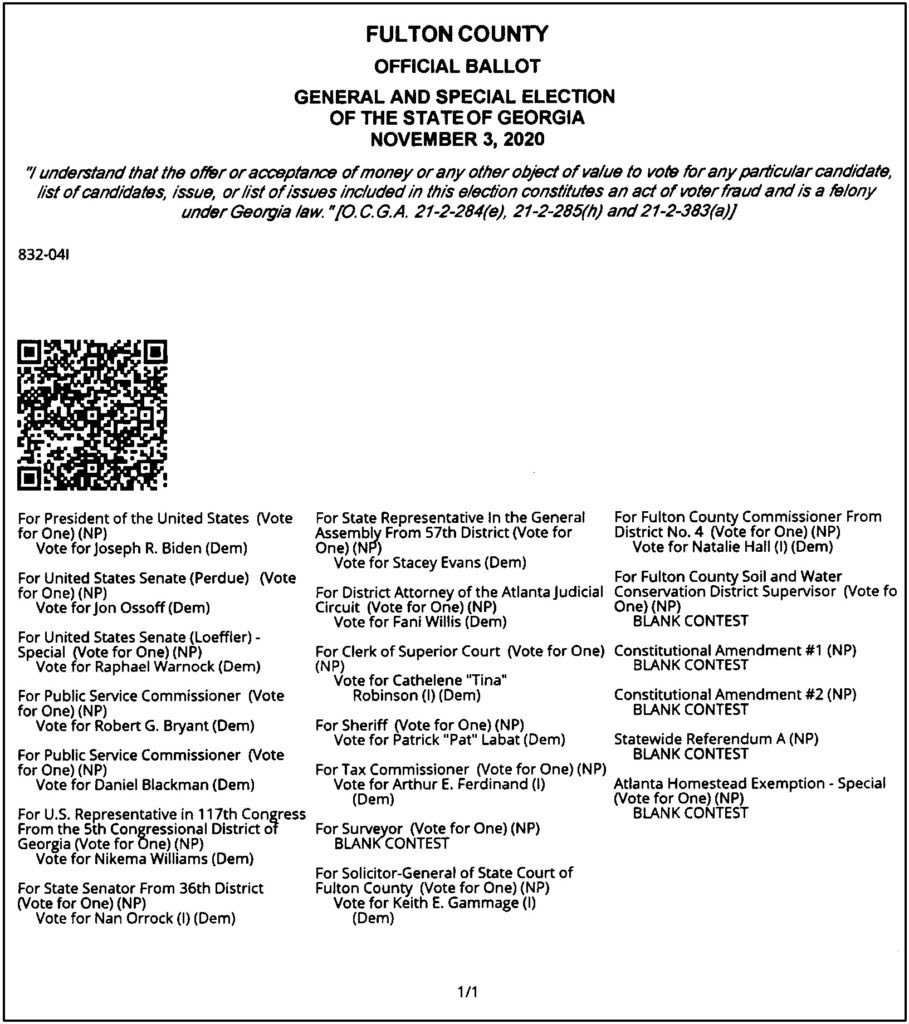
"Attackers can alter the QR codes on printed ballots to modify voters’ selections."
@imyourmoderator - Chris Paul
"The software update that Georgia installed in October 2020 left Georgia’s BMDs in a state where anyone can install malware with only brief physical access to the machines. I show that this problem can potentially be exploited in the polling place even by non-technical voters."
@imyourmoderator - Chris Paul
"Without needing any secret information, I created a counterfeit technician card that can unlock any ICX in Georgia."
@imyourmoderator - Chris Paul
Everyone who has paid attention to the election fraud issue knows that these machines are wide-open to manipulation through obvious vulnerabilities and that they cannot produce reliable results. Dominion's own discovery documentation in the Fox/Dominion lawsuit said it as well.
@imyourmoderator - Chris Paul
Lulz. Halderman worries that the people trying to secure our elections in Georgia will now know how to exploit the machines simply by having access to similar machines. That would mean anyone with access to similar machines could exploit them. It also means it's GOOD that people are proving it, because the machines cannot and do not produce reliable election results.
@imyourmoderator - Chris Paul
This alone is absolutely damning, and we've been making this argument for 2.5 years. "Despite the addition of a paper trail, ICX malware can still change individual votes and most election outcomes without detection. Election results are determined from ballot QR codes, which malware can modify, yet voters cannot check that the QR codes match their intent, nor does the state compare them to the human-readable ballot text." That should be horrifying, but we're told the presence of "risk-limiting audits" (basically, fake audits) would detect exploitation.
@imyourmoderator - Chris Paul
Your elections are not secure. They haven't been in a very long time, if ever. (p6-7) "Although outcome-changing fraud conducted in this manner could be detected by a risk-limiting audit, Georgia requires a risk-limiting audit of only one contest every two years, so the vast majority of elections and contests have no such assurance. And even the most robust risk-limiting audit can only assess an election outcome; it cannot evaluate whether individual votes counted as intended."
@imyourmoderator - Chris Paul
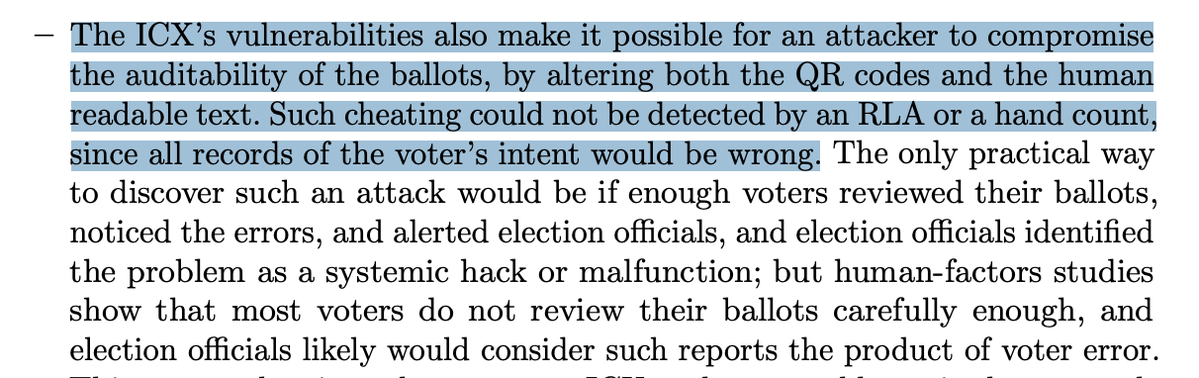
Every sentence of this report should provoke only one reaction: The machines must be completely eliminated, immediately. Everyone in office knows this is how our elections are run. Every single one. "The ICX’s vulnerabilities also make it possible for an attacker to compromise the auditability of the ballots, by altering both the QR codes and the human readable text. Such cheating could not be detected by an RLA or a hand count, since all records of the voter’s intent would be wrong."
@imyourmoderator - Chris Paul
"This means that in a close contest, ICX malware could manipulate enough ballots to change the election outcome with low probability of detection. In contrast, risk-limiting audits of hand-marked paper ballots, when used with appropriate procedural precautions, provide high confidence that individual votes are counted as intended and election outcomes are correct even if the election technology is fully compromised.
@imyourmoderator - Chris Paul
"Using vulnerable ICX BMDs for all in-person voters, as Georgia does, greatly magnifies the security risks compared to jurisdictions that use hand-marked paper ballots"
@imyourmoderator - Chris Paul
Every word of this is absolutely damning. "Likewise, previous security testing efforts as part of federal and state certification processes appear not to have uncovered the critical problems I found. This suggests that either the ICX’s vulnerabilities run deep or that earlier testing was superficial." How could all of that Dominion testing and state-mandated testing by state-certified techs not uncover the problems? It's like they want the machines to be vulnerable! Oh, wait... 🤔
@imyourmoderator - Chris Paul
Can't we PLEASE just stop pretending? "My technical findings leave Georgia voters with greatly diminished grounds to be confident that the votes they cast on the ICX BMD are secured, that their votes will be counted correctly, or that any future elections conducted using…
@imyourmoderator - Chris Paul
@threadreaderapp unroll

@jeffmfulgham - Jeff Fulgham
Breaking: 2020 Election Machines Report A Federal court finally unsealed a 2021 report that found Georgia voting machines had/have "critical vulnerabilities that can be exploited to subvert all its security mechanisms..." The report has been conveniently sealed since 2021!
@jeffmfulgham - Jeff Fulgham
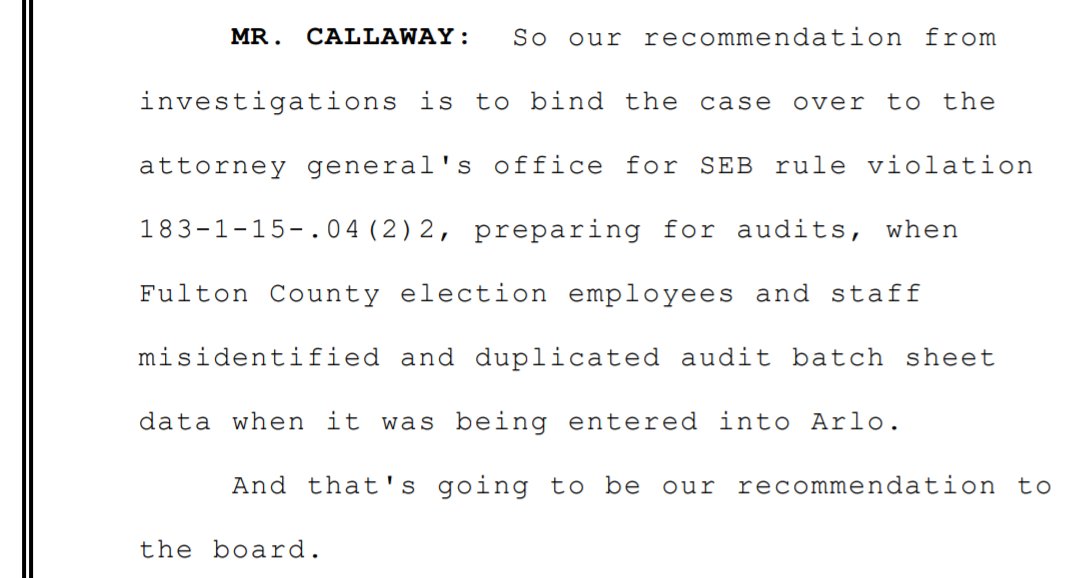
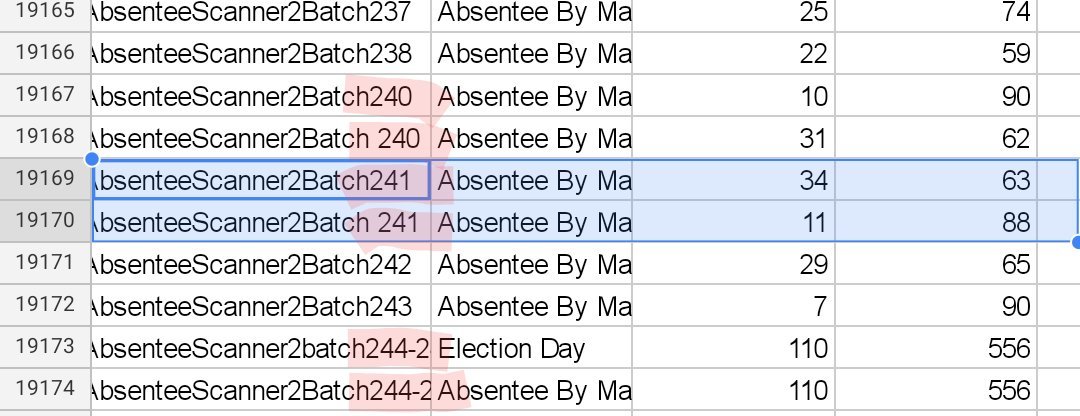
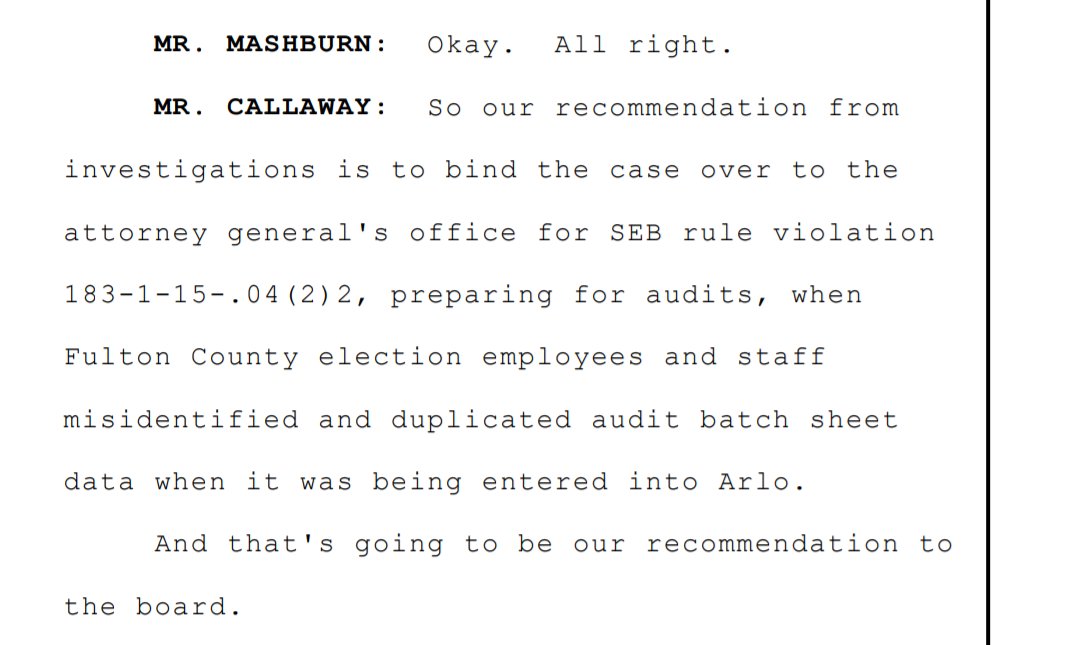
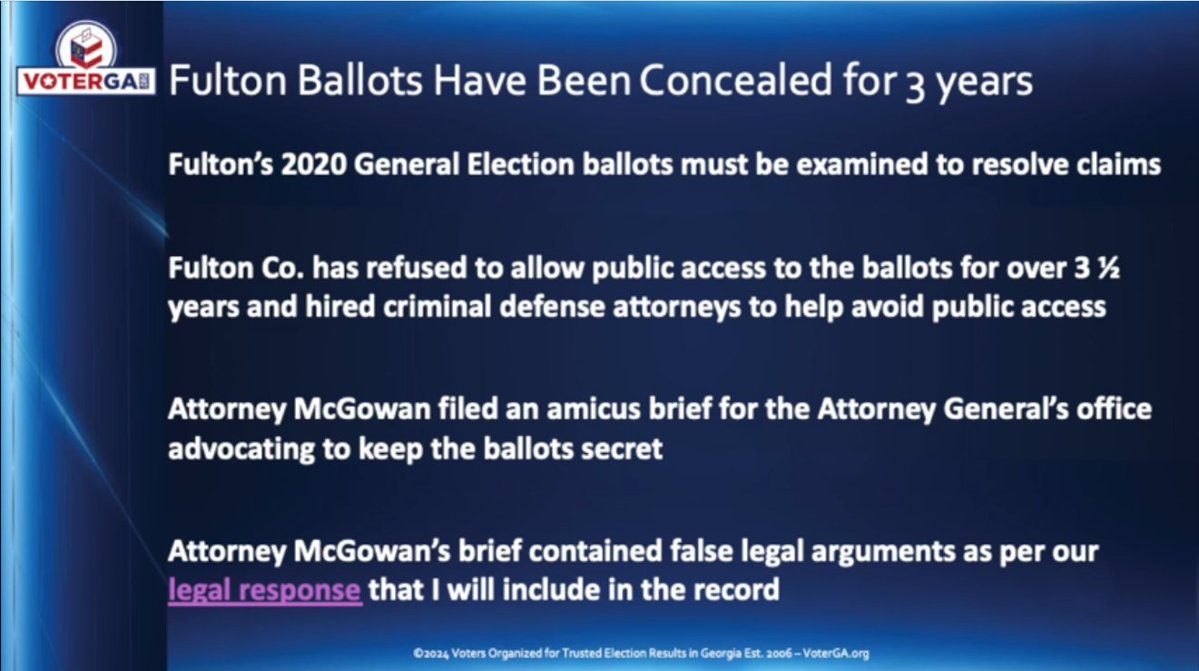
Keep in mind that 14 months after the election GASOS Brad Raffensperger finally admitted that "several thousand" ballots had been counted twice in Fulton Co. https://www.washingtonpost.com/politics/2023/06/15/court-unseals-long-awaited-election-security-reports/

@jeffmfulgham - Jeff Fulgham
At 1 hr 9 min Raffensperger admits several thousand ballots were counted twice in Fulton Co. https://fyntv.com/2022/02/22/r-brad-raffensperger-ga-secretary-of-state-joins-bkp-politics/


@CatTheGreat_ - CatTheGreat
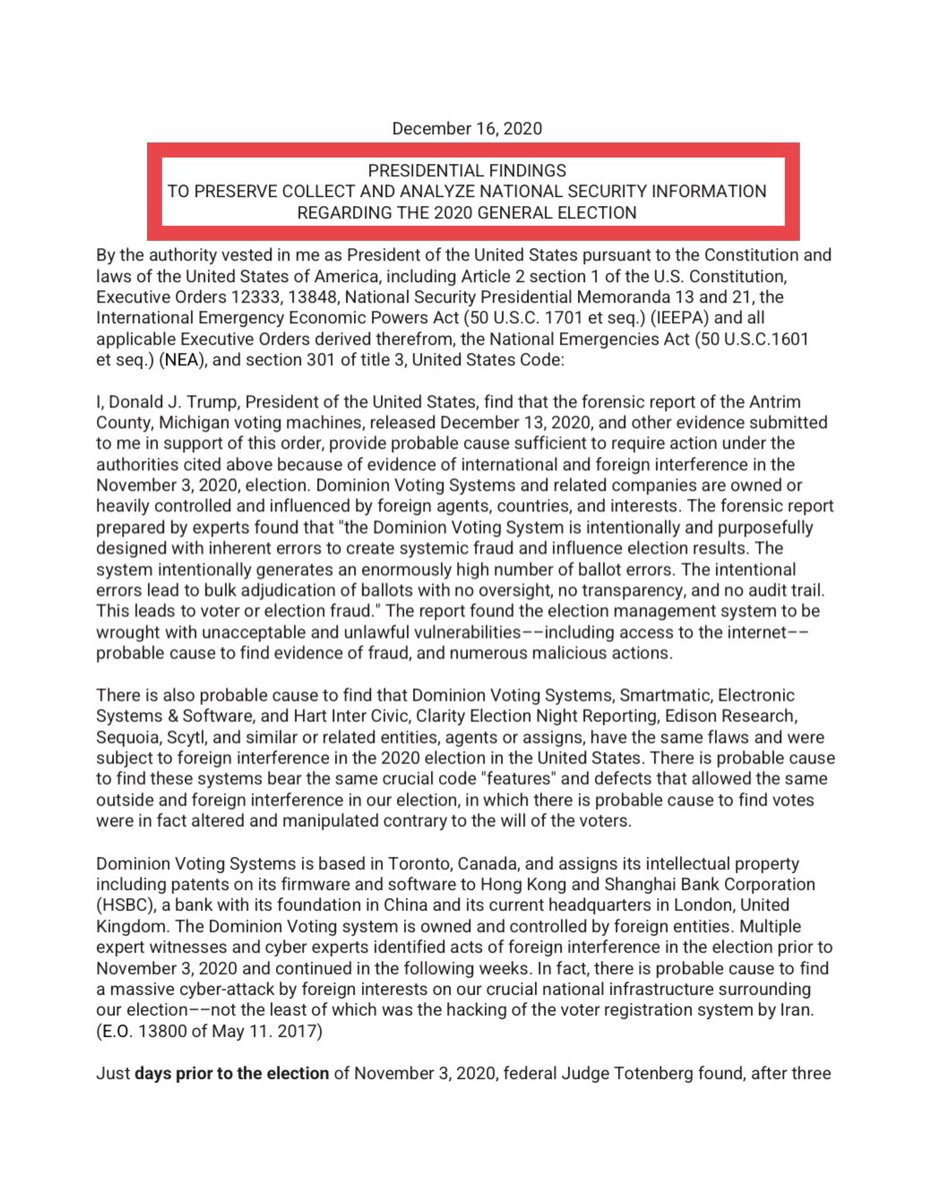
Trump’s famous claim “we caught the swamp, we caught them all!” after the 2020 election… Did that really happen? Is there any EVIDENCE we might really “have the goods”?!? It’s all coming back up NOW because of the DOJ’s case against Trump for January 6th… but interestingly enough, a document unearthed by the J6 “Un-Select Committee” may just be a CLUE into how Trump could’ve done it… 🧵
@CatTheGreat_ - CatTheGreat
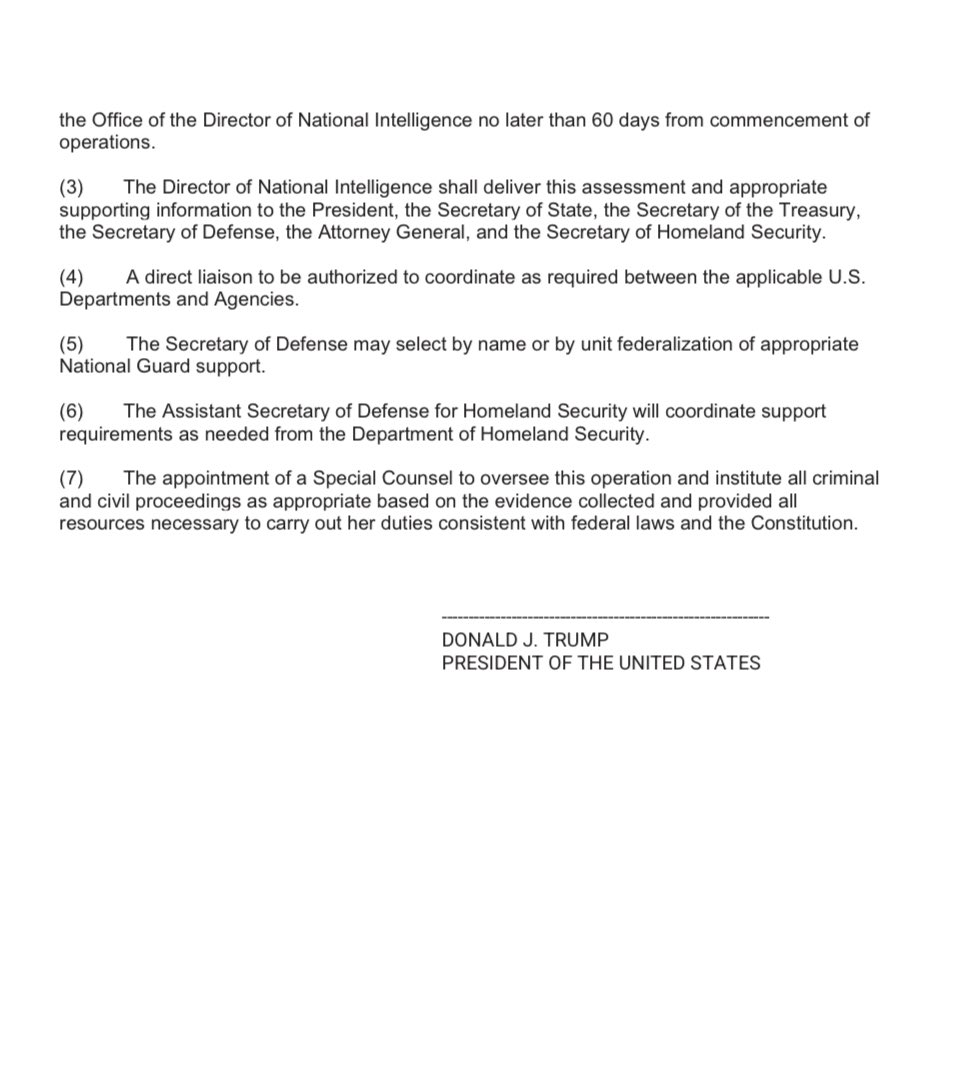
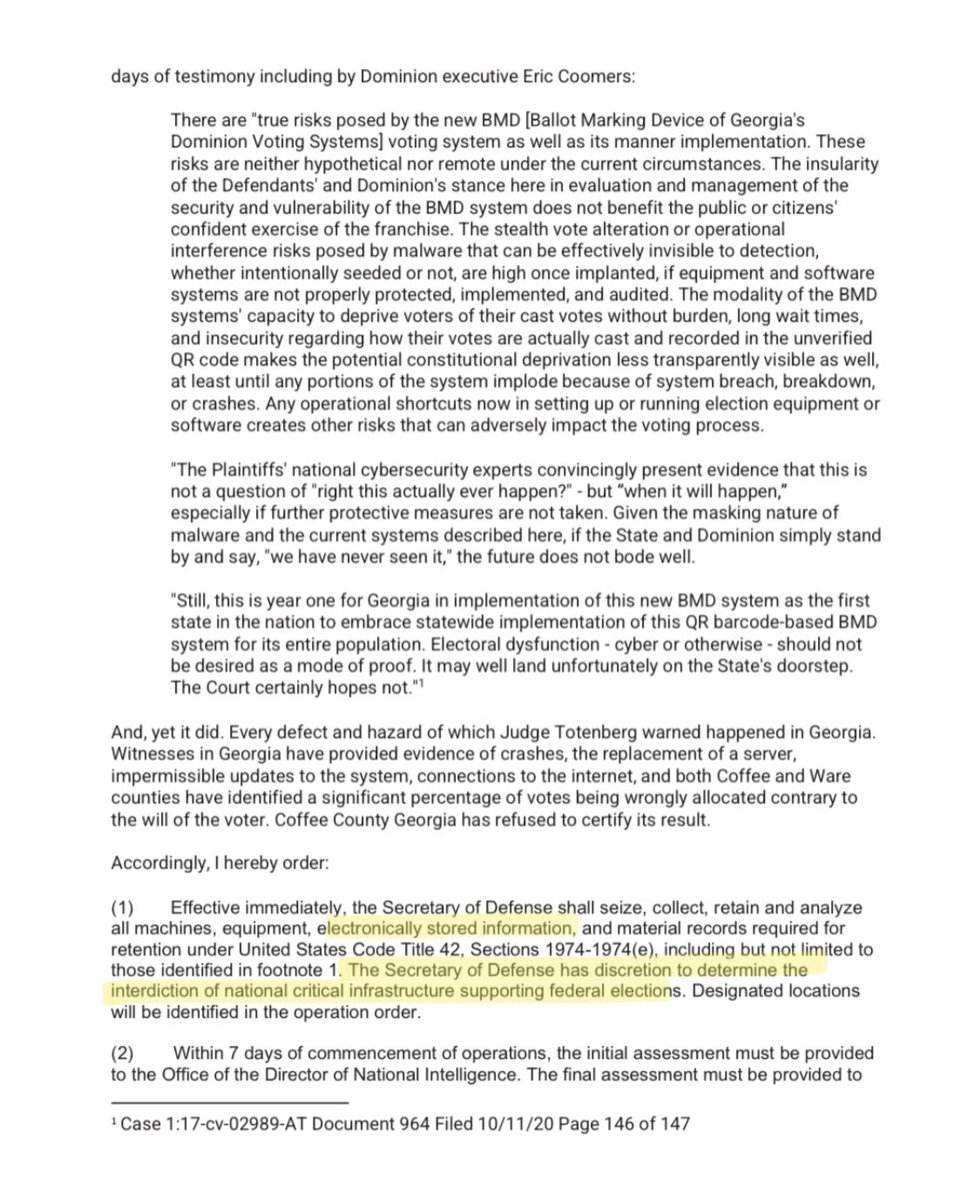
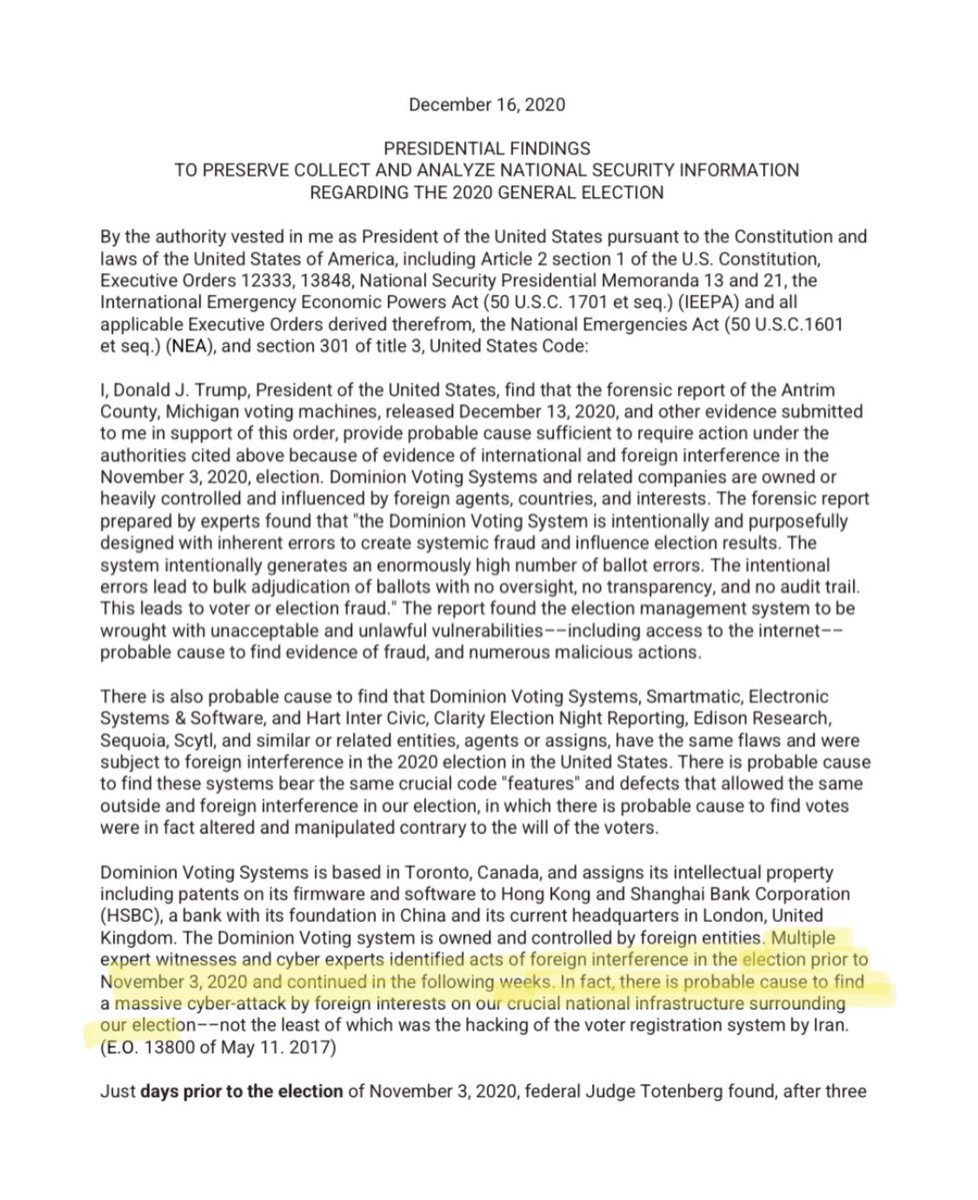
Remember that “draft Executive Order” to seize voting machines that the J6 Committee thought was a huge “gotcha moment”? If you look closely, it was curiously NOT titled an EO, but “Presidential Findings” This matters! https://t.co/SxYbnevMYW
@CatTheGreat_ - CatTheGreat
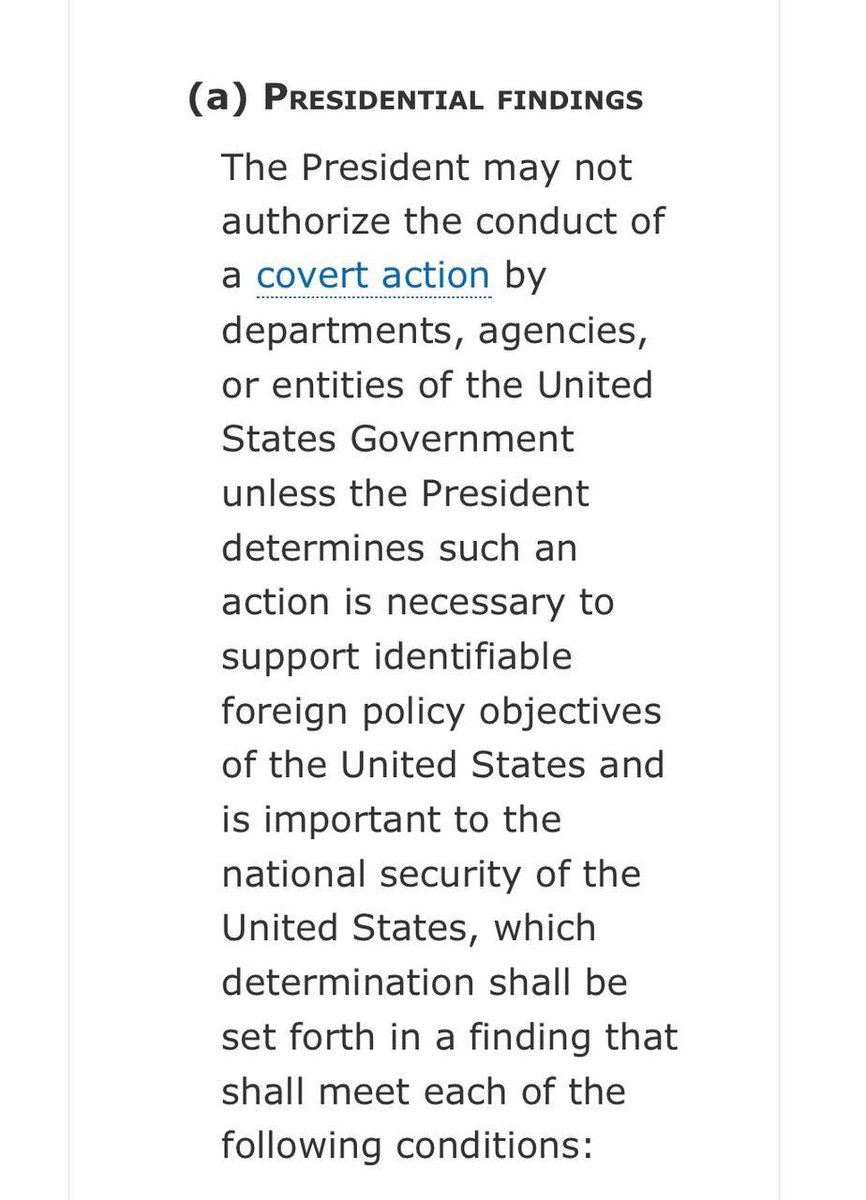
“Presidential Findings” deal with the President being able to authorize covert action in the name of national security. According to 50 US Code 3093: “The President may not authorize the conduct of a covert action by departments, agencies, or entities of the United States Government unless the President determines such an action is necessary to support identifiable foreign policy objectives of the United States and is important to the national security of the United States…” Foreign (or domestic?) interference in the election = national security, obviously.
@CatTheGreat_ - CatTheGreat
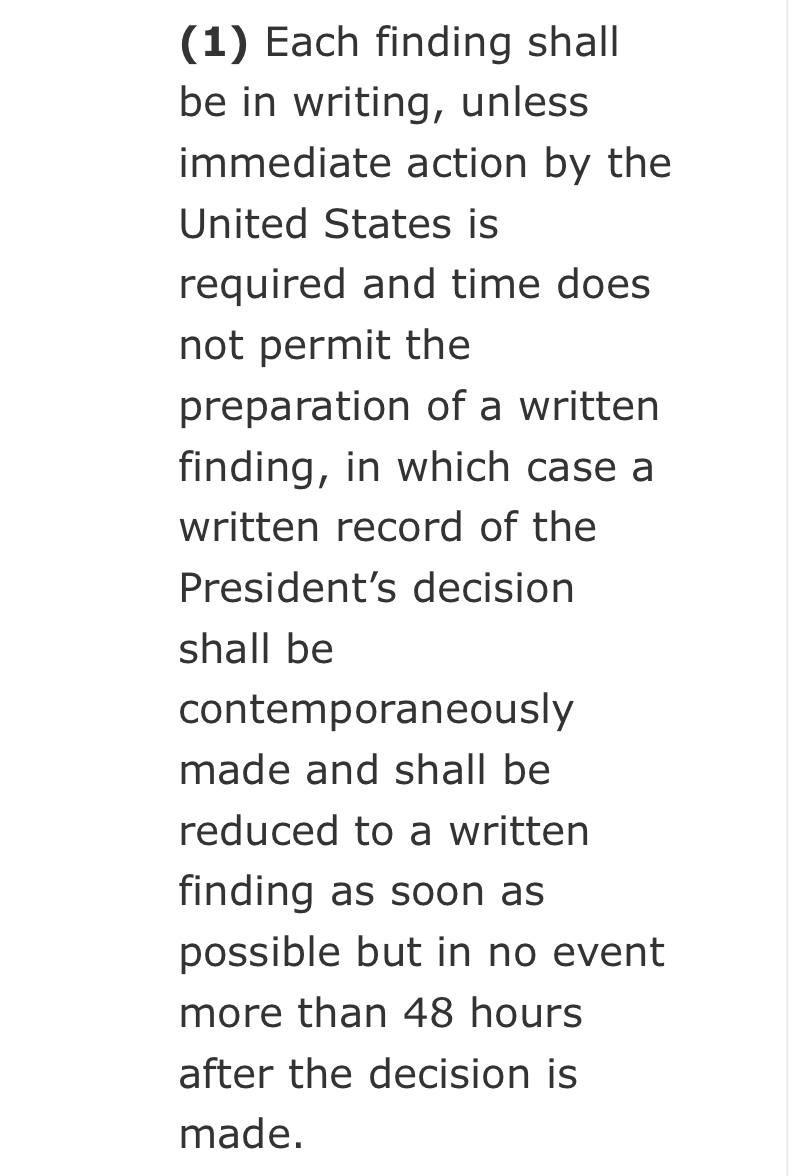
Presidential Findings must be in writing “unless immediate action by the United States is required and time does not permit the preparation of a written finding, in which case a written record of the President’s decision shall be contemporaneously made and shall be reduced to a written finding as soon as possible but in no event more than 48 hours after the decision is made.” Presidential Findings authorize COVERT action, and can be created AFTER a time-sensitive operation has commenced. So technically, these Presidential Findings could’ve been created AFTER a clandestine operation involving the collection/seizure of “machines, equipment, ELECTRONICALLY STORED INFORMATION , and material records”
@CatTheGreat_ - CatTheGreat
The Findings claim witnesses and cyber experts found foreign interference in the election BEFORE, DURING & AFTER it happened. “Multiple expert witnesses and cyber experts identified acts of foreign interference in the election prior to November 3, 2020 and continued in the following weeks. In fact, there is probable cause to find a massive cyber-attack by foreign interests on our crucial national infrastructure surrounding the election” (Hello! Solarwinds!)
@CatTheGreat_ - CatTheGreat
Obviously the voting machines and physical records were not seized, but could the Findings have justified PART of the actions that actually took place? Space Force’s defense and collection of data from the “hackable” voting machines AFTER IT WAS ALREADY DONE? End 🧵

@BehizyTweets - George
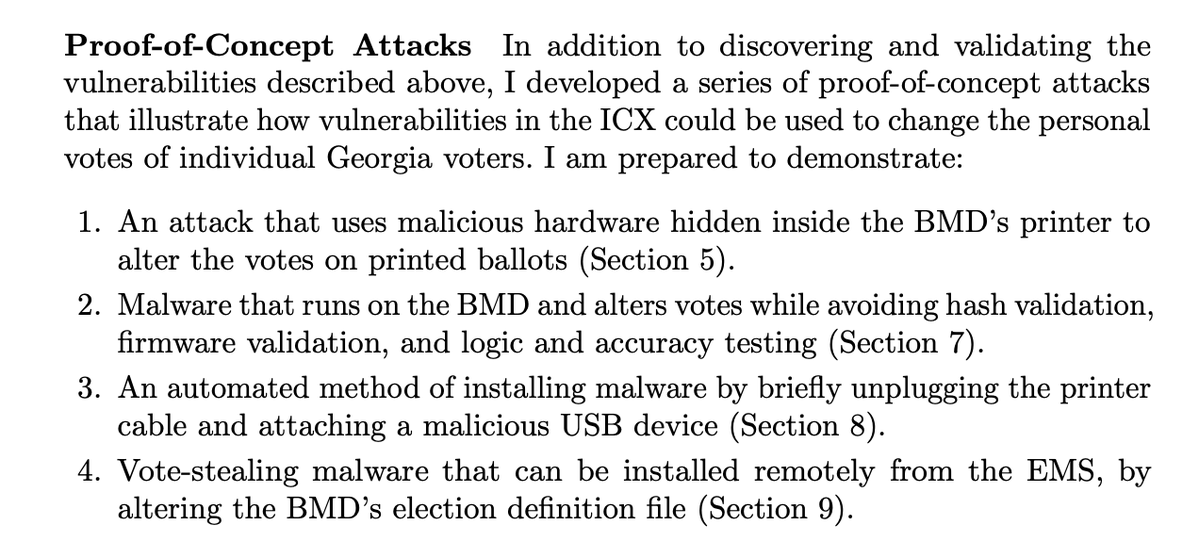
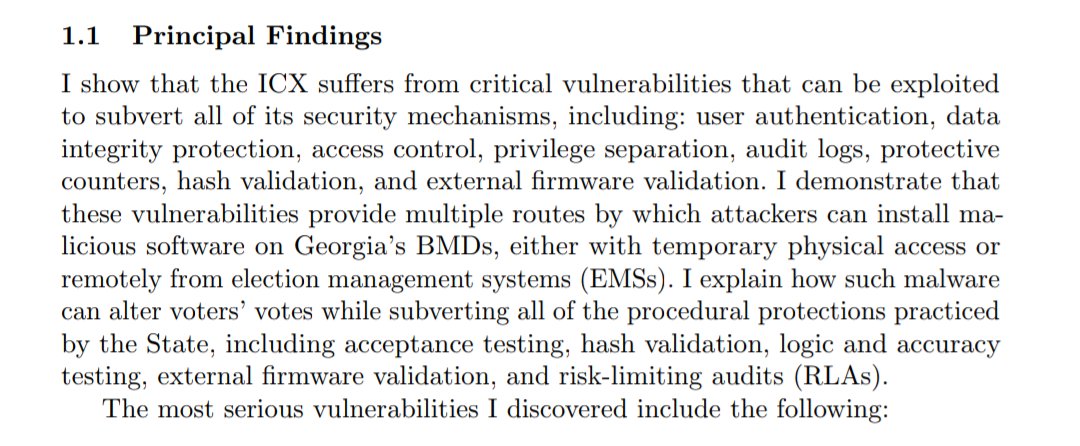
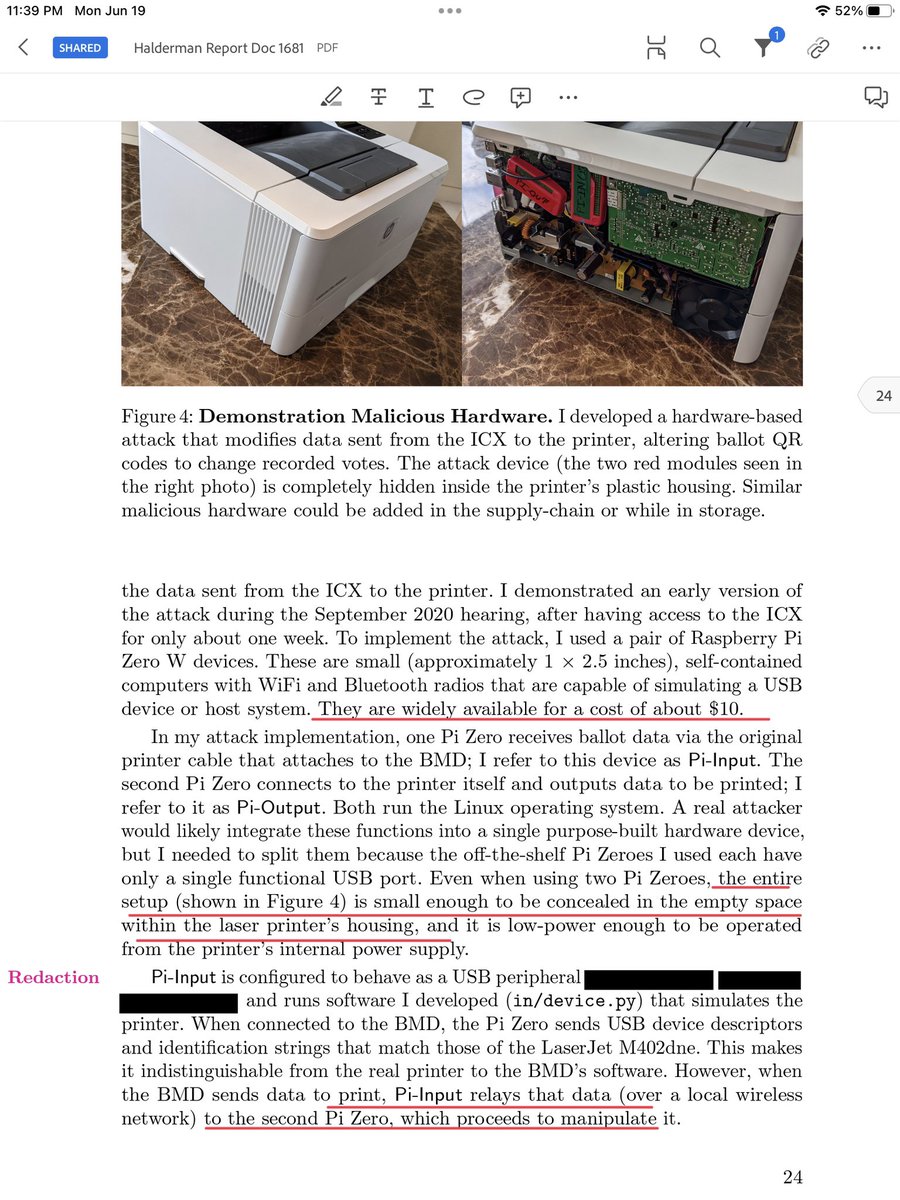
BREAKING: Voting machine expert Professor Alex Halderman from the University of Michigan did a thorough analysis of Dominion voting machines used in Georgia for the 2020 election and what he found was SHOCKING "Attackers can alter the QR codes on printed ballots to modify voters' selections." (Section 7) "Attackers can forge or manipulate the smart cards that the ICX uses the authenticate technicians, poll workers, and voters." (Section 6) "I show that the ICX suffers from critical vulnerabilities that can be exploited to subvert all of its security mechanisms" ".... these vulnerabilities provide multiple routes by which attackers can install malicious software on Georgia's BMDs (Ballot marking devices), either with temporary physical access or remotely from election management systems (EMSs)." "... such malware can alter voters' votes while subverting all of the procedural protections practiced by the State, including acceptance testing, hash validation, logic & accuracy testing, external firmware validation, and risk-limiting audits"
@BehizyTweets - George
"The software update that Georgia installed in October 2020 left Georgia's BMDs in a state where anyone can install malware with only brief physical access to the machines." "I show that this problem the polling place even by NON-technical voters." (Section 8) "I demonstrate that attackers can execute arbitrary code with root (supervisory) privileges by altering the election definition file that county workers copy to every BMD before each election." "Attackers could exploit this to spread malware to all BMDs across a county or the entire state." (Section 9) "In addition to discovering and validating the vulnerabilities described above, I developed a series of proof-of-concept attacks that illustrate how vulnerabilities in the ICX could be used to change the personal votes of individual Georgia voters." "It is very like that there are other, equally critical flaws in the ICX that are yet to be discovered. Fully defending it will require discovering and mitigating them all, but attackers would only have to find ONE."
@BehizyTweets - George
There's so much evidence that the 2020 election was rigged that we could fill the whole grand canyon

@TheNickyMo - nick moseder
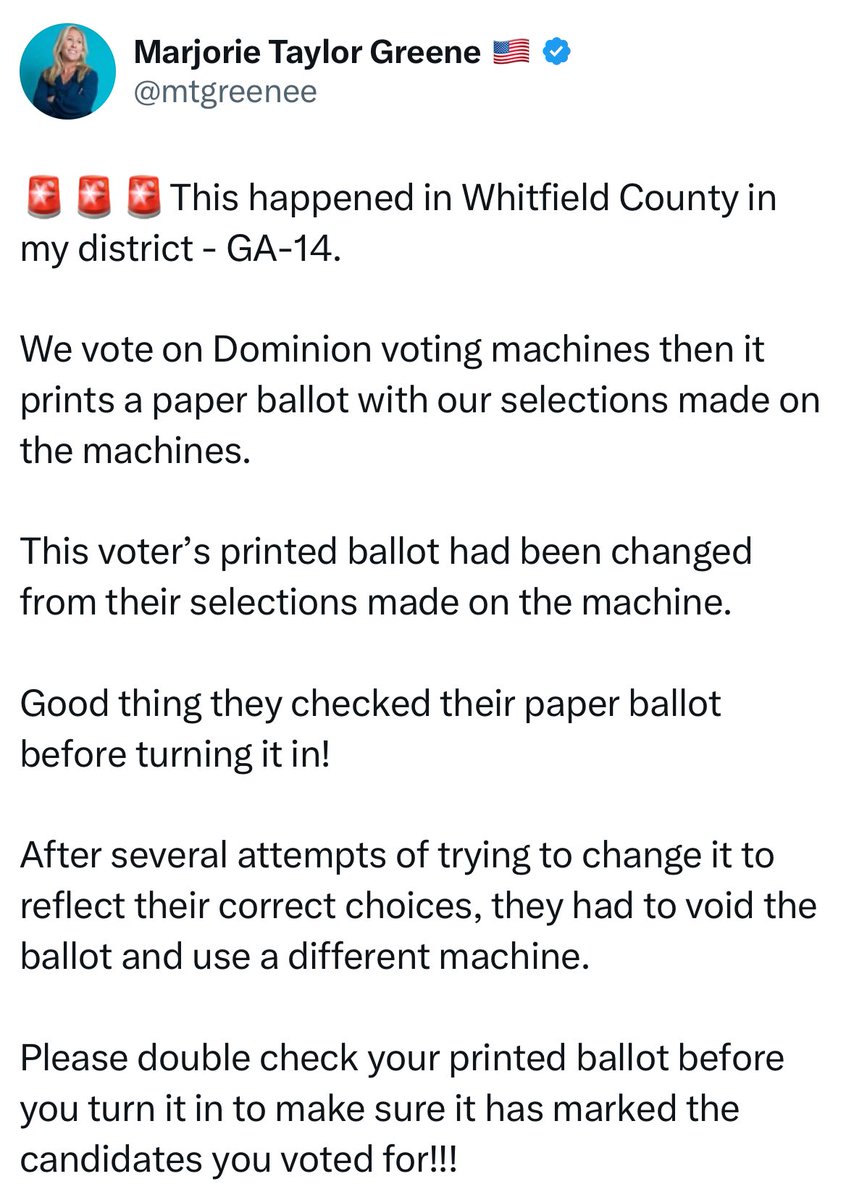
🧵THREAD: Donald Trump and several co-defendants have been indicted for inspecting the voting systems in Coffee County Georgia… Want to know what REALLY happened in Georgia?!
@TheNickyMo - nick moseder
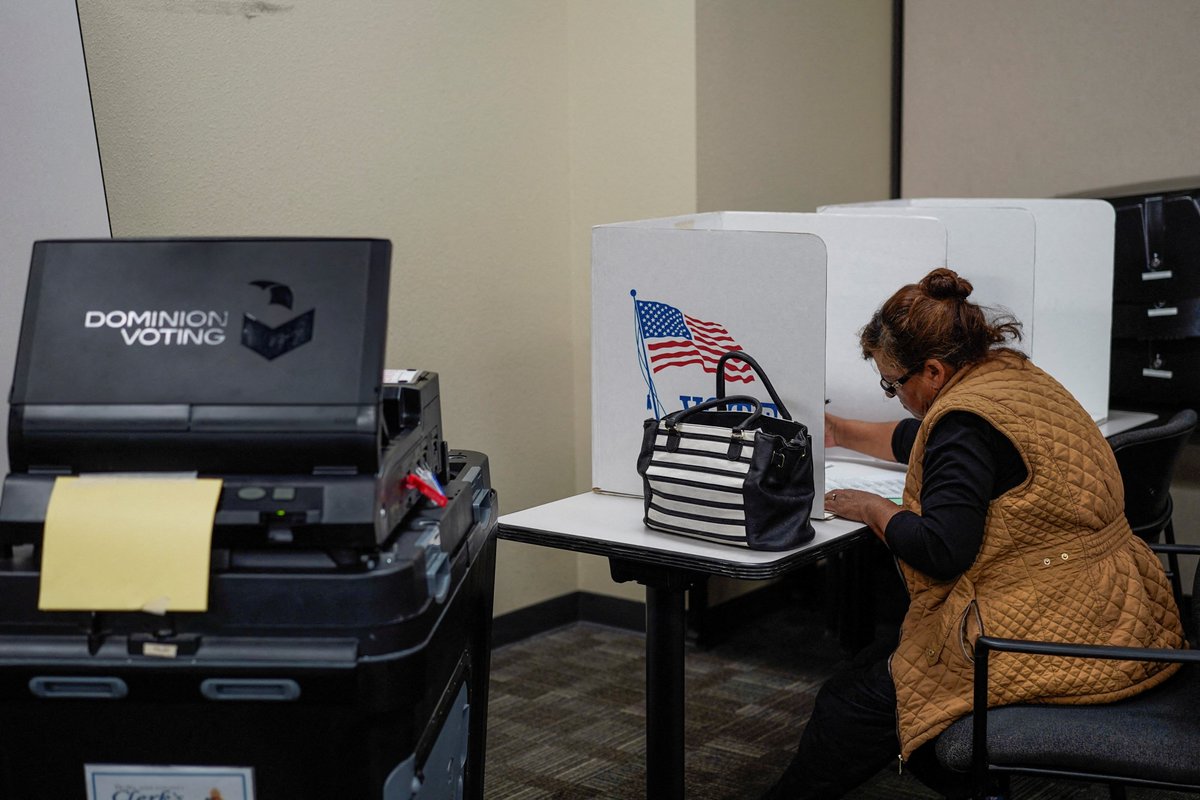
Let’s read some snippets from Cathy A Latham’s SWORN affidavit. These allegations were submitted under penalty of perjury! 👇 Latham was present as a GOP observer during early voting along with Misty Hampton (who later allowed Trump's legal team to come inspect the scanner). https://t.co/H8CRUajIDx
@TheNickyMo - nick moseder
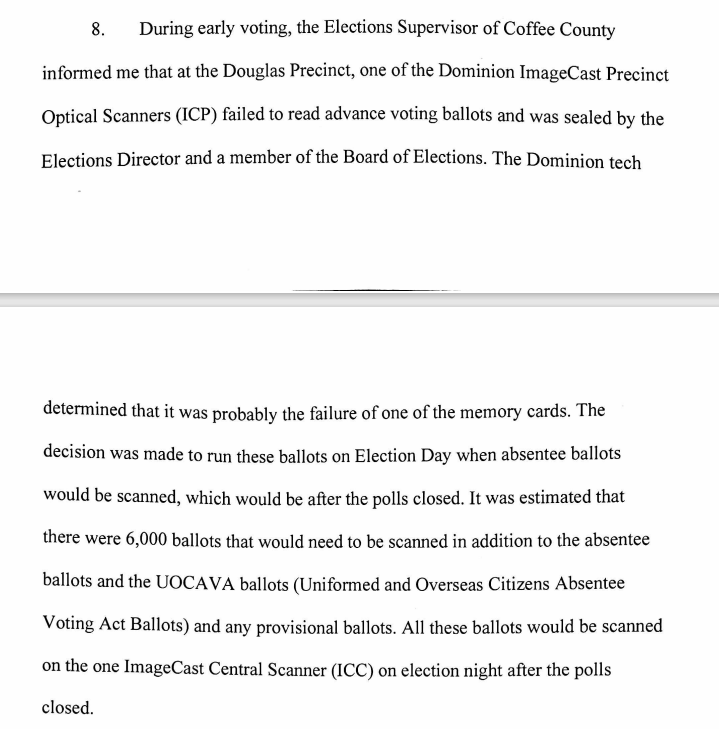
During early voting, Elections supervisor of Coffee County informed Latham that one of the scanners at the Douglas precinct was rejecting 6,000 ballots. They decided to process these absentee ballots at the central count on election day, along with the overseas ballots. https://t.co/9fdcQMMkME
@TheNickyMo - nick moseder
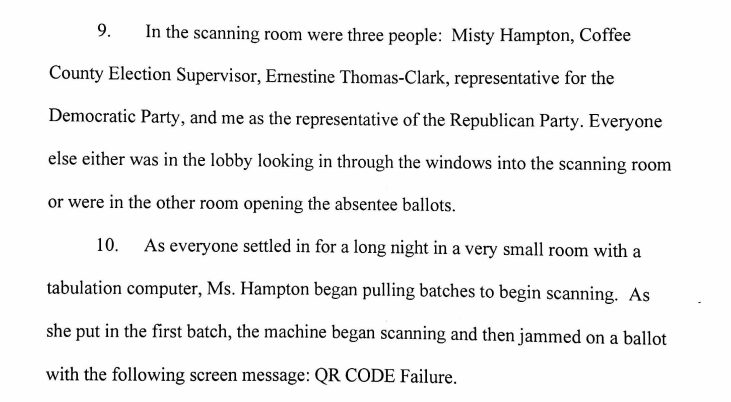
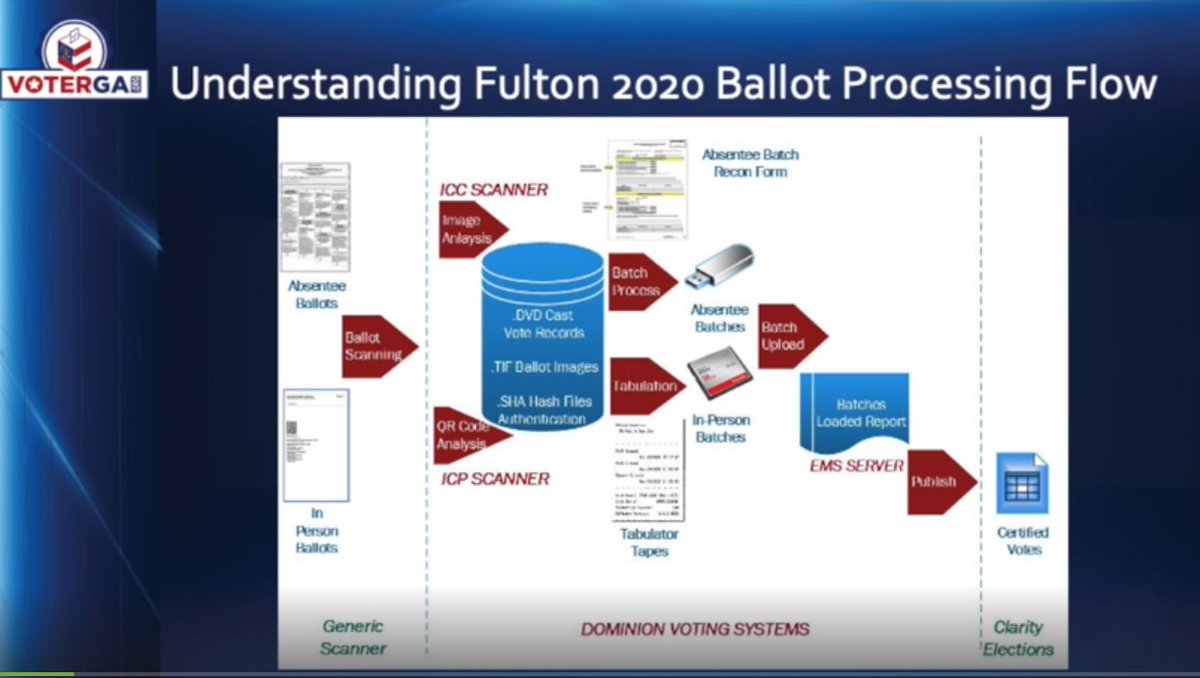
At the central count scanning room, 3 people were present. 1) Misty Hampton (Coffee Election Supervisor) 2) Ernestine Thomas-Clark (Democrat observer) 3) Latham (Republican observer). Upon scanning, the scanner gave a QR CODE failure message. https://t.co/y5JeAKAI8T
@TheNickyMo - nick moseder
Dominion tech Samuel Challandes from Colorado was sent in and suggested that they wipe down the scanner with a cloth and blow compressed air on the optical lens, which they did several times to no avail. https://t.co/sE8J55YGEa
@TheNickyMo - nick moseder
WOAH! At this point they noticed an interesting "coincidence". ALL (meaning every single one) of the 5,800 ballots that was giving a QR CODE FAILURE, were for the three Republican candidates: Kelly Loeffler, David Perdue, and Bubba McDonald! Gosh, that seems odd! https://t.co/oN2x1lYx0H
@TheNickyMo - nick moseder
Mr Chaney (board chairman) gets angry and demands for the Dominion tech to call his boss and fix this! Chaney starts threatening to bring in news agencies and expose the failure of dominion's ICP scanner. Challandes calls his boss Scott Tucker on speaker first, then steps out of the room alone...
@TheNickyMo - nick moseder
Challandes comes back and stands next to the scanner, smiling ear to ear, and tells them to wipe down the machine one more time, ensuring them that THIS TIME it's going to work. https://t.co/vR40TCUnD7
@TheNickyMo - nick moseder
They perform the same wipe down that they had tried countless times already, and what do you know? THIS TIME, it worked. Chaney, Hampton, Latham, and Thomas-Clark are all left dumbfounded, and suspicious that Challandes and/or his boss Tucker remotely altered the machine. https://t.co/YJ9dfKFsne
@TheNickyMo - nick moseder
So, to anyone who says that these election workers were working on behalf of Trump to alter the outcome of the Coffee County election, think again. They gave access to an independent research team to figure out what the hell happened that night. (Please share this thread)

@DC_Draino - DC_Draino
Did Gov Kemp really just say “if you give anyone a voting machine, they can hack it”?! Yep! He openly admits GA elections are filled w/fraud Yet he’ll never say “we need to get rid of machines & move to hand-counting” B/c he benefits from the fraud

@KanekoaTheGreat - KanekoaTheGreat
Rep. Jerry Nadler (D-NY) in 2004: "If someone were deliberately hacking these machines, you could steal millions of votes, and no one would know it... We've documented a machine in this county that recorded 11,000 extra votes for Bush. In that county, there was counting Kerry votes for Bush... These machines are hackable. A dishonest employee of the vendor, or a dishonest employee of a local board of elections, or simply someone who knows electronics, and has a computer at home, could hack into these machines and put in secret instructions to disregard every 20th Democratic vote. Or add 10% to the Kerry or Bush vote or whatever, and you might not even know it... There was one county where on some local race or some referendum, they lost 4500 votes, the machine hiccuped, and 4500 people didn't have the votes counted... We have all these professors and these computer experts telling us that the encryption algorithms aren't sufficient. That the protections aren't sufficient. They are proprietary data, so they're kept secret, so we don't really know." Full thread below. 🧵👇
@KanekoaTheGreat - KanekoaTheGreat
MUST WATCH🚨 20 minutes of prominent Democrats, computer scientists, and election security experts warning that America's election system is online, easily hackable, and often running on Windows 7 or older operating systems. https://t.co/upFIU1g8SN

@pepesgrandma - Bad Kitty Unleashed 🦁💪🏻
How could anyone allow all of this to happen in their state without remedy. And to have such a lackadaisical attitude on protecting the registration information of every resident in Georgia? Did you see one of those emails from the Oct 23, 2020 hacking? “Typically our clients prefer to give us sensitive information like this via phone, this limits the exposure of the information and ensures it is NOT DISCOVERABLE.” Brad Raffensperger is the one who should be on trial. Thred

@matttttt187 - {Matt} $XRPatriot
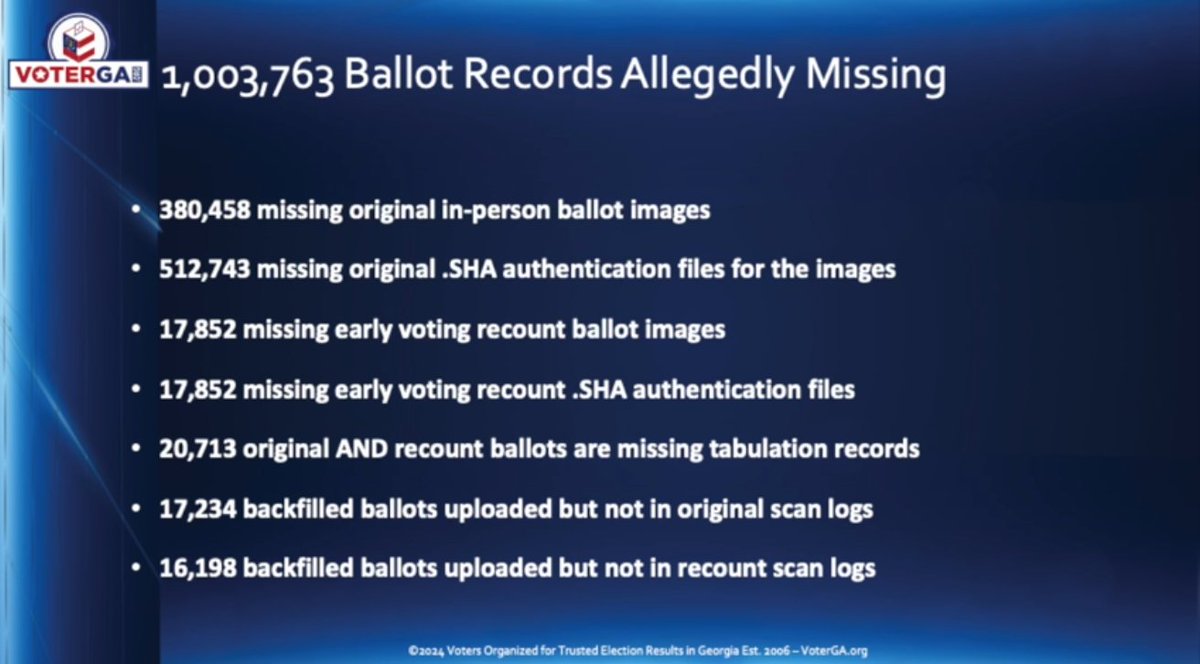
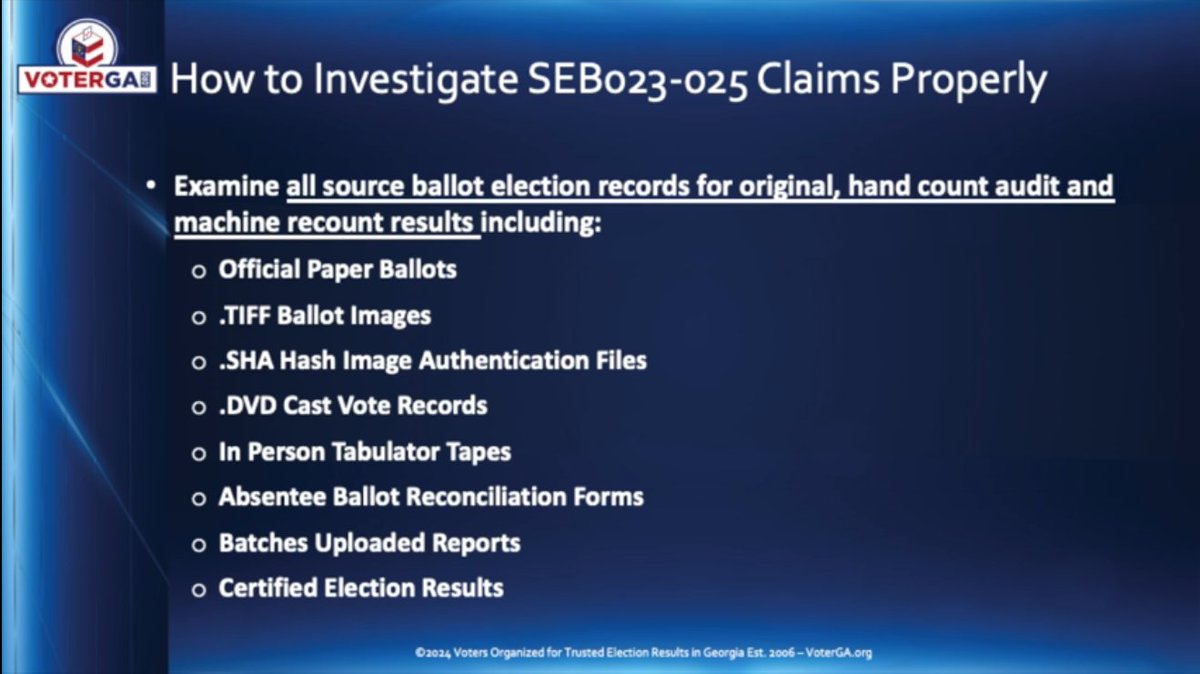
𝐔𝐏𝐃𝐀𝐓𝐄𝐃 𝟗/𝟏𝟖 {1/3} 𝐋𝐄𝐓’𝐒 𝐋𝐎𝐎𝐊 𝐀𝐓 𝐀𝐋𝐋 𝐎𝐅 𝐓𝐇𝐄 𝐄𝐋𝐄𝐂𝐓𝐈𝐎𝐍 𝐅𝐑𝐀𝐔𝐃 𝐀𝐍𝐃 𝐈𝐍𝐓𝐄𝐑𝐅𝐄𝐑𝐄𝐍𝐂𝐄 𝐍𝐄𝐖𝐒 𝐓𝐇𝐀𝐓 𝐃𝐑𝐎𝐏𝐏𝐄𝐃 𝐈𝐍 𝐉𝐔𝐒𝐓 𝐓𝐇𝐄 𝐏𝐀𝐒𝐓 𝟏𝟏 𝐃𝐀𝐘𝐒 𝐎𝐑 𝐒𝐎 𝐒𝐇𝐀𝐋𝐋 𝐖𝐄? 𝐓𝐇𝐄 𝐃𝐀𝐌 𝐈𝐒 𝐀𝐁𝐎𝐔𝐓 𝐓𝐎 𝐁𝐑𝐄𝐀𝐊 9/18- An election integrity group claims 10.9 million out of a total of 22.1 million ballots that had been mailed out to registered voters in California during the 2022 midterm elections went ‘unaccounted for.’" 9/18- As many as 34,000 absentee ballots cast in several Detroit, MI, precincts illegally had no signed ballot application, according to a report by The Spekin Forensic Laboratories. 9/18- Wayne County, Michigan, never lawfully certified their 2020 presidential election results, potentially making Donald Trump the winner 9/18- An election integrity research group reported that the required chain of custody documentation is missing for 740,000 Maricopa County, Arizona, ballots from the 2020 election 9/18- A voting machine expert says Fulton County, Georgia, conducted no signature verification in the 2020 election, and election officials admitted 9/17- Kari Lake’s newly filed appeal says evidence demonstrates that Maricopa did not test but falsely certified that its 446 vote-center tabulators passed mandatory L&A certification testing prior to Election Day and strongly suggests Maricopa planned the Election Day debacle 9/16- Kari Lake’s newly filed appeal suggests that new evidence shows Maricopa County did not comprehensively compare 275,000 voter signatures according to the county's and state’s own rules. 9/15- Electronic voting machine expert Garland Favorito has testified that about 100,000 improper chain of custody forms were picked up after the election was conducted, or pickups were marked 3 minutes apart when the locations were 30 minutes apart in Georgia in 2020 9/15- Approximately 43,000 DeKalb County, Georgia, drop box ballots have no chain of custody forms to authenticate them. 9/15- An electronic voting machine expert testified that his team found as many as 148k ballots tampered with in the 2020 Fulton County, Georgia, election alone; his team didn't look at other counties. 9/14- Electronic voting machine expert Garland Favorito testified that nearly 35,000 people who voted in the Georgia 2020 election had moved out of their registered county prior to the election, which exceeds the 11,779-vote victory margin and is thus sufficient to place the results of the presidential election in Georgia in question. 9/14- Evidence shows the Maricopa County Election Day printer "failures" were caused by malware or by remote access; 200,000 ballots were ejected out of 248,000 votes cast. 9/14- Election machine expert Garland Favorito testified that he found 106,000 2020 Georgia ballots had massive problems with the chain of custody, like the times and places didn't make sense or were contradictory, and in some instances the documentation was just flat out missing. 9/14- Evidence shows the Maricopa County Election Day printer "failures" were caused by malware or by remote access; 200,000 ballots were ejected out of 248,000 votes cast 9/13- Electronic voting machine expert Garland Favorito says a hand count audit of Ware County, Georgia’s 2020 presidential election, found about a .25% misrecorded vote rate, almost exactly the victory margin rate that Joe Biden received over Donald Trump 9/13- A comprehensive report compiled by Look Ahead America provides specific, verifiable evidence that illegal ballots in Georgia likely exceeded the margin of victory in the 2020 presidential race. 9/13- Electronic voting machines expert Garland Favorito says he found counties in Georgia had destroyed 1.7 million ballot images in violation of the law, and the surveillance video of drop boxes for 181,000 ballots was deleted in violation of the law.

@matttttt187 - {Matt} $XRPatriot
🚨 𝐔𝐏𝐃𝐀𝐓𝐄𝐃 𝟗/𝟐𝟖 🚨 LET’S LOOK AT ALL OF THE ELECTION FRAUD AND INTERFERENCE NEWS THAT’S DROPPED IN SEPTEMBER SHALL WE?? DO YOU THINK ITS JUST COINCIDENCE THAT THIS IS ALL BEING DRIPPED OUT AND REPORTED…RIGHT NOW? 💥 9/28- Georgia Secretary of State Brad Raffensperger allegedly sent a threatening letter to counties, telling them not to allow forensic exams on the Dominion voting machines 💥 9/28- During the 2020 Arizona election, 204,430 mail-in ballots had mismatched signatures that were never sent to review, and 740,000 mail-in ballots had a broken chain of custody, all far more necessary than the 10,457 votes needed for a Trump win. 💥 9/27- A former police officer and a poll watcher says he witnessed a pile of ballots pulled out of a box that were 171 to 1 for Biden in Cobb County, Georgia, and then noticed someone had illegally sorted through the boxes. 💥 9/27- A certified Fulton County Georgia audit monitor claims to have observed many boxes of 2020 ballots that appeared to be perfectly filled out as though they were preprinted and did not look done by hand, of which 98% were filled out for Biden and 2% for Trump. She and other observers have a list of suspicious batches. 💥 9/26- Georgia Secretary of State Brad Raffensperger certified the 2020 election before investigating the 364,000 ineligible voter records based on residency alone, of which 67,000 voted. 💥 9/25- Montana is the 25th state to ban or restrict the use of private money (Meta CEO Mark Zuckerberg) in the conduct of elections, preventing millions of dollars from being poured into local election offices in battleground states and expanding unsupervised election protocols like mail-in voting and the use of ballot drop boxes. 💥 9/25- The voting machine company that sued Mike Lindell, Rudy Giuliani, Fox News, and Newsmax for defamation about the 2020 election has been implicated in a bribery scheme, according to a new indictment from the 💥 9/24- Texas AG Ken Paxton says they stopped counting ballots during the 2020 election because they needed to figure out how many real votes there were so they could figure out how many mail-in ballots to apply to the election. 💥 9/24- Texas AG Ken Paxton says he stopped 2.5 million illegal mail-in ballots that would have stolen the 2020 election from Trump in Texas. 💥 9/24- During the 2020 election in Green Bay, Wisconsin, a Mark Zuckerberg-paid election operator decided which ballots would be tallied and which ones would not. 💥 9/24- Arizona Senate has laid out RICO indictments against Katie Hobbs and others in violation of RICO ACT-13-2301, including bribery, racketeering, money laundering, drug trafficking, human trafficking, aiding and abetting the Sinaloa Cartel, and election fraud. 💥 9/24- Articles of impeachment have been filed against the Wisconsin Election Chief after many lawmakers say her policies and directives “rigged” the election in favor of Joe Biden in 2020. 💥9/24- Election integrity experts report 26 strange huge net vote dumps for Joe Biden, of 25,000 or more, appeared on election night in 2020 in 14 states suspected of election fraud, with some having more than one spike; Pennsylvania had four spikes (none in favor of Trump) 💥 9/23- 150 trained election workers' review of 25% of all 2020 mail-in ballots in Arizona shows they had no signature match, meaning 420,987 ballots out of 1.9 million were fraudulent, invalid, or illegitimate 💥9/23- 200,000 ‘non-conforming’ ballots were found in Maricopa County, Arizona’s 2020 election, after discovering ten additional ballot types being used when only one official ballot type was approved 💥 9/22- A former USPS employee blows the whistle on 100,000 missing Wisconsin ballots. 💥 9/22- Wisconsin Republicans introduced 15 articles of impeachment against Meagan Wolfe, the Administrator of the Wisconsin Elections Commission, citing allegations of maladministration in office and potential violations of election laws.
@matttttt187 - {Matt} $XRPatriot
💥 9/22- Absentee drop boxes have been banned by the Wisconsin Supreme Court. 💥9/21- A legal review conducted on the 92 court challenges filed over the 2020 election found that a clear majority of the cases decided on the merits were ruled favorably for the GOP and Trump. 💥9/21- Former Secretary of State Ruth Johnson says that over 800,000 ballot applications were sent to non-qualified voters in Michigan in 2020. 💥9/21- AG Ken Paxton says a Texas court’s ruling has blocked him from prosecuting voter fraud. 💥9/21- Texas AG Ken Paxton says Democrats stole the election from Trump in 2020 by stopping the count of votes on election night so they could figure out how many mail-in ballots to apply. 💥 9/20- Gwinnett County, Georgia, Election Board had 40,000 mail-in ballot challenges but would not hear them 💥 9/20- Investigations into voting machine failures and signature verification put over 500,000 ballots in question from the 2022 Arizona midterms. (Hobbs won by less than 20,000 votes.) 💥 9/20- National intelligence researcher Mary Fanning says communist China changed 3,477 votes from Trump to Biden in Emmet County, Michigan, alone 💥 9/19- The Amistad Project claims that they have sworn declarations that say over 300,000 ballots are at issue in Arizona, 548,000 in Michigan, 204,000 in Georgia, and over 121,000 in Pennsylvania 💥 9/19- Electronic voting machine expert claims the number of unsupportable 2020 ballots found for Fulton County, GA, alone is forty-five times larger than Biden’s margin of victory for the entire state. 💥 9/17- An election integrity group claims 10.9 million out of a total of 22.1 million ballots that had been mailed out to registered voters in California during the 2022 midterm elections went ‘unaccounted for.’" 💥 9/17- As many as 34,000 absentee ballots cast in several Detroit, MI, precincts illegally had no signed ballot application, according to a report by The Spekin Forensic Laboratories. 💥 9/17- Wayne County, Michigan, never lawfully certified their 2020 presidential election results, potentially making Donald Trump the winner 💥9/17- An election integrity research group reported that the required chain of custody documentation is missing for 740,000 Maricopa County, Arizona, ballots from the 2020 election 💥 9/17- A voting machine expert says Fulton County, Georgia, conducted no signature verification in the 2020 election, and election officials admitted 💥 9/17- Kari Lake’s newly filed appeal says evidence demonstrates that Maricopa did not test but falsely certified that its 446 vote-center tabulators passed mandatory L&A certification testing prior to Election Day and strongly suggests Maricopa planned the Election Day debacle 💥 9/16- Kari Lake’s newly filed appeal suggests that new evidence shows Maricopa County did not comprehensively compare 275,000 voter signatures according to the county's and state’s own rules. 💥 9/15- Electronic voting machine expert Garland Favorito has testified that about 100,000 improper chain of custody forms were picked up after the election was conducted, or pickups were marked 3 minutes apart when the locations were 30 minutes apart in Georgia in 2020 💥 9/15- Approximately 43,000 DeKalb County, Georgia, drop box ballots have no chain of custody forms to authenticate them. 💥 9/15- An electronic voting machine expert testified that his team found as many as 148k ballots tampered with in the 2020 Fulton County, Georgia, election alone; his team didn't look at other counties. 💥 9/14- Electronic voting machine expert Garland Favorito testified that nearly 35,000 people who voted in the Georgia 2020 election had moved out of their registered county prior to the election, which exceeds the 11,779-vote victory margin and is thus sufficient to place the results of the presidential election in Georgia in question.
@matttttt187 - {Matt} $XRPatriot
💥 9/14- Evidence shows the Maricopa County Election Day printer "failures" were caused by malware or by remote access; 200,000 ballots were ejected out of 248,000 votes cast. 💥 9/14- Election machine expert Garland Favorito testified that he found 106,000 2020 Georgia ballots had massive problems with the chain of custody, like the times and places didn't make sense or were contradictory, and in some instances the documentation was just flat out missing. 💥 9/14- Evidence shows the Maricopa County Election Day printer "failures" were caused by malware or by remote access; 200,000 ballots were ejected out of 248,000 votes cast 💥 9/13- Electronic voting machine expert Garland Favorito says a hand count audit of Ware County, Georgia’s 2020 presidential election, found about a .25% misrecorded vote rate, almost exactly the victory margin rate that Joe Biden received over Donald Trump 💥 9/13- A comprehensive report compiled by Look Ahead America provides specific, verifiable evidence that illegal ballots in Georgia likely exceeded the margin of victory in the 2020 presidential race. 💥 9/13- Electronic voting machines expert Garland Favorito says he found counties in Georgia had destroyed 1.7 million ballot images in violation of the law, and the surveillance video of drop boxes for 181,000 ballots was deleted in violation of the law. 💥 9/13- Election software (KNOWiNK Systems) that is used in 36 states plus Washington, D.C., has contracts that include a clause that allows the election staff to override the results of an election. 💥 9/13- All or large parts of 2,000,000 2020 original ballot images from 70+ Georgia counties are missing. 💥 9/12- There are six sworn affidavits of counterfeit mail-in ballots in Fulton County, Georgia, with election results scaling into the tens of thousands. 💥 9/12- Fulton and Cobb, two of Georgia’s most populous counties, admit they are missing some or all of their 2020 original ballot images, a violation of federal and state retention laws. (Estimated 393k+ in Cobb and 350k+ in Fulton) 💥 9/12- Issues were found with transfer forms for 43,907 out of 61,731 absentee ballots cast via drop box in DeKalb County, Georgia, in the 2020 election. 💥 9/11- A forensic expert claims Dominion was connected to the internet at the ‘same exact time’ the official results of Maricopa County 2020 general election were deleted. 💥 9/11- Former Wisconsin Supreme Court Justice claims his investigation into election fraud in Wisconsin's 2020 election found that election officials failed to record noncitizens in the voter database, so they were able to vote. 💥 9/11- Former Wisconsin Supreme Court Justice Michael Gableman testified that his investigation found that there were far more people registered to vote than were eligible; 4.5 million eligible voters, but over 7 million on the rolls. 💥 9/11- A Wisconsin judge has ruled that the "National Mail Voter Registration Form" used to register over 250,000 voters before the 2022 midterms is illegal due to the form not including an area to fill in whether a voter has been convicted of a felony or how long they’ve lived in their district (required by state law). 💥 9/11- BREAKING: Trump’s legal team’s accusations of election fraud in Georgia • 2,506 felons voted illegally • 66,248 underage • 2,423 were not listed as registered • 1,043 illegal voters casted a vote via post office box • 4,926 voted past the registration date • 10,315 were deceased before election • 395 cast ballots in another state • 15,700 changed address before election • 40279 moved across county lines at least 30 days prior to Election Day and failed to reregister 💥 9/10- Trump's attorney John Eastman says there is “evidence of coordination in Wisconsin between election officials and Democratic Party officials.”
@matttttt187 - {Matt} $XRPatriot
💥 9/10- A Runbeck Election Services whistleblower claims approximately 300,000 illegal ballots for Katie Hobbs were inserted into the Arizona 2022 election without going through the lawful chain of custody. 💥 9/10- Kari Lake’s attorney says they found evidence of malware put on printers used at 223 vote centers, resulting in over 7,000 ballot rejections every 30 minutes, all the way until after the polls closed. (That is over 200,000 ballot rejections on a day when there were only 248,000 votes cast.) 💥 9/8- The US Office of Special Counsel learned that all machines in Green Bay were ESS machines and were connected to a secret, hidden Wi-Fi access point at the Grand Hyatt hotel, which was the location used by the City of Green Bay on the day of the 2020 Presidential election 💥 9/8- Former Wisconsin Supreme Court Justice Michael Gableman says he found that nursing home workers were forging residents' signatures for absentee ballots and pressuring residents to cast ballots who had been adjudicated incompetent during the 2020 election. 💥 9/8- Wisconsin Supreme Court rules absentee ballot drop boxes are illegal 💥 9/8- Trump attorney John Eastman’s testimony - • Zuckbucks, with $8.8 million provided to Wisconsin's five large cities, violated the law: • Zuckerberg's "employees" work for the clerk’s offices and get access to voter information that costs the public $12,500 but has a 4-5 day delay, so there is no way to verify activation. • If clerks did not comply with Zuckerburg’s employees, there was a ‘penalty.’ • They had access and chased down ballots that were requested but not returned. • Zuckerberg's employees essentially "ran the elections" while making statements against Trump. • The WI Supreme Court confirmed ballot boxes were illegally placed, causing "illegally cast votes." • The guy Zuckerburg hired to run the operation wrote a book on how to win the election in this manner. 💥 9/7- Former Wisconsin Supreme Court Judge Michael Gableman testified election officials failed to have bipartisan observers present when collecting votes from nursing homes and just told clerks to break the law - Gableman claims there is video proof of officials admitting guilt. 💥 9/7- Preliminary AZ Senate forensic ballot audit findings show over 200,000 'non-conforming' 2020 ballots. 💥 9/7- Election expert claims 25% of all the 2020 Maricopa County, AZ mail-in-ballots have no signature match, meaning 420,987 ballots out of 1.9 million are fraudulent, invalid and illegal. 💥 9/7- Lawsuit filed against Fulton County, Ga claims there is a total of nearly 150,000 'non-conforming' 2020 ballots still locked up.

@jeffmfulgham - Jeff Fulgham
My posts on evidence of election fraud in GA 2020 have 1 million+ views. Let me explain how we arrived at this point where the Deep State is running state elections. The Obama Admin seized control in 2016/17 by designating elections as a federal Critical Infrastructure. https://t.co/LNBBTujQvz
@jeffmfulgham - Jeff Fulgham
This designation enabled the federal government to assign security jurisdiction over all state election systems to the DHS. They began establishing leverage and control over Secretaries of State, especially in key swing states. https://t.co/ZsHfYnaqWe
@jeffmfulgham - Jeff Fulgham
This seizure of state election systems was literally one of the last actions by the outgoing Obama Admin. Then in 2018 CISA (DHS) was established and this agency took the lead cyber security role in state election systems. https://t.co/30hcbAqkde
@jeffmfulgham - Jeff Fulgham
Now evidence from the ongoing Missouri V Biden case shows that CISA was using social media and shady non profits to censor the speech of conservatives in 2020 and beyond. The Deep State controls the office of the GASOS. This is the challenge we face.
@jeffmfulgham - Jeff Fulgham
"The November 3rd election was the most secure in America history." -CISA This was announced on November 12, but the GA hand count wasn't completed until November 19. GASOS later admitted several thousand Fulton ballots counted twice. Evidence shows the hand count was faked. https://t.co/8aZJMpUjwq

@CannConActual - CannCon
🧵 1/ Georgia Election Thread: John Eastman said this on Jan 6. I'll explain why that could be so significant to what happened in Georgia, and maybe elsewhere. This is not just important for election integrity, but also for the indictment of @hw_floyd and @realDonaldTrump
@CannConActual - CannCon
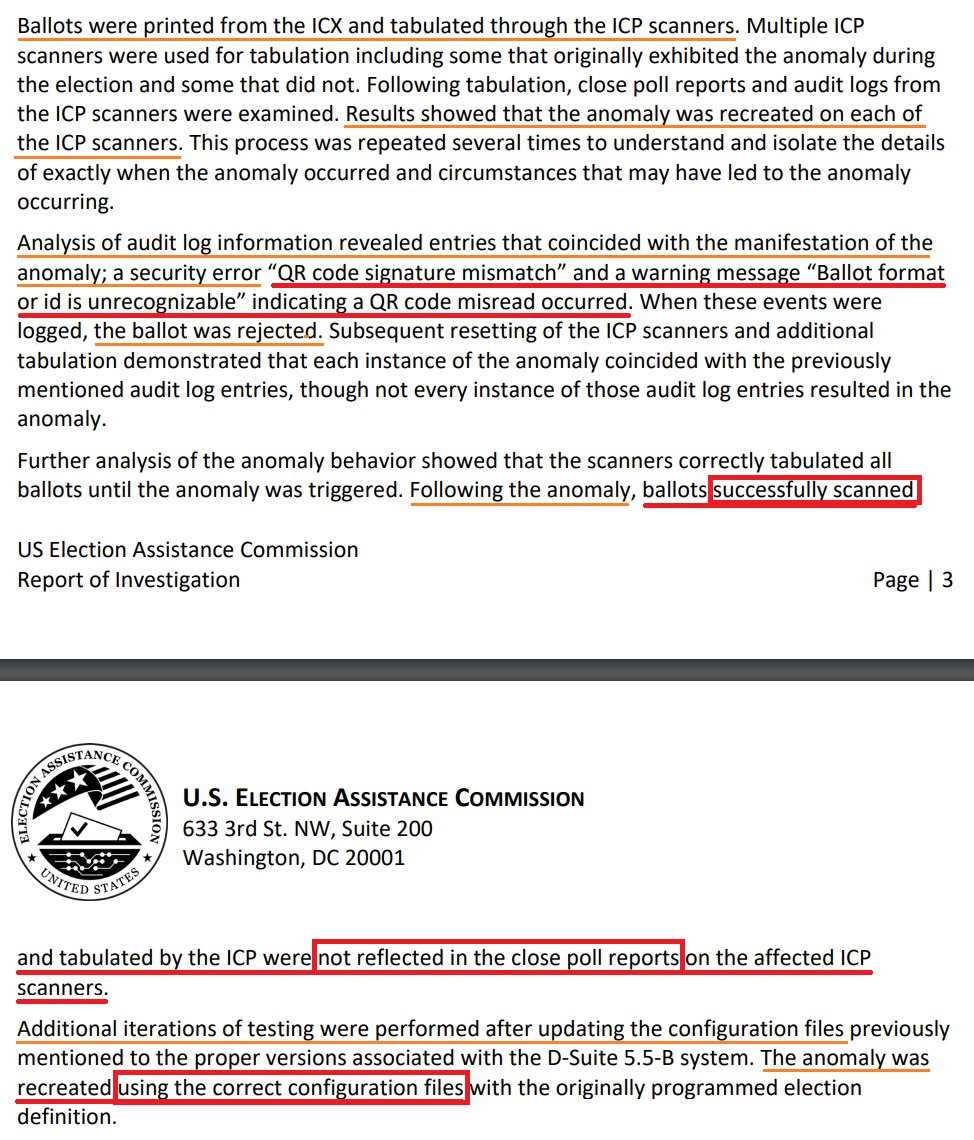
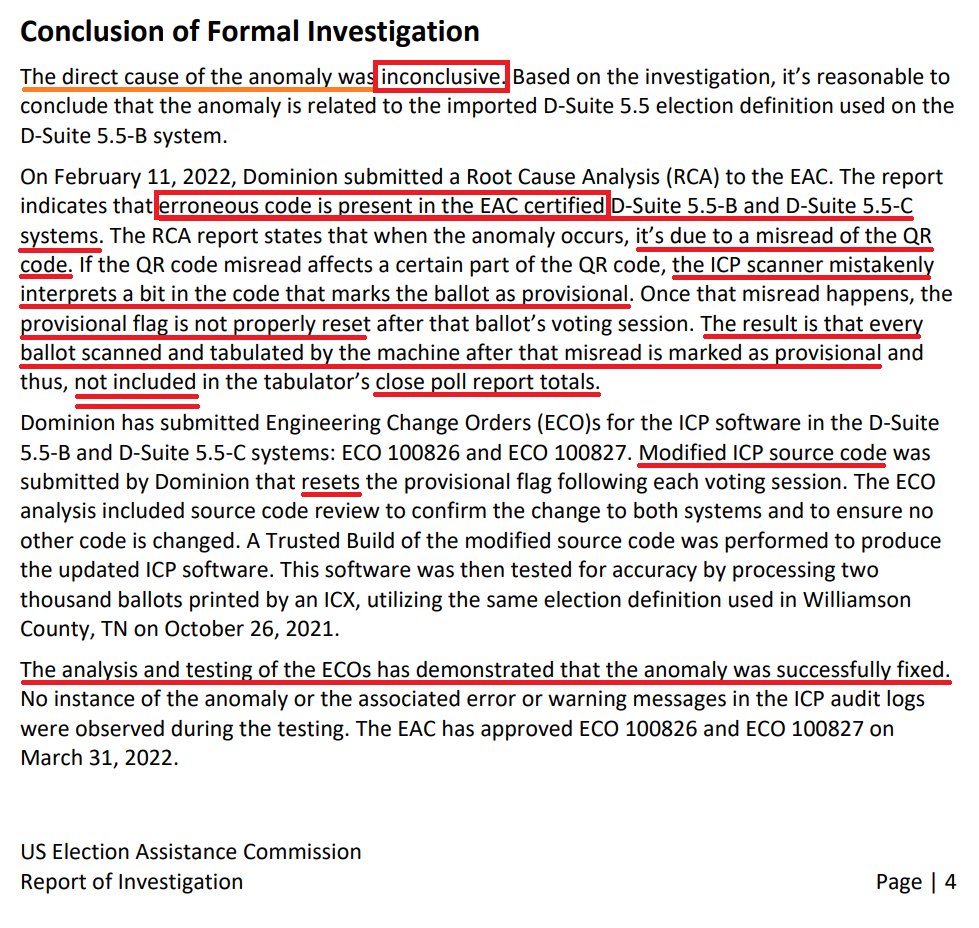
2/ On Oct 26, 2021, almost a year later, the TN Sec. State sent a report to the Elections Assistance Commission (EAC) about "an anomaly" during a municipal election on Dominion tabulators. 7 of 18 tabulators *did not match the number of ballots scanned.* https://www.eac.gov/sites/default/files/TestingCertification/EAC_Report_of_Investigation_Dominion_DSuite_5.5_B.pdf

@CannConActual - CannCon
2 cont'd: This anomaly was discovered after an alert election worker found 163 ballots in a tabulator but only had 79 votes recorded by the machine. The other tabulator had 167 ballots inside of it but only recorded 19! Did these ballots end up in a "cache" secret folder??
@CannConActual - CannCon
3/ Williamson Co uses Dominion ICX BMDs to print/mark ballots and then tabulate them on Dominion ICP tabulators. The EAC's analysis that was performed by Pro V&V and SLI Compliance (voting systems test labs) *with* the EAC, Williams staff, TN SOS *AND* Dominion present.
@CannConActual - CannCon
4/ The report goes on to say that the "direct cause" is "inconclusive" --> Very important word. It also admits that "erroneous code" was found in the *EAC CERTIFIED* systems. *CERTIFIED* The explanation of a "misread of the QR code" is, according to many experts, "absurd".
@CannConActual - CannCon
5/ It's been explained to me that a QR code cannot be "misread". It's either read or its not read. For a scanner to "misinterpret" a bit and cause a ballot to incorrectly be designated "provisional" is extremely concerning. Especially when you see what happens next...
@CannConActual - CannCon
6/ The "misread" ballot (and all succeeding ballots) are also marked as "provisional". They don't reflect in the poll report totals. But they didn't just disappear. This is where Eastman's assertion over ONE YEAR *before* this report is so important.
@CannConActual - CannCon
7/ It's important to note that the problem was not "successfully fixed", as Dominion claims. Instead, some proverbial duct tape was thrown at it and the root cause was ignored. It'd be like resetting your Check Engine light and saying "my car is fixed!"
@CannConActual - CannCon
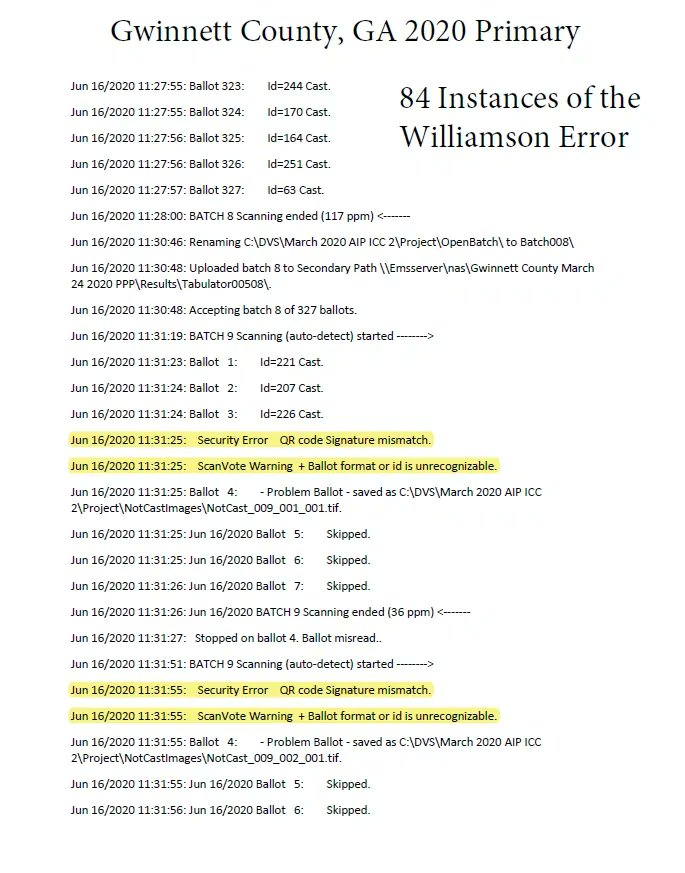
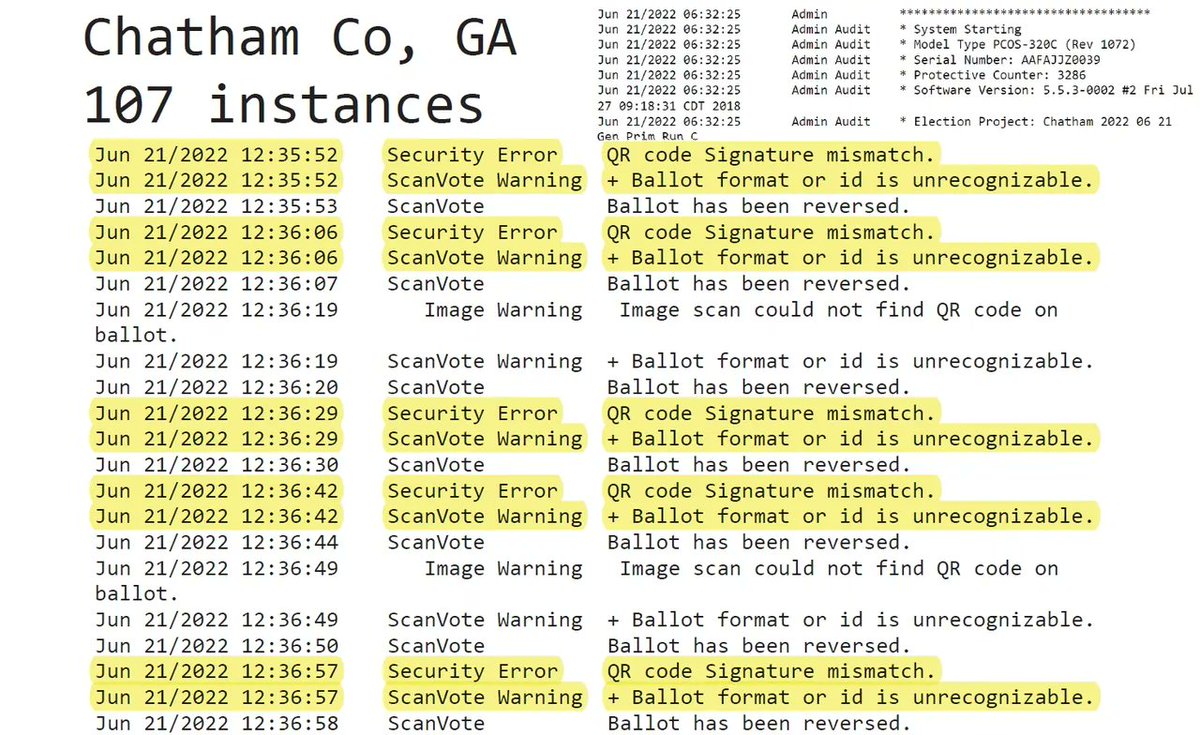
8/ Now here's how its relevant to what Eastman said about Georgia on January 6th! Georgia uses Dominion ICX BMDs and Dominion ICPs, much like Williamson. And much like Williamson, audit logs *and* evidence suggests the same thing may have happened in Georgia.
@CannConActual - CannCon
9/ The Elections Oversight Group (givesendgo.com/ElectionsOvers…) analyzed the system log files for 66 Georgia counties (acquired through Open Records Requests). In **64 out of 66 counties**, they found the same error messages as Williamson. https://gaballots.com/evidence/f/scanner-failures-in-georgia-match-the-williamson-error

@CannConActual - CannCon
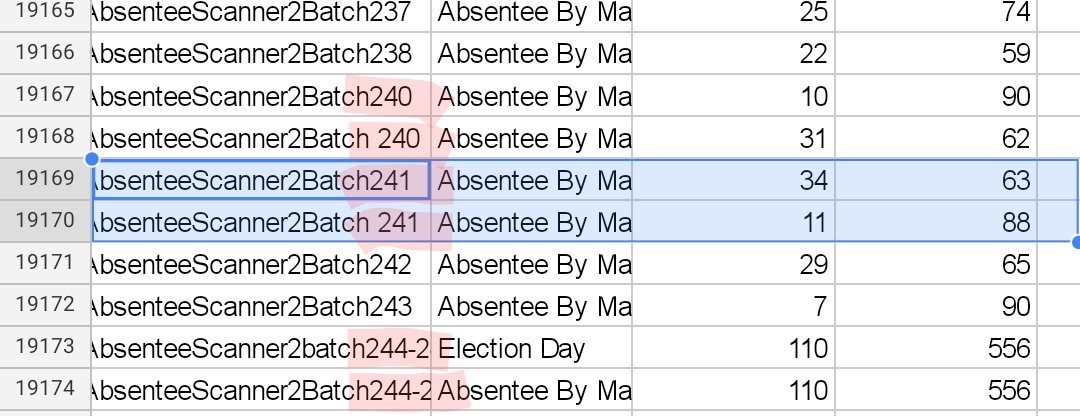
10/ Several GA counties had *more ballots* than recorded votes, as discovered during the hand-recount in Nov 2020. Those included Floyd Co (2600), Fayette (2700), Walton (284) and Douglas (293). Dekalb Co 2022 Dem Primary found 2810 extra votes in a hand count as well.
@CannConActual - CannCon
11/ It is worth noting that the hand-recount was off in Fulton by thousands and thousands of votes and had to double/triple scan ballots to make the numbers match. They entered a Consent Agreement admitting as much. Evidence suggests other counties were off as well.
@CannConActual - CannCon
12/ @TalkMullins was in Floyd County covering this discrepancy. It was reported by the GA SOS Office that this was because a USB wasn't properly uploaded. Officials in Floyd, in the presence of a Dominion rep, disagreed: https://x.com/TalkMullins/status/1328857648276574210?s=20
@CannConActual - CannCon
13/ This issue persisted in 2022 as well. Nothing suggests that this anomaly has even been considered in Georgia despite this evidence. In fact, the @GaSecofState has declined to "patch" their system with a security upgrade recommended after the Halderman report.
@CannConActual - CannCon
14/ In '20, GA was able to update machines with a "de minimis" patch in just a few days, but the vulnerabilities pointed out by @jhalderm apparently can't be applied with over 16 months (since report was released) until the '24 election. "Most secure election American history"
@CannConActual - CannCon
End/ Oh and, for another thread, the ACLU had unfettered access to Georgia's E-net, some on their PERSONAL computers, during the 2020 Election. Here's a veteran poll manager on what that could access could be used for: https://t.co/rtD68FKcM1

@Real_RobN - 🇺🇸RealRobert🇺🇸
And here is how the incompetent, unequipped criminal Georgia Secretary of State Rat Raffensperger re-elected himself on Nov 8, 2022, Dominion Voting Services, https://t.co/JLKhBYs5ik

@Rasmussen_Poll - Rasmussen Reports
"University of Michigan Professor of Computer Science and Engineering J. Halderman and Security Researcher and Assistant Professor at Auburn University Drew Sringall collaborated on the report where they discovered many exploitable vulnerabilities in the Dominion ... 1/3
@Rasmussen_Poll - Rasmussen Reports
... Voting Systems’ ImageCast X system. Far-left Georgia Judge Amy Totenberg sealed and covered up the results of the investigation on Dominion voting machines in Georgia and sat on the report for two years until its release last summer. The report confirms that votes ... 2/3
@Rasmussen_Poll - Rasmussen Reports
... can be altered in the Dominion voting machines. In fact, the report reveals that the Dominion software is vulnerable and can be hacked. Trump-hating Georgia Secretary of State Brad Raffensperger hid this information from the public until June 2023." https://www.thegatewaypundit.com/2023/12/this-is-big-georgia-secretary-state-brad-raffensperger/


@KanekoaTheGreat - KanekoaTheGreat
🚨JUST IN - President Trump Releases Summary of Election Fraud in the 2020 Presidential Election in the Swing States Introduction: It has often been repeated there is “no evidence” of fraud in the 2020 Election. In actuality, there is no evidence Joe Biden won. Ongoing investigations in the Swing States reveal hundreds of thousands of votes were altered and/or not lawfully cast in the Presidential Election. Joe Biden needed them. On Election Night Nov. 3, 2020, President Donald J. Trump was sailing to reelection with landslide leads in numerous battlegrounds. In Georgia, President Trump was up by 12 points, and over 335,000 votes, with 56 percent of the vote in at 10:17 p.m. In Wisconsin, President Trump was leading by 121,380 votes and 5 points at 12:12 a.m., which Fox News anchor Bret Baier noted was “not a small margin.” In Pennsylvania, President Trump was leading by 659,145 votes at 12:38 a.m., a full 15 points. In Michigan, President Trump was leading by 293,052 votes and 10 points. The election was over. However, precincts in Atlanta, Detroit, Philadelphia, Phoenix, and Milwaukee kept counting until the results reached the desired outcome, which was the opposite of the will of the voters. Georgia went from having a total of 4.7 million votes, already a record for the state, according to Brad Raffensperger’s count on Nov. 4, to certifying almost 5 million. This was 300,000 more votes than what the top elections official claimed were cast in the Election. Getting to this result in Georgia, and other states, created an irredeemably compromised Election, filled with violations of the Constitution, unlawful ballots, widespread broken chain of custody, electronic manipulation, and missing and corrupted election files that made it uncertifiable — and impossible to recreate the results. President Trump was right to voice his objections to what had unfolded before the country’s eyes. Republican poll watchers were denied access to the counting in multiple jurisdictions and ballots were counted in secret in the middle of the night without media or observers present. Countless irregularities emerged, including reports of ineligible voters, voting machine anomalies, “water main breaks,” improbable percentages of ballots for Biden, and more. Since, investigations across the country have uncovered an avalanche of irregularities, unlawful activity, manipulation of election records, destruction of evidence, and fraud. The findings, which are outcome determinative, are detailed in the summaries of the Swing States. GEORGIA🚨 • Georgia was called by 11,779 votes. • Fulton County, Georgia, the most populous county in the state, has no digital record of all in person votes cast in its original results. • Not a single ballot purportedly cast during early in-person voting was witnessed to and signed off by poll managers, as required by Georgia election rules. Seals were broken and memory cards removed from tabulators for the results of these 315,000 votes, which were printed out on different machines than the ones that tabulated them. This prevented the reconciliation of how many votes were cast on each machine. • The ballot images of these votes, along with the rest of in-person ballots cast on Election Day, were destroyed. • The vote in Georgia was counted three times: the original machine count, a statewide hand recount, and a second machine count. Each time the state, and Fulton County, reported three different results. • Fulton County did not count the same ballots during the original count and the machine recount. There are 19,541 distinct ballots that appear in one machine count but not the other. • Thousands of fraudulent “presidential only” ballots were injected into the second machine count, with huge margins favoring Joe Biden. Ballots that are blank except for the presidential contest were counted in batches together, with the pattern appearing in at least eight counties, including Fulton. This means Georgia did not have the votes to justify its original Election “results.” • The second machine count was over 17,000 votes “short.” Fulton County was instructed to “reconcile” the results by the Secretary of State, and recertified its results without divulging the extent of the vote deficiency to members of the Fulton County Board of Registrations and Elections. • “Thousands of bogus votes” were ultimately added into the Election results via the second machine count. This includes 20,977 unsubstantiated votes of unknown origin. The results were missing 17,852 ballot images, and included 3,125 duplicate ballot images that were counted twice. • At least 2,871 ballots were counted two or three times in the second machine count, totaling 6,118 questionable votes. • Eighty-eight percent of Fulton County’s precincts reported a different total number of votes between the first and second machine count. • The only electronic votes that survived from the first count were the mail-in ballots, since they were tabulated on the high speed scanner their ballot images were automatically uploaded to the election server. • Ninety percent of these approximately 148,000 absentee ballots cast in Fulton County cannot be authenticated. Ballot images for 132,284 mail-in votes have no .SHA file, which is created automatically when a ballot is scanned and used to authenticate the digital image of the vote, lacking evidence they were scanned and tabulated properly, or even cast by a real voter. • 104,994 ballot image files of these mail-in ballots from the original count contained identical modified time stamps, suggesting electronic manipulation. • Fulton County does not know “how many voters cast votes” and its “lack of basic accounting controls make it impossible to determine who really won” in 2020, according to Philip Stark, a University of California, Berkeley professor who invented risk-limiting audits. Stark noted, “The electronic records of the election are not intact.” • 376,863 ballot images are missing from the first machine count, which includes all in-person votes in Fulton County. • None of the 315,000 votes cast during early voting in Fulton County were witnessed to and signed by the poll manager and two poll workers, as required by state election rules. The closing tapes for these votes are all unsigned, showed more tabulated votes than the tabulators had recorded as scanning in their protective counters, and recorded improbably low percentages for President Trump. For example, President Trump received only 0.9 percent, 2.4 percent, 3.7 percent from some of the tabulators, as if he was a third party candidate, or in a third world country. The anomalies indicate ballots were not scanned on the tabulators that printed the closing tapes, making the closing tapes fraudulent. • Tabulators used in Fulton County during early voting had their seals broken, and memory cards were reprogrammed and inserted into different scanners to count absentee ballots, in violation of election rules. This made it impossible to reconcile the true number of votes tabulated on the machines from the start of the Election to the end of counting. • 235,000 absentee ballots were requested and accepted too early, prior to the lawful date 180 days before the 2020 Election, which was May 6, 2020. These votes should have never been counted in the 2020 Election. • 4,081 false votes for Joe Biden were included in the hand count audit results for Fulton County. The false votes were the result of 36 accounting errors, which were confirmed by Governor Brian Kemp’s office and investigators working for Secretary Brad Raffensperger, yet they have never been removed from the official hand count results. These errors alone would reduce the margin to 7,698 votes. • The hand count audit included 3,935 unaccounted for votes due to 11 missing batch sheets in Fulton County. Differences from the original count to the hand audit total at least 15,690 votes, which is more than the entire election margin alone. This includes the 4,081 false Biden votes, plus “missing” votes discovered in Gwinett (1,642), Fayette (2,755), Floyd (2,700), Douglas (293), and Walton (284) counties that were likely due to machine counting errors. • Thousands of “pristine,” unfolded absentee ballots were counted during the hand count audit in Fulton County, according to at least six witnesses, which is the subject of ongoing litigation. These absentee ballots had no folds, and went 98 percent to Joe Biden, had “been added in a fraudulent manner,” witnesses said. • Fulton County certified 59,143 in-person votes on Election Day, despite the fact that only 14,152 people had voted as of 5 p.m. on Nov. 3, 2020. Evidence suggests the in-person vote total on Election Day was inflated by approximately 37,000 votes, as records show no rush to the polls during the final two hours of voting, and a screenshot of the in-person Election Day results shared by a government contractor showed only 21,843 people voted at the polls in Fulton County on Nov. 3. • Fulton County ordered over 1 million absentee ballots days before the 2020 Election, without any envelopes and the time necessary to mail. There were only 808,680 active voters in Fulton County as of Nov. 1, 2020, meaning the county had more blank mail-in ballots than the number of registered voters, and ordered them after the vast majority of mail-in ballot requests had already been sent to voters by Runbeck Election Services. • An estimated 30,000 to 92,670 illicit votes were trafficked in Georgia, as part of a massive ballot trafficking operation discovered by True the Vote. The group identified 242 traffickers in Georgia who engaged in 5,662 ballot drops into drop boxes, making an average of runs per trafficker. Over 40 percent of the illicit drops that were captured on camera were recorded between the non-voting hours of midnight and 5 a.m. • There were over 364,000 ineligible voter registrations on the rolls during the 2020 Election and likely 67,284 votes were cast from voters with invalid residency. • Massive manipulation of the Georgia voter rolls surrounding the 2020 Election has been uncovered. This includes 1,500 Voter IDs that received credit for voting in 2020, but were not on any voter rolls from 2020, some appearing for the first time on the voter rolls on Nov. 4, 2021, a year after the Election. Other findings include manipulation of inactive voters to cast ballots, “gifting” Nov. 3 votes up to 2 years after the Election, and casting votes on ballots previously rejected, cancelled, or not even turned in. • In 2020, there were absentee ballots issued to “Bangkok Thailand, Ga.,” “Denver, Ga.,” “Detroit, Ga.,” “Los Angeles, Ga.,” and other fraudulent addresses that do not exist. Ballots were fraudulently cast in 2020 from addresses listed as “Bronx, Ga.,” “Hilton Head, Ga.,” “Louisville, Ga.,” “San Diego, Ga.,” “New Orleans, Ga.,” “French Creek, Ga.,” “Virginia Beach, Ga.,” “Vicksburg, Ga.,” “Baltimore, Ga.,” “New York, Ga.,” and “Sarasota, Ga.,” all with zip codes out of state. • 43,907 drop box ballots violated chain of custody requirements in DeKalb County. • 59,000 of the 79,460 drop box ballots in Fulton County were not immediately transported to the election registrar, in violation of State Election Board rules. • An estimated 355,000 ballot transfer forms for drop box ballots are missing statewide. • Over 100,000 tally sheets for Fulton County were missing from the hand count audit, and remained missing for months after the Election. • In early January 2021, Ruby Freeman asked for an attorney because she wanted to “go live on every platform” to divulge information about how “the USB ports” were used in the 2020 Election. The expert cyber report by Professor J. Alex Halderman explained how external USB ports with election-changing malware can be inserted into Dominion machines by anyone with access, including election workers. • The presence of a “QR code mismatch” error within the Dominion tabulators that systematically undercounts votes was found in 65 out of 67 Georgia counties where records were available. The error was present in system log files for tabulators used in elections in 2020, 2021, and 2022. • The election results in Georgia in 2020 are not only unreliable, but were electronically altered, and are unsupported by the state’s own election records. The appearance of tens of thousands of unconfirmed ballots in subsequent hand and machine counts suggest reconciliation happened after the Election, meaning after it was clear what margins were needed to win. • Fulton County election officials admitted in early 2021 they do not engage in any reconciliation until weeks after Election Day. This means the number of voters showing up at the polls during each day of voting is not checked with the number of ballots tabulated each day, a basic process to ensure the number of ballots and voters match, and cannot be manipulated later. • “We can’t start reconciling that until usually a couple days before certification,” said then-Fulton County Elections Director Richard Barron, during a January 2021 Board meeting. “Because we have to get that report from KnowInk. I think KnowInk sends those to the state or KnowInk sends those directly to us. But those aren’t compiled then, on Election night. So we don’t have any way to balance those then. That’s like the post-election process that we do.”
@KanekoaTheGreat - KanekoaTheGreat
JUST IN - President Trump Releases Summary of Election Fraud in the 2020 Presidential Election in the Swing States WISCONSIN🚨 • Wisconsin was called by 20,682 votes. • The Wisconsin Supreme Court ruled drop boxes are illegal under Wisconsin law, in a 4-3 decision issued in July 2022. • Wisconsin Election Commissioner Meagan Wolfe unilaterally declared ballot drop boxes could be used to vote in 2020 elections, even though “WEC’s commissioners never voted to adopt this memo.” • Ahead of the November 2020 Election, Wolfe encouraged clerks to use “creative solutions” to deploy drop boxes, that she said could be “unstaffed.” There were 528 drop boxes used in the General Election, and a total of 1,969,274 absentee votes cast, including 1,346,731 votes cast by mail, and 653,236 in-person. • In a concurring opinion to the ruling finding drop boxes to be unlawful, Justice Rebecca Bradley writes, “If the right to vote is to have any meaning at all, elections must be conducted according to law. Throughout history, tyrants have claimed electoral victory via elections conducted in violation of governing law… in Wisconsin elected officials “deriv[e] their just powers from the consent of the governed.” • “The right to vote presupposes the rule of law governs elections. If elections are conducted outside of the law, the people have not conferred their consent on the government. Such elections are unlawful and their results are illegitimate.” • Justice Bradley concluded “thousands of votes have been cast via this unlawful method,” using drop boxes, “thereby directly harming the Wisconsin voters.” • “The illegality of these drop boxes weakens the people’s faith that the election produced an outcome reflective of their will,” Justice Bradley writes. “The Wisconsin voters, and all lawful voters, are injured when the institution charged with administering Wisconsin elections does not follow the law, leaving the results in question…Electoral outcomes obtained by unlawful procedures corrupt the institution of voting, degrading the very foundation of free government. Unlawful votes do not dilute lawful votes so much as they pollute them, which in turn pollutes the integrity of the results.” • In the city of Milwaukee, nearly half of all its votes were cast by mail, totaling 217,424 ballots. The city deployed 15 drop boxes, with election officials claiming the drop boxes would be “under 24-hour surveillance.” However, after the election, not a single municipality in the county produced video surveillance of drop boxes in response to open records requests. Various responses included, “No records exist for your request,” “No video from requested time frame,” “No such records exist,” and “No security camera.” • The election integrity group True the Vote identified 107 ballot traffickers in Milwaukee County between Oct. 20 and Nov. 3, 2020, who each made 20 or more visits to drop boxes. Each trafficker made an average 26 visits, and as many as 15 in one day, and made multiple visits to non-governmental organizations. • The 107 traffickers made a total of 2,824 trips to drop boxes during the 2020 Election, with a majority of visits occurring after 8:00 p.m. • In 2020 there was a surge of “indefinitely confined” votes in Wisconsin, resulting in 220,404 votes cast from individuals who were exempted from showing voter ID. This surge of suspect votes was due to Democrat election clerks giving advice that was deemed illegal after the election, instructing voters to identify themselves as disabled during the COVID pandemic to avoid voter ID laws. • Indefinitely confined voters, who are supposed to be physically unable to go to the polls due to age, disability, or illness, increased by an astounding 393 percent in Dane County from 2016 to 2020; 492 percent in Racine County; 281 percent in Milwaukee County; and 287 percent in the state overall. • There were just 56,978 indefinitely confined votes in 2016, and roughly 70,000 43 in 2019. In 2020, however, there were 220,404 votes cast using indefinite confinement status. Over 77 percent of these individuals had never been listed as indefinitely confined before. The Wisconsin Legislative Audit Bureau identified 48,554 people who voted as indefinitely confined in November 2020 who had never provided photo identification or did not have photo identifications on file with clerks, which is more than twice the vote margin of 20,682. • Scott McDonell, the Democrat clerk of Dane County, which encompasses the area of Madison, told all residents they could identify themselves as indefinitely confined because of COVID, specifically citing it as a way to get around the Voter ID law. • McDonell previously blamed Wisconsin’s voter ID law for President Trump’s victory in 2016, claiming in a 2018 Twitter post that “thousands of voters [were] deterred from voting due to [the] ID law.” • In 2020, McDonell urged all voters to declare themselves indefinitely confined in order to obtain an absentee ballot and “skip the step of uploading an ID” in the April 2020 primary election. Once a voter is identified as indefinitely confined, they continue to receive absentee ballots automatically for subsequent elections. “I urge all voters who request a ballot and have trouble presenting a valid ID to indicate that they are indefinitely confined,” McDonell said in a Facebook post. • The Wisconsin Supreme Court ruled in December 2020 that the pandemic “did not render all Wisconsin electors ‘indefinitely confined,’ thereby obviating the requirement of a valid photo identification to obtain an absentee ballot,” and the clerks’ “interpretation of Wisconsin election laws was erroneous.” • The Wisconsin Election Commission ordered nursing homes to violate the law by not allowing Special Voting Deputies (SVDs) inside their facilities, which led to election fraud where incapacitated elderly residents had votes cast in their name with the assistance of nursing home staff. • An investigation by the Racine County Sheriff found the Wisconsin Elections Commission “shattered” state election laws. Nursing homes saw an “unusual surge in voting activity,” and at least 8 cases of felony voter fraud were found in one nursing home, accounting for nearly 1 in 5 families of residents. • The Wisconsin Election Commission admitted it was “essentially telling the clerks to break the law” by ordering the sending of absentee ballots to nursing homes and barring Special Voting Deputies inside the facilities. • An interim report released by Special Counsel Michael J. Gableman raised “serious and legitimate questions that the certification of Wisconsin’s election results may have been undertaken in an unlawful and unconstitutional manner.” • Gableman claimed “Democracy in the Park” events in Madison involved numerous possible violations of the law, “calling into question the validity of over 17,000 absentee ballots.” • These outdoor events to collect mail-in ballots were the subject of numerous complaints, and it is “not clear that all of the workers at those events were properly deputized and trained, swore and filed the mandatory oath of office, or documents related to absentee ballots were properly handled.” • The Office of the Special Counsel also claimed evidence of “undue influence by well-funded private groups, who leveraged large grants to certain Wisconsin cities in order to co-opt our election apparatus to their benefit.” • The report confirms at least 17.5 percent of election clerks “were not properly trained,” and that “exploitation of elders” occurred in nursing homes. • In one example, Maryl Barrett, who was 104 years old and did not recognize her own children, had a ballot cast in her name in the 2020 Presidential Election. • The Office of Special Counsel’s second interim report found nursing homes in Milwaukee, Dane, and Racine counties with 100 percent turnout due to the Wisconsin Election Commission’s order. • The special counsel said it possessed evidence of nursing home facility staff and directors who “assisted residents in completing ballots; assisted residents in obtaining absentee ballots; pressured residents to vote; collected completed ballots from residents; forged signatures of residents; illegally returned residents’ ballots to the municipal clerks by mail, by placing the ballots in drop boxes, and/ or delivering them directly to the clerks; pressured and/or assisted incompetent persons to complete and cast ballots in the November 2020 election, up to and including persons who have had their right to vote take away by court order due to mental incompetence.” • The second interim report also detailed an $8.8 million “election bribery scheme” involving Mark Zuckerberg’s Center for Tech and Civic Life and the cities of Milwaukee, Madison, Racine, Kenosha, and Green Bay. “In the agreement, the Cities took CTCL’s money to facilitate in-person and absentee voting within their respective city.” • The “Wisconsin Safe Voting Plan” developed for CTCL facilitated grants to major Wisconsin cities to deploy drop boxes for mail-in ballots, including $50,000 to Green Bay, $40,000 to Kenosha, $50,000 to Madison, $58,500 to Milwaukee, and $18,000 to Racine. • Whitney May, the director of government services for CTCL, posted numerous anti-Trump posts on social media, including telling people “don’t vote for Trump” in 2016. • Internal emails from election officials in Green Bay revealed Michael SpitzerRubenstein, a former Democratic Party operative, served as a “de facto elections administrator and had access to Green Bay’s absentee ballots days before the election.” • The Office of the Special Counsel referenced this case, and has evidence that this grantee, which was funded by CTCL, was “directly involved in all aspects of management of election officials, was entrusted with the only sets of physical keys to the city’s central count location, managed the transportation of ballots, and instructed the counting of unlawful ballots that had arrived at the central count location beyond the lawful time window.”
@KanekoaTheGreat - KanekoaTheGreat
JUST IN - President Trump Releases Summary of Election Fraud in the 2020 Presidential Election in the Swing States PENNSYLVANIA🚨 • Pennsylvania was called by 80,555 votes. • Months after the election, there were 121,240 more votes than voters, according to the Pennsylvania Department of State. By law, Pennsylvania cannot certify an election with this type of discrepancy. • Republican lawmakers, led by State Representative Frank Ryan, were tracking the vote discrepancy in real time in the Statewide Uniform Registry of Electors (SURE) system. Ryan, a certified public accountant, initially reported that there were 170,830 more votes than voters in the Presidential race, more than twice the margin in Pennsylvania. “These numbers just don’t add up, and the alleged certification of Pennsylvania’s presidential election results was absolutely premature, unconfirmed, and in error,” the lawmakers said. • The Pennsylvania Department of State’s office called this “obvious misinformation,” while admitting the “only way to determine the number of voters who voted in November from the SURE system is through the vote histories,” which they said Philadelphia, Allegheny, and other counties had still not completed — an admission the election was certified without ensuring the number of voters and votes matched in the SURE system. The election was certified on Nov. 24, 2020, and the Department of State’s statement came on Dec. 29, 2020. • The SURE system was checked and downloaded weekly with updated voter histories from the general Election until all the counties uploaded their vote histories, which was not completed until February 2021. At this time there were still over 121,000 votes that did not have a corresponding voter in the SURE system. • The statement by the Department of State “that the voting would reconcile, once the counties completed their SURE uploads, was incorrect,” according to Verity Vote. “When the final county finished uploading their voter histories and closed the election in SURE, it was February 1, 2021, which was the same day that [Secretary of State Kathy] Boockvar announced her resignation. At the time that Philadelphia closed the election in SURE, the voter histories showed that the county accepted at least 7,944 ballots that could not be associated with a registered voter.” • Pennsylvania credited 71,893 people for voting who returned mail-in ballots after Election Day, and these individuals were included in the voter history files. This includes 50,285 received between Nov. 4 and Nov. 6; 11,570 received between Nov. 7 and Nov. 11; and 10,038 that were received on or after Nov. 12. Boockvar claimed only 10,000 ballots were received between the close of the polls on Election Day and Nov. 6. • While 71,893 people received credit for voting by mail, these votes purportedly did not count. Even while including these voters in the total number of who participated in the Election, Pennsylvania still came up 121,240 voters short. • According to the Department of State data, there were 7,035,746 ballots cast in the 2020 Presidential Election, including all write-in votes, over-votes, and under-votes. “After all counties closed the election in SURE, only 6,914,556 voters were credited with participation in the 2020 General Election. This reveals a voter deficit of 121,240.” • In Philadelphia, hundreds of thousands of mail-in ballots were unlawfully counted in secret, in defiance of a court order, while Republican poll watchers were thrown out of buildings where voting took place. • U.S. Attorney Bill McSwain was told to stand down and not investigate election irregularities by Attorney General Bill Barr. McSwain said he was instructed to not discuss the allegations of voter fraud he received, and to pass any “serious” investigations along to then-State Attorney General Josh Shapiro, a Democrat who promised days before the election that President Trump “is going to lose.” • Mark Zuckerberg of Facebook poured over $25 million into the administration of the election in Pennsylvania in 2020. Over $10 million went to the Democrat-controlled jurisdiction of Philadelphia, which included $5.5 million on “ballot processing equipment” and $552,000 for drop boxes. • A lawsuit filed in Delaware County revealed video evidence of election officials discussing destroying election evidence from the November 2020 Election. “It’s a felony,” one official says after talking about the need to “get rid” of voting “pads and second scanners.” Sources involved in the litigation alleged the Delaware County officials violated numerous election laws and that the destruction of records was “done to ensure records eventually provided actually matched the election results that were reported in Nov. 2020.” • Delaware County received $2.2 million from Zuckerberg’s Center for Tech and Civic Life (CTCL), which it spent on “recruiting and training a sufficient number of poll workers; setting up drop box locations for voters to return ballots,” and other Get Out the Vote efforts. • The election integrity group True the Vote said Philadelphia was the worst offender it witnessed when investigating the widespread ballot trafficking scheme operating across multiple Swing States in 2020. They identified 1,155 ballot traffickers who each visited at least 10 drop boxes and five non-governmental organizations. Some ballot traffickers made hundreds of trips to drop boxes.
@KanekoaTheGreat - KanekoaTheGreat
JUST IN - President Trump Releases Summary of Election Fraud in the 2020 Presidential Election in the Swing States ARIZONA🚨 • Arizona was called by a margin of 10,457 votes. • Maricopa County accepted 20,500 mail-in ballots after Election Day 2020, including 18,000 – more than the entire election margin – on Nov. 4 picked up from the U.S. Postal Service. By law, ballots must be received no later than 7 p.m. on Election Day, which was Nov. 3. • “The 20,000 ballots recorded as incoming from the USPS on and after November 4 were of sufficient quantity to change the result of the 2020 General Election in Arizona,” according to Verity Vote. • The findings were based on Maricopa County’s official Elections Department records, which were withheld from a public records request for nearly seven months. The records showed 18,000 mail-in ballots received on Nov. 4; 1,000 received on Nov. 5; and 1,500 received on Nov. 6. • The 18,000 mail-in ballots received on Nov. 4 and subsequently counted represented a significant spike in ballots received, higher than every single day total since Oct. 29, 2020. The receipt of mail-in ballots had steadily declined from 14,500 ballots on Oct. 29 to 10,500 on Oct. 30; 6,000 on Oct. 31; 1,500 on Nov. 1; 1,000 on Nov. 2; and 2,500 on Nov. 3. • In the 2020 General Election, 420,987 ballots failed signature verification standards, “thus the election was openly vulnerable to fraud,” according to an ongoing analysis conducted by We the People Arizona Alliance and presented to the state legislature. • The initial analysis of 380,976 ballots, using official state records and official signature verification training techniques, identified 181,378 ballots that should not have been counted, or nearly half of all reviewed. • This includes: 1,870 blank envelopes, some of which were approved on Nov. 5 and Nov. 8; 542 with a signature other than the voter; 2,104 scribbles; 128 duplicate voters processed; 48,117 unreasonably different control signatures; 1,875 where the signature did not match until after the election; 36,034 control signatures that do not match the voter; 4,433 unusable control signatures; 47,366 that failed Secretary of State standards; and 38,909 egregious signature mismatches, where not one point of a signature matched any on file. • In the case of the 1,875 votes, the ballot envelopes did not have a signature match on Election Day, but “matching” signatures were later put on file for the voter on either Jan. 28, 2021, Feb. 3, 2021, or Feb. 8, 2021. There were 783 signatures digitally inserted on Feb. 3, 2021 alone. • Since the findings were presented to the Arizona State Legislature, the number of egregious mismatches found has increased to 76,354, over seven times the election margin. This is an error rate of 9.30 percent of ballot envelopes reviewed. • Throughout the signature verification analysis, which remains ongoing, analysts have consistently found 20 percent do not meet the Secretary of State’s standards, and 9 percent are egregious violations. Extrapolated to all 1.9 million mail-in ballots in 2020, 176,700 ballots “should have been rejected for improper signature verification due to egregious signature mismatches.” • Maricopa County has no documented chain of custody for 740,000 ballots from the 2020 Election. • Out of the 923,000 early vote ballots accepted at vote centers or drop boxes, only 183,406 ballots are accounted for on ballot transport forms. More than 80 percent of the ballot transport forms have no ballot counts. • Without proper documentation of how many votes were cast at the time they were cast, it is impossible to verify the origin and true total of ballots in a given election. “Without this count, there is no way to determine if the transport staff retrieved one ballot or one thousand ballots,” according to Verity Vote. “Keeping a proper chain of custody is more than a best practice - it is essential to encouraging trust in our democracy,” according to the Election Assistance Commission. • Of the 1,895 early vote ballot transport forms, 48 did not have the required two witness signatures attesting to the ballot transfer, including some with no witness signatures at all. “As a result, the public is not assured that both parties witnessed the transfer of ballots,” as required. • Millions of files of 2020 General Election data and security logs were deleted from the Elections Management Server and purged on critical days, including the day before the Arizona audit of the 2020 Election began on Feb. 2, 2021. • The Maricopa County Board of Supervisors admitted they purged the system and moved election data after they received a subpoena, in testimony before the U.S. House of Representatives. • Two precincts in Pima County had over 100 percent turnout for mail-in ballots, and 40 precincts had over 97 percent returned. • The national mail-in ballot return rate was 71 percent, but in Pima County the mail-in ballot return rate was 15 percent higher, and 19 percent higher than all the counties combined in the entire state of Arizona. One precinct with 99.5 percent mail-in turnout had 9,812 ballots counted. Another precinct with 100.6 percent turnout had 2,182 ballots returned, but only 2,170 mail-ins were ever sent. These two precincts total 11,994 ballots, which alone is more than the margin needed to alter the outcome of the Presidential Election. • In all, there were 264,000 votes from precincts in Pima County with over 92 percent turnout for mail-in ballots. • Significant anomalies were discovered for mail-in ballot returns in Pima County. In precincts with anomalous high turnout of over 92 percent in Pima County, mail-in ballots started flipping from 6 percent Republican for Biden to 40 percent of Republicans voting for Biden. • The election integrity group True the Vote identified more than 202 ballot traffickers in Maricopa County who made 4,282 individual drop box visits during the 2020 General Election. • Two individuals were charged and plead guilty for ballot harvesting in Yuma County, Arizona during the 2020 primary election. • A computer scientist testified that an algorithm similar to what is used in cruise control or self-driving cars was present affecting the early votes in Pima and Maricopa counties in the 2020 General Election, with the ability to “reach and maintain a predetermined setpoint (outcome) despite unplanned disturbances.” • Walter C. Daugherity, a senior lecturer emeritus in the Department of Computer Science and Engineering at Texas A&M University who developed courses in artificial intelligence, expert systems, programming and software design, analyzed the Cast Vote Records, finding, “ballots in Maricopa County and Pima County were artificially processed through the tabulators tracking a ProportionalIntegral-Derivative (PID) type control function in a closed-loop feedback system.” • Daugherity, who has received over $2.8 million in grant funding and was previously consulted as a computer expert by the New York Times, Washington Post, IBM Federal Systems Division, the Texas Department of Agriculture, U.S. Customs Service, as well as classified work, discovered “significant and systematic decline in the cumulative ratio as counting progresses,” in the early mail-in and in-person votes for the Presidential Election results in Maricopa County and Pima County. • For example, the “first block of ballots being 75 [percent] for a candidate, the next block of ballots being 74 [percent] for a candidate, the next block of ballots being 73 [percent] for a candidate, and so on, systematically declining all the way to Election Day.” • Daugherity’s expert opinion is that the downward sloping line in the sequence that votes were recorded indicated a strong control. The cumulative ratio of Biden to Trump votes for all cast vote records before Election Day in recorded order for Pima County declines from over 300 percent to 157 percent by Election Day. • “Such a uniform and predictable pattern is so statistically implausible that it would not occur without artificial manipulation,” according to Daugherity. The data’s lack of independence cannot be explained by the preference of Democrats voting earlier than Republicans.
@KanekoaTheGreat - KanekoaTheGreat
JUST IN - President Trump Releases Summary of Election Fraud in the 2020 Presidential Election in the Swing States MICHIGAN🚨 • Michigan was called by 154,188 votes. • A record 5,579,317 votes were cast and certified in Michigan in the 2020 General Election, the highest turnout in 60 years. To date, Michigan has never shown 5,579,317 voters listed for the 2020 Election in its Qualified Voter File, the state’s database for all voter registration records. • As of December 2023, Michigan has 271,566 more votes than the number of voters listed in its Qualified Voter File for Nov. 3, 2020, more than one and a half times the Election margin. • In data obtained from the Secretary of State’s office on nearly a monthly basis since the Election, the most voters ever recorded in the Qualified Voter File was 5,511,303 voters in April 2021. This means Michigan’s own election records showed 68,014 more votes than voters. However, the number of voters listed in the Qualified Voter File has been in flux ever since December 2020, and always short of the voters needed to reconcile the total votes cast. A complete list of voters from 2020 has never been provided. • The number of voter IDs listed as voting in 2020 has steadily declined since February 2022. As of December 2023, there was a total of 5,307,751 voters listed as voting on Nov. 3, 2020 in the Qualified Voter File. Voter history files continue to be removed from the record, resulting in 271,566 less vote history records than necessary to reconcile the results. • Each month voter histories from the 2020 Election are being manipulated. Thousands of unique votes are removed from the voter history files, and other unique votes added. Since December 2020, 270,559 voter histories for 2020 have been removed, while 103,128 have been added. • Individual voter histories are constantly changing, including the history of the state’s Democrat Governor Gretchen Whitmer, whose voting history is missing votes throughout 2020. • A complete list of voters was requested via a Freedom of Information Act request in December 2021 and took nine months for the state to fulfill. Two datasets were provided, and neither matched. The first dataset fell 22,146 voters short, while the second dataset was 120,883 absentee ballots short. • Democrats threatened Republicans on the Wayne County Board of Canvassers and doxxed children in order to certify the 2020 results. Monica Palmer, then the chair of the Wayne County Board of Supervisors, cited the fact that 70 percent of Detroit’s mail-in ballot counts were still “out of balance and unexplained” from the August primary as a reason why she initially voted against certifying the 2020 Election results. Palmer was “bullied and threatened” and “feared for her safety” due to threats she received for voting no. A Democrat Michigan State representative-elect attacked Palmer over her certification vote, and revealed where her children went to school, saying, “I want you to think about what that means for your kids.” • Officials in Detroit illegally blocked Republican poll challengers’ access, covered the windows, called the cops, and denied lawful challenges in order to count ballots in secret. • Affidavits and video evidence revealed thousands of ballots were delivered through a back door of the TCF center, the central counting facility in Detroit, at 3:30 a.m. on Election night. • A report seeking to “debunk” issues of fraud released by the Michigan State Senate Oversight Committee confirmed a “large volume” of ballots were delivered to the TCF center with no chain of custody in the middle of the night. • An estimated 289,866 absentee ballots were identified as sent to people who never requested them, “something that would be illegal,” according to the senate committee. • Mark Zuckerberg gave Michigan $16.8 million through his nonprofit Center for Tech and Civic Life. • Detroit received $7.4 million to “dramatically” expand the vote for Democrats. The grants financed drop boxes “to facilitate the return of absentee ballots,” like the ones that came in the TCF center after midnight. • The election integrity group True the Vote uncovered the same pattern of widespread ballot trafficking between NGOs and ballot drop boxes in Michigan. Numerous instances of ballot stuffing were caught on camera in Detroit, including video where a woman can be seen going to a drop box, and abruptly returning to her car after realizing the stack had no signatures. The woman then signs the ballots, and deposits the illicit ballots she had just signed into the drop box. • Secretary Jocelyn Benson made unlawful changes to signature verification rules for absentee ballots, ordering election workers to presume all were legitimate. A judge ruled Benson’s order was invalid, but not until months following the election, and just 0.1 percent of mail-in ballots were rejected in the November 2020 Election for all signature issues. The rejection rate for mismatching signatures was just 0.04 percent, as only 1,400 out of 3.4 million ballots were rejected. • Secretary Benson has lost in court six times for issues related to the 2020 Election. • A fraudulent voter registration scheme was discovered in October 2020 and documented in a police report in Muskegon County and hidden for nearly 3 years after the 2020 Election. • A city clerk in Muskegon witnessed a woman drop off between 8,000 and 10,000 voter registrations at the clerk office on Oct. 8, 2020, many appearing to be fraudulent. The incident was reported it to the Muskegon Police Department one week later. Eight thousand new voter registrations in Muskegon would amount to over 20 percent of the city’s population of only 38,000 residents. • An ensuing investigation confirmed thousands of voter registrations in the same handwriting and many invalid or non-existent addresses. The suspect told Michigan State Police that she was being paid $1,150 per week to “find unregistered voters and provide them with a form so they can get registered to vote or obtain their absentee ballot.” The police found “dozens of new phones” and “hundreds of pre-paid payment cards” during the investigation. • A Department of State analyst consulted in the investigation confirmed a quantity of voter applications were “clearly fraudulent” and others were “highly suspicious having either erroneous or are missing key pieces of information.” Others appeared to be legitimate. • The organization behind the scheme was GBI Strategies, a firm hired by numerous Democrat campaigns. GBI Strategies was funded by a super PAC called “Black PAC,” which paid the firm $11,254,919 to register voters for Joe Biden in 2020. Employees of GBI Strategies were paid $15 an hour or $120 a day, according to the police report. • GBI Strategies was believed to be operating not just in Muskegon, but throughout Michigan and in other Swing States. • Democrat Attorney General Dana Nessel’s office contacted the Muskegon Police Department and asked Michigan State Police to assist with a joint investigation. The Michigan police then turned their investigation over to the FBI. • Andrew Kloster, deputy general counsel at the United States Office of Personnel Management during the Trump Administration, said he was made aware of the investigation into GBI Strategies before the 2020 Election and attempted to raise the issue for further investigation. He was informed there were “standing orders not to deal with election matters” in the offices of the White House counsel office and Attorney General Bill Barr. • The investigation was not made public until 2023, after the police reports were obtained through a Michigan Freedom of Information Act request.
@KanekoaTheGreat - KanekoaTheGreat
President Trump Releases Summary of Election Fraud in the 2020 Presidential Election in the Swing States I look forward to fact-checkers debunking this, citing sources from the corporate media that spent four years claiming Donald Trump was a Russian agent and dismissing Hunter Biden's laptop as Russian disinformation. I encourage you to personally review the numerous citations in this report and reach your own conclusions. https://cdn.nucleusfiles.com/e0/e04e630c-63ff-4bdb-9652-e0be3598b5d4/summary20of20election20fraud20in20the20swing20states.pdf

@Crimsontider - Debbie Dooley
🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨🚨 An election cyber security firm in Palo Alto, CA warned both legislators and Raffensperger in 2019 that Dominion produces a paper ballot with a QR Code that violates GA law aka HB316 that requires voters be able to validate their ballot. They knew Dominion violated Georgia law, yet they purchased it anyway. 😡😡😡😡😡😡😡😡😡😡😡😡 https://drive.google.com/file/d/1gacOdB8BYdPGSwaRfXcUQVQCbNPq3KoV/view?usp=drivesdk

@pjcolbeck - Patrick Colbeck✝️
IMPORTANT: In one exceptional 14 minute presentation, Garland Favorito of @VoterGa dissects the problems with the integrity of elections using electronic voting systems. No hyperbole. Just facts painstakingly assembled by himself and skilled patriots such as Clay Parikh, Kevin Moncla and Phil Davis. Election officials hide negligence and/or malfeasance behind the opaqueness and complexity of modern electronic voting systems. This needs to stop. Transparency is the key to convincing myself and others that our elections are lawful and accurate. https://rumble.com/v58l10r-garland-favorito-shreds-2020-fulton-election-lies.html

@BehizyTweets - George
BREAKING: Politico just unleashed an article titled "The nation’s best hackers found vulnerabilities in voting machines — but no time to fix them." Hackers said the vulnerabilities they found were "particularly troubling during an election year like this.” "They found vulnerabilities in EVERYTHING from voting machines to e-poll books" So, after years of gaslighting us, Democrats are now openly admitting what We The Conspiracy Theorists have been right about voting machines since we started raising the alarm after the stolen 2020 election “As far as time goes, it is hard to make any real, major, systemic changes, but especially 90 days out from the election,” said Catherine Terranova, one of the organizers of the DEF CON “Voting Village” hacking event “It’s not a 90-day fix, It’s not a Microsoft every Tuesday, issue your patch and everything works fine,” Scott Algeier said. “It’s a pretty complicated process.” The gist of this is that they found outrageous vulnerabilities (in my opinion, features) that allowed hackers to flip votes without detection, and say we can't fix it in time for the 2024 election How about this? We just STOP using the machines and go back to caveman voting. The UK gave us hand-counted results within hours. There's no reason states with smaller populations take days and even weeks to count a couple thousand votes

@Rasmussen_Poll - Rasmussen Reports
Update: Testimony today affirmed that every Dominion system these government qualified cyber experts have examined in multiple states has these same 'open encryption keys.' This allows anyone with basic skills to gain access and change votes undetected. And some people ... have even higher skills ...

@realLizUSA - Liz Harrington
This is new??? Two experts testify in DeKalb GOP v Raffensperger that the election system in Gwinnett County, Georgia was remotely accessed from Belgrade, Serbia DURING the 2020 Election Similar activity also happened in Colorado, Michigan, and other states https://t.co/s00FxPLGsP

@BehizyTweets - George
BREAKING: Congresswoman MTG just reported that a voter in her district caught a Dominion voting machine flipping their vote to another candidate, likely from Trump to Kamala Georgia has the most corrupt election system in the country. Voters make selections on machines and then have to trust the machine to print out a piece of paper with their real selections. The tabulator doesn't even read the selections. It reads the QR code that SHOULD have the real selections, but as Professor J. Alex Halderman has demonstrated in court numerous times, the QR code can be manipulated to change votes without detection. Halderman also conducted a study showing that an overwhelming majority of voters don't even look at the "ballot" after it has been printed. Most trust the machine to do its job. This particular vulnerability is damning, and although patriots in Georgia have been screaming about it since 2020, corrupt Gov. Brian Kemp has continued to gaslight them.
@BehizyTweets - George
According to the person who wrote this, the election workers made "several attempts for correction" but got the same result from the machine & printer. All votes from that machine should be identified and set aside for inspection. The election officials must also preserve all data on the machines as required by federal & state law, unlike the mass deletion they pulled off after the 2020 election.
@BehizyTweets - George
The DOJ under Trump must make election integrity a super-priority. In my opinion, Dominion, E&S, Hart, etc, defrauded the federal government when they lied about internet connectivity on their machines. That's crime numero uno

@KylieJaneKremer - Kylie Jane Kremer
🚨GEORGIA ELECTION FRAUD🚨 Dominion voting machines. We are already seeing MAJOR issues with the machines across the Peach State as early voting is underway Congresswoman MTG confirmed there is an issue in her district (14th) with the machines flipping votes from Trump to Kamala A voter chose Trump on the BMD (ballot marking device) & then when the printed ballot came out of the table top printer (before it was scanned to actually cast the ballot), the text showed they selected Kamala After several attempts to fix it, they finally had to void out the ballot, use another machine and start fresh. They were able to successfully select Trump and it correctly showed on the printed ballot text. The ballot was then cast by scanning the printed ballot in the Polling Place Scanner (tabulator) A picture of a Fulton County ballot from 2020 is shown below so you can see how a printed ballot looks after selections are made (picture from Google) Voters across Georgia are now being told to double check the printed ballot, before it is scanned into the tabulator, to make sure the correct selections are shown in the text on the printed ballot, which is below the QR code that is also printed on the ballot However, I want to know what difference does it make what the printed text on the ballot shows when the tabulator is only reading the QR code, not the text on the printed ballot????? To those who may not be familiar with how the process works, selections are privately made on a BMD (ballot marking device aka touch screen tablet) and then are printed out on a table top printer. Each printed ballot shows a QR code on top and below it are the selections in text. The printed ballot is then scanned into the Polling Place Scanner (aka tabulator) where the QR code is read and tallies and then the process is complete The Polling Place Scanner only scans the QR code, which is NOT readable by the human eye. The QR code also cannot be read by any other device other than the Polling Place Scanner. It’s NOT like what we’re accustomed to with QR codes being easily scanned by our phones in our everyday lives So it DOES NOT MATTER what the text on the printed ballot states because the machine is not reading that, it is ONLY reading the QR code How do we know that this voter who had issues with their vote being switched, that was identified in the text portion of the printed ballot, is also not having this same issue with the QR code? There is literally NO WAY for anyone to verify what the QR code will be read as This is beyond disturbing as Governor Kemp, SOS Raffensperger, AG Chris Carr and the Georgia State Legislature had four years to secure our elections after all of the issues that happened with Dominion in 2020 and they chose NOT to do a damn thing I have been sounding the alarm bells that although Trump is overwhelmingly winning in the State of Georgia, nothing of substance has been done on election integrity, so we are being set up for a repeat of 2020 for a stolen election How does anyone that already cast their ballot know that their vote wasn’t switched, if they didn’t double check their printed ballot text, before feeding it into the tabulator? How does anyone know that even if the printed ballot text is correct, that the QR code is correct? How does anyone know anything, except for Dominion employees? Isn’t it our right as citizens to be able to ensure we are voting the way we intend? We are in BIG TROUBLE in Georgia & DJT’s path back to the White House depends on the Peach State The ONLY option at this point to ensure voters in Georgia have a secure, free & fair election is by declaring a State of Emergency to get rid of the machines and go to hand-marked, hand-counted paper ballots We are only on day four of early voting, with 17 more days to go, before Election Day. Buckle up because the powers that be have shown they will do ANYTHING to stop Trump & it seems they are just getting started
@KylieJaneKremer - Kylie Jane Kremer
Oh look, GA SOS COO @GabrielSterling already gaslighting Georgians that there is NO PROBLEM Nothing to see here folks 👀 Just machines flipping votes & no one being able to verify who they are voting for because of the QR code, that is unable to be read by the human eye https://t.co/2oOp6MLsr8